LDAP (Lightweight Directory Access Protocol) is a widely used protocol designed to manage and access directory information such as user accounts, authentication data, organizational structures, and system resources. It plays a crucial role in enterprise environments where centralized identity management is required. LDAP itself does not define a single way of transmitting data securely; instead, it relies on different transport methods and port configurations to determine how communication is handled between clients and directory servers.
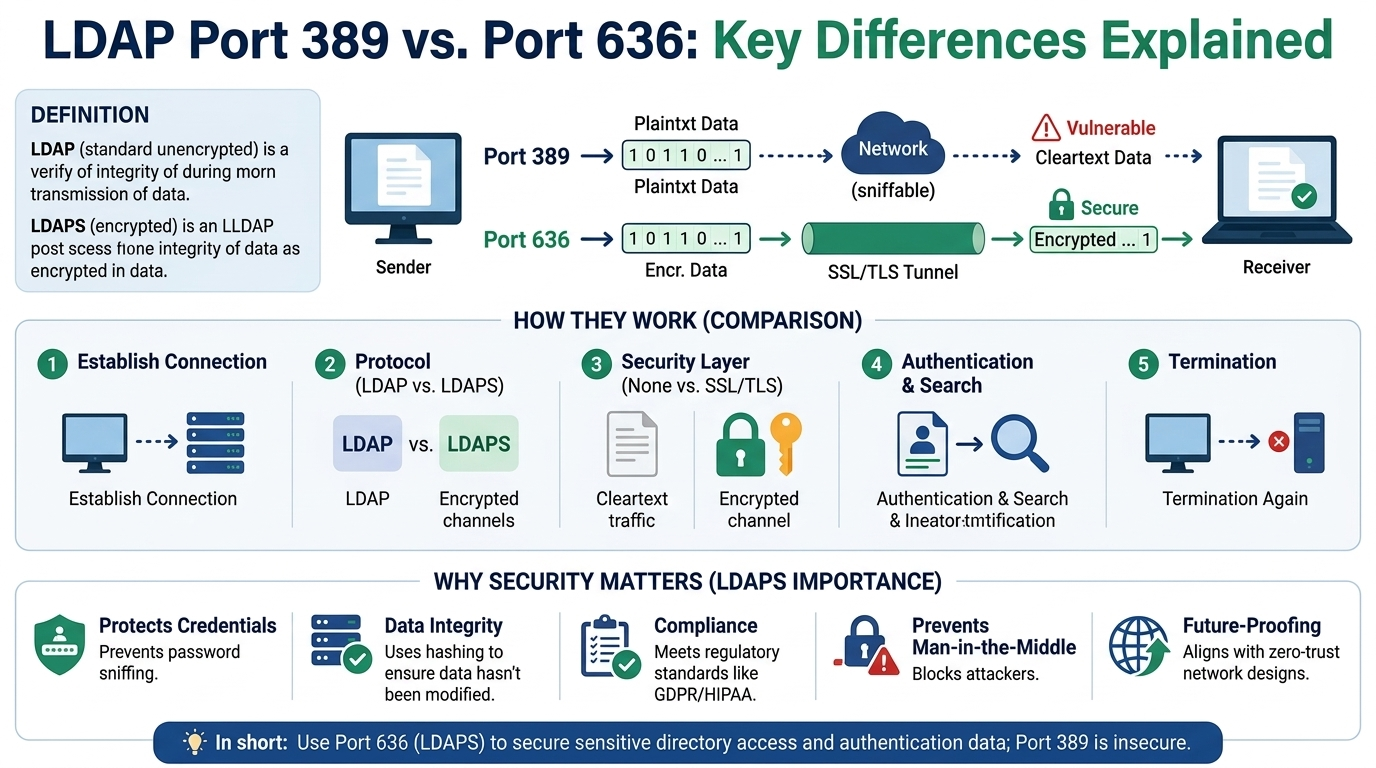
The two most commonly used ports, 389 and 636, represent different approaches to handling security and data transmission. While both are used for LDAP operations, the way they establish connections and protect information differs significantly, making each suitable for different environments and security requirements.
