Cryptography is the foundation of secure communication in modern digital systems. It ensures that sensitive information such as passwords, financial data, and personal messages remains protected from unauthorized access. Two of the most important cryptographic methods used today are symmetric encryption and asymmetric encryption. Both serve the same purpose of securing data, but they work in very different ways and are used in different situations depending on the requirements of speed, security, and scalability. Understanding how each method functions and where it is best applied is essential for building secure systems.
Understanding the Concept of Symmetric Encryption
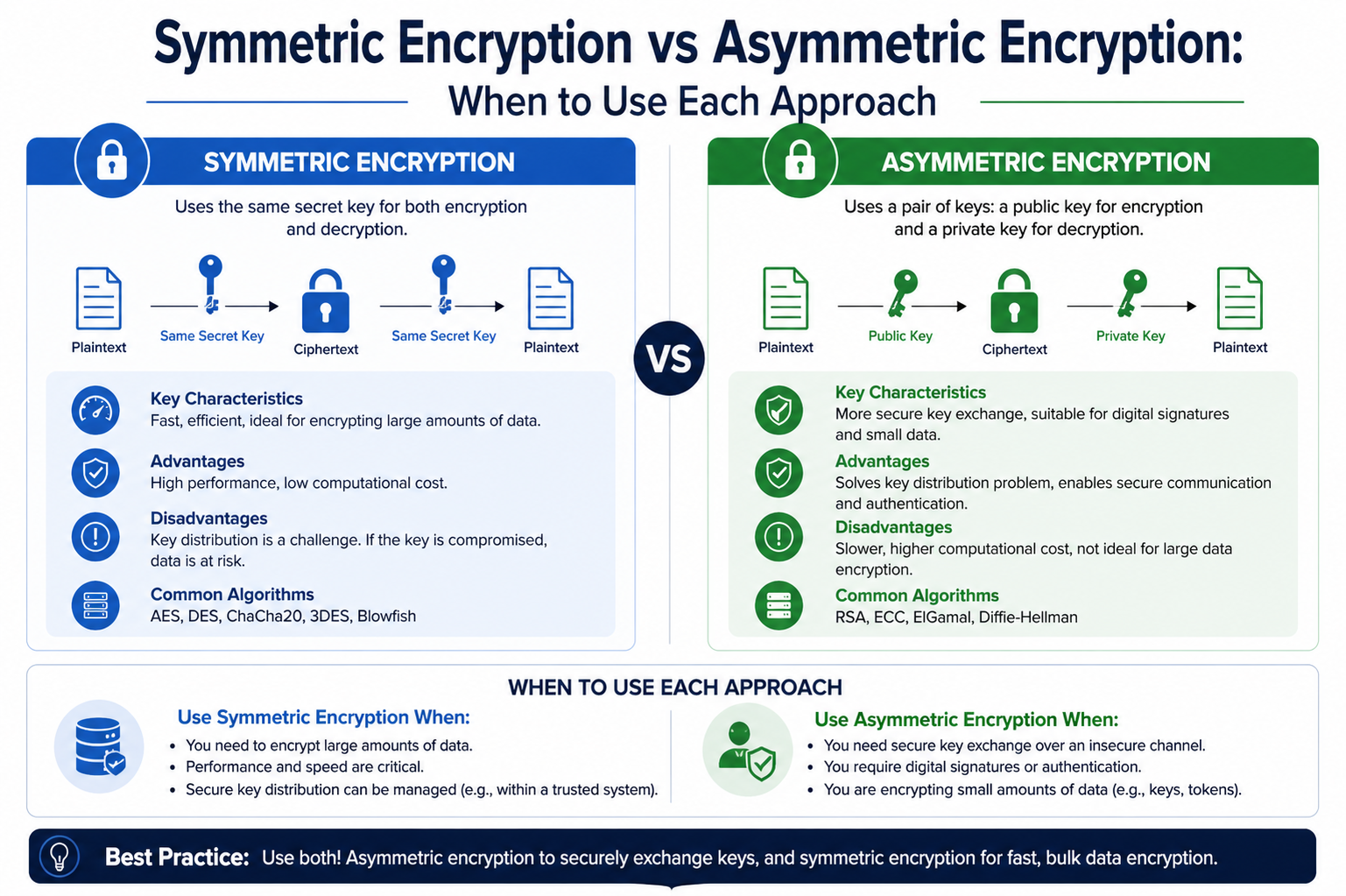
Symmetric encryption is one of the oldest and most straightforward forms of encryption. It uses a single secret key to both encrypt and decrypt data. This means that the same key must be shared between the sender and the receiver before communication begins. Once both parties have the key, encrypted messages can be sent securely and decoded only by those who possess the same key.
