802.1X is a standardized network access control protocol that provides a structured method for authenticating devices before they are allowed to connect to a network. It was developed to address a major security gap in traditional network environments where devices could often plug in or connect wirelessly and immediately gain access without identity verification. As networks expanded in size and complexity, especially in enterprise and public environments, the need for a stronger, identity-based access control mechanism became essential.
At its core, 802.1X ensures that every device must prove its identity before it is granted access to network resources. This applies to both wired Ethernet connections and wireless Wi-Fi networks. The protocol acts as a protective checkpoint at the very edge of the network, preventing unauthorized or unknown devices from interacting with internal systems. This approach significantly reduces the attack surface and helps organizations maintain a secure and controlled environment.
The importance of 802.1X lies in its ability to enforce security at the point of entry rather than relying only on internal defenses. Instead of allowing unrestricted access and then filtering threats later, it ensures that only trusted devices can even enter the network in the first place.
Core Architecture of 802.1X
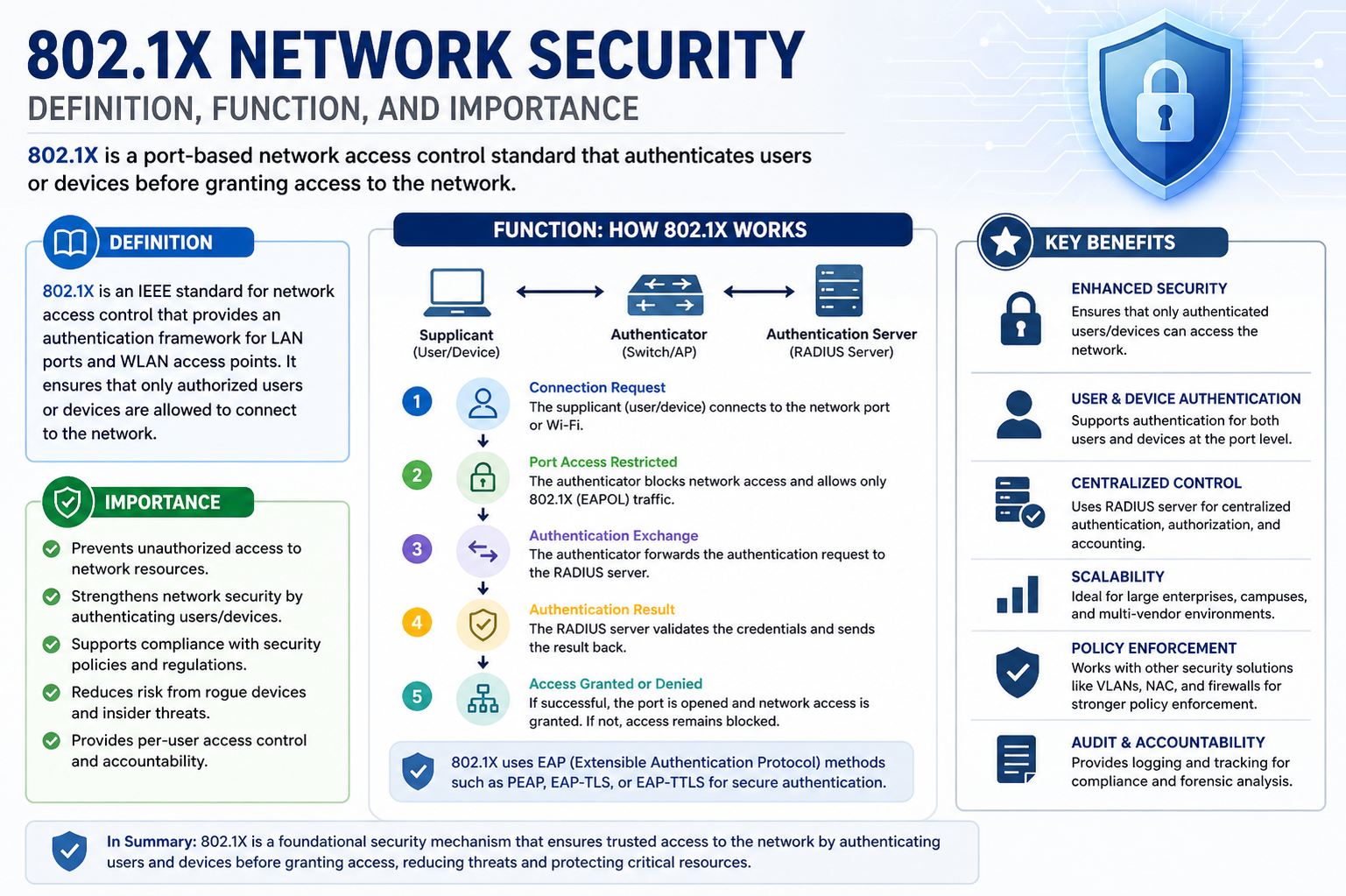
The 802.1X framework is built around three essential components that work together to manage authentication and access control. These components include the supplicant, the authenticator, and the authentication server.