Understanding LDAP Port 389 in Detail
Port 389 is the default port assigned to LDAP services. It is historically the standard communication endpoint for directory queries and authentication requests. When a client connects to an LDAP server using this port, the connection is typically initiated without encryption. This means that the initial communication, including login credentials and directory queries, can be transmitted in plain text unless additional security mechanisms are explicitly enabled.
One of the key features of port 389 is its support for StartTLS. StartTLS is an extended operation that allows an existing unencrypted LDAP connection to be upgraded to a secure TLS-encrypted connection. This means that the session begins in an open state but can transition into a secure state if both the client and server support encryption and the configuration enforces it.
This flexibility makes port 389 widely compatible with older systems and environments where strict encryption is not enforced by default. However, it also introduces potential risks if StartTLS is not properly configured or if systems continue to operate without enforcing encryption.
In many legacy infrastructures, port 389 is still heavily used due to its compatibility with older directory services and applications. However, modern security standards increasingly discourage unencrypted LDAP traffic due to the sensitivity of the data involved, particularly credentials and identity information.
StartTLS and Its Role in Secure LDAP on Port 389
StartTLS is a critical mechanism that enhances the security of LDAP communication over port 389. It works by initiating a standard LDAP connection first and then negotiating encryption through TLS. Once the TLS handshake is successfully completed, all further communication is encrypted.
This approach provides a balance between backward compatibility and security. Systems that do not support TLS can still communicate using LDAP, while modern systems can upgrade the connection to secure mode.
However, the reliance on StartTLS also introduces configuration complexity. If clients fail to request encryption or servers do not enforce it, the connection may remain unencrypted. This is why many security policies require explicit enforcement of StartTLS or discourage its use in favor of always-encrypted connections.
Understanding LDAP Port 636 in Detail
Port 636 is dedicated to LDAPS, which stands for LDAP over SSL/TLS. Unlike port 389, this port enforces encryption from the moment the connection is established. There is no initial unencrypted phase, and the entire session is secured using SSL/TLS protocols.
When a client connects to port 636, the TLS handshake occurs immediately. This ensures that all data exchanged between the client and server is encrypted before any LDAP operations take place. This includes authentication credentials, directory searches, and any updates or modifications to directory entries.
Because encryption is mandatory on this port, it is generally considered the more secure option for LDAP communication. It eliminates the risk of accidental exposure of sensitive data due to misconfiguration or lack of encryption enforcement.
Port 636 is widely used in modern enterprise environments where compliance requirements and security standards mandate encrypted communication for all identity-related traffic.
SSL/TLS Encryption and Its Importance in LDAPS
The security model used in port 636 relies on SSL/TLS encryption protocols. These protocols ensure confidentiality, integrity, and authenticity of the communication between LDAP clients and servers.
During the connection process, the server presents a digital certificate to the client. This certificate is used to verify the identity of the server and establish a trusted connection. Once the handshake is complete, all subsequent data is encrypted using symmetric encryption algorithms, which provide both performance efficiency and strong security.
This approach significantly reduces the risk of man-in-the-middle attacks, credential theft, and data interception. Because encryption is enforced at the transport level, LDAPS provides a more consistent security model compared to optional encryption mechanisms.
Key Security Differences Between Port 389 and Port 636
The primary difference between the two ports lies in how and when encryption is applied. Port 389 allows both encrypted and unencrypted communication depending on configuration, while port 636 enforces encryption from the start.
This distinction has major implications for security posture. Port 389 can be vulnerable if StartTLS is not enforced or properly configured, potentially allowing sensitive information to be transmitted in plain text. In contrast, port 636 eliminates this risk by requiring encryption for all communication.
