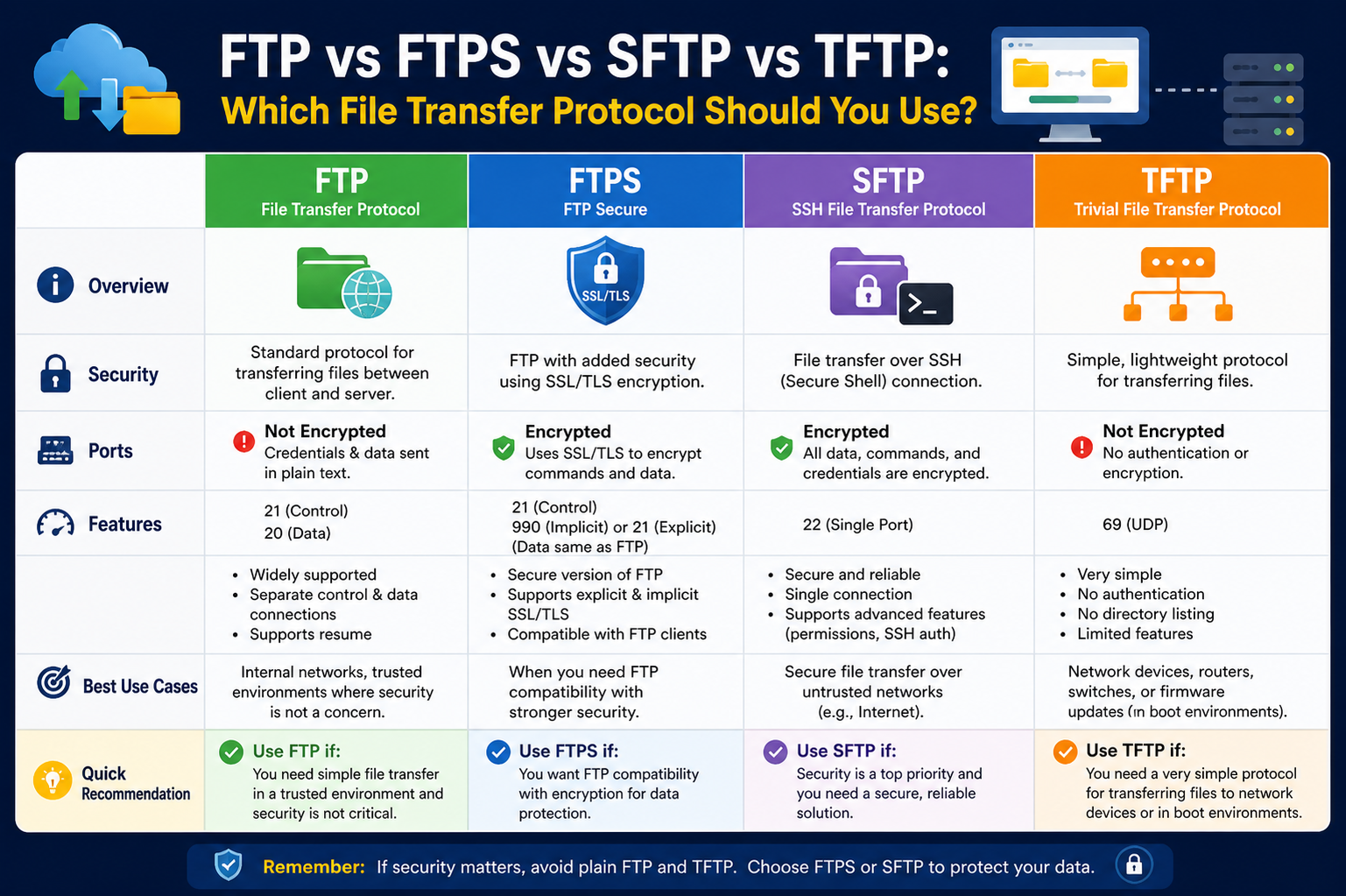
File transfer protocols play a critical role in how data is exchanged between systems across networks. Although FTP, FTPS, SFTP, and TFTP are often grouped together, they differ significantly in architecture, security, performance, and use cases. Understanding these differences is essential for choosing the right protocol in real-world environments where reliability, speed, and data protection all matter.