The supplicant is the device or client attempting to gain access to the network. This could be a laptop, smartphone, printer, or any other network-enabled device. The supplicant is responsible for initiating the authentication process by sending credentials or identity information.
The authenticator is the network device that acts as the gatekeeper. This is usually a network switch in wired environments or a wireless access point in Wi-Fi networks. The authenticator controls whether the supplicant is allowed to communicate with the rest of the network. Until authentication is successfully completed, the authenticator restricts access.
The authentication server is the system that validates the credentials provided by the supplicant. In most implementations, this role is handled by a RADIUS server. The authentication server checks whether the credentials are valid and determines whether access should be granted or denied. It then communicates the decision back to the authenticator.
This separation of roles ensures a secure and scalable authentication process. Each component has a clearly defined responsibility, making the system easier to manage and more resistant to compromise.
The Authentication Process Explained
The 802.1X authentication process begins when a device attempts to connect to the network. At this stage, the authenticator places the port or connection in a blocked state, allowing only authentication traffic to pass through. No normal data traffic is permitted until the device is verified.
The supplicant then sends an initial request to the authenticator, which forwards it to the authentication server. The communication between these components is handled using the Extensible Authentication Protocol, which supports a wide range of authentication methods.
Once the authentication server receives the credentials, it evaluates them based on predefined policies. If the credentials are valid, the server sends an approval message back to the authenticator. The authenticator then opens network access for the supplicant, allowing full communication with authorized resources. If authentication fails, the device remains blocked and cannot access the network.
This process happens quickly and is usually transparent to the user, but it plays a critical role in ensuring that only verified devices are allowed to connect.
Role of EAP in 802.1X
The Extensible Authentication Protocol is a key part of how 802.1X operates. It is not a single authentication method but rather a framework that supports multiple methods of verifying identity. This flexibility allows organizations to choose the authentication approach that best fits their security requirements.
Common EAP methods include password-based authentication, certificate-based authentication, and token-based systems. Certificate-based methods are often considered the most secure because they rely on digital certificates issued by trusted authorities. Password-based methods are easier to deploy but may be less secure if not properly managed.
EAP allows 802.1X to remain adaptable across different environments, from small office networks to large enterprise infrastructures. It ensures that the protocol can evolve alongside emerging security technologies without requiring a complete redesign.
802.1X in Wired and Wireless Networks
Although 802.1X is often associated with wireless security, it is equally important in wired environments. In wired networks, each physical port on a switch can be configured to require authentication before granting access. This prevents unauthorized users from simply plugging into a network jack and gaining immediate access.
In wireless networks, 802.1X is commonly used in enterprise Wi-Fi deployments. When a user connects to a secure wireless network, the authentication process occurs before the device is allowed to join the network. This ensures that only authorized users can access internal resources over Wi-Fi.
By securing both wired and wireless access points, 802.1X provides comprehensive protection across the entire network infrastructure.
Security Benefits of 802.1X
One of the most significant advantages of 802.1X is its ability to prevent unauthorized access at the network edge. By requiring authentication before granting access, it eliminates many common attack vectors used by malicious actors.
It also helps reduce the risk of insider threats by ensuring that even internal users must authenticate before accessing sensitive resources. This creates a more controlled and auditable environment where access can be tracked and managed effectively.
Another important benefit is the support for centralized authentication management. Organizations can enforce consistent security policies across all devices and users, making it easier to maintain compliance with security standards and regulations.
802.1X also enhances visibility into network activity. Since every connection must be authenticated, administrators can track who is accessing the network, when they are accessing it, and from which device. This level of visibility is valuable for both security monitoring and troubleshooting.
Challenges and Limitations of 802.1X
Despite its advantages, 802.1X can introduce complexity in network configuration and management. Proper deployment requires coordination between network infrastructure, authentication servers, and client devices.
