Buffer overflow is a critical concept in computer science and cybersecurity that describes a situation where a program writes more data into a memory buffer than it is designed to hold. This excess data spills over into adjacent memory locations, potentially overwriting important program instructions, variables, or control information. While it may initially appear to be a simple programming mistake, buffer overflow has historically been one of the most dangerous and widely exploited software vulnerabilities.
At its core, buffer overflow highlights a fundamental challenge in computing: managing memory safely. Computers allocate memory in fixed segments for efficiency and structure. When these boundaries are violated, the system no longer behaves predictably. Understanding buffer overflow is essential not only for developers but also for cybersecurity professionals, as it provides insight into how attackers exploit weaknesses in software systems.
Understanding Memory and Buffers in Depth
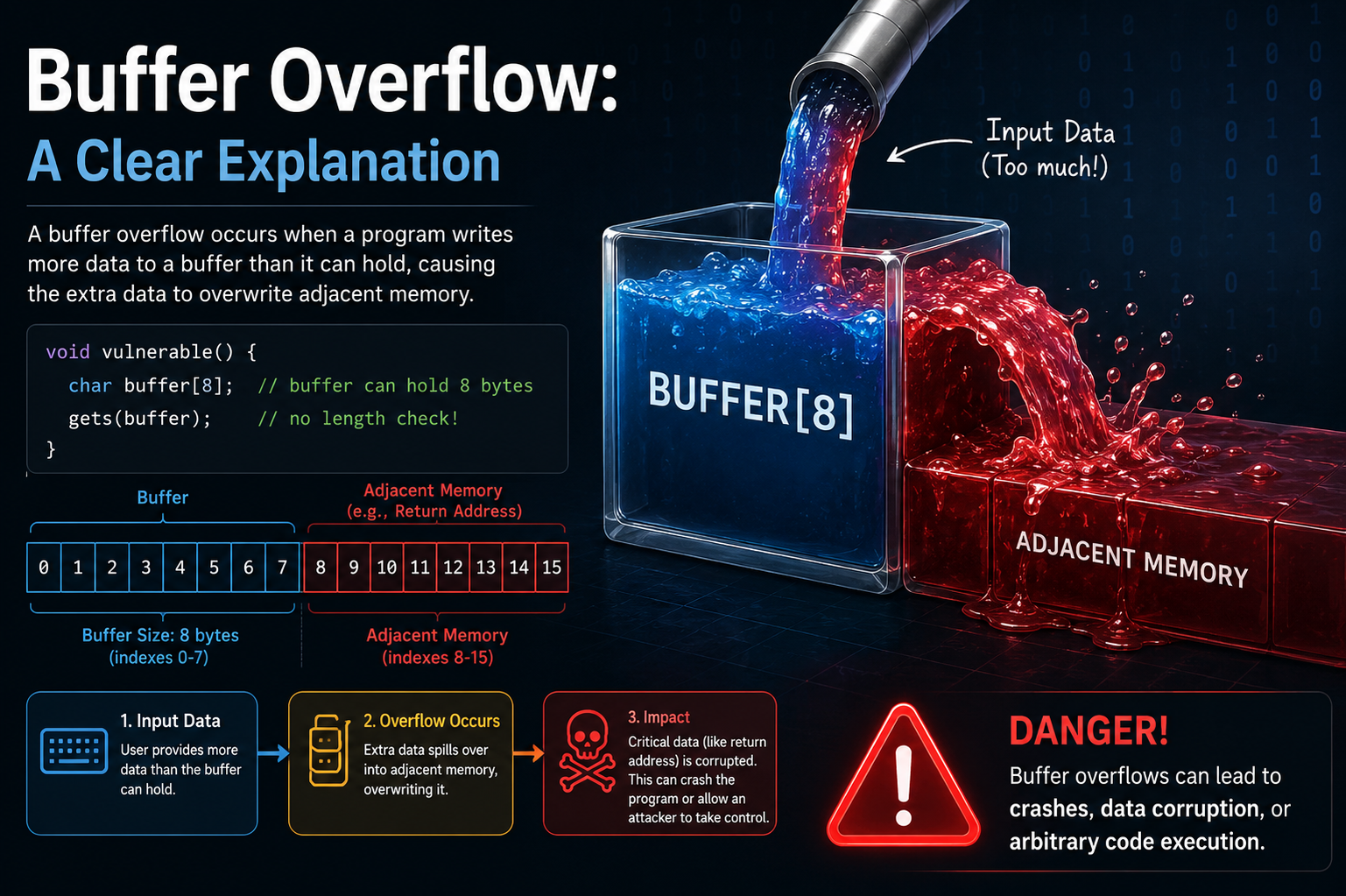
To fully grasp buffer overflow, it is important to understand how memory works in a running program. When a program executes, it uses memory to store variables, function calls, and temporary data. A buffer is simply a reserved space in memory used to hold data temporarily.