Understanding the Role of File Transfer Protocols
File transfer protocols are designed to enable communication between a client and a server for sending and receiving files. These protocols define how data is formatted, transmitted, and received across a network. Some focus on simplicity and speed, while others prioritize encryption and secure communication. Over time, the need for secure data exchange has increased significantly, leading to the development of more advanced protocols beyond the original FTP standard.
Each protocol serves a specific purpose. Some are designed for general-purpose file sharing, while others are optimized for secure environments or low-level network device communication. Choosing the wrong protocol can lead to performance issues or security risks, especially in enterprise or production systems.
FTP (File Transfer Protocol) in Detail
FTP is one of the earliest and most widely recognized file transfer methods. It operates on a client-server model and uses separate channels for commands and data transfer. Its simplicity made it extremely popular in early networking environments where security was not a major concern.
However, FTP transmits all data in plain text. This includes usernames, passwords, and file contents, making it highly vulnerable to interception and unauthorized access. In modern environments, this is a major drawback. Despite this, FTP is still used in isolated or internal systems where security risks are minimal or controlled by other layers such as private networks.
FTP is also relatively fast because it lacks encryption overhead. This makes it suitable for non-sensitive data transfers where performance is prioritized over confidentiality. However, due to its lack of built-in security, it has largely been replaced or upgraded in most professional environments.
FTPS (FTP Secure) and Its Enhanced Protection
FTPS is essentially an extension of FTP that adds support for encryption through SSL or TLS protocols. This means that data, including authentication credentials and file contents, is encrypted during transmission. This significantly reduces the risk of interception or tampering.
FTPS can operate in two modes: implicit and explicit. In implicit mode, encryption is established immediately upon connection, while in explicit mode, the client requests security before proceeding. This flexibility allows FTPS to be used in environments that require backward compatibility with traditional FTP systems while still enforcing security.
One of the strengths of FTPS is that it maintains the structure of FTP, making it easier for organizations to upgrade existing systems without completely changing infrastructure. However, it can be more complex to configure, especially when firewalls and multiple ports are involved. This complexity sometimes leads organizations to consider alternative secure protocols.
FTPS is commonly used in industries that require compliance with data protection standards but still rely on legacy FTP infrastructure. It offers a balance between security and compatibility, though it is not as streamlined as newer protocols.
SFTP (SSH File Transfer Protocol) and Modern Secure Transfers
SFTP is often confused with FTPS, but it is fundamentally different. It is not an extension of FTP but a completely separate protocol built on top of SSH (Secure Shell). This means it uses a single secure connection for both commands and data, simplifying communication and improving security.
One of the major advantages of SFTP is that everything transmitted between client and server is encrypted by default. This includes authentication credentials, commands, and file data. It also supports key-based authentication, which eliminates the need for password transmission entirely and enhances security further.
SFTP is widely used in modern IT infrastructure, cloud environments, and enterprise systems. It is particularly favored in situations where secure automation and remote file management are required. Since it operates over a single port, it is also easier to manage through firewalls compared to FTPS.
Another important aspect of SFTP is its reliability in unstable network conditions. It supports resuming interrupted transfers, directory listings, and file permissions, making it more versatile than basic FTP.
In today’s security-focused environments, SFTP is often the default choice for secure file transfers due to its simplicity, encryption strength, and ease of deployment.
TFTP (Trivial File Transfer Protocol) and Its Lightweight Design
TFTP is a highly simplified version of FTP designed for minimal overhead and fast execution. Unlike other file transfer protocols, it does not include authentication or encryption. This makes it extremely lightweight but also insecure for general use.
TFTP operates using a very basic request-and-response model. Because it lacks advanced features, it is typically used in controlled environments where security is not a concern or is handled at a different layer.
Its most common use cases include network device configuration, firmware updates, and system boot operations over a network. For example, routers and switches often use TFTP to load configuration files or firmware during startup.
The simplicity of TFTP allows it to function efficiently in environments where resources are limited. However, its lack of security and minimal functionality make it unsuitable for general file sharing or sensitive data transfer.
Security Differences Between FTP, FTPS, SFTP, and TFTP
Security is one of the most important factors when choosing a file transfer protocol. FTP and TFTP do not provide encryption, making them vulnerable to interception. FTPS improves security by adding SSL/TLS encryption, while SFTP provides full encryption through SSH by default.