One challenge is ensuring compatibility across all devices. Older devices or specialized hardware may not support 802.1X, requiring alternative access methods or exceptions in security policies.
Another limitation is the dependency on a reliable authentication server. If the authentication system becomes unavailable, it can disrupt network access for legitimate users. For this reason, redundancy and failover mechanisms are often necessary in enterprise environments.
Initial setup and configuration can also be time-consuming, especially in large organizations with diverse device ecosystems. However, once properly implemented, the long-term security benefits typically outweigh the setup complexity.
Best Practices for Implementing 802.1X
Successful implementation of 802.1X requires careful planning and consistent policy enforcement. One important practice is to use certificate-based authentication wherever possible, as it provides stronger security compared to password-based methods.
Network segmentation can also improve security by limiting access based on user roles or device types. This ensures that even authenticated devices only access the resources they are authorized to use.
Regular monitoring and auditing of authentication logs help identify suspicious activity and ensure compliance with security policies. Keeping authentication infrastructure updated and properly maintained is also critical to avoid vulnerabilities.
Testing the deployment in stages before full rollout can help identify compatibility issues and reduce disruption to users.
Real-World Use Cases of 802.1X
In enterprise environments, 802.1X is widely used to secure corporate networks, ensuring that only company-issued or approved devices can connect. Educational institutions use it to manage student and staff access to campus networks, maintaining separation between different user groups.
Healthcare organizations rely on 802.1X to protect sensitive patient data by ensuring that only authorized medical devices and personnel can access clinical systems. Government agencies use it to secure classified and internal networks, where strict access control is essential.
Public Wi-Fi networks in controlled environments, such as airports or corporate guest networks, also use modified forms of 802.1X to manage user authentication and access restrictions.
Future of 802.1X in Network Security
As network environments continue to evolve, 802.1X remains a foundational technology for access control. Its integration with modern identity management systems, cloud-based authentication services, and zero-trust security models is becoming increasingly important.
In zero-trust architectures, where no device is trusted by default, 802.1X plays a critical role in verifying identity before access is granted. This aligns with modern security principles that emphasize continuous verification and least-privilege access.
With the growth of IoT devices and mobile endpoints, the need for scalable and flexible authentication mechanisms will continue to increase. 802.1X is expected to evolve alongside these trends, maintaining its relevance as a core component of network security infrastructure.
Role of 802.1X in Modern Enterprise Security
In modern enterprise environments, 802.1X has become a foundational element of secure network design. As organizations increasingly adopt cloud services, remote work models, and bring-your-own-device (BYOD) policies, controlling who and what connects to internal systems has become more complex. 802.1X helps address this challenge by enforcing identity-based access control at the network entry point, ensuring that every connection is verified before trust is established.
This is especially important in large-scale organizations where thousands of devices may attempt to connect daily. Without a centralized authentication mechanism, managing access manually would be inefficient and highly error-prone. 802.1X allows administrators to enforce consistent security policies across all access points, regardless of location or device type.
It also plays a major role in supporting zero-trust security strategies. In a zero-trust model, no device is automatically trusted, even if it is inside the corporate network. Every access request must be verified continuously. 802.1X supports this approach by ensuring that authentication occurs at the initial connection stage and can be combined with additional security checks throughout the session.
Integration with Identity and Access Management Systems
One of the key strengths of 802.1X is its ability to integrate with identity and access management systems. These systems store user identities, credentials, and access policies, allowing organizations to centralize control over authentication.
When a device attempts to connect, 802.1X forwards authentication requests to these identity systems, which evaluate whether the user or device complies with security policies. This integration allows for advanced access control decisions based not only on credentials but also on factors such as device type, user role, location, and security posture.
For example, a company may allow full access to corporate devices while restricting guest devices to internet-only access. Similarly, employees in different departments may be granted different levels of network access based on their job responsibilities.
This level of granularity enhances security while maintaining flexibility for legitimate users.
Device Authentication vs User Authentication
802.1X supports both device-based and user-based authentication, depending on how it is configured. Device authentication focuses on verifying the identity of the hardware itself, often using digital certificates installed on trusted devices. This ensures that only approved machines can connect to the network.
User authentication, on the other hand, verifies the credentials of the individual attempting to access the network. This may involve usernames, passwords, or multi-factor authentication methods. In many enterprise environments, both methods are used together to provide layered security.