The simplicity of symmetric encryption makes it highly efficient. It requires less computational power compared to other encryption methods, which allows it to process large amounts of data quickly. Because of this efficiency, it is widely used in systems where performance is critical, such as encrypting files on a device, securing database storage, and protecting data during internal communication within trusted networks.
However, the main challenge lies in key distribution. Since both parties need the same secret key, it must be shared in a secure way before communication starts. If an attacker intercepts the key during transmission, the entire security system is compromised. This limitation is one of the key weaknesses of symmetric encryption.
Strengths and Limitations of Symmetric Encryption
Symmetric encryption has several advantages that make it highly useful in practical applications. Its primary strength is speed. Because it uses simple mathematical operations, it can encrypt and decrypt data much faster than more complex encryption systems. This makes it ideal for handling large datasets or real-time data processing.
Another advantage is its low computational cost. It does not require heavy processing power, making it suitable for devices with limited resources such as mobile phones or embedded systems. It is also relatively easy to implement compared to more advanced encryption techniques.
Despite these strengths, symmetric encryption has significant limitations. The biggest issue is secure key exchange. If the secret key is exposed, anyone with that key can access the encrypted data. Additionally, in systems with many users, managing and distributing keys becomes increasingly complex. Each pair of users may require a unique key, which can quickly become difficult to maintain in large networks.
Understanding the Concept of Asymmetric Encryption
Asymmetric encryption, also known as public-key cryptography, was developed to solve the key distribution problem found in symmetric encryption. Instead of using a single key, it uses a pair of mathematically linked keys: a public key and a private key.
The public key is openly shared and can be distributed to anyone. It is used to encrypt data. Once data is encrypted with the public key, it can only be decrypted using the corresponding private key, which is kept secret by the owner. This means that even if the public key is widely available, it cannot be used to decrypt the information.
This system eliminates the need to share secret keys in advance, making it much more secure for communication over untrusted networks such as the internet. It is widely used in secure email communication, digital signatures, and establishing secure connections between clients and servers.
Strengths and Limitations of Asymmetric Encryption
The main strength of asymmetric encryption is its ability to provide secure communication without requiring both parties to share a secret key beforehand. This makes it highly suitable for environments where secure key exchange is difficult or impossible.
It also supports digital signatures, which help verify the authenticity and integrity of messages. This ensures that data has not been altered and confirms the identity of the sender.
However, asymmetric encryption is significantly slower than symmetric encryption. It requires complex mathematical operations, which makes it computationally expensive. As a result, it is not practical for encrypting large volumes of data. Instead, it is usually used for small pieces of data, such as encryption keys or authentication information.
Another limitation is that it requires more processing power, which can impact performance in systems that require high-speed communication.
Comparing Both Encryption Methods in Practice
When comparing symmetric and asymmetric encryption, the differences become clear in terms of speed, security approach, and use cases. Symmetric encryption focuses on efficiency and speed, making it ideal for handling large amounts of data. In contrast, asymmetric encryption focuses on secure communication and identity verification, especially in situations where no prior trust exists between parties.
Symmetric encryption requires both parties to share the same secret key, which creates a challenge in secure key distribution. Asymmetric encryption solves this problem by using a public-private key pair, eliminating the need to share secret keys directly.
However, because of its computational intensity, asymmetric encryption is not used for bulk data encryption. Instead, it is often used as a supporting mechanism to establish secure communication channels.
Real-World Importance of Encryption
Encryption plays a critical role in modern digital systems. Every time a user logs into a website, sends a message, or makes an online transaction, encryption is working in the background to protect data. Without encryption, sensitive information would be vulnerable to interception and misuse.
Symmetric encryption is commonly used in scenarios where speed is essential, such as securing data stored on devices or transferring large files. Asymmetric encryption is used when establishing secure connections over the internet, such as when accessing secure websites or verifying digital identities.