For example, when a user types a password into a login form, that input is stored in a buffer before being processed. These buffers are allocated with a fixed size. If the system allocates space for 8 characters and the user inputs 20 characters, the extra data has nowhere safe to go.
Instead of being rejected automatically, the extra data spills into adjacent memory. This is where the danger begins. The overwritten memory might belong to another variable, a function pointer, or even system-level instructions that control program execution.
Memory in most programming environments is organized into regions such as the stack, heap, code segment, and data segment. Buffer overflow typically affects the stack or heap, depending on where the buffer is allocated. Each region plays a different role, and corruption in any of them can lead to unpredictable behavior.
How Buffer Overflow Occurs Step by Step
Buffer overflow does not happen randomly. It follows a predictable sequence of events. First, a program allocates a fixed-size buffer. Next, it receives input from a user, file, or network source. If that input is not properly validated, it may exceed the buffer’s capacity.
Once the buffer limit is exceeded, the extra data begins to overwrite adjacent memory locations. This overwrite may not immediately crash the program, which makes the vulnerability more dangerous. Instead, the program may continue executing with corrupted data.
If critical memory regions are affected, such as return addresses or control flags, the program’s execution flow can be altered. In advanced exploitation scenarios, attackers carefully craft input so that the overflowed data includes malicious instructions that the system later executes.
This transition from simple overflow to execution control is what makes buffer overflow a powerful attack vector.
Stack-Based Buffer Overflow Explained
The stack is a region of memory used to manage function calls and local variables. Each time a function is called, a stack frame is created containing return addresses, parameters, and local data.
In a stack-based buffer overflow, the attacker targets a buffer located on the stack. When the buffer is overflowed, it can overwrite the return address stored in the same stack frame. The return address tells the program where to continue execution after a function completes.
If this address is overwritten with malicious data, the program may jump to an unintended location in memory. In older systems, this technique allowed attackers to execute arbitrary code by injecting malicious instructions directly into memory.
Even though modern protections exist, stack-based overflow remains an important concept in understanding how memory corruption attacks work.
Heap-Based Buffer Overflow Explained
Unlike the stack, the heap is used for dynamic memory allocation. Programs allocate and free memory on the heap during runtime. Heap-based buffer overflow occurs when a buffer in this region is overrun.
Although heap overflows are generally more complex to exploit, they can still lead to serious consequences. Overwriting heap metadata or adjacent objects can corrupt program logic, alter data structures, or lead to unexpected behavior.
In some cases, heap overflow can be used to manipulate object-oriented structures, especially in languages that rely heavily on dynamic memory allocation. This makes heap overflows particularly relevant in modern software systems.
Why Buffer Overflow is Dangerous
The danger of buffer overflow lies in its ability to break the fundamental assumption of memory safety. Programs assume that memory boundaries will be respected. When this assumption is violated, the entire execution flow becomes unreliable.
One of the most serious outcomes is arbitrary code execution. If an attacker can control what is written into memory, they may be able to insert instructions that the system executes unknowingly. This can lead to full system compromise.
Another danger is privilege escalation. A low-privilege user may exploit a buffer overflow in a system service to gain higher-level access. This is especially critical in operating systems and server environments.
Even when exploitation is not possible, buffer overflow can still cause denial of service. A corrupted program may crash repeatedly, disrupting services and causing downtime.
Historical Importance of Buffer Overflow Attacks
Buffer overflow vulnerabilities have played a major role in the history of cybersecurity. Many early worms and viruses relied on these flaws to spread across networks. Because older systems lacked strong memory protections, exploitation was relatively straightforward.
Over time, attackers refined their techniques, developing methods such as return-to-libc and return-oriented programming. These advanced techniques allowed exploitation even when direct code injection was blocked.
The historical significance of buffer overflow lies in how it shaped modern security practices. Many of today’s protective mechanisms were introduced specifically to counter these attacks.
