A modern computer network is built on multiple layers of organization that ensure devices can communicate efficiently, securely, and without unnecessary congestion. Two of the most commonly used concepts in this structure are subnetting and VLANs. Although they are often mentioned together and sometimes even confused with each other, they serve different purposes and operate at different layers of the networking model. Understanding how they differ is essential for anyone working with networks, whether in small office environments or large enterprise infrastructures.
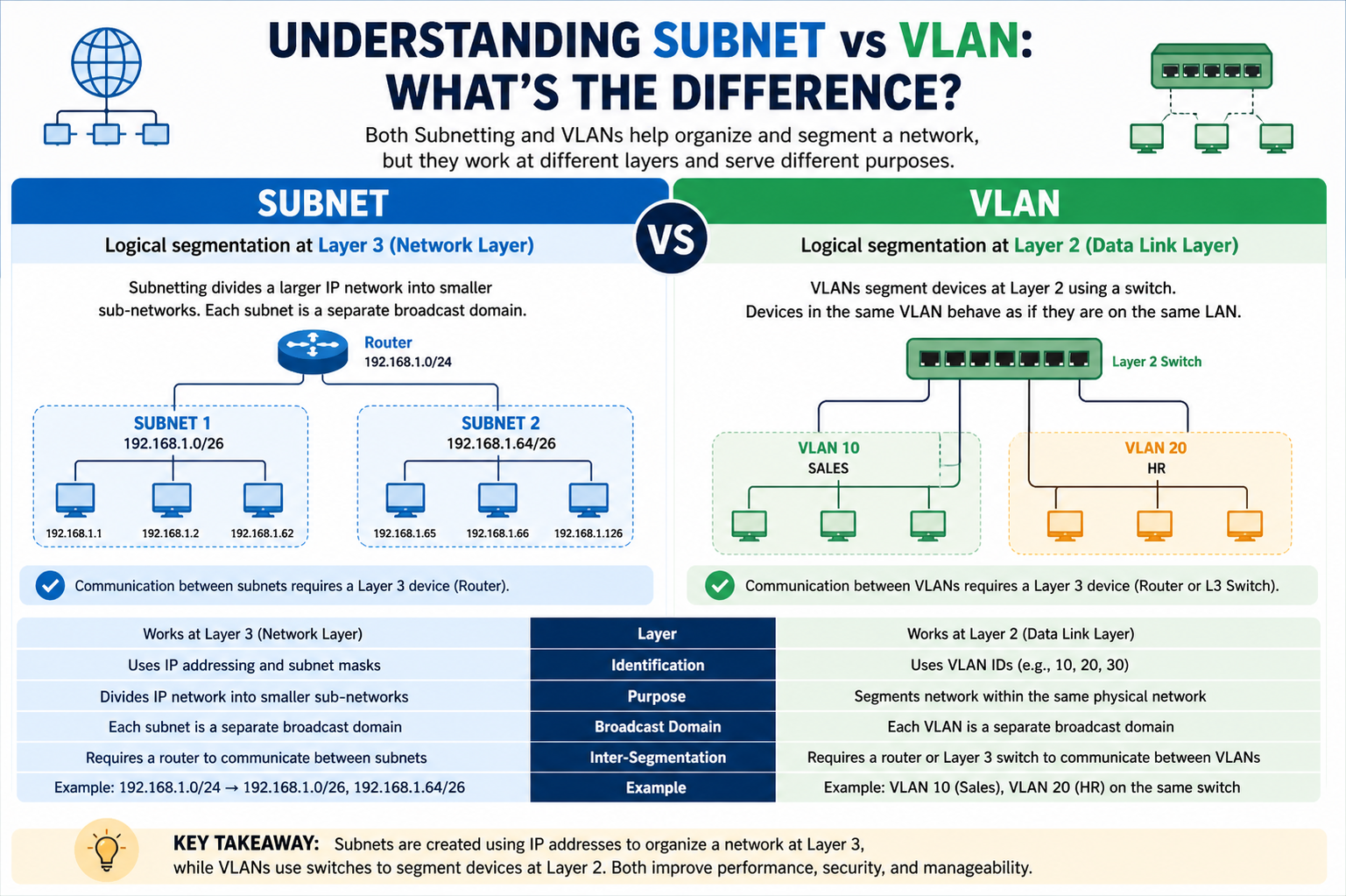
Subnetting is primarily a Layer 3 concept in the OSI model, meaning it operates at the network layer and deals with IP addressing. A subnet, short for subnetwork, is a logically divided section of an IP network. It allows a larger network to be broken down into smaller, more manageable segments. This segmentation improves performance, reduces broadcast traffic, and enhances security by limiting communication within defined boundaries. Each subnet is identified by a unique range of IP addresses defined through a subnet mask, which determines how many devices can exist within that segment.