Combining device and user authentication strengthens protection by ensuring that even if one layer is compromised, additional verification is still required before access is granted.
Security Policies Enforced Through 802.1X
802.1X enables organizations to enforce a wide range of security policies at the network level. One common policy is network segmentation, where users are assigned to different network segments based on their identity or role. This limits lateral movement within the network and reduces the potential impact of a security breach.
Another important policy is dynamic VLAN assignment. Based on authentication results, devices can be automatically placed into specific virtual LANs with predefined access rules. This allows for flexible yet secure network management without requiring manual configuration for each device.
Access control policies can also include restrictions on time of access, device health checks, and compliance requirements. For example, a device may only be allowed to connect if it has up-to-date security patches and antivirus software installed.
These policies make 802.1X a powerful tool for enforcing organizational security standards consistently across the entire network.
802.1X in Wireless Security Environments
In wireless networks, 802.1X is widely used to secure enterprise Wi-Fi connections. Unlike open or shared password-based networks, 802.1X-based wireless networks require individual authentication for each user or device.
When a user connects to a secure Wi-Fi network, the authentication process takes place before the device is granted access to internet or internal resources. This ensures that unauthorized users cannot simply guess or share a single password to gain access.
Wireless implementations of 802.1X are often combined with strong encryption protocols to protect data in transit. This combination ensures both secure authentication and secure communication over the air.
As mobile device usage continues to grow, 802.1X remains a critical component of secure wireless infrastructure in enterprises, universities, hospitals, and government facilities.
Wired Network Security with 802.1X
While wireless security often receives more attention, wired networks are equally vulnerable if not properly protected. 802.1X provides a strong defense mechanism for Ethernet-based environments by controlling access at the switch port level.
When a device is plugged into a network port, the switch initially blocks all traffic except authentication requests. Only after successful verification is the port fully activated. This prevents unauthorized users from gaining access simply by physically connecting to a network jack.
This approach is particularly useful in environments such as office buildings, data centers, and shared workspaces, where physical access to network ports may not always be fully controlled.
Scalability and Performance Considerations
One of the advantages of 802.1X is its ability to scale across large and complex networks. However, proper planning is required to ensure that authentication systems can handle high volumes of requests without performance degradation.
In large enterprises, authentication servers must be designed for redundancy and load balancing. This ensures that even during peak usage or system failures, network access remains available to authorized users.
Caching mechanisms can also be used to improve performance by temporarily storing successful authentication results, reducing the need for repeated verification in certain scenarios.
Despite the additional overhead of authentication, modern network hardware is optimized to handle 802.1X processes efficiently with minimal impact on user experience.
Common Deployment Challenges
Deploying 802.1X across an organization can present several challenges. One of the most common issues is device compatibility. Not all legacy systems or specialized hardware support 802.1X, which may require exceptions or alternative access methods.
Another challenge is user experience during initial setup. If authentication fails due to misconfiguration or expired credentials, users may be locked out of the network, leading to support requests and delays.
Certificate management can also be complex, especially in environments using certificate-based authentication. Proper lifecycle management of certificates is essential to avoid disruptions.
To address these challenges, organizations often implement phased rollouts, starting with pilot groups before expanding to full deployment.
Monitoring and Troubleshooting 802.1X Networks
Effective monitoring is essential for maintaining a stable 802.1X environment. Administrators must regularly review authentication logs to identify failed login attempts, unusual activity, or configuration issues.
Troubleshooting typically involves checking communication between the supplicant, authenticator, and authentication server. Issues may arise from incorrect credentials, expired certificates, network misconfigurations, or server downtime.
Network management tools can help visualize authentication flows and quickly identify where failures are occurring. This improves response times and reduces downtime for end users.
Importance of Continuous Security Improvement
802.1X is not a static solution but part of an evolving security strategy. As cyber threats become more advanced, organizations must continuously update their authentication policies and infrastructure.
This includes adopting stronger authentication methods, integrating with modern security frameworks, and regularly reviewing access controls. Combining 802.1X with additional security layers such as endpoint detection and response systems further strengthens overall protection.
Continuous improvement ensures that the network remains resilient against emerging threats while maintaining efficient access for legitimate users.
Advanced Authentication Methods in 802.1X
802.1X supports multiple advanced authentication methods that enhance security beyond basic username and password verification. One of the most secure approaches is certificate-based authentication, where digital certificates are issued to trusted devices and users. These certificates are validated by the authentication server before network access is granted, ensuring a high level of trust and reducing the risk of credential theft.