Both methods are essential, and neither can fully replace the other. Instead, they complement each other to provide a complete security solution.
Hybrid Encryption Systems in Real-World Applications
In practical cybersecurity systems, symmetric and asymmetric encryption are rarely used in isolation. Instead, modern systems combine both approaches into what is known as hybrid encryption. This design takes advantage of the strengths of each method while reducing their weaknesses. Asymmetric encryption is used first to securely exchange a symmetric key between two parties. Once this secure exchange is completed, symmetric encryption takes over for the actual data transmission.
This approach is widely used because it solves two major problems at the same time. It ensures secure key distribution through asymmetric encryption while maintaining high-speed data processing through symmetric encryption. Without this combination, secure communication over the internet would either be too slow or too risky to implement at scale.
Hybrid encryption is the foundation of most secure communication protocols used today. It allows systems to establish secure sessions even between parties that have never interacted before, while still maintaining efficiency during ongoing communication.
Role of Encryption in Secure Internet Communication
Whenever a user accesses a secure website or sends sensitive data online, both encryption methods work together behind the scenes. The connection begins with asymmetric encryption, which is used to authenticate the server and securely exchange a session key. After this handshake process is completed, symmetric encryption is used for all further communication during that session.
This layered approach ensures that sensitive data such as login credentials, credit card numbers, and personal information remains protected from interception. Even if an attacker manages to observe the communication, they cannot decrypt the data without access to the session key.
This combination is essential for building trust in digital systems, especially in environments where data passes through multiple networks and servers before reaching its destination.
Common Algorithms Used in Symmetric Encryption
Symmetric encryption relies on several well-known algorithms that define how data is transformed into secure ciphertext. One of the most widely used algorithms is the Advanced Encryption Standard, which is known for its speed and strong security. It is commonly used in government systems, financial applications, and secure file storage.
Other symmetric algorithms include older systems that were once popular but are now considered less secure due to advancements in computing power. Modern implementations focus on algorithms that balance performance and resistance to attacks.
The strength of symmetric encryption depends heavily on the key length and the algorithm used. Longer keys generally provide stronger security but may slightly reduce performance. However, even with this trade-off, symmetric encryption remains extremely efficient compared to asymmetric methods.
Common Algorithms Used in Asymmetric Encryption
Asymmetric encryption relies on more complex mathematical structures. One of the most widely used methods is based on large prime number factorization, which forms the foundation of secure key pairs. Another important approach uses elliptic curve mathematics, which provides similar levels of security with smaller key sizes and improved performance.
These algorithms are designed to make it extremely difficult for attackers to derive the private key even if they have access to the public key. The computational difficulty of reversing these mathematical relationships is what makes asymmetric encryption secure.
However, because of this complexity, asymmetric encryption requires significantly more processing power and is therefore limited to specific tasks such as key exchange and authentication.
Performance Differences and System Efficiency
One of the most important differences between symmetric and asymmetric encryption is performance. Symmetric encryption is optimized for speed and can process large volumes of data quickly. This makes it suitable for environments where real-time processing is required.
Asymmetric encryption, on the other hand, is much slower due to its complex mathematical operations. It is not designed for bulk data encryption but rather for secure key management and identity verification.
In large-scale systems, this difference in performance is critical. Using asymmetric encryption alone for all data would create significant delays and inefficiencies. This is why hybrid systems are preferred in modern architecture, ensuring both security and performance are maintained.
Security Considerations and Potential Risks
While both encryption methods are highly secure when implemented correctly, they are not immune to threats. The security of symmetric encryption depends entirely on the secrecy of the key. If the key is exposed, the entire system becomes vulnerable.
Asymmetric encryption, although more secure in terms of key distribution, can still be vulnerable to certain types of attacks if weak algorithms or insufficient key lengths are used. Additionally, poor implementation or insecure storage of private keys can compromise the system.
Another important risk involves human error. Many security breaches occur not because of weaknesses in encryption algorithms but because of improper key management, weak passwords, or insecure system configurations.
Key Exchange Mechanisms in Secure Systems
Secure communication systems rely on specialized methods to exchange encryption keys safely. In asymmetric encryption systems, a public key is used to encrypt a session key, which is then securely transmitted to the receiver. The receiver uses their private key to decrypt it.
Once both parties have the shared session key, they switch to symmetric encryption for faster communication. This process ensures that even if an attacker intercepts the communication, they cannot access the session key without the private key.