VLANs, or Virtual Local Area Networks, on the other hand, operate at Layer 2, the data link layer. A VLAN is a logical grouping of devices within a network that allows them to behave as if they are on the same physical LAN, even if they are located on different switches or physical locations. VLANs are used to segment network traffic without requiring physical separation of hardware. This makes them highly flexible and cost-effective for organizing large networks.
Core Purpose of Subnetting
The main purpose of subnetting is to divide a large IP network into smaller, efficient segments. This division helps reduce broadcast traffic because devices within a subnet communicate more directly with each other without flooding the entire network. Subnetting also helps in better IP address management, which is especially important given the limited availability of IPv4 addresses.
For example, an organization with a single large IP network can create multiple subnets for different departments such as HR, finance, and IT. Each department will have its own range of IP addresses, which prevents unnecessary communication between unrelated systems and improves overall network performance. Subnetting also adds a layer of security because it isolates network traffic logically, making it harder for unauthorized access to spread across the entire network.
Core Purpose of VLANs
VLANs are designed to logically separate network devices regardless of their physical location. This means that devices connected to different switches can still be part of the same VLAN if configured accordingly. VLANs help in organizing a network into functional groups such as departments, project teams, or security zones.
One of the biggest advantages of VLANs is flexibility. Network administrators can easily move devices from one VLAN to another without changing physical connections. This reduces the need for rewiring and makes network management significantly more efficient. VLANs also enhance security by isolating sensitive traffic. For example, guest users can be placed in a separate VLAN that has no access to internal company resources.
Layer Difference Between Subnet and VLAN
The most fundamental difference between subnetting and VLANs lies in the layer at which they operate. Subnetting works at Layer 3 and is associated with IP addressing and routing. VLANs work at Layer 2 and are associated with MAC addressing and switching.
Because of this difference, subnetting requires a router or Layer 3 device to communicate between subnets, while VLANs require a Layer 3 device or inter-VLAN routing to communicate between VLANs. Even though VLANs and subnets are often configured to align with each other, they are not dependent on one another. A VLAN can exist without a subnet, and a subnet can exist without a VLAN, but in practical network design, they are often used together for better control.
How Subnets Control Traffic
In subnetting, communication is restricted by IP boundaries. Devices within the same subnet can communicate directly without needing a router. However, if a device needs to communicate outside its subnet, the traffic must pass through a router or gateway. This routing process ensures that data is directed properly across different network segments.
Subnetting helps reduce network congestion by limiting broadcast domains. A broadcast sent within a subnet will not travel beyond its boundary, which reduces unnecessary traffic across the network. This improves performance, especially in large-scale environments where excessive broadcast traffic can slow down operations.
How VLANs Control Traffic
VLANs control traffic at the switch level by grouping ports into logical networks. Devices in the same VLAN can communicate as if they are on the same physical switch, even if they are connected to different switches across the network. VLANs also define broadcast domains, meaning broadcasts are contained within a VLAN and do not affect other VLANs.
This separation improves efficiency because it reduces unnecessary traffic between unrelated devices. For example, employees in the finance department will not receive broadcast messages intended for the engineering department if they are placed in separate VLANs. This improves both security and network performance.
Security Differences
Subnetting provides security by isolating IP address ranges. Since devices in different subnets require routing to communicate, administrators can control and filter traffic at the routing level. Access control lists and firewall rules can be applied between subnets to restrict communication.
VLANs provide security by isolating groups of devices at the switch level. Even if devices share the same physical infrastructure, VLAN separation ensures that they cannot communicate unless explicitly allowed. This is particularly useful in environments where multiple user groups share the same network hardware.