Another widely used method is multi-factor authentication, which combines something the user knows (like a password) with something they have (like a mobile device or token) or something they are (such as biometric data). When integrated with 802.1X, multi-factor authentication significantly strengthens network access security by adding additional verification layers.
Some environments also use machine authentication alongside user authentication. In this setup, the device itself is authenticated first, and then the user logs in separately. This dual-layer approach ensures that both the device and the user are verified independently before full access is granted.
These advanced methods make 802.1X adaptable to high-security environments where basic authentication alone is not sufficient.
Role of Certificates in Secure Network Access
Digital certificates play a critical role in strengthening 802.1X security. These certificates are issued by a trusted certificate authority and installed on devices or user systems. During the authentication process, the authentication server verifies the certificate’s validity, expiration date, and issuing authority.
If the certificate is valid and trusted, the device is allowed to proceed with network access. If the certificate is missing, expired, or revoked, access is denied. This eliminates many risks associated with password-based systems, such as phishing, brute-force attacks, and credential reuse.
Certificate-based authentication also simplifies large-scale deployments because users do not need to manually enter credentials every time they connect. Once installed, certificates provide seamless and secure access while maintaining strong identity verification.
802.1X and Network Segmentation Strategies
Network segmentation is a critical security strategy that works effectively with 802.1X. By dividing a network into smaller, isolated segments, organizations can limit access to sensitive resources and reduce the impact of potential security breaches.
When integrated with 802.1X, segmentation becomes dynamic. Devices are automatically assigned to specific network segments based on authentication results. For example, employees may be placed in a secure corporate network, while guests are directed to a restricted internet-only segment.
This dynamic segmentation reduces the need for manual configuration and ensures that access policies are consistently enforced. It also prevents unauthorized lateral movement within the network, making it more difficult for attackers to spread across systems if a breach occurs.
Dynamic VLAN Assignment in 802.1X Networks
Dynamic VLAN assignment is one of the most powerful features enabled by 802.1X. VLANs, or virtual local area networks, allow administrators to logically separate network traffic without requiring physical separation of infrastructure.
When a device successfully authenticates, the authentication server can assign it to a specific VLAN based on predefined policies. This assignment determines what resources the device can access.
For example, a finance department device may be placed in a VLAN with access to financial systems, while a guest device may be assigned to a restricted VLAN with internet-only access. This dynamic approach improves security while simplifying network management.
It also reduces administrative overhead because VLAN assignments are handled automatically during authentication rather than manually configured for each device.
802.1X in Zero Trust Architecture
Zero trust security is a modern approach that assumes no device or user should be trusted by default, even if they are inside the network perimeter. 802.1X aligns closely with this philosophy by enforcing strict authentication at the network entry point.
In a zero trust model, every access request is verified, and trust is continuously evaluated. 802.1X provides the first layer of this verification by ensuring that only authenticated devices can connect to the network.
When combined with additional security tools such as endpoint monitoring, identity management, and continuous risk assessment, 802.1X becomes a key component of a fully integrated zero trust architecture.
This approach is increasingly adopted by organizations seeking to strengthen their cybersecurity posture in response to evolving threats.
Policy-Based Access Control Using 802.1X
802.1X enables organizations to implement policy-based access control, where network access decisions are made based on predefined rules. These rules can consider multiple factors, including user identity, device type, security compliance, and location.
For example, a policy may allow employees to access internal systems only if they are using company-managed devices with updated security software. Similarly, remote users may be required to pass additional verification steps before accessing sensitive data.
This level of control ensures that access is not simply granted based on credentials alone but is influenced by a broader security context. It allows organizations to enforce consistent security standards across all users and devices.
Impact of 802.1X on Network Performance
While 802.1X adds an authentication step to the network connection process, modern implementations are highly optimized to minimize performance impact. Authentication typically occurs within seconds and does not significantly delay user access.
However, network performance can be affected if authentication servers are overloaded or improperly configured. To prevent this, organizations often deploy multiple authentication servers with load balancing and redundancy.
Caching successful authentication results can also reduce repeated authentication requests, improving efficiency without compromising security.
Overall, the performance overhead of 802.1X is minimal compared to the significant security benefits it provides.