This mechanism is essential for establishing trust in environments where communication occurs over untrusted networks. It allows secure connections to be formed dynamically without requiring prior coordination between users.
Applications in Modern Technology
Encryption is used across nearly every aspect of modern technology. In cloud computing, symmetric encryption is used to protect stored data, while asymmetric encryption secures access and authentication. In mobile communication, both methods work together to protect messages, calls, and data transfers.
Financial systems rely heavily on encryption to protect transactions and prevent fraud. Similarly, secure messaging applications use hybrid encryption to ensure that only intended recipients can read messages.
Even everyday activities such as browsing the internet, using social media, or accessing online banking depend on these encryption systems working seamlessly in the background.
Future Trends in Encryption Technology
As technology continues to evolve, encryption methods are also advancing. One major trend is the development of more efficient algorithms that provide stronger security with lower computational costs. This is especially important as devices become more connected and data volumes continue to increase.
Another emerging area is the development of encryption systems that can resist attacks from future computing technologies. Researchers are actively working on new approaches to ensure long-term data security.
At the same time, hybrid encryption systems are expected to remain the standard for most applications due to their balance of speed and security. As digital systems become more complex, the need for efficient and secure encryption will only continue to grow
Key Management Challenges in Symmetric Encryption
One of the most critical aspects of symmetric encryption is key management. Since the same key is used for both encryption and decryption, maintaining its confidentiality becomes extremely important. In any system where multiple users communicate, each pair of users may require a separate shared key. This quickly increases the complexity of managing keys as the number of participants grows.
In small systems, key distribution can be handled manually or through secure channels. However, in large-scale environments such as enterprise networks or global communication platforms, manual key distribution becomes impractical. Organizations must rely on secure key management systems that generate, distribute, rotate, and revoke keys efficiently.
Another challenge is key rotation. Over time, using the same encryption key increases the risk of exposure. Regularly updating keys helps reduce this risk, but it also introduces additional overhead in terms of synchronization between communicating parties. If key updates are not properly coordinated, communication can break or become insecure.
Despite these challenges, symmetric encryption remains widely used because modern systems have developed strong key management frameworks to handle these issues effectively.
Key Management in Asymmetric Encryption Systems
Asymmetric encryption simplifies key distribution but introduces its own set of management challenges. In this system, the public key is freely distributed, but the private key must be carefully protected at all times. If the private key is compromised, the entire security of the system is broken.
One major concern is ensuring the authenticity of public keys. Since public keys are distributed openly, attackers may attempt to replace a legitimate key with a fake one. To prevent this, systems rely on trusted verification methods that confirm the identity of the key owner.
Another important aspect is certificate-based systems. These systems bind public keys to verified identities, ensuring that users can trust the source of the key they are using. This helps prevent impersonation attacks and builds trust in digital communication systems.
Even though asymmetric encryption reduces the complexity of key sharing, protecting private keys remains a critical responsibility. Secure storage mechanisms, hardware-based security modules, and strict access controls are often used to protect private keys from unauthorized access
Scalability Differences Between Both Methods
Scalability is another important factor when comparing symmetric and asymmetric encryption. Symmetric encryption can become difficult to scale in large systems because each pair of users may require a unique shared key. As the number of users increases, the number of keys required grows rapidly, making management more complex.
Asymmetric encryption scales more efficiently in terms of communication between multiple users because public keys can be shared openly. However, it does not eliminate the need for secure private key management, which still requires strict protection mechanisms.
In large distributed systems, hybrid approaches solve scalability issues by using asymmetric encryption for secure key exchange and symmetric encryption for high-speed communication. This ensures that systems can grow without sacrificing performance or security.
Cryptographic Strength and Attack Resistance
The strength of encryption methods depends on how resistant they are to attacks. Symmetric encryption is generally resistant to brute-force attacks when strong keys are used. The difficulty of guessing the correct key increases exponentially with key length, making modern symmetric encryption extremely secure when properly implemented.
However, symmetric encryption can still be vulnerable to attacks if weak keys are used or if patterns in encrypted data are exploited. Proper implementation and strong key generation are essential to maintaining security.