While both subnetting and VLANs improve security, VLANs are generally more flexible in isolating users within the same physical infrastructure, whereas subnetting provides stronger control at the IP routing level.
Performance Impact
Subnetting improves network performance by reducing broadcast domains and organizing IP traffic more efficiently. It ensures that routing is optimized and that unnecessary traffic does not overwhelm the network.
VLANs also improve performance by segmenting traffic at the switch level. Since VLANs limit broadcast traffic within logical groups, network congestion is reduced. VLANs are particularly effective in large enterprise networks where multiple departments share the same physical infrastructure.
When used together, subnetting and VLANs can significantly enhance overall network performance by combining Layer 2 and Layer 3 segmentation.
Configuration and Management Differences
Subnetting requires careful IP address planning. Network administrators must calculate subnet masks, determine available host ranges, and assign IP addresses accordingly. This process requires a strong understanding of IP addressing schemes and routing principles.
VLAN configuration is typically done on managed switches. Administrators assign switch ports to specific VLANs and configure trunk links to allow VLAN traffic between switches. VLAN management is generally more flexible and easier to modify compared to subnetting because it does not require changes to IP addressing schemes.
However, misalignment between VLANs and subnets can lead to network confusion. In well-designed networks, each VLAN is often mapped to a corresponding subnet to maintain consistency and simplify routing.
Real-World Use Case of Subnets
In a corporate environment, subnetting is often used to separate different departments or services. For example, a company may assign one subnet to employee devices, another to servers, and another to guest users. This structure helps control traffic flow and ensures that sensitive systems are isolated from general user access.
Subnetting is also widely used in internet service providers to allocate IP address blocks to customers. Each customer receives a subnet that defines how many devices they can connect to the network.
Real-World Use Case of VLANs
VLANs are commonly used in offices, universities, and data centers. For instance, in a university, students, faculty, and administrative staff may all use the same physical network infrastructure, but VLANs separate their traffic logically. This ensures that student devices cannot access administrative systems.
In data centers, VLANs help isolate different application environments such as development, testing, and production. This separation ensures stability and security across different workloads.
Relationship Between Subnetting and VLANs
Although subnetting and VLANs are different technologies, they are often used together to create structured and secure networks. A common design practice is to assign one subnet per VLAN. This approach simplifies routing, improves security, and makes network management more predictable.
When a device in one VLAN needs to communicate with a device in another VLAN, routing between their corresponding subnets is required. This process is known as inter-VLAN routing and is handled by a Layer 3 device.
Key Conceptual Difference
The simplest way to understand the difference is that subnetting divides networks logically at the IP level, while VLANs divide networks logically at the switch level. Subnetting focuses on addressing and routing, while VLANs focus on segmentation and switching.
Subnetting and VLANs are both essential tools in modern networking, but they serve distinct purposes. Subnetting is about dividing IP networks for efficient routing and management, while VLANs are about creating logical separation within physical networks. When used together, they create highly efficient, secure, and scalable network architectures that support complex organizational needs.
Advanced Comparison Between Subnetting and VLANs in Network Design
In more advanced networking environments, subnetting and VLANs are not just simple segmentation tools but foundational elements that define how large-scale systems operate. As networks grow in complexity, the relationship between logical addressing and physical connectivity becomes increasingly important. Subnetting and VLANs work together to provide structure, but they do so from different perspectives. Subnetting organizes how devices are identified and routed, while VLANs determine how devices are grouped and communicated within switching infrastructure.
In enterprise architecture, subnetting is often aligned with organizational structure, security policies, and application requirements. Each subnet typically represents a distinct logical network with its own addressing rules and routing boundaries. VLANs, meanwhile, represent functional or operational groupings of devices that may or may not correspond directly to physical locations. This separation allows network engineers to design flexible systems where physical layout does not limit logical organization.
Traffic Flow Behavior in Subnets
Understanding how traffic flows in subnetted networks is essential for grasping their role in communication control. When a device sends data within the same subnet, the communication occurs directly at the local level using ARP resolution to identify MAC addresses. This process ensures fast and efficient data transfer without involving routing devices.