Modern Defensive Mechanisms
Modern operating systems and compilers include several protections against buffer overflow attacks. One of the most common is stack canaries. These are special values placed between buffers and control data on the stack. If a buffer overflow occurs, the canary value is overwritten and the system detects the anomaly before execution continues.
Another important protection is Address Space Layout Randomization. This technique randomizes memory locations each time a program runs, making it difficult for attackers to predict where to inject or redirect code.
Data Execution Prevention is another defense mechanism that marks certain memory regions as non-executable. This prevents injected data from being executed as code.
While these defenses significantly reduce the risk, they do not eliminate buffer overflow vulnerabilities entirely. Poorly written code can still be exploited under certain conditions.
Programming Errors That Lead to Buffer Overflow
Buffer overflow is often the result of simple yet dangerous programming mistakes. One common issue is lack of input validation. When a program assumes that input will always be within expected limits, it becomes vulnerable.
Another issue is the use of unsafe functions that do not check memory boundaries. These functions may copy data without verifying whether the destination buffer is large enough.
Incorrect loop conditions can also lead to overflow. For example, iterating beyond the allocated size of an array can overwrite adjacent memory.
Additionally, misunderstanding memory allocation and deallocation can create situations where buffers are misused or overwritten unintentionally.
Role of Programming Languages in Buffer Overflow
Programming languages play a significant role in determining vulnerability to buffer overflow. Low-level languages such as C and C++ provide direct access to memory, which gives developers great control but also introduces risk.
These languages do not inherently enforce memory safety, so developers must manually manage buffers and ensure boundaries are not violated.
Higher-level languages such as Java, Python, and C# include built-in memory management and boundary checking. This reduces the likelihood of buffer overflow significantly, although it does not completely eliminate security risks.
The trade-off between performance and safety is an important consideration in software design.
Real-World Impact on Systems and Applications
Buffer overflow vulnerabilities can affect a wide range of systems, from desktop applications to critical infrastructure. In enterprise environments, a single vulnerability can expose entire networks to compromise.
Embedded systems, such as those used in medical devices or industrial machinery, are particularly sensitive because they often run outdated software with limited security updates.
Web servers, database systems, and network services are also common targets. Since these systems often process untrusted input from external sources, they are especially vulnerable if proper validation is not implemented.
The widespread nature of software makes buffer overflow a persistent concern in cybersecurity.
Techniques Used by Attackers
Attackers use various techniques to exploit buffer overflow vulnerabilities. One common approach is crafting specially designed input that overwrites specific memory locations.
Another technique involves shellcode injection, where malicious instructions are inserted into memory and executed by the program.
More advanced methods include bypassing security protections using indirect execution techniques. These methods do not rely on injecting new code but instead reuse existing code fragments in memory.
Understanding these techniques is important for defenders to anticipate and prevent attacks.
Prevention Strategies in Software Development
Preventing buffer overflow requires a combination of good coding practices and security awareness. Input validation is one of the most important strategies. Every input should be checked for size, format, and validity before being processed.
Using safe libraries and functions that enforce boundary checks is also essential. Developers should avoid outdated or unsafe memory manipulation functions.
Code reviews and static analysis tools can help identify potential vulnerabilities before software is deployed. Regular testing, including fuzz testing, can also reveal hidden buffer overflow issues.
Security should be integrated into every stage of software development rather than treated as an afterthought.
Importance of Developer Awareness
One of the most effective defenses against buffer overflow is developer education. Many vulnerabilities arise simply because developers are unaware of how memory management errors can be exploited.
Training developers to understand memory architecture, input validation, and secure coding principles significantly reduces risk.
As software systems become more complex, awareness of low-level vulnerabilities remains essential even when using high-level programming languages.
Conclusion
Buffer overflow remains one of the most important concepts in understanding software vulnerabilities and system security. Although modern defenses have made exploitation more difficult, the underlying issue still exists in many applications, especially those written in low-level languages or legacy systems.
At its core, buffer overflow demonstrates how small programming mistakes can lead to large-scale security risks. From simple crashes to full system compromise, the consequences can be severe.
Understanding how buffer overflow occurs, how it is exploited, and how it can be prevented is essential for building secure software. As technology continues to evolve, the importance of secure memory management remains constant.
Ultimately, buffer overflow serves as a reminder that security must be built into software from the ground up, not added later as an afterthought.