In modern environments, encrypted protocols are essential because data is often transmitted over public or shared networks. Without encryption, sensitive information such as login credentials and business data can be easily exposed.
SFTP is generally considered the most secure option due to its strong encryption and simplified connection model. FTPS also provides strong security but requires more complex configuration. FTP and TFTP are typically restricted to internal or non-sensitive environments.
Performance and Efficiency Considerations
Performance varies depending on the protocol used. FTP and TFTP are generally faster in raw speed because they lack encryption overhead. However, this speed comes at the cost of security.
FTPS introduces some performance overhead due to encryption and decryption processes, especially during large file transfers. SFTP also involves encryption overhead but is optimized for secure communication over a single connection, which can make it more efficient in certain network conditions.
In real-world applications, the difference in performance is often negligible compared to the importance of security and reliability. As a result, most organizations prioritize secure protocols even if they are slightly slower.
Ease of Configuration and Maintenance
FTP is relatively simple to set up but requires additional security measures to be safe. FTPS can be more complex due to certificate management and firewall configuration. SFTP is often easier to manage because it uses a single port and integrates with SSH-based authentication systems.
TFTP is simple to configure but is only suitable for very specific use cases. Its lack of authentication means it should only be used in trusted, isolated environments.
From an administrative perspective, SFTP is often preferred because it reduces configuration complexity while maintaining strong security.
Common Use Cases in Real-World Environments
Different protocols are used in different industries depending on requirements. FTP may still be found in legacy systems or internal networks. FTPS is used in organizations that require compliance with data protection regulations but still rely on FTP infrastructure.
SFTP is widely used in cloud services, software development pipelines, secure file sharing systems, and remote server management. It is the most common choice in modern IT environments.
TFTP is primarily used in networking hardware and system recovery scenarios where speed and simplicity are more important than security.
How to Choose the Right Protocol
Selecting the right file transfer protocol depends on several factors including security requirements, system compatibility, performance expectations, and administrative complexity.
If security is a priority, SFTP is usually the best choice. If compatibility with existing FTP systems is required, FTPS can be a good transitional solution. For simple, non-sensitive transfers in controlled environments, FTP may still be acceptable. For specialized networking tasks, TFTP remains useful due to its lightweight design.
In most modern scenarios, SFTP is the recommended standard because it provides a balance of security, efficiency, and ease of use.
In the first part, we covered the basic working principles, strengths, and limitations of FTP, FTPS, SFTP, and TFTP. To fully understand which protocol fits best in real-world systems, it is also important to go deeper into how they behave in different environments, how they are implemented at a technical level, and what practical challenges appear during deployment and maintenance.
Technical Architecture Differences Between Protocols
Although all four protocols are used for file transfer, their underlying architecture is significantly different. FTP and FTPS are built on a dual-channel system where one channel handles commands and another handles data transfer. This separation improves functionality but also introduces complexity in firewall configuration and connection management.
FTP operates using a control connection and a data connection. The control connection stays active during the session, while the data connection opens and closes as needed for file transfers. FTPS follows the same structure but adds encryption layers on top using SSL or TLS. This means both channels must be secured, which increases configuration complexity.
SFTP, on the other hand, uses a single encrypted channel over SSH. This simplifies architecture significantly. Instead of managing multiple connections, everything flows through one secure tunnel. This design reduces firewall issues and improves consistency in data transmission.
TFTP uses a minimal request-response architecture. It does not maintain persistent connections like FTP or SFTP. Instead, it sends small packets and waits for acknowledgment before continuing. This makes it extremely lightweight but also limits functionality and reliability in unstable networks.
Port Usage and Network Behavior
Each protocol uses different network ports, which affects how easily they can be deployed in secure environments.
FTP typically uses port 21 for commands and additional dynamic ports for data transfer. This dynamic nature often creates issues with firewalls and NAT configurations.
FTPS also uses port 21 for explicit mode but may require additional ports for encrypted data channels. In implicit mode, it commonly uses port 990. The need for multiple ports makes it more challenging in tightly controlled network environments.
SFTP uses a single port, usually port 22, which is also used by SSH. This simplicity makes it much easier to configure in firewalled environments and is one of the reasons it is widely preferred in modern systems.