However, when communication is required outside the subnet, the data packet is forwarded to a default gateway. The router then determines the appropriate path to the destination subnet. This routing process introduces controlled segmentation, ensuring that traffic between different subnets is explicitly managed rather than freely broadcasted. This structure allows administrators to implement strict policies on inter-subnet communication.
Subnet-based traffic control is particularly useful in environments where security boundaries must be enforced at the IP level. For example, databases may be placed in a restricted subnet that only allows access from specific application servers, preventing direct access from general user systems.
Traffic Flow Behavior in VLANs
VLANs control traffic flow differently by operating at the switching layer. Devices within the same VLAN can communicate as if they are on a single broadcast domain, regardless of their physical location. Switches maintain VLAN membership information and ensure that frames are only forwarded to ports within the same VLAN.
When a device sends a broadcast message within a VLAN, that message is contained entirely within that VLAN boundary. It does not propagate to other VLANs, which significantly reduces unnecessary network traffic. This containment improves efficiency and reduces congestion in large switched networks.
To enable communication between VLANs, a process called inter-VLAN routing is required. This involves a Layer 3 device that can route traffic between VLANs based on IP addressing. Without this routing mechanism, VLANs remain isolated from each other even if they exist on the same physical infrastructure.
Security Architecture Differences
From a security standpoint, subnetting and VLANs offer different layers of protection. Subnetting enforces security through IP-level separation. Access control lists, firewalls, and routing policies are used to regulate traffic between subnets. This makes subnetting highly effective for controlling access between different network zones such as internal systems, external-facing services, and management networks.
VLANs provide security by isolating broadcast domains at the data link layer. This prevents unauthorized devices from receiving or sending traffic within a specific group. VLANs are especially effective in environments where multiple user groups share the same physical hardware but require strict separation.
For example, in a corporate environment, guest users can be placed in a VLAN that restricts access to internal resources, while employees are placed in another VLAN with broader access rights. Even though both groups may use the same switches and cables, VLAN configuration ensures strict separation.
Scalability Considerations
Subnetting plays a critical role in scalability at the IP addressing level. As organizations grow, they require more structured IP allocation to avoid address conflicts and routing inefficiencies. Proper subnet planning ensures that networks can expand without requiring complete redesigns of addressing schemes.
Large organizations often design hierarchical subnet structures where regional networks, departmental networks, and service-specific networks are logically separated. This hierarchical approach simplifies routing tables and improves network stability.
VLANs contribute to scalability by allowing networks to grow without physical restructuring. New departments or services can be added simply by creating new VLANs and assigning switch ports accordingly. This flexibility reduces infrastructure costs and simplifies expansion.
In combination, subnetting and VLANs provide a scalable framework where both IP addressing and physical connectivity can evolve independently while still maintaining logical alignment.
Troubleshooting and Network Management
Troubleshooting in subnetted networks typically involves analyzing routing tables, IP configurations, and gateway settings. Network administrators must ensure that devices have correct IP addresses, subnet masks, and default gateways. Misconfiguration at the subnet level often results in connectivity issues that require deep inspection of routing paths.
In VLAN-based networks, troubleshooting focuses on switch configurations, port assignments, and trunk link settings. Issues often arise when devices are assigned to incorrect VLANs or when VLAN tagging is misconfigured on trunk links between switches.
While subnet issues are generally related to logical addressing, VLAN issues are more related to physical or switch-level configuration. Understanding this distinction is crucial for efficient network diagnostics.
Inter-VLAN Routing and Subnet Integration
One of the most important intersections between VLANs and subnetting is inter-VLAN routing. Since VLANs operate at Layer 2 and subnets operate at Layer 3, communication between VLANs requires routing functionality. Each VLAN is typically assigned a corresponding subnet, creating a one-to-one mapping between logical groups and IP ranges.
A router or Layer 3 switch performs the routing between VLANs by examining IP addresses and forwarding packets accordingly. This setup allows devices in different VLANs to communicate securely and efficiently while maintaining logical separation.
For example, a network might assign one VLAN and subnet to human resources, another to engineering, and another to finance. Inter-VLAN routing ensures that controlled communication can occur between these departments when necessary, while still enforcing security boundaries.