Another important difference is the predictability of security behavior. Port 636 provides consistent encryption enforcement, whereas port 389 relies on client and server negotiation, which can vary depending on implementation and configuration.
Performance Considerations in LDAP Communication
While both ports support secure communication, there are subtle performance differences due to the way encryption is handled. Port 389 may have slightly faster initial connection times when not using StartTLS because it begins without encryption overhead. However, once StartTLS is enabled, performance becomes comparable to LDAPS.
Port 636 introduces encryption immediately, which adds a small initial overhead due to the TLS handshake process. However, this difference is generally negligible in modern systems and is outweighed by the security benefits.
In large-scale enterprise environments, the performance difference between the two ports is rarely a deciding factor. Instead, security requirements typically take priority.
Firewall and Network Configuration Considerations
From a network perspective, both ports require appropriate firewall rules to allow LDAP traffic. Port 389 is often used in internal networks, while port 636 is preferred for secure or external-facing communication.
Network administrators must ensure that only authorized systems can access these ports to prevent unauthorized directory access. Additionally, some environments restrict port 389 entirely to enforce encrypted communication through port 636 only.
Proper network segmentation and access control policies play an important role in securing LDAP traffic regardless of which port is used.
Certificate Management in LDAP over SSL/TLS
One of the most important aspects of LDAPS on port 636 is certificate management. The LDAP server must present a valid SSL/TLS certificate that is trusted by client systems.
If the certificate is self-signed or expired, clients may reject the connection or require manual trust configuration. This makes certificate lifecycle management a critical component of maintaining secure LDAP communication.
Proper certificate configuration ensures secure authentication of the server and prevents impersonation attacks. In enterprise environments, certificates are often issued by internal certificate authorities or trusted public authorities depending on the use case.
Common Misconfigurations and Security Risks
One of the most common issues in LDAP deployments is improper configuration of encryption settings. In port 389 setups, failure to enforce StartTLS can result in unencrypted credential transmission. This creates a significant security risk, especially in environments handling sensitive identity data.
Another common issue involves incorrect certificate configuration in LDAPS. If clients cannot validate the server certificate, they may fail to establish a secure connection or fall back to insecure methods if allowed.
Mixing both ports without clear security policies can also lead to inconsistent behavior, where some applications use encrypted communication while others do not.
Enterprise Usage Patterns and Best Practices
In modern enterprise environments, port 636 is generally preferred for all LDAP communication due to its enforced encryption model. Organizations dealing with compliance requirements such as data protection regulations typically mandate LDAPS usage.
Port 389 is still used in some environments for compatibility reasons, particularly where legacy applications cannot support LDAPS. However, even in such cases, StartTLS is usually enforced to ensure encryption is applied.
Best practices recommend disabling unencrypted LDAP traffic entirely wherever possible and standardizing on secure communication channels.
Technical Comparison
The choice between LDAP ports 389 and 636 ultimately comes down to security requirements and system compatibility. Port 389 offers flexibility and backward compatibility through optional encryption, while port 636 provides a more secure and modern approach with mandatory encryption.
In environments where data security is a priority, LDAPS on port 636 is generally the preferred choice. However, understanding both ports is essential for managing hybrid systems and ensuring secure directory communication across different infrastructure layers.
Operational Differences in Real-World LDAP Environments
In practical deployments, the choice between LDAP port 389 and 636 is not just a theoretical security preference but a decision that affects how authentication systems, applications, and directory services interact daily. Large organizations often run hybrid configurations where both ports may exist simultaneously, supporting different generations of applications and varying security capabilities.
Port 389 is often integrated into systems that rely on flexibility in communication. Applications that were developed before modern encryption standards were widely enforced may still depend on unencrypted LDAP or optional StartTLS upgrades. This allows older systems to continue functioning without requiring complete redevelopment or replacement.