Security Risks Without 802.1X
Without 802.1X, networks are more vulnerable to unauthorized access and a wide range of security threats. Any device connected to an open port or unsecured wireless network may gain immediate access to internal systems.
This increases the risk of malware infections, data breaches, and unauthorized data exfiltration. Attackers can easily exploit unsecured network entry points to gain a foothold inside the organization.
Even internal threats become more dangerous in the absence of proper authentication controls, as malicious insiders or compromised devices can move freely within the network.
802.1X significantly reduces these risks by ensuring that every connection is verified before access is granted.
Integration with Modern Security Technologies
802.1X is often integrated with other modern security technologies to create a comprehensive defense system. These include endpoint detection and response systems, intrusion detection systems, and security information and event management platforms.
By combining these technologies, organizations can monitor network activity in real time, detect suspicious behavior, and respond quickly to potential threats.
Integration with cloud-based identity platforms also allows for centralized authentication across on-premises and cloud environments, improving consistency and scalability.
This interconnected approach strengthens overall security and provides deeper visibility into network activity.
Future Evolution of 802.1X Technology
As networks continue to evolve, 802.1X is expected to become even more tightly integrated with automated and intelligent security systems. Machine learning and artificial intelligence may be used to analyze authentication patterns and detect anomalies in real time.
The growth of Internet of Things devices will also drive further enhancements, as organizations need scalable methods to authenticate a large number of diverse devices securely.
Cloud-based authentication services are likely to play a larger role, enabling more flexible and distributed deployment models. Despite these changes, the core principle of 802.1X—verifying identity before granting access—will remain central to network security.
Final Perspective on 802.1X Importance
802.1X remains one of the most important protocols in modern network security because it enforces control at the most critical point: the network entry layer. By ensuring that only authenticated devices and users can connect, it provides a strong foundation for all other security measures.
Its adaptability, scalability, and integration capabilities make it suitable for a wide range of environments, from small organizations to global enterprises. As cybersecurity threats continue to grow in complexity, 802.1X will remain a key technology in protecting digital infrastructure and maintaining secure network access.
802.1X in Bring Your Own Device (BYOD) Environments
Bring Your Own Device environments introduce significant complexity into network security because personal devices are not always managed or controlled by the organization. 802.1X helps address this challenge by enforcing strict authentication before any device is allowed to connect to the network, regardless of ownership.
In BYOD scenarios, employees may use personal laptops, smartphones, or tablets to access corporate resources. Without proper control, these devices can become entry points for malware or unauthorized access. 802.1X reduces this risk by requiring each device to authenticate before gaining access, ensuring that only approved users and compliant devices can connect.
Organizations often combine 802.1X with device profiling and compliance checks. This allows the network to evaluate whether a personal device meets security requirements, such as having updated operating systems, encryption enabled, and security software installed. Devices that fail these checks can be restricted to limited network access or completely blocked.
This controlled approach allows organizations to support flexibility for users while maintaining strong security standards.
Guest Network Access Control Using 802.1X
Guest access is another important use case for 802.1X in modern networks. Visitors such as clients, contractors, and partners often require temporary internet access without being granted access to internal systems.
With 802.1X, guest users can be authenticated through separate credentials or captive portal systems integrated with the authentication infrastructure. Once verified, guests are typically assigned to isolated network segments that provide internet access only.
This segmentation ensures that guest devices cannot interact with sensitive corporate resources or other internal systems. It also provides accountability, as guest activity can be monitored and logged for security purposes.
By using 802.1X for guest access, organizations can maintain a balance between convenience and security without compromising internal network integrity.
Role of RADIUS in 802.1X Authentication
RADIUS plays a central role in the functioning of 802.1X networks. It acts as the backend authentication server that processes requests from network devices and makes decisions about whether access should be granted.
When a device attempts to connect, the authenticator forwards authentication requests to the RADIUS server. The server then checks the credentials against its database or external identity systems. Based on the result, it sends an accept or reject response back to the network device.
RADIUS also supports advanced features such as accounting and policy enforcement. It can track session duration, monitor user activity, and apply access rules based on organizational policies.
This centralized approach simplifies authentication management and ensures consistency across the entire network infrastructure.
802.1X and Network Access Visibility
One of the often overlooked benefits of 802.1X is improved visibility into network access. Because every device must authenticate before connecting, administrators gain detailed insight into who is accessing the network and from which device.