Performance Optimization in Combined Environments
When subnetting and VLANs are properly aligned, network performance improves significantly. Broadcast traffic is reduced at both the Layer 2 and Layer 3 levels, resulting in lower congestion and faster data transmission. Proper segmentation ensures that devices only process relevant traffic.
Additionally, routing efficiency improves when subnet structures are logically designed. Smaller routing domains reduce the complexity of routing tables, which allows routers to make faster forwarding decisions. Similarly, VLAN segmentation reduces unnecessary switch processing overhead.
In high-performance environments such as data centers, this combined approach is essential for maintaining low latency and high throughput.
Administrative Control and Policy Enforcement
Subnetting allows administrators to enforce policies based on IP address ranges. This includes bandwidth limitations, access restrictions, and traffic filtering. Because subnets are tied to IP addresses, policies can be applied consistently across devices regardless of their physical location.
VLANs allow administrators to enforce policies based on device grouping. This includes restricting access to certain services, prioritizing traffic types, or isolating specific user groups. VLAN-based policies are often implemented directly on switches, making them highly effective for local traffic control.
When combined, subnetting and VLANs provide multi-layered policy enforcement that operates at both the switching and routing levels.
Common Misunderstandings Between Subnetting and VLANs
A frequent misunderstanding in networking is assuming that subnetting and VLANs are the same or interchangeable. While they are often configured together, they serve fundamentally different roles. Subnetting is concerned with IP addressing and routing, while VLANs are concerned with switching and traffic segmentation.
Another misconception is that VLANs automatically require different subnets. While this is a common design practice, it is not technically mandatory. However, aligning VLANs with subnets simplifies management and reduces configuration complexity.
Final Perspective on Their Relationship
Subnetting and VLANs are best understood as complementary technologies rather than competing ones. Subnetting defines how devices are identified and routed across a network, while VLANs define how devices are grouped and isolated within the switching environment. Together, they create a structured, scalable, and secure networking framework that supports modern communication requirements.
In practical network design, ignoring either concept leads to inefficiencies and potential security risks. Proper integration ensures that networks remain organized, manageable, and capable of supporting both current and future demands.
Real-World Network Design Using Subnetting and VLANs
In real-world networking environments, subnetting and VLANs are rarely used in isolation. Instead, they are combined to create structured, layered architectures that support large numbers of users, devices, and services. This combined approach is what allows modern organizations to maintain order in complex infrastructures that may span multiple buildings, cities, or even countries.
In a typical enterprise design, VLANs are first used to separate traffic based on function or department. Each VLAN represents a logical group of devices such as employees, servers, voice systems, or guest users. Once these VLANs are defined, subnetting is applied to assign a unique IP address range to each VLAN. This ensures that both Layer 2 and Layer 3 segmentation align with each other, creating a consistent and manageable network structure.
This alignment is not accidental; it is a best practice in network engineering. When VLANs and subnets are properly mapped, troubleshooting becomes easier, security policies become clearer, and routing behavior becomes more predictable. Without this alignment, networks can quickly become confusing and difficult to maintain.
Designing Department-Based Network Segmentation
One of the most common use cases for combining subnetting and VLANs is departmental separation. In a large organization, different departments such as finance, human resources, marketing, and engineering all have unique communication needs and security requirements.
Each department is typically assigned its own VLAN to isolate traffic at the switch level. This prevents unnecessary communication between departments and reduces broadcast traffic. At the same time, each VLAN is assigned a corresponding subnet to manage IP addressing and routing.
For example, the finance department might operate on one VLAN and subnet, while engineering operates on another. This ensures that finance systems remain logically separated from engineering systems, even if they share the same physical infrastructure. If communication between these departments is required, it must pass through a router or Layer 3 switch, where security rules can be enforced.
This structure allows organizations to maintain strict control over sensitive data while still enabling controlled collaboration where necessary.
Guest Network Isolation Strategy
Guest networks are another important example of subnetting and VLAN usage. In most organizations, guests such as visitors or contractors require internet access but should not have access to internal systems.