TFTP uses port 69 and operates using UDP instead of TCP. This makes it faster in simple tasks but less reliable because UDP does not guarantee delivery or ordering of packets.
Security Model and Encryption Depth
Security is one of the most important differentiators among these protocols.
FTP provides no encryption at all. Everything is transmitted in plain text, making it highly vulnerable to packet sniffing, man-in-the-middle attacks, and credential theft. In modern networks, FTP is considered unsafe unless used inside isolated environments.
FTPS improves security by adding SSL/TLS encryption. This ensures that both authentication and data transfer are protected. However, certificate management becomes an important responsibility. Expired or misconfigured certificates can cause connection failures.
SFTP provides strong security by default because it is built on SSH. It uses encryption for the entire session, including authentication, commands, and data. It also supports key-based authentication, which is significantly more secure than password-based login.
TFTP provides no security features at all. There is no authentication, encryption, or user verification. It is assumed to operate in trusted local networks where security is handled externally.
Performance and Scalability Considerations
Performance is influenced by encryption overhead, connection type, and protocol efficiency.
FTP offers high raw speed because it does not encrypt data. However, its performance advantage is often irrelevant in modern environments where security is mandatory.
FTPS introduces encryption overhead, which can slightly reduce performance during large file transfers. The impact depends on CPU capacity and encryption strength.
SFTP also includes encryption overhead but is optimized for stable performance over long sessions. Its single-channel design reduces connection overhead, making it efficient in many real-world scenarios.
TFTP is extremely fast for small tasks due to its lightweight nature. However, it is not suitable for large-scale or critical file transfers because it lacks reliability features such as resuming transfers or advanced error handling.
Reliability and Error Handling Mechanisms
Reliability plays a major role in enterprise environments.
FTP provides basic error handling but does not support advanced recovery mechanisms. If a transfer is interrupted, it often needs to be restarted manually.
FTPS improves reliability slightly by securing communication but still relies on FTP’s underlying structure for transfer handling.
SFTP offers strong reliability features, including file resumption, directory operations, and consistent session management. It handles interruptions more gracefully compared to FTP-based systems.
TFTP has very limited reliability. It uses a simple acknowledgment system, and packet loss can disrupt transfers. Because of this, it is only used in controlled or local environments.
Use in Modern Cloud and Enterprise Systems
Modern IT systems increasingly rely on automation, cloud infrastructure, and remote access. This has significantly changed how file transfer protocols are used.
FTP is rarely used in cloud environments due to its lack of security. When it is used, it is typically inside isolated private networks.
FTPS is still used in some enterprise systems that have legacy FTP infrastructure but require compliance with security standards. It is often found in industries with strict regulatory requirements.
SFTP has become the dominant protocol in cloud computing, DevOps pipelines, and remote server management. It integrates well with automation tools, scripting environments, and secure authentication systems.
TFTP remains relevant in networking hardware environments, especially for booting devices, firmware updates, and system recovery processes.
Common Misconfigurations and Operational Issues
Each protocol comes with its own set of operational challenges.
FTP often fails in modern networks due to firewall restrictions and NAT traversal issues. Its use of multiple dynamic ports makes it difficult to manage.
FTPS can suffer from certificate-related issues, including expired certificates, mismatched domain names, or incorrect trust chains. These issues often lead to failed connections.
SFTP issues are usually related to SSH configuration, such as incorrect key permissions or authentication failures. However, these are generally easier to troubleshoot compared to FTP-based problems.
TFTP issues are often related to packet loss, network instability, or incorrect server configuration. Because it lacks authentication, troubleshooting is usually simpler but more limited.
Migration from FTP to Secure Protocols
Many organizations still using FTP eventually migrate to FTPS or SFTP due to security requirements.
Migration to FTPS is often easier when existing FTP infrastructure is deeply integrated into systems. It allows gradual upgrades without completely redesigning workflows.
Migration to SFTP usually requires more changes but results in a more secure and modern system. It often involves updating scripts, authentication methods, and server configurations.
During migration, organizations typically evaluate factors such as compliance requirements, system compatibility, and long-term scalability.
Best Practices for Secure File Transfers
To ensure safe and efficient file transfers, several best practices are commonly followed.
Using encrypted protocols like SFTP or FTPS is essential for protecting sensitive data. Password-based authentication should be replaced with key-based authentication wherever possible.