This visibility allows organizations to detect unusual behavior, such as repeated failed login attempts or unauthorized device connections. It also helps with auditing and compliance reporting, as access logs can be used to demonstrate adherence to security policies.
In addition, visibility improves incident response capabilities. If a security issue occurs, administrators can quickly identify the affected devices and users, isolate them from the network, and take corrective action.
Common Misconfigurations and Their Impact
While 802.1X is highly effective when properly configured, misconfigurations can lead to security gaps or connectivity issues. One common mistake is improper certificate deployment, which can prevent legitimate devices from authenticating successfully.
Another issue arises when fallback authentication methods are too permissive. If a network allows unsecured access when 802.1X fails, attackers may exploit this weakness to bypass security controls.
Incorrect VLAN assignments or policy rules can also lead to unauthorized access or restricted connectivity for legitimate users. These issues highlight the importance of careful planning and testing during deployment.
Regular audits and configuration reviews help ensure that the system remains secure and functions as intended.
802.1X in High-Security Industries
Certain industries require extremely strict access control due to the sensitivity of their data and operations. Healthcare, finance, government, and defense sectors heavily rely on 802.1X to protect critical systems.
In healthcare environments, 802.1X helps secure patient records and medical devices, ensuring that only authorized personnel can access sensitive information. In financial institutions, it protects transactional systems and customer data from unauthorized access.
Government and defense networks use 802.1X as part of broader security frameworks to protect classified information and critical infrastructure. In these environments, authentication is often combined with multi-layered security controls for maximum protection.
802.1X and Endpoint Security Integration
Modern security strategies often integrate 802.1X with endpoint security solutions. These solutions monitor the health and compliance of devices before and after they connect to the network.
For example, an endpoint security system may check whether a device has updated antivirus software, firewall protection, and security patches installed. If a device does not meet these requirements, 802.1X can restrict or deny access until the issue is resolved.
This integration ensures that network access is not based solely on identity but also on device security posture. It significantly reduces the risk of compromised devices entering the network.
Automation and Policy Enforcement in 802.1X Networks
Automation plays an important role in modern 802.1X deployments. Network policies can be automatically enforced based on authentication results without requiring manual intervention.
For example, when a user connects, the system can automatically assign them to the correct VLAN, apply firewall rules, and configure access permissions based on their role. This reduces administrative workload and ensures consistent policy enforcement across the network.
Automation also improves scalability, making it easier to manage large and dynamic environments where users and devices frequently change.
Challenges in Large-Scale Deployments
In large organizations, deploying 802.1X across thousands of devices and network ports can be complex. Coordination between IT teams, security teams, and infrastructure systems is required to ensure smooth implementation.
One challenge is maintaining consistent policy enforcement across multiple locations. Remote offices, data centers, and cloud environments must all follow the same authentication standards.
Another challenge is managing device diversity. Organizations often support a wide range of operating systems and hardware, each with different levels of 802.1X support.
Proper planning, phased rollouts, and standardized configuration templates help address these challenges effectively.
Long-Term Strategic Value of 802.1X
Beyond immediate security benefits, 802.1X provides long-term strategic value by supporting scalable and adaptable network security architectures. It enables organizations to build secure foundations that can evolve with changing technology landscapes.
As networks continue to expand and become more distributed, identity-based access control becomes increasingly important. 802.1X provides the framework needed to support this shift, ensuring that security remains consistent across all environments.
It also supports future integration with emerging technologies such as artificial intelligence-driven security analytics and adaptive access control systems.
Conclusion
802.1X remains a critical component of modern network security because it enforces authentication at the most important point of access. By verifying every device before it connects, it significantly reduces the risk of unauthorized access and strengthens overall security posture.
Its flexibility, scalability, and compatibility with modern security frameworks make it suitable for virtually all types of network environments. As cybersecurity threats continue to evolve, 802.1X will remain a foundational technology in protecting digital infrastructure and ensuring secure communication across networks. It also continues to adapt alongside emerging authentication models, cloud-based identity systems, and zero-trust architectures, making it highly relevant in modern IT ecosystems.
Organizations benefit from its ability to integrate with advanced monitoring and policy enforcement tools, which strengthens overall visibility and control. With increasing adoption of remote work, mobile devices, and IoT systems, the demand for strong, identity-based access control is growing rapidly. In this evolving landscape, 802.1X provides a reliable, future-ready framework that helps maintain trust, reduce vulnerabilities, and support secure, scalable network operations across both enterprise and distributed environments.