Bidirectional Forwarding Detection is built on a simple but highly efficient architecture that allows two network devices to monitor each other’s forwarding capability. At its core, BFD relies on two endpoints, often called neighbors, which establish a logical session. This session becomes the foundation for continuous health monitoring of the link or path between them. Each endpoint maintains state information about the session, including whether the neighbor is reachable and whether packets are being received within expected time intervals.
The architecture is intentionally lightweight so that it can operate across different types of network devices and protocols without requiring significant processing power. BFD sessions are independent of the routing protocol itself, which means they function at the forwarding layer while providing feedback to higher-level routing decisions. This separation is one of the reasons BFD can detect failures much faster than traditional protocol-based timers.
Each BFD session maintains a set of parameters that define how quickly and how frequently control messages are exchanged. These parameters include transmission intervals, detection multipliers, and session states. Together, they ensure that both devices agree on how the session should behave and what constitutes a failure condition.
Session Establishment Process
When two devices begin a BFD session, they first negotiate parameters through control packets. This negotiation ensures that both sides agree on timing intervals and operational modes before active monitoring begins. Once agreement is reached, the session transitions into an established state where continuous monitoring starts.
During this process, each device assigns a unique identifier to the session, which helps differentiate multiple BFD sessions running between the same devices or across multiple links. This is especially important in complex network topologies where multiple paths may exist between two endpoints.
After the session is established, both devices begin sending periodic control messages. These messages are small in size but critical in function, as they serve as proof that the forwarding path is still operational. If either device fails to receive these messages within the expected timeframe, it assumes a failure and transitions the session into a down state.
The speed of session establishment and failure detection is one of the key advantages of BFD, making it suitable for environments where rapid convergence is essential.
Control Packets and Their Role
Control packets in BFD are the primary mechanism for maintaining session health. These packets are exchanged at regular intervals and contain essential information such as session state, detection time, and diagnostic codes. The simplicity of these packets allows them to be processed quickly by network devices, minimizing overhead.
Each control packet acts as a heartbeat signal between the two endpoints. When received consistently, it confirms that the forwarding path is functioning correctly. If packets stop arriving, it indicates a potential failure in the network path or device.
Control packets also carry diagnostic information that helps network administrators identify the type of failure that has occurred. This may include indications of a control detection time expiration, echo failure, or neighbor down condition. These diagnostics are valuable for troubleshooting and root cause analysis.
Because control packets are lightweight, they can be transmitted frequently without significantly impacting network performance. This frequent transmission is what enables BFD to achieve sub-second failure detection times.
Echo Functionality and Fast Failure Detection
One of the advanced features of BFD is the echo function, which provides an additional layer of verification for forwarding paths. In echo mode, one device sends packets that are looped back by the neighboring device using its forwarding path. This ensures that the data plane itself is functioning correctly, not just the control plane.
The echo mechanism is particularly useful in detecting issues that may not affect control packets but still disrupt actual data traffic. By testing the forwarding path directly, BFD can identify failures that would otherwise go unnoticed until traffic is impacted.
Echo packets are typically sent at a higher frequency than control packets, allowing for extremely fast detection of failures. However, because echo mode relies on proper forwarding behavior, it may not be supported in all network environments.
When combined with control packet exchange, echo functionality significantly improves the accuracy and speed of failure detection, making BFD highly reliable in critical network infrastructures.
Demand Mode Operation
BFD can operate in demand mode, which reduces the frequency of control packet exchange under normal conditions. In this mode, once a session is established, devices do not continuously send periodic control packets. Instead, they rely on periodic checks initiated by the routing protocol or higher-layer systems.
Demand mode is useful in environments where reducing control traffic is important, such as large-scale networks with many BFD sessions. It helps conserve bandwidth and processing resources while still maintaining the ability to quickly verify connectivity when needed.
Even in demand mode, devices must be capable of switching back to asynchronous monitoring if required. This flexibility allows BFD to adapt to different operational requirements without compromising reliability.