Asymmetric encryption relies on complex mathematical problems that are computationally difficult to solve. The security of these systems is based on the assumption that certain mathematical operations cannot be reversed efficiently. This makes them highly resistant to direct attacks, although advancements in computing power may pose future challenges.
Both methods are considered secure when used correctly, but their effectiveness depends heavily on implementation quality and system design.
Role of Encryption in Authentication and Digital Identity
Encryption is not only used for securing data but also plays a major role in verifying identity. Asymmetric encryption is especially important in authentication systems because it allows users to prove ownership of a private key without revealing it.
Digital signatures are a key application of this process. They ensure that a message has not been altered and confirm the identity of the sender. This is widely used in software distribution, financial transactions, and secure communication platforms.
Symmetric encryption is less commonly used for identity verification because both parties share the same key, making it difficult to prove unique ownership. However, it is still useful in internal systems where trust has already been established.
Together, both methods support secure authentication systems that help prevent unauthorized access and impersonation.
Efficiency in Real-Time Systems
Real-time systems require fast processing and minimal delay. Symmetric encryption is highly suitable for such environments because it can quickly encrypt and decrypt data with minimal computational overhead. This makes it ideal for applications like video streaming, voice communication, and live data transmission.
Asymmetric encryption, due to its slower processing speed, is not used for continuous data streams. Instead, it is used at the beginning of a session to establish secure communication parameters.
By combining both methods, real-time systems can maintain both speed and security without compromising performance.
Evolution of Encryption Techniques
Encryption technology has evolved significantly over time in response to increasing security demands and computational advancements. Early systems relied heavily on simple symmetric encryption methods, which were sufficient for basic communication needs. However, as digital communication expanded, the limitations of symmetric encryption became more apparent.
The introduction of asymmetric encryption marked a major breakthrough in cryptography. It solved the key distribution problem and enabled secure communication over open networks. Since then, both methods have evolved further to become more efficient, secure, and scalable.
Modern encryption systems are designed to withstand sophisticated attacks while maintaining high performance. Continuous research in cryptography ensures that encryption methods remain effective against emerging threats.
Importance of Proper Implementation
Even the strongest encryption methods can become weak if implemented incorrectly. Many security breaches occur not because of flaws in encryption algorithms but due to poor system design, weak key management, or human error.
Proper implementation involves selecting appropriate key lengths, using secure random number generators, protecting private keys, and ensuring secure communication channels. Regular updates and security audits are also essential to maintaining system integrity.
Organizations must follow best practices to ensure that encryption systems function as intended and provide maximum protection.
Performance Trade-offs in Large-Scale Systems
In large-scale digital systems, performance becomes one of the most important factors when choosing between symmetric and asymmetric encryption. Systems that handle millions of requests per second, such as cloud platforms, messaging applications, and financial networks, cannot rely solely on asymmetric encryption due to its computational cost. Even though it offers strong security advantages, its slow processing speed makes it unsuitable for continuous data encryption at scale.
Symmetric encryption, on the other hand, is designed for speed and efficiency. It can handle high-throughput environments with minimal delay, making it ideal for encrypting data streams, large databases, and persistent storage systems. This performance advantage is the main reason symmetric encryption dominates in backend systems where speed is critical.
However, performance alone is not enough. Systems must also ensure secure key distribution and identity verification, which is where asymmetric encryption plays a supporting role. The combination ensures that systems remain both fast and secure even under heavy load.
Security Layering in Modern Architectures
Modern security systems rarely depend on a single encryption method. Instead, they use multiple layers of security, where symmetric and asymmetric encryption work together in a structured way. This layered approach ensures that even if one layer is compromised, the system remains protected by another.
At the outer layer, asymmetric encryption is used to establish trust, verify identities, and exchange secure keys. Once this trust is established, symmetric encryption takes over to protect the actual data being transmitted. This separation of responsibilities improves both efficiency and security.
This layered architecture is especially important in distributed systems, where data passes through multiple servers, networks, and devices before reaching its destination. Each layer of encryption adds an additional barrier against potential attacks, making unauthorized access significantly more difficult.
Cryptographic Key Lifespan and Rotation Policies
Another important consideration in encryption systems is key lifespan. Encryption keys cannot be used indefinitely because prolonged usage increases the risk of exposure. Both symmetric and asymmetric systems implement key rotation strategies to improve security.