Regular monitoring of file transfer logs helps detect unauthorized access or unusual activity. Proper firewall configuration ensures that only necessary ports are open.
In addition, limiting user permissions reduces the risk of accidental or malicious data exposure. Keeping server software updated is also critical for maintaining security.
Real-World Decision Making Between Protocols
In practice, the choice of protocol is rarely theoretical. It depends on infrastructure, compliance requirements, and operational constraints.
Organizations with legacy systems may continue using FTP or FTPS due to compatibility needs. However, new systems are increasingly designed around SFTP because it offers better security and easier maintenance.
TFTP remains specialized and is not part of general file transfer strategy in most organizations. Its role is limited but still important in networking and embedded systems.
Comparative Understanding
When comparing all four protocols, a clear pattern emerges. FTP represents simplicity without security. FTPS represents enhanced security built on legacy systems. SFTP represents modern secure design with strong encryption and simplicity. TFTP represents minimal functionality for specialized technical tasks.
The evolution of these protocols reflects the broader shift in computing from convenience-focused systems to security-first architectures. Today, secure protocols are not optional but a requirement in most environments.
Ultimately, understanding these protocols in depth allows better decision-making when designing systems, managing infrastructure, or implementing secure file transfer solutions.
Advanced Security Considerations in Modern Environments
Security in file transfer is no longer just about encryption. It now includes identity verification, access control, auditing, and compliance enforcement. While earlier comparisons focused on whether data is encrypted or not, modern systems require a deeper security model.
FTP provides no security layers beyond basic authentication. This means it fails to meet almost all modern security requirements. Even when used in internal networks, it relies heavily on external security measures such as VPNs or isolated subnets.
FTPS improves the situation by introducing SSL/TLS encryption, but security still depends on proper certificate management. If certificates are not rotated or validated correctly, the entire system becomes vulnerable. This makes FTPS secure in theory but operationally dependent on disciplined administration.
SFTP provides a stronger security foundation because it is built on SSH. SSH itself includes multiple layers of security, including encrypted transport, public key authentication, and session integrity checks. This reduces dependency on external certificate authorities and simplifies secure deployment.
TFTP does not provide any security mechanisms at all. In modern contexts, its usage assumes a physically or logically secure environment. Because of this limitation, it is rarely considered in security-sensitive architectures.
Authentication Methods and Access Control
Authentication plays a critical role in determining how users and systems access file transfer services.
FTP relies on simple username and password authentication. These credentials are transmitted in plain text, making them highly vulnerable to interception. There is no built-in support for advanced authentication methods.
FTPS supports traditional authentication but secures it using encryption. However, it does not fundamentally change the authentication model. It still depends on credentials and optionally certificates.
SFTP provides much more flexibility. It supports password authentication, public key authentication, and even integration with centralized authentication systems. Public key authentication is particularly important because it eliminates password transmission entirely and significantly reduces attack surfaces.
TFTP does not include authentication at all. Any client that can reach the server can request files. This makes it unsuitable for environments where access control is required.
Automation and Scripting Capabilities
Modern IT environments rely heavily on automation. File transfers are often embedded within scripts, deployment pipelines, and scheduled tasks.
FTP can be automated using scripts, but security limitations restrict its use. Credentials must often be stored in plain text or insecure configuration files, which introduces risk.
FTPS can also be automated, but certificate handling adds complexity. Scripts must account for certificate validation, expiration, and trust chains.
SFTP is highly automation-friendly. It integrates well with scripting languages, DevOps pipelines, and configuration management tools. Because it uses SSH keys, it is easier to automate securely without embedding sensitive credentials.
TFTP is simple enough to be automated in network device environments, especially for firmware deployment or boot processes. However, its functionality is too limited for broader automation use cases.
Protocol Behavior in Enterprise Architecture
In enterprise systems, file transfer protocols are rarely used in isolation. They are part of larger architectures involving databases, application servers, storage systems, and APIs.
FTP is typically found in legacy systems where older applications still depend on it. These systems often require additional security layers around them.
FTPS is used in transitional architectures where organizations are moving from legacy FTP systems to more secure environments but cannot immediately replace existing workflows.
SFTP is commonly integrated into modern architectures. It works well with microservices, cloud storage gateways, and automated deployment systems. Its compatibility with SSH makes it suitable for distributed systems.
TFTP is mostly isolated within network infrastructure layers. It is used by routers, switches, and embedded systems rather than application-level architectures.
Firewall, NAT, and Network Traversal Challenges
One of the most practical challenges in file transfer systems is network traversal.
FTP is notoriously difficult to manage through firewalls because it uses multiple dynamic ports. This often requires special firewall configurations or passive mode setups.
FTPS inherits the same challenges as FTP, with additional complexity introduced by encrypted channels. Firewalls must understand and allow secure traffic while managing multiple connection paths.
SFTP is significantly easier to manage because it uses a single port. This reduces firewall complexity and makes it ideal for cloud and hybrid environments where network boundaries are strict.
TFTP uses UDP, which can be problematic for firewalls because UDP is connectionless. However, because TFTP is usually used in controlled environments, this limitation is often acceptable.
Performance Optimization in Real Systems
Performance tuning depends on understanding how each protocol handles data.
FTP performs well in raw throughput scenarios but lacks resilience. It is most effective in stable, trusted environments.
FTPS introduces encryption overhead, which can impact performance during large-scale transfers. However, modern hardware acceleration reduces this impact significantly.
SFTP balances performance and security. While encryption adds overhead, its single-channel design reduces connection complexity and improves consistency in long-running transfers.
TFTP performs well in small, controlled transfers but cannot scale effectively. It is optimized for simplicity rather than throughput or reliability.
Logging, Monitoring, and Auditing Capabilities
In enterprise systems, visibility into file transfers is essential for security and compliance.
FTP provides basic logging but lacks detailed auditing capabilities. This makes it unsuitable for regulated environments.
FTPS improves security but still depends on server-side logging mechanisms for auditing. Logs must be carefully configured to ensure compliance.
SFTP provides detailed session logging, including authentication attempts, file operations, and session durations. This makes it ideal for audit-heavy environments.
TFTP provides minimal logging capabilities. It is not designed for compliance or auditing purposes.
Compliance and Regulatory Requirements
Many industries require strict compliance with data protection standards.
FTP generally fails to meet compliance requirements due to lack of encryption and auditing.
FTPS can meet compliance requirements if properly configured with strong encryption and secure certificate management. It is often used in environments requiring adherence to regulatory frameworks.
SFTP is widely accepted in compliance-driven industries because of its strong encryption, authentication options, and audit capabilities. It is commonly used in financial services, healthcare systems, and enterprise IT.
TFTP is not suitable for compliance environments due to its lack of security and authentication.
Common Misconceptions About File Transfer Protocols
One common misconception is that FTPS and SFTP are similar because both are “secure FTP.” In reality, they are fundamentally different in architecture and design.
Another misconception is that FTP is completely obsolete. While it is insecure for public or sensitive networks, it still exists in isolated internal systems.
It is also often assumed that SFTP is slower than FTP. While encryption introduces overhead, modern systems minimize this difference, and the security benefits outweigh minor performance differences.
TFTP is sometimes misunderstood as a general-purpose lightweight FTP, but in reality, it is highly specialized and not intended for general file sharing.
Future of File Transfer Technologies
The role of traditional file transfer protocols is gradually changing. Modern systems are increasingly shifting toward API-based data exchange, cloud storage synchronization, and managed file transfer platforms.
While FTP, FTPS, SFTP, and TFTP still remain in use, especially in legacy and infrastructure systems, newer technologies are reducing dependency on traditional file transfer methods.
Secure APIs and HTTPS-based transfers are becoming more common because they integrate directly with web services and cloud applications. However, SFTP remains widely used due to its simplicity and strong security model.
TFTP will likely continue to exist in networking hardware environments where its simplicity is still valuable.
Choosing the Right Protocol in Real Scenarios
Selecting the correct protocol depends on balancing multiple factors such as security, performance, compatibility, and operational complexity.
In highly secure environments, SFTP is generally the preferred choice due to its encryption, authentication flexibility, and ease of firewall configuration.
In legacy environments where FTP is deeply integrated, FTPS provides a transitional path toward better security.
For simple internal transfers where security is not a concern, FTP may still be used, although it is increasingly discouraged.
For specialized network operations such as firmware updates and boot processes, TFTP remains relevant due to its minimal overhead.
Strategic Perspective
File transfer protocols are not just technical tools; they are part of a broader infrastructure strategy. Choosing the right one affects security posture, system reliability, operational efficiency, and long-term scalability.
FTP represents the foundation of file transfer technology but lacks modern security. FTPS improves upon it but retains structural complexity. SFTP represents the modern standard for secure file transfer. TFTP remains a specialized tool for network-level operations.
Understanding these distinctions allows better architectural decisions, stronger security implementation, and more efficient system design in both traditional and modern IT environments.
Scalability in Large-Scale Systems
Scalability is a key factor when selecting a file transfer protocol for growing systems. In environments where thousands of transfers occur daily, even small inefficiencies can become significant bottlenecks.
FTP can handle moderate workloads but does not scale efficiently in modern distributed systems. Its reliance on multiple ports and unencrypted communication creates operational overhead that increases with system size.
FTPS scales better in secure environments compared to FTP, but certificate management and multi-port communication can become increasingly complex as systems grow. Large-scale deployments often require additional tools to manage certificates and ensure consistent encryption policies across servers.
SFTP is generally the most scalable option among the four protocols. Its single-port design simplifies network configuration, and its reliance on SSH makes it easier to integrate into automated scaling environments such as cloud infrastructure. This simplicity allows organizations to expand file transfer capabilities without significantly increasing administrative burden.
TFTP does not scale for enterprise-level file transfer workloads. It is designed for small, controlled transfers and cannot handle large volumes or complex workflows.
Integration with Modern Development and DevOps Pipelines
Modern software development relies heavily on automation pipelines that include build, test, and deployment stages. File transfer protocols play a role in moving artifacts, configuration files, and deployment packages.
FTP is rarely used in modern DevOps workflows due to its lack of security and weak integration capabilities. If used, it is typically restricted to legacy deployment systems.
FTPS can be integrated into pipelines, but its configuration complexity and certificate requirements can slow down automation processes. This makes it less ideal for rapid deployment environments.
SFTP integrates very well with DevOps practices. It works seamlessly with CI/CD pipelines, configuration management tools, and automation scripts. Because authentication can be handled through SSH keys, it eliminates the need for hardcoded credentials, improving both security and maintainability.
TFTP is not used in software development pipelines. Its role is limited to network booting and device configuration tasks rather than application deployment.
Maintenance and Long-Term Operational Costs
The long-term cost of maintaining a file transfer system includes server management, security updates, troubleshooting, and infrastructure support.
FTP has relatively low initial setup complexity, but long-term maintenance costs can be high due to security risks and the need for additional protective layers such as VPNs or network isolation.
FTPS introduces higher maintenance overhead due to certificate lifecycle management. Organizations must regularly update, renew, and validate certificates to ensure uninterrupted secure communication.
SFTP has lower long-term maintenance costs compared to FTPS and FTP. Once SSH keys and access controls are properly configured, ongoing management is relatively simple. This makes it a cost-effective solution for long-term deployments.
TFTP has minimal maintenance requirements, but its usage is limited to very specific scenarios. While easy to maintain, its limited functionality restricts its applicability.
Error Recovery and Fault Tolerance
Fault tolerance determines how well a protocol handles interruptions such as network failures or system crashes.
FTP provides basic error reporting but limited recovery options. Interrupted transfers often need to be restarted from the beginning.
FTPS inherits FTP’s limitations in fault tolerance but adds secure communication. Recovery still depends on the underlying FTP mechanisms.
SFTP offers strong fault tolerance capabilities. It supports resuming interrupted transfers, maintaining session integrity, and handling partial file recovery more effectively than FTP-based protocols.
TFTP has very limited error recovery. Packet loss can result in failed transfers, and recovery mechanisms are minimal due to its simplified design.
Data Integrity and Transfer Reliability
Data integrity ensures that files are transferred accurately without corruption.
FTP does not inherently guarantee strong data integrity, although basic checks exist.
FTPS improves integrity through encryption, which helps prevent tampering during transmission.
SFTP provides strong data integrity guarantees due to its encrypted and verified communication channel. It ensures that data is not altered during transfer.
TFTP provides minimal integrity assurance. While it uses acknowledgment-based transmission, it is not designed for high reliability or data verification.
Administrative Control and User Management
Managing users and permissions is essential in multi-user environments.
FTP offers basic user management but lacks advanced access control mechanisms.
FTPS improves security but still relies on traditional FTP user models, which can become difficult to manage at scale.
SFTP integrates with SSH-based user management systems, allowing granular control over permissions, directories, and authentication methods. It can also integrate with centralized identity systems, making it suitable for enterprise environments.
TFTP does not support user management. Any client with network access can retrieve files.
Protocol Efficiency in Virtualized and Cloud Environments
Virtualization and cloud computing have changed how file transfer systems operate.
FTP performs poorly in highly dynamic environments due to its multi-port design and security limitations.
FTPS can function in cloud environments but often requires additional configuration for certificate handling and firewall rules.
SFTP is highly efficient in cloud and virtualized environments. It works well with containerized systems, virtual machines, and distributed storage architectures.
TFTP is mostly irrelevant in cloud environments, except in specialized networking or boot scenarios.
Cross-Platform Compatibility
Compatibility across different operating systems and platforms is another important consideration.
FTP is widely supported across all systems but is increasingly restricted due to security concerns.
FTPS is supported on most platforms but may require additional configuration depending on the system.
SFTP is universally supported across modern operating systems, including Linux, Windows, and macOS, making it highly versatile.
TFTP is supported mainly in networking hardware and embedded systems rather than general computing platforms.
Real-World Industry Applications
Different industries use these protocols based on their operational needs.
FTP is still found in older internal systems and legacy applications that have not been updated.
FTPS is commonly used in industries that require compliance but still depend on FTP-based infrastructure.
SFTP is widely used in finance, healthcare, software development, cloud computing, and enterprise IT due to its strong security and flexibility.
TFTP is used in networking, telecommunications, and embedded systems for firmware deployment and recovery tasks.
Future Relevance of Each Protocol
The future of file transfer technologies is moving toward secure, automated, and API-driven systems. However, traditional protocols still play a role in specific contexts.
FTP is gradually declining but will likely remain in legacy systems for some time.
FTPS will continue to exist in transitional environments where organizations are upgrading security without redesigning systems.
SFTP is expected to remain the dominant file transfer protocol in secure environments due to its balance of simplicity and security.
TFTP will continue to exist in specialized networking and embedded system roles but is unlikely to expand beyond those areas.
Strategic Final Understanding
When evaluating FTP, FTPS, SFTP, and TFTP from a strategic perspective, it becomes clear that each protocol represents a different stage in the evolution of file transfer technology.
FTP represents the original foundation, focusing on simplicity over security. FTPS represents an upgrade path for legacy systems requiring encryption. SFTP represents the modern standard combining security, simplicity, and scalability. TFTP represents a highly specialized tool designed for minimal, controlled tasks.
In modern system design, SFTP is generally the most balanced and widely adopted solution. However, the other protocols still hold relevance depending on specific technical and operational requirements.
Understanding these protocols in depth allows for better infrastructure planning, stronger security implementation, and more efficient system architecture decisions in both traditional and modern computing environments.
Conclusion
Choosing between FTP, FTPS, SFTP, and TFTP ultimately comes down to balancing security, performance, and operational needs. Each protocol was designed with a specific purpose, and none of them is universally “best” for every situation.
FTP remains the simplest option, but its lack of encryption makes it unsuitable for modern security standards. FTPS improves on FTP by adding encryption, making it a better choice for legacy systems that still rely on FTP infrastructure but require secure communication. However, it introduces additional complexity in configuration and certificate management.
SFTP stands out as the most practical and widely adopted solution in modern environments. Its use of SSH for secure communication, single-port design, and strong authentication methods make it reliable, scalable, and easier to manage. For most current use cases—especially in cloud systems, enterprise networks, and automated workflows—SFTP is the preferred standard.
TFTP, while extremely lightweight and fast, is highly limited in functionality and offers no security. It is only suitable for very specific tasks such as network device configuration and firmware transfers in controlled environments.
In summary, FTP and TFTP are largely legacy or specialized tools, FTPS serves as a transitional secure option, and SFTP represents the modern, secure, and flexible approach to file transfers. The right choice depends entirely on the environment, but in most cases today, secure and scalable solutions like SFTP provide the most reliable long-term value.