On the other hand, port 636 is commonly adopted in environments where security policies are strictly enforced. Systems using this port assume that encryption is non-negotiable, which simplifies compliance and reduces the risk of accidental insecure communication. In such environments, directory services become part of a fully encrypted identity infrastructure.
Authentication Flow Differences Between Both Ports
Authentication behavior is another area where the difference between these two ports becomes important. When using port 389, authentication requests may initially travel in plain text unless StartTLS is successfully negotiated before credentials are transmitted. If encryption is not enforced early in the session, sensitive information such as usernames and passwords can be exposed.
In contrast, port 636 ensures that authentication occurs only after a secure TLS channel has been established. This means credentials are never exposed outside of encrypted traffic. This fundamental difference significantly reduces the attack surface for credential interception.
From a security design perspective, this makes port 636 more suitable for systems that handle privileged accounts, administrative access, or sensitive organizational data.
Client Compatibility and Legacy System Support
One of the reasons port 389 still exists in many environments is its broad compatibility with legacy systems. Older directory-enabled applications, operating systems, and authentication tools were originally designed to work with unencrypted LDAP communication. Introducing LDAPS in such systems often requires configuration changes, certificate management updates, or even software upgrades.
Port 389 allows these systems to continue operating without immediate modifications. However, this convenience comes at the cost of reduced security unless StartTLS is properly enforced.
In contrast, port 636 requires clients to support SSL/TLS from the beginning of the connection. While most modern systems support this without issue, older applications may not be compatible, which can create migration challenges during security upgrades.
Security Compliance and Regulatory Requirements
Modern security frameworks and regulatory standards strongly influence the preference for LDAP over port 636. Many compliance frameworks require encryption of sensitive data in transit, especially when dealing with authentication credentials and personally identifiable information.
Port 636 naturally aligns with these requirements because encryption is mandatory and always active. This simplifies audits and reduces the complexity of proving compliance, since there is no risk of unencrypted LDAP traffic under normal operation.
Port 389, however, requires additional validation during audits. Organizations must demonstrate that StartTLS is enforced and that no unencrypted bind operations are permitted. This often involves stricter monitoring and configuration controls.
Because of this, many security policies explicitly discourage or even disable plain LDAP usage over port 389 unless it is strictly necessary.
Network Architecture Considerations
From a network design perspective, LDAP traffic must be carefully controlled regardless of which port is used. Directory services are critical infrastructure components, and unauthorized access can lead to significant security breaches.
Port 389 is sometimes allowed only within internal trusted networks, where additional layers of security such as firewalls, VPNs, or network segmentation are in place. Even then, organizations often enforce StartTLS to ensure that traffic is encrypted within the internal environment.
Port 636 is more commonly exposed within controlled boundaries where encrypted communication is required by default. This reduces the need for conditional security checks at the application level, since encryption is guaranteed at the transport layer.
Proper firewall configuration is essential in both cases to ensure that only authorized systems can access directory services.
Debugging and Troubleshooting Differences
Troubleshooting LDAP issues can also vary depending on whether port 389 or 636 is used. With port 389, administrators may need to determine whether a connection is encrypted or not, and whether StartTLS was successfully negotiated. This adds an additional layer of complexity when diagnosing authentication or communication issues.
In contrast, port 636 simplifies troubleshooting from a security perspective because encryption is always expected. If a connection fails, administrators can immediately focus on certificate validation, TLS configuration, or network connectivity rather than determining whether encryption was applied.
However, LDAPS-related issues often involve certificate trust problems, which can be more complex to resolve than plain connectivity issues in unencrypted LDAP.
Certificate Trust and Client-Side Validation Challenges
A key aspect of LDAPS communication over port 636 is the requirement for trusted certificates. Clients must validate the server’s certificate against a trusted certificate authority. If this validation fails, the connection may be rejected.
Common issues include expired certificates, mismatched hostnames, or missing intermediate certificate chains. These problems can prevent successful LDAP authentication even when network connectivity is correct.
Port 389 with StartTLS also relies on certificates when encryption is enabled, but because encryption is optional, misconfigurations may go unnoticed until security enforcement is applied.
Proper certificate lifecycle management becomes essential in environments relying heavily on LDAPS.
Performance Implications in Large-Scale Systems
In high-volume environments such as enterprise authentication systems, performance considerations become important. LDAP servers often handle thousands of authentication requests per second, and even small inefficiencies can accumulate.
Port 389 without encryption may offer slightly lower latency because no TLS handshake is required. However, this performance gain comes at a significant security cost.
Port 636 introduces a TLS handshake at the start of each session, but modern implementations often reuse connections or optimize session resumption, minimizing performance impact.
In most real-world systems, the difference in performance is negligible compared to the importance of secure communication.
Migration Strategies from LDAP to LDAPS
Organizations transitioning from port 389 to port 636 typically follow a phased migration strategy. This involves first enabling LDAPS alongside existing LDAP services, then gradually updating applications to use secure connections.
During this transition, both ports may remain active to ensure compatibility. However, security policies often enforce logging and monitoring to ensure that insecure connections are not used for sensitive operations.
Eventually, organizations aim to disable unencrypted LDAP traffic entirely, leaving only LDAPS as the supported communication method.
Security Risks of Mixed Environments
Running both port 389 and 636 without clear governance can introduce security inconsistencies. Some applications may use encrypted communication while others continue transmitting sensitive data in plain text.
This inconsistency can lead to security gaps that are difficult to detect, especially in large distributed environments. Attackers often target these weak points to intercept credentials or perform man-in-the-middle attacks.
For this reason, many security architectures recommend standardizing on a single encrypted LDAP method wherever possible.
Operational Comparison
The operational differences between LDAP ports 389 and 636 extend beyond simple port numbers. They influence authentication security, system compatibility, network design, compliance posture, and long-term infrastructure strategy.
Port 389 offers flexibility and backward compatibility but requires strict enforcement to avoid insecure communication. Port 636 provides a more secure, standardized approach by enforcing encryption at all times.
In modern environments, LDAPS over port 636 is generally considered the preferred and safer choice, while port 389 remains relevant mainly for legacy support or controlled internal scenarios where StartTLS is strictly enforced.
Advanced Security Implications of LDAP Port Selection
When organizations evaluate LDAP port 389 versus 636, the discussion eventually moves beyond basic encryption into deeper security architecture concerns. The choice impacts how identity data flows across systems, how attackers might attempt interception, and how resilient the directory service is against modern threat models.
Port 389 introduces a conditional security model. Because encryption depends on StartTLS negotiation or strict administrative enforcement, there is always a theoretical risk of downgrade or misconfiguration. In poorly managed environments, a client may connect without upgrading to TLS, leaving sensitive authentication traffic exposed. Even if encryption is intended, the system relies on correct behavior from both client and server, which increases complexity.
Port 636 removes this conditional behavior entirely. It enforces encryption at the transport layer before any LDAP operations occur. This eliminates downgrade risks and reduces the number of variables that could lead to insecure communication. From a security engineering perspective, this makes LDAPS more predictable and easier to validate during audits or penetration testing.
Attack Surface Considerations in LDAP Deployments
The attack surface of LDAP services is directly influenced by which port is used and how it is configured. Port 389, when not strictly hardened, can expose multiple attack vectors. These include credential sniffing on unencrypted sessions, StartTLS stripping attempts, and misconfigured bind requests that do not enforce encryption.
In contrast, port 636 significantly reduces exposure to these risks by requiring TLS from the beginning. While it does not eliminate all LDAP-related vulnerabilities, it ensures that the transport layer is not the weak point. Attackers would need to focus on certificate impersonation, weak cipher configurations, or server-side vulnerabilities rather than simply intercepting traffic.
However, it is important to understand that encryption alone does not secure the entire LDAP ecosystem. Even on port 636, weak authentication policies, poor access controls, or excessive directory permissions can still lead to serious security breaches.
Certificate-Based Trust Models in LDAPS
One of the most critical components of LDAP over port 636 is the certificate trust model. Unlike port 389 with optional encryption, LDAPS relies heavily on SSL/TLS certificates to establish identity verification between client and server.
This introduces a trust hierarchy where certificates must be issued, validated, and maintained properly. If a client cannot verify the server certificate, the connection may fail or require manual trust overrides, which can introduce security risks if not managed carefully.
Certificate expiration is another common operational risk. If an LDAPS certificate expires, authentication systems depending on port 636 may suddenly fail, potentially disrupting business-critical services. This makes certificate lifecycle management a core operational requirement in secure LDAP deployments.
In contrast, port 389 with StartTLS may appear more tolerant in misconfigured environments, but this tolerance often masks underlying security weaknesses.
Identity Management and Authentication Security Models
LDAP is often at the center of identity management systems, serving as the backbone for authentication across applications, services, and infrastructure components. The security of this identity layer is therefore critical to the overall security posture of an organization.
With port 389, authentication flows can be more complex because encryption may not be guaranteed unless explicitly enforced. This can lead to inconsistent security states across different applications connecting to the same directory service.
Port 636 simplifies this model by ensuring that all authentication exchanges occur within an encrypted channel. This consistency reduces the likelihood of configuration drift, where some systems are secure while others are not.
From an identity governance perspective, consistent encryption enforcement is a key advantage of LDAPS.
Operational Reliability and Failure Modes
Another important difference between the two ports lies in how failures occur and how they are diagnosed. Port 389 environments may experience subtle failures where authentication appears to work but is actually occurring without encryption. This can create hidden security exposures that are difficult to detect without deep inspection.
Additionally, StartTLS failures can be intermittent, depending on client support, certificate validation, or network conditions. This unpredictability can complicate troubleshooting in production environments.
Port 636 failures are typically more explicit. If LDAPS does not work, the issue is usually related to certificate trust, TLS configuration, or network connectivity. This makes failure modes more transparent and easier to isolate.
However, LDAPS failures can also be more disruptive, because there is no fallback to unencrypted communication. While this improves security, it reduces tolerance for misconfiguration.
Scalability Considerations in Directory Services
In large-scale systems, LDAP is often used for authentication across thousands or even millions of users. In such environments, scalability is not just about handling traffic volume but also about maintaining consistent security behavior across distributed systems.
Port 389 can scale effectively, but only if security enforcement is consistently applied across all nodes and clients. Any inconsistency in StartTLS enforcement can create security gaps that scale with system size.
Port 636 scales more predictably in terms of security because encryption is enforced uniformly. This reduces variability in client behavior and simplifies architecture design in distributed identity systems.
Modern directory services often rely on connection pooling and session reuse, which helps mitigate the overhead introduced by TLS in LDAPS environments.
Administrative Control and Policy Enforcement
From an administrative standpoint, LDAP port selection is closely tied to policy enforcement mechanisms. Organizations that prioritize strict security often implement policies that disable unencrypted LDAP binds entirely.
In such environments, port 389 may still exist but is restricted to internal use cases or legacy system support. Administrators typically enforce rules that require StartTLS before any bind operation is allowed.
Port 636 simplifies enforcement because encryption is not optional. This reduces administrative overhead and decreases the likelihood of policy violations caused by misconfiguration.
Centralized identity systems benefit from this predictability, especially in environments with multiple administrative teams or complex infrastructure layers.
Interoperability with Modern Security Frameworks
Modern security frameworks emphasize encryption in transit as a baseline requirement. This aligns more naturally with LDAPS on port 636, which enforces encryption by design.
Port 389 can still comply with these frameworks, but only when StartTLS is strictly enforced and validated. This adds complexity during security assessments, as auditors must verify not just the presence of LDAP traffic but also whether it is consistently encrypted.
In contrast, LDAPS simplifies compliance verification because encryption is inherent to the connection model.
Long-Term Infrastructure Evolution
As infrastructure evolves toward zero-trust architectures and encrypted-by-default communication models, LDAP over port 636 aligns more naturally with these trends. The shift toward always-on encryption reflects broader industry changes in how identity and authentication systems are designed.
Port 389 remains relevant primarily for backward compatibility and transitional environments. However, its reliance on optional encryption makes it less suitable for long-term strategic security planning.
Organizations modernizing their identity infrastructure often prioritize migrating fully to LDAPS as part of broader security transformation initiatives.
Final Perspective on Strategic Port Selection
The decision between LDAP ports 389 and 636 ultimately reflects a balance between compatibility and security maturity. Port 389 offers flexibility and supports legacy integration scenarios, but it requires strict governance to avoid insecure communication.
Port 636 represents a more modern, security-first approach that eliminates ambiguity in encryption enforcement. While it introduces dependencies on certificate management and TLS configuration, it provides a more consistent and defensible security posture.
In contemporary enterprise environments, LDAPS is increasingly the standard choice, while port 389 remains a controlled exception rather than a default configuration.
Performance Optimization and Connection Handling in LDAP Systems
In large enterprise environments, LDAP is not just a directory lookup service but a high-throughput authentication backbone that must handle continuous requests from applications, users, and services. The way port 389 and port 636 manage connections can influence overall system efficiency, especially under heavy load.
Port 389, when operating without encryption, can establish connections slightly faster because it avoids the immediate overhead of a TLS handshake. This can be beneficial in extremely low-latency environments where raw speed is prioritized over security. However, once StartTLS is enabled, the performance difference between port 389 and port 636 becomes minimal, since both eventually rely on TLS encryption for secure communication.
Port 636 introduces encryption at the very beginning of the session, which adds a small initial delay due to certificate exchange and handshake negotiation. Modern systems mitigate this through session reuse, persistent connections, and TLS optimization techniques. As a result, in real-world enterprise deployments, the performance difference is typically negligible compared to the security benefits gained.
Session Persistence and Resource Utilization
LDAP connections often remain open for extended periods, especially in systems that rely heavily on authentication caching or frequent directory queries. In such scenarios, the cost of the initial handshake becomes less significant than the efficiency of maintaining long-lived sessions.
Port 636 benefits from secure session reuse mechanisms, allowing repeated authentication requests to occur over an already encrypted channel without redoing the full handshake each time. This improves efficiency while maintaining strict security enforcement.
Port 389, on the other hand, may introduce variability depending on whether sessions start unencrypted and later transition to TLS. If StartTLS is not consistently used, session behavior can differ across clients, leading to inconsistent security states and potential performance unpredictability in mixed environments.
Logging, Monitoring, and Visibility Differences
Monitoring LDAP traffic is an essential part of maintaining secure identity infrastructure. The choice of port can influence how easily administrators can inspect and analyze directory activity.
With port 389, unencrypted traffic can be easier to inspect in environments where StartTLS is not enforced. This may help with debugging or auditing in controlled internal systems. However, this visibility also introduces a security risk if sensitive data is exposed in logs or network captures.
Port 636 encrypts all traffic, which significantly improves security but reduces direct visibility into raw LDAP queries at the network level. Administrators must rely on application logs, directory server logs, or specialized monitoring tools that can interpret encrypted sessions without exposing sensitive content.
This trade-off between visibility and security is an important consideration when designing monitoring strategies for identity systems.
Compatibility Challenges in Mixed Infrastructure
Many real-world environments are not homogeneous. They often include a mix of modern applications and legacy systems, each with different LDAP capabilities. This creates scenarios where both port 389 and port 636 must coexist.
Port 389 provides compatibility for older systems that do not support TLS or have limited encryption capabilities. This makes it easier to integrate legacy applications without immediate refactoring.