Demand mode is often used in conjunction with other optimization techniques to balance performance and resource utilization in complex networks.
Single-Hop and Multi-Hop Sessions
BFD supports both single-hop and multi-hop sessions, depending on the network topology. Single-hop sessions are used when two devices are directly connected, typically over the same subnet. These sessions provide the fastest detection times and are commonly used in local network segments.
Multi-hop sessions, on the other hand, are used when devices are separated by multiple routing hops. These sessions are more complex because they must account for intermediate devices that may not be aware of the BFD process. Despite this complexity, multi-hop BFD still provides faster detection compared to traditional routing protocol timers.
In multi-hop scenarios, BFD relies heavily on the underlying routing infrastructure to deliver control packets across the network. This makes proper routing configuration essential for accurate failure detection.
Both session types serve different purposes but share the same fundamental goal of ensuring rapid detection of connectivity issues.
Failure Detection and Response Mechanism
When BFD detects a failure, it immediately transitions the session state to down and informs the associated routing protocols. This rapid notification allows routing systems to begin recalculating paths without waiting for traditional timeout periods.
The failure detection mechanism is based on missed control packets within a predefined detection interval. If the number of missed packets exceeds the allowed threshold, the session is declared down. This threshold is determined by the detection multiplier and transmission interval settings.
Once a failure is detected, routing protocols such as OSPF or BGP are triggered to remove the failed path from their routing tables. This ensures that traffic is quickly rerouted through alternative paths, minimizing disruption.
The speed of this process is critical in maintaining network stability, especially in environments where even short outages can have significant impact.
Scalability and Performance Considerations
BFD is designed to scale efficiently across large and complex networks. Its lightweight packet structure ensures that even thousands of sessions can operate simultaneously without overwhelming network devices. However, proper configuration is essential to maintain performance at scale.
Excessively aggressive timer settings can lead to increased CPU usage and unnecessary control traffic. On the other hand, overly relaxed timers may reduce the effectiveness of failure detection. Finding the right balance is key to optimizing BFD performance in large deployments.
Network administrators must also consider the impact of BFD on routing protocol convergence and overall system load. In well-designed networks, BFD enhances performance by reducing downtime and improving convergence speed.
Scalability is one of the reasons BFD is widely adopted in service provider and enterprise backbone networks.
Best Practices for Deployment
Successful deployment of BFD requires careful planning and configuration. One important practice is to align BFD timers with the capabilities of the underlying network devices to avoid unnecessary load. It is also recommended to start with conservative timer values and gradually adjust them based on network performance.
Another best practice is to enable BFD selectively on critical links rather than across the entire network. This helps reduce overhead while still providing fast failure detection where it matters most.
Monitoring and logging BFD sessions is also important for maintaining network health. Regular observation of session states and failure events can help identify potential issues before they escalate.
Proper integration with routing protocols ensures that BFD provides maximum benefit in terms of convergence speed and reliability.
Troubleshooting and Operational Insights
When issues arise in a BFD-enabled network, troubleshooting typically involves examining session states, timer mismatches, and control packet flow. Common problems include sessions failing to establish due to configuration inconsistencies or excessive packet loss causing false failure detection.
Understanding diagnostic codes within control packets can help pinpoint the exact cause of a failure. These codes provide valuable insight into whether the issue is related to forwarding, control plane processing, or configuration errors.
Network administrators often use session state information to verify whether both endpoints are properly synchronized. If one side reports a down state while the other remains up, it usually indicates a communication breakdown.
Effective troubleshooting of BFD requires a clear understanding of both its operational mechanics and its integration with routing protocols.