In symmetric encryption systems, keys are often rotated frequently, especially in environments where sensitive data is transmitted. Short-lived session keys are commonly used to limit the impact of any potential key compromise.
In asymmetric systems, key pairs also have defined lifespans. While public keys can be distributed widely, private keys must be carefully rotated and replaced when necessary. Proper key lifecycle management ensures that even if a key is compromised, its usefulness to an attacker is limited.
Effective key rotation strategies are essential for maintaining long-term security in both encryption models.
Impact of Quantum Computing on Encryption
One of the emerging concerns in cryptography is the potential impact of quantum computing. Traditional encryption methods, especially asymmetric encryption, rely on mathematical problems that are difficult for classical computers to solve. However, quantum computers may eventually be able to solve some of these problems much more efficiently.
Asymmetric encryption methods that rely on factoring large numbers or solving discrete logarithm problems could become vulnerable in a post-quantum world. This has led to active research into quantum-resistant algorithms designed to protect data against future computational threats.
Symmetric encryption is also affected, but to a lesser extent. Quantum computing may reduce the effective strength of symmetric keys, but increasing key sizes can help maintain security. Because of this, symmetric encryption is generally considered more resistant to quantum threats compared to traditional asymmetric methods.
This evolving landscape is pushing the development of next-generation cryptographic systems that can withstand future technological advancements.
Role in Digital Trust and Secure Communication
Encryption is not just about protecting data; it is also about establishing trust in digital communication. Asymmetric encryption plays a major role in building this trust by enabling identity verification and secure key exchange between unknown parties.
When a user connects to a secure system, asymmetric encryption helps confirm that the system they are communicating with is legitimate. This prevents attackers from impersonating trusted services and intercepting sensitive data.
Once trust is established, symmetric encryption ensures that ongoing communication remains fast, efficient, and secure. Together, they form the foundation of digital trust in modern communication systems.
Without these encryption methods, secure online transactions, messaging, and data sharing would not be possible at the scale we see today.
Use in Authentication Systems and Secure Logins
Authentication systems rely heavily on encryption to verify user identities and protect login credentials. Asymmetric encryption is commonly used in authentication protocols because it allows secure verification without exposing sensitive information.
For example, when a user logs into a system, their credentials may be protected using encryption techniques that ensure they cannot be intercepted during transmission. Digital signatures may also be used to verify that the login request is genuine and has not been altered.
Symmetric encryption is often used after authentication to maintain secure sessions. Once a user is verified, a symmetric session key is generated to handle ongoing communication efficiently.
This combination ensures both secure access and smooth user experience without compromising performance.
Efficiency in Cloud and Distributed Computing
Cloud computing environments rely heavily on encryption to protect data stored and transmitted across distributed systems. Symmetric encryption is commonly used for encrypting stored data due to its efficiency and ability to handle large-scale storage systems.
Asymmetric encryption is used for secure access control, identity verification, and secure key exchange between clients and cloud servers. This ensures that only authorized users can access sensitive resources.
In distributed systems, where data is constantly moving between different nodes, encryption plays a critical role in maintaining confidentiality and integrity. The hybrid use of both encryption methods ensures that cloud systems remain scalable, secure, and efficient.
Future Direction of Encryption Technologies
The future of encryption is focused on improving both security and performance while preparing for new computational threats. Researchers are working on optimizing existing algorithms and developing new ones that can resist advanced attacks, including those from quantum computers.
There is also a growing emphasis on automation in key management, where systems can automatically generate, rotate, and revoke encryption keys without manual intervention. This reduces the risk of human error and improves overall system security.
Another important trend is the integration of encryption directly into hardware, which improves performance and enhances protection against software-based attacks. These advancements are expected to make encryption even more seamless and efficient in future systems.
Practical Challenges in Real-World Deployment
In real-world environments, deploying encryption is not only about choosing between symmetric and asymmetric methods but also about handling practical limitations such as system compatibility, latency, and integration complexity. Many legacy systems were originally built around symmetric encryption because of its simplicity and speed. When newer security requirements demand asymmetric encryption, integrating both systems can create compatibility challenges.
Another issue is latency introduced during secure handshakes. While asymmetric encryption is essential for establishing trust, it adds initial delay before communication can begin. In high-performance systems, even small delays matter. This is why systems are carefully optimized to minimize the number of asymmetric operations and quickly switch to symmetric encryption once a secure session is established.
Additionally, developers must consider error handling in encryption workflows. If key exchange fails or encryption parameters mismatch, communication can break entirely. These operational challenges make encryption design a critical part of system architecture rather than just a security feature.
Human and Operational Factors in Encryption Security
Encryption strength does not depend only on algorithms but also on how humans interact with systems. Many security breaches occur due to weak passwords, improper key storage, or accidental exposure of sensitive credentials.
In symmetric encryption systems, users must securely share and store secret keys. If users write down keys insecurely or transmit them through unsafe channels, the system becomes vulnerable regardless of the encryption strength.
In asymmetric systems, private key protection becomes the most critical responsibility. If a private key is stolen or mismanaged, attackers can impersonate the key owner and decrypt sensitive data. This makes secure storage solutions such as hardware security modules or encrypted key vaults essential.
Training, awareness, and strict operational policies play a major role in ensuring that encryption systems remain effective in practice.
Regulatory and Compliance Considerations
Encryption is also influenced by legal and regulatory requirements across different industries. Many sectors such as banking, healthcare, and government operations are required to follow strict data protection standards.
Symmetric encryption is often used to comply with data-at-rest protection requirements because of its efficiency in encrypting large datasets. Asymmetric encryption is frequently used for secure authentication, digital signatures, and secure communication protocols required by compliance frameworks.
Organizations must also ensure proper key management practices, including key rotation policies, access control, and audit logging. Failure to comply with encryption standards can result in legal penalties, data breaches, and loss of trust.
These regulations reinforce the importance of using both encryption methods together in a structured and well-managed way.
Performance Optimization Techniques
To improve efficiency, modern systems implement several optimization techniques when using encryption. One common approach is session reuse, where a single asymmetric handshake is used to establish a long-lived symmetric session. This reduces the number of expensive cryptographic operations.
Another technique is hardware acceleration, where encryption tasks are offloaded to specialized processors. This significantly improves performance, especially in systems that handle large volumes of encrypted data.
Caching mechanisms are also used to store frequently accessed encryption keys securely, reducing the need for repeated key generation or exchange. These optimizations ensure that encryption does not become a bottleneck in high-performance systems.
Security Evolution and Continuous Improvement
Encryption systems are not static; they evolve continuously to respond to new threats and technological advancements. Attack methods are becoming more sophisticated, requiring constant updates to cryptographic algorithms and implementation strategies.
Symmetric encryption continues to evolve through stronger algorithms and larger key sizes, improving resistance to brute-force and analytical attacks. Asymmetric encryption is also advancing with more efficient mathematical models and better resistance against emerging computational threats.
Security updates, patch management, and algorithm deprecation are essential practices in maintaining long-term encryption strength. Outdated encryption methods are regularly replaced to prevent exploitation of known vulnerabilities.
Interdependence of Symmetric and Asymmetric Encryption
Although symmetric and asymmetric encryption are often compared, they are deeply interconnected in modern systems. Neither method alone can fully satisfy all security requirements. Symmetric encryption provides the speed required for large-scale data handling, while asymmetric encryption provides the trust and security needed for secure communication setup.
Their interdependence is what makes modern cybersecurity systems both practical and secure. Removing either method would significantly weaken the overall security model and reduce system efficiency.
This relationship highlights the importance of understanding both methods not as alternatives but as complementary components of a unified security strategy.
Conclusion
Symmetric and asymmetric encryption are two fundamental pillars of modern cryptography, each serving a distinct but interconnected role in securing digital communication. Symmetric encryption excels in speed, efficiency, and scalability, making it ideal for encrypting large volumes of data and supporting real-time applications. However, it faces challenges in secure key distribution and management.
Asymmetric encryption addresses these challenges by enabling secure key exchange and identity verification without requiring shared secrets. Although it is slower and more computationally intensive, it is essential for establishing trust in untrusted environments such as the internet.
In practice, both methods are combined in hybrid encryption systems, which form the backbone of modern secure communication protocols. Asymmetric encryption is used to securely exchange keys, while symmetric encryption handles the actual data transmission for efficiency.
Together, they ensure confidentiality, integrity, and authenticity in digital systems. As technology continues to evolve, both encryption methods will continue to adapt, strengthen, and integrate with emerging technologies to protect data in an increasingly connected and complex digital world.