Port 636 supports modern systems that expect secure communication by default. However, integrating both ports in the same environment requires careful policy enforcement to ensure that insecure communication does not become the default fallback.
Without strict governance, mixed environments can inadvertently allow some systems to use encrypted LDAP while others continue using unencrypted communication, creating uneven security coverage across the infrastructure.
Administrative Overhead and Maintenance Complexity
From an operational perspective, maintaining LDAP over port 389 can introduce additional administrative overhead. Administrators must ensure that StartTLS is correctly configured, enforced, and consistently applied across all clients and services.
This often requires ongoing validation, policy enforcement, and monitoring to ensure that encryption is not accidentally bypassed. Misconfigurations can lead to silent security gaps that are difficult to detect without deep inspection.
Port 636 reduces this complexity by eliminating optional encryption states. Since TLS is mandatory, administrators do not need to verify whether encryption is enabled for each connection. This simplifies maintenance and reduces configuration drift over time.
However, LDAPS introduces its own operational responsibility in the form of certificate management, renewal schedules, and trust chain validation. While different in nature, this overhead is generally more predictable and easier to automate than enforcing optional encryption across multiple systems.
Risk Management and Threat Mitigation
From a risk management perspective, LDAP communication must be evaluated based on potential exposure to interception, impersonation, and credential theft.
Port 389 increases risk when encryption is not strictly enforced. Attackers positioned within the network can potentially capture sensitive authentication data if traffic is transmitted in plain text. Even with StartTLS available, misconfigurations or downgrade scenarios can expose vulnerabilities.
Port 636 significantly reduces these risks by ensuring that all communication is encrypted before any sensitive data is transmitted. This minimizes opportunities for interception and strengthens the overall security posture of identity systems.
However, LDAPS is not immune to all threats. Weak certificate validation, outdated cipher suites, or compromised certificate authorities can still introduce vulnerabilities if not properly managed.
Integration with Modern Identity Architectures
Modern identity systems increasingly rely on centralized authentication services, single sign-on solutions, and federated identity models. LDAP often serves as the underlying directory layer supporting these systems.
Port 636 aligns more naturally with these architectures because secure communication is a foundational requirement. Identity providers expect consistent encryption behavior to maintain trust relationships between services.
Port 389 may still be used internally within tightly controlled environments, but it is less aligned with modern zero-trust principles, which assume that all network communication must be encrypted and verified.
As identity architectures evolve, LDAPS is increasingly becoming the default standard for directory communication.
Troubleshooting Real-World Authentication Failures
When LDAP authentication issues occur, the root cause often depends on which port is being used. With port 389, troubleshooting may involve determining whether StartTLS was successfully negotiated, whether credentials were transmitted securely, or whether fallback to unencrypted communication occurred.
These layered possibilities make diagnosis more complex and time-consuming.
With port 636, troubleshooting is more focused. Issues typically revolve around certificate trust, TLS negotiation failures, or network connectivity problems. While certificate-related issues can be complex, they are generally more deterministic than mixed encryption states.
This difference makes LDAPS environments easier to standardize in large-scale operations.
Conclusion
LDAP ports 389 and 636 represent two fundamentally different approaches to securing directory communication. Port 389 provides flexibility and backward compatibility, allowing systems to operate in both encrypted and unencrypted modes depending on configuration. This makes it useful in legacy environments but introduces security risks if encryption is not strictly enforced.
Port 636 enforces encryption from the beginning of every connection, providing a more secure and consistent communication model. It simplifies compliance, reduces configuration complexity, and aligns better with modern security standards such as encrypted-by-default and zero-trust architectures.
While port 389 still has a role in supporting older systems and transitional environments, port 636 is generally preferred for secure, production-grade identity infrastructures. In most modern deployments, LDAPS is considered the standard approach, while plain LDAP over port 389 is increasingly restricted or phased out in favor of stronger security guarantees.