To achieve this, a dedicated VLAN is created specifically for guest users. This VLAN is isolated from internal VLANs at the switch level. A separate subnet is assigned to the guest VLAN, ensuring that guest devices receive IP addresses from a controlled range.
Routing rules are then configured so that traffic from the guest subnet is only allowed to access external networks, such as the internet, while internal subnets remain inaccessible. This layered approach ensures strong isolation and protects internal resources from unauthorized access.
Data Center Network Architecture
In data center environments, subnetting and VLANs become even more critical due to the high density of servers and applications. Data centers often host thousands of virtual machines and services that must be carefully segmented for performance and security.
VLANs are used to separate different types of traffic, such as application traffic, storage traffic, and management traffic. Each VLAN is assigned a corresponding subnet to ensure proper IP addressing and routing.
For example, storage systems may exist on a dedicated VLAN and subnet to isolate high-volume data transfer from general application traffic. This separation improves performance by reducing congestion and ensuring that critical workloads are not affected by unrelated traffic.
Virtualization platforms also rely heavily on VLANs to isolate virtual networks within physical infrastructure. This allows multiple virtual environments to coexist on the same hardware while remaining logically separated.
Role of Routing in Combined Architectures
Routing plays a central role in connecting subnetted VLAN environments. Since each VLAN typically corresponds to a separate subnet, routers or Layer 3 switches are required to facilitate communication between them.
Inter-VLAN routing allows controlled communication between different segments of the network. For example, a web server in one VLAN may need to communicate with a database server in another VLAN. This communication is allowed through routing rules that define which traffic is permitted.
The routing device evaluates IP addresses and applies security policies before forwarding traffic between subnets. This ensures that even though communication is possible, it remains controlled and secure.
Without proper routing design, VLANs and subnets would remain isolated, preventing necessary communication between critical systems.
Broadcast Control and Network Efficiency
One of the major advantages of using both subnetting and VLANs together is the significant reduction in broadcast traffic. Broadcasts are messages sent to all devices within a network segment, and excessive broadcast traffic can degrade performance.
VLANs limit broadcasts to their own Layer 2 domain, ensuring that broadcast messages do not spread across the entire physical network. Subnetting further limits broadcast impact at the Layer 3 level by dividing networks into smaller IP segments.
This dual-layer restriction results in highly efficient networks where unnecessary traffic is minimized. Devices only receive relevant communication, which improves overall responsiveness and reduces network congestion.
Security Layering and Defense Strategy
Modern network security relies on multiple layers of protection, and subnetting and VLANs form an important part of this defense strategy. VLANs provide isolation at the switch level, preventing unauthorized access between groups of devices. Subnetting adds another layer of control by enforcing IP-based restrictions through routing policies.
This layered approach is often referred to as defense in depth. Even if one layer is compromised, the other layer still provides protection. For example, even if a device is mistakenly placed in the wrong VLAN, subnet-based routing rules can still prevent unauthorized access.
Similarly, even if IP-based access is attempted within a subnet, VLAN isolation can prevent communication at the switching level. This redundancy makes networks significantly more secure.
Scalability in Large Organizations
As organizations grow, their networks must scale efficiently without becoming overly complex. Subnetting supports scalability by allowing structured IP allocation across different regions, departments, or services.
VLANs support scalability by allowing new logical networks to be created without physical changes to infrastructure. New VLANs can be added to switches, and devices can be reassigned without rewiring or replacing hardware.
Together, these technologies enable networks to expand smoothly. Whether adding new employees, new offices, or new services, administrators can scale both IP addressing and logical segmentation in a controlled and predictable way.
Common Configuration Mistakes in Practice
Despite their benefits, subnetting and VLANs are often misconfigured in real-world environments. One common mistake is mismatching VLANs and subnets, which leads to confusion in routing and troubleshooting.
Another frequent issue is incorrect trunk configuration between switches, which prevents VLAN traffic from being properly transmitted across the network. On the subnet side, incorrect subnet masks or gateway settings can cause devices to lose connectivity.
These issues highlight the importance of careful planning and documentation when designing network architectures. Without proper alignment between VLANs and subnets, even well-designed networks can experience operational problems.
Operational Efficiency and Network Management
From an operational perspective, combining VLANs and subnetting simplifies network management. Administrators can quickly identify which devices belong to which segment based on both VLAN and IP information.
This dual identification system makes it easier to monitor traffic, apply policies, and troubleshoot issues. It also improves visibility across the network, allowing administrators to detect anomalies or performance bottlenecks more efficiently.
In addition, centralized management tools can use VLAN and subnet information to automate configurations and enforce consistent policies across large infrastructures.
Troubleshooting Subnet and VLAN Issues in Real Networks
In practical network environments, problems related to subnetting and VLANs are among the most common challenges network administrators face. Although both concepts are powerful when correctly implemented, even small configuration errors can lead to connectivity failures, performance issues, or unexpected traffic behavior. Understanding how to troubleshoot these systems requires a clear understanding of where each technology operates and how they interact.
When troubleshooting subnet-related issues, the focus is usually on IP configuration, routing paths, and gateway accessibility. A common problem is incorrect IP addressing, where a device is assigned an IP outside its designated subnet range or is configured with an incorrect subnet mask. This can prevent devices from communicating even if they are physically connected to the network. Another frequent issue is incorrect default gateway configuration, which stops devices from reaching other subnets or external networks.
Routing problems can also occur when routes between subnets are missing or misconfigured. In such cases, devices may communicate within their own subnet but fail to reach external networks. Administrators typically resolve these issues by reviewing routing tables and ensuring that correct paths exist between all required subnets.
In VLAN-related troubleshooting, the focus shifts to switch configuration and port assignments. One of the most common issues is assigning a device to the wrong VLAN. This results in the device being isolated from expected network resources or placed in an unintended broadcast domain. Another frequent issue involves trunk links between switches, where VLAN tagging may be incorrectly configured or missing. This prevents VLAN traffic from being properly transmitted across the network infrastructure.
Understanding whether the issue is related to Layer 2 (VLAN) or Layer 3 (subnetting) is crucial for efficient troubleshooting. Misdiagnosing the layer often leads to wasted time and ineffective solutions.
Performance Optimization Techniques
Optimizing network performance using subnetting and VLANs involves careful planning and continuous monitoring. One of the primary goals is to reduce unnecessary broadcast traffic, which can consume bandwidth and degrade performance in large networks.
Subnetting improves performance by dividing large IP networks into smaller segments, which reduces the scope of broadcast domains. This ensures that broadcast traffic remains limited to relevant devices. VLANs further enhance this effect by restricting broadcasts at the switch level, ensuring that only devices within the same VLAN receive broadcast messages.
Another optimization technique involves proper network segmentation based on traffic patterns. High-traffic systems such as servers or databases are often placed in separate VLANs and subnets to prevent congestion caused by user traffic. This separation ensures that critical services maintain consistent performance even under heavy network load.
Load distribution is also improved through segmentation. By dividing users and services across multiple VLANs and subnets, network traffic is more evenly distributed, reducing bottlenecks and improving responsiveness.
Security Enforcement in Layered Networks
Security is one of the most important reasons for implementing both subnetting and VLANs. In layered network architectures, security is enforced at multiple points, making unauthorized access significantly more difficult.
At the VLAN level, security is enforced by isolating devices into separate broadcast domains. Devices in one VLAN cannot directly communicate with devices in another VLAN without routing intervention. This prevents lateral movement within the network, which is a common technique used in cyberattacks.
At the subnet level, security is enforced through routing policies, access control lists, and firewall rules. These controls determine which traffic is allowed to pass between subnets. Even if a device is able to reach another subnet, routing rules can block or filter the communication based on predefined policies.
This dual-layer security model ensures that even if one layer is compromised, the other still provides protection. It also allows organizations to implement granular access control, where different departments or services have tailored communication permissions.
Network Segmentation in Cloud and Virtual Environments
In modern cloud and virtualized environments, subnetting and VLAN concepts are still widely used, although they are often implemented in software-defined ways. Virtual networks use VLAN-like segmentation to isolate traffic between virtual machines, containers, or services.
Subnetting is used to assign IP ranges within virtual networks, ensuring that each virtual environment has structured addressing. This is particularly important in cloud environments where multiple tenants may share the same physical infrastructure.
Virtual networks rely heavily on automated routing and segmentation rules to enforce isolation. This allows cloud providers to offer scalable and secure environments where users can deploy applications without worrying about underlying physical infrastructure.
The combination of subnetting and virtual VLAN-like segmentation enables flexible and scalable cloud architectures that can support dynamic workloads and rapid provisioning.
Impact on Network Design Decisions
When designing a network, the decision to use subnetting and VLANs is influenced by several factors including scale, security requirements, performance needs, and administrative complexity. Smaller networks may use simple subnetting without VLANs, while larger enterprise networks almost always require both.
Designers must carefully plan how many VLANs are needed and how subnets will be allocated. Poor planning can lead to IP exhaustion, routing complexity, or inefficient traffic flow. Proper design ensures that each VLAN has a clear purpose and each subnet is appropriately sized for expected device counts.
Another important consideration is future growth. Networks must be designed with scalability in mind, allowing new VLANs and subnets to be added without disrupting existing configurations. This requires careful IP planning and modular VLAN design.
Differences in Administrative Control
Subnetting and VLANs also differ in how they are managed administratively. Subnetting is typically managed by network engineers responsible for IP addressing schemes and routing policies. Changes to subnet structures often require careful planning because they affect multiple systems and routing configurations.
VLANs, on the other hand, are managed at the switch level and can often be modified more quickly. Administrators can add or remove VLAN assignments on ports without changing IP addressing. This makes VLANs more flexible for day-to-day network adjustments.
However, despite this flexibility, VLAN changes must still be carefully coordinated with subnet configurations to avoid mismatches and connectivity issues.
Enterprise-Level Integration Strategy
In enterprise environments, subnetting and VLANs are integrated into a unified network architecture. Each VLAN is mapped to a specific subnet, and routing is used to control communication between them. This integration creates a predictable and manageable structure where both logical and physical segmentation are aligned.
This strategy allows organizations to enforce consistent security policies, optimize performance, and simplify troubleshooting. It also enables automation in network management systems, where VLAN and subnet data can be used to dynamically configure services and policies.
Large enterprises often use hierarchical network designs, where core, distribution, and access layers all incorporate VLAN and subnet planning. This layered approach ensures that traffic flows efficiently from edge devices to core systems.
Long-Term Benefits of Structured Segmentation
Over time, the combined use of subnetting and VLANs provides significant long-term benefits. Networks become easier to scale, more secure, and more efficient to manage. Administrative overhead is reduced because structured segmentation makes it easier to locate issues and apply changes.
Additionally, structured networks are more resilient to change. Whether adding new departments, expanding infrastructure, or integrating new technologies, well-designed subnet and VLAN architectures allow seamless adaptation without major disruptions.
This long-term stability is one of the key reasons why subnetting and VLANs remain fundamental concepts in networking, even as technologies continue to evolve.
Conclusion
Subnetting and VLANs are both essential components of modern network design, but they serve different roles and operate at different layers of the networking model. Subnetting focuses on dividing and organizing IP address space at the network layer, ensuring efficient routing, controlled communication, and structured IP management. VLANs, on the other hand, focus on logically separating devices at the data link layer, allowing flexible grouping of systems regardless of their physical location.
When used independently, each technology provides value on its own. Subnetting helps reduce broadcast traffic and improves routing efficiency, while VLANs enhance flexibility and isolate traffic within switch-based environments. However, their true strength becomes clear when they are used together in a coordinated design. Mapping VLANs to subnets creates a structured architecture where logical grouping and IP addressing align, making networks easier to manage, secure, and scale.
In real-world environments such as enterprises, data centers, and cloud infrastructures, this combination is not optional but standard practice. It enables administrators to enforce security policies at multiple layers, optimize performance by reducing unnecessary traffic, and maintain clear organizational separation between different departments, services, or user groups.
Ultimately, understanding the difference between subnetting and VLANs is not just about knowing definitions. It is about understanding how modern networks are built, controlled, and protected. Subnetting defines how communication is routed, while VLANs define how communication is grouped. Together, they form the backbone of efficient and scalable network architecture, ensuring that complex systems remain organized, secure, and reliable as they grow.