BFD Timers and Detection Mechanism in Detail
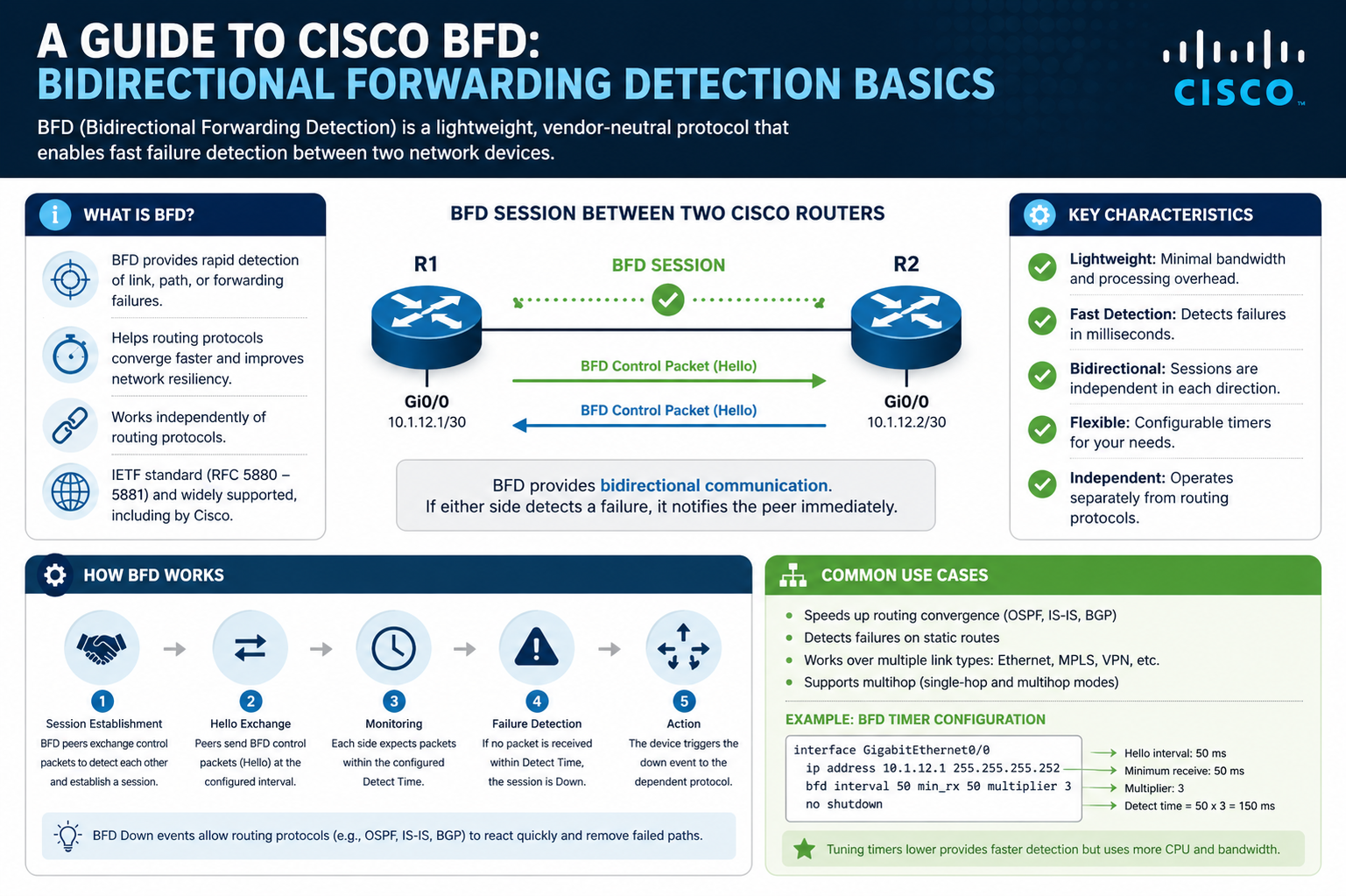
Bidirectional Forwarding Detection relies heavily on its timer system to achieve fast and reliable failure detection. The timer structure is designed to balance speed with stability, ensuring that the network can detect real failures quickly without triggering false alarms due to minor delays or transient congestion. At the heart of this system are two primary values: the transmission interval and the detection multiplier.
The transmission interval defines how frequently BFD control packets are sent from one device to another. This interval is typically configured in milliseconds, allowing for extremely fast exchange of keepalive signals. A shorter interval increases responsiveness but also increases control traffic, while a longer interval reduces overhead but slows down detection.
The detection multiplier works together with the transmission interval to define how many missed packets are allowed before declaring a session failure. For example, if the multiplier is set to three and the transmission interval is 50 milliseconds, the system will declare a failure if no packets are received within 150 milliseconds. This mechanism prevents temporary packet loss from immediately causing a session down event.
Together, these timers form a detection window that determines how quickly BFD reacts to network issues. The flexibility of these values allows administrators to tune BFD for different environments, ranging from highly sensitive financial networks to more stable enterprise backbones where slightly slower detection is acceptable.
State Machine and Session Behavior
BFD operates using a simple but effective state machine that defines how sessions behave under different conditions. The primary states include Down, Init, and Up. Each state represents a specific stage in the lifecycle of a BFD session.
In the Down state, no valid communication has been established between the two endpoints. This may occur when a session is first configured or when a failure has been detected. During this state, devices attempt to initiate or re-establish communication.
The Init state represents an intermediate phase where one device has started receiving valid BFD packets from its neighbor, but bidirectional communication has not yet been fully confirmed. This state ensures that both devices are aware of each other before marking the session as fully operational.
The Up state indicates that the session is fully established and both devices are successfully exchanging control packets. In this state, the network path is considered healthy, and continuous monitoring takes place.
Transitions between these states are driven entirely by the reception or loss of control packets. This simple state machine design allows BFD to operate efficiently while providing clear and predictable behavior during network changes.
Role of BFD in Fast Convergence
One of the most important functions of BFD is enabling fast convergence in dynamic routing environments. Traditional routing protocols rely on periodic hello messages and timeout intervals to detect failures, which can take several seconds to complete. In contrast, BFD reduces this detection time to milliseconds.
When a failure is detected by BFD, it immediately notifies the associated routing protocol. This triggers the routing process to recompute available paths and update routing tables without waiting for standard protocol timers to expire. As a result, traffic can be rerouted almost instantly.
This fast convergence is especially important in environments where uptime is critical, such as financial systems, data centers, and service provider backbones. Even a brief disruption in connectivity can have significant consequences, making rapid recovery essential.
By decoupling failure detection from routing protocol timers, BFD provides a more efficient and responsive mechanism for maintaining network stability.
Interaction with Control and Data Planes
BFD operates across both the control plane and the data plane, providing a comprehensive view of network health. Control packets are used to verify session status at the protocol level, while echo packets and forwarding checks validate the actual data path.
The control plane is responsible for session negotiation, parameter exchange, and state management. It ensures that both devices agree on how the session should operate and maintains the logic for detecting failures.
The data plane, on the other hand, handles the actual forwarding of packets through the network. By testing the data plane directly using mechanisms like echo functionality, BFD ensures that the physical path used for traffic is also operational.
This dual-layer approach makes BFD more reliable than methods that rely solely on control plane signaling. It allows detection of issues that may affect actual traffic flow even if control communication remains intact.
BFD in Layered Network Architectures
In layered network architectures, BFD plays a critical role at multiple levels. It can be used between routers, switches, and even across virtualized network functions. Its flexibility allows it to integrate seamlessly into both physical and virtual environments.
At the access layer, BFD helps detect failures in direct device connections, ensuring that local traffic can quickly reroute if a link goes down. At the distribution layer, it provides fast detection of intermediate path failures, helping maintain stable routing across larger segments of the network.
In core network layers, BFD becomes even more important due to the high volume of traffic and the critical nature of backbone links. Here, even small delays in failure detection can lead to significant traffic disruption. BFD ensures that failures are detected and resolved almost instantly.
This layered applicability makes BFD a universal tool in modern network design, capable of enhancing reliability at every level of the infrastructure.
Load Balancing and Redundancy Support
BFD also plays an important role in environments that use load balancing and redundant paths. In such systems, multiple paths may exist between two endpoints, and traffic is distributed across these paths for efficiency and reliability.
By continuously monitoring each path, BFD can quickly identify when one of the redundant links fails. This allows the network to shift traffic away from the failed path and maintain service continuity without manual intervention.
In load-balanced environments, BFD ensures that traffic distribution remains optimal by removing faulty paths from the active set. Once the failed path is restored, BFD can quickly detect its recovery and reintegrate it into the load balancing process.
This dynamic adaptability makes BFD an essential component in high-availability network designs where redundancy is a key requirement.
Scenarios of False Positives and Stability Concerns
Although BFD is highly efficient, improper configuration can sometimes lead to false positives, where a session is incorrectly marked as down. This typically occurs when timer values are too aggressive or when network congestion causes temporary packet loss.
To avoid such issues, it is important to carefully tune BFD parameters based on the stability of the network. Networks with higher latency or variable traffic patterns may require more conservative settings to prevent unnecessary session resets.
Another factor that can contribute to instability is CPU overload on network devices. If a device is unable to process BFD packets in time, it may incorrectly assume a failure has occurred. Proper resource allocation and monitoring are essential to prevent such conditions.
Despite these challenges, BFD remains highly reliable when configured correctly, offering a strong balance between speed and accuracy.
Security Considerations in BFD Deployments
While BFD is primarily focused on performance and reliability, security is also an important consideration. Because BFD relies on control packet exchange, it is potentially vulnerable to spoofing or unauthorized session manipulation if not properly secured.
To mitigate these risks, many implementations support authentication mechanisms that ensure only valid devices can participate in BFD sessions. This helps prevent malicious actors from injecting false control packets or disrupting session states.
Additionally, network segmentation and access control policies can be used to restrict where BFD sessions are allowed to operate. This reduces the attack surface and enhances overall network security.
Security considerations are especially important in large-scale or multi-tenant environments where different systems share infrastructure.
Operational Efficiency and Network Optimization
Beyond failure detection, BFD contributes to overall network optimization by improving operational efficiency. Faster detection means less time spent on broken paths, resulting in better utilization of available resources.
It also reduces the need for aggressive routing protocol timers, which can be resource-intensive and less reliable. By offloading failure detection to BFD, routing protocols can focus on path computation and traffic management.
This separation of responsibilities leads to cleaner network design and improved scalability. Networks become easier to manage and more predictable in behavior.
In optimized environments, BFD acts as a foundational component that supports both performance and reliability objectives.
Real-World Deployment Patterns
In real-world deployments, BFD is often used in combination with multiple routing protocols and redundancy mechanisms. Service providers typically deploy it across backbone links to ensure uninterrupted connectivity between major network nodes.
Enterprises use BFD to enhance high availability in data centers and branch connections. It is commonly paired with dynamic routing protocols to ensure that failover happens instantly when a link goes down.
In cloud and virtualized environments, BFD helps maintain connectivity between virtual routers and overlay networks. Its lightweight design makes it suitable for software-defined networking environments where agility is essential.
These deployment patterns highlight the versatility of BFD and its importance in modern networking architectures.
BFD Integration with Routing Protocols
Bidirectional Forwarding Detection is not a standalone routing mechanism; instead, it functions as an enhancement layer that works closely with routing protocols to improve failure detection speed. Its primary role is to notify routing systems instantly when a forwarding path becomes unavailable, allowing them to react far quicker than they would using native timers alone.
When integrated with protocols such as OSPF, BGP, or IS-IS, BFD acts as a real-time monitoring system underneath the routing logic. Instead of waiting for hello intervals or hold timers to expire, these protocols rely on BFD to signal failures immediately. This tight coupling significantly reduces convergence time across the network.
In OSPF environments, BFD helps detect link failures between neighbors almost instantly, which prevents traffic from being sent over broken paths. In BGP deployments, it ensures that session failures are identified quickly so that alternative routes can be selected without delay. In IS-IS networks, it improves the responsiveness of adjacency changes, ensuring that topology updates are propagated rapidly.
This integration is usually achieved through simple configuration binding, where BFD sessions are associated with routing neighbors. Once established, BFD operates transparently in the background while routing protocols respond to its state changes.
Impact on Network Convergence Time
Network convergence refers to the time it takes for all devices in a network to agree on the current topology after a change occurs. Without BFD, convergence depends heavily on protocol timers, which are often set conservatively to avoid instability. This can result in delays of several seconds before a failure is fully recognized and corrected.
BFD dramatically reduces this convergence time by detecting failures within milliseconds. When a link goes down, BFD immediately transitions the session state and notifies the routing protocol. This triggers instant recalculation of routes and updates to forwarding tables.
The reduction in convergence time is particularly valuable in high-performance environments where even brief interruptions can affect application performance. Financial trading systems, real-time communication platforms, and large-scale cloud infrastructures all benefit from this improved responsiveness.
By accelerating failure detection, BFD ensures that networks remain highly available and capable of adapting quickly to changing conditions.
BFD Scalability in Large Networks
As networks grow in size and complexity, scalability becomes a critical factor in protocol design. BFD is built with scalability in mind, allowing it to operate efficiently even when thousands of sessions are active simultaneously.
One of the key reasons for this scalability is its lightweight packet structure. BFD control messages are small and require minimal processing, which reduces the load on network devices. This allows large-scale deployments without significant performance degradation.
However, scalability is not just about packet size; it also involves session management. Devices must maintain state information for each active BFD session, which can become resource-intensive in extremely large environments. To address this, network engineers often selectively enable BFD only on critical links rather than every possible connection.
Proper tuning of timers also plays a major role in scalability. Overly aggressive settings can overwhelm devices with frequent packet exchanges, while balanced configurations ensure efficient operation without unnecessary overhead.
In well-designed networks, BFD scales effectively across enterprise, service provider, and cloud infrastructures.
Hardware Acceleration and Performance Optimization
Modern network devices often use hardware acceleration to improve BFD performance. Instead of relying solely on software processing, certain tasks such as packet transmission and reception are offloaded to specialized hardware components.
This acceleration allows BFD to operate with extremely low latency, further improving failure detection speed. It also reduces CPU usage on network devices, freeing resources for other critical functions such as routing computation and traffic management.
Hardware-based BFD implementations are especially useful in high-speed environments where large volumes of traffic are processed continuously. In such cases, software-based processing alone may not be sufficient to maintain optimal performance.
By leveraging hardware acceleration, BFD can achieve consistent and predictable behavior even under heavy network load.
Multi-Hop BFD Complexity and Challenges
While single-hop BFD is relatively straightforward, multi-hop BFD introduces additional complexity. In multi-hop scenarios, devices are not directly connected, and control packets must traverse intermediate routers.
This introduces several challenges, including packet loss, varying latency, and dependency on intermediate routing paths. Because of this, multi-hop BFD typically operates with slightly relaxed timer settings compared to single-hop sessions.
Another challenge is ensuring consistent delivery of control packets across multiple hops. Any instability in the intermediate path can affect BFD accuracy, potentially leading to false failure detections if not properly configured.
Despite these challenges, multi-hop BFD is extremely valuable in large-scale networks where direct connectivity between endpoints is not always possible. It allows for end-to-end path monitoring across complex topologies.
Careful planning and configuration are essential to ensure reliable operation in multi-hop environments.
BFD in Virtualized and Cloud Environments
With the rise of virtualization and cloud computing, BFD has become increasingly important in software-defined environments. In these setups, network functions are often virtualized and distributed across multiple physical hosts.
BFD helps maintain connectivity between virtual routers, overlay networks, and cloud-based routing systems. Its lightweight nature makes it ideal for virtual environments where efficiency and speed are critical.
In cloud infrastructures, BFD is often used to monitor tunnel endpoints, ensuring that encapsulated traffic paths remain active. If a tunnel fails, BFD quickly detects the issue and triggers failover to an alternate path.
This capability is especially important in distributed systems where physical infrastructure may be abstracted away, making traditional failure detection methods less effective.
By providing consistent monitoring across both physical and virtual layers, BFD enhances reliability in modern cloud architectures.
Troubleshooting BFD Issues in Complex Networks
Troubleshooting BFD requires a structured approach, especially in large and complex networks. One of the first steps is to verify session states on both endpoints. If one device shows the session as up while the other shows it as down, there is likely a communication mismatch.
Another common issue involves timer mismatches. If devices are configured with incompatible transmission intervals or detection multipliers, sessions may fail to establish properly. Ensuring consistent configuration across both endpoints is essential.
Packet loss is another frequent cause of instability. Since BFD relies on continuous control packet exchange, even minor disruptions can trigger session failures. Monitoring network congestion and interface errors can help identify these issues.
Diagnostic codes provided by BFD sessions are also valuable in troubleshooting. These codes indicate whether the failure was due to control timeout, forwarding issues, or administrative shutdown.
Effective troubleshooting requires both protocol knowledge and a clear understanding of underlying network behavior.
Operational Best Practices for Stability
To ensure stable BFD operation, network engineers follow several best practices. One important practice is to avoid overly aggressive timer settings unless absolutely necessary. While fast detection is desirable, it should not come at the cost of stability.
Another best practice is to enable BFD only on critical links where fast failure detection is most important. This reduces unnecessary overhead and simplifies network management.
Consistent configuration across devices is also essential. Differences in timer values or session parameters can lead to unpredictable behavior.
Regular monitoring of BFD sessions helps detect early signs of instability. By analyzing session flaps and failure patterns, administrators can proactively address potential issues.
These practices help maintain a balance between performance, reliability, and resource efficiency.
Evolution and Modern Role of BFD
Over time, BFD has evolved from a simple failure detection mechanism into a critical component of modern networking architectures. Its adoption has expanded from traditional routing environments into cloud, virtualization, and software-defined networks.
Modern implementations continue to enhance its capabilities, including better integration with automation systems and improved scalability for large distributed networks. It is now commonly used as part of broader network intelligence frameworks that emphasize real-time responsiveness.
Its role has shifted from optional enhancement to essential infrastructure component in many high-availability environments. As networks continue to grow in complexity, the importance of rapid failure detection becomes even more significant.
BFD remains a foundational protocol that supports the reliability expectations of modern digital systems.
Extended Understanding
Bidirectional Forwarding Detection provides a fast, efficient, and scalable method for detecting network failures across a wide range of environments. Through tight integration with routing protocols, flexible timer configurations, and lightweight operation, it significantly improves network responsiveness and stability.
Its ability to operate across physical, virtual, and cloud infrastructures makes it a versatile solution for modern networking challenges. When properly configured and managed, BFD becomes a powerful tool for ensuring continuous connectivity and minimizing downtime in critical systems.
BFD Deployment in Service Provider Networks
In service provider environments, Bidirectional Forwarding Detection plays a critical role in maintaining uninterrupted connectivity across large-scale backbone infrastructures. These networks carry massive volumes of traffic for multiple customers, so even brief interruptions can have widespread impact. BFD is deployed on core and edge routers to ensure that any link or path failure is detected almost instantly.
Service providers often design networks with multiple redundant paths. BFD continuously monitors these paths and ensures that traffic is always directed through the most stable route. When a failure occurs, BFD immediately signals the routing system, allowing traffic to be rerouted without waiting for slower protocol timers.
This rapid detection is especially important in MPLS-based networks, where label-switched paths must remain highly stable. BFD ensures that failed label paths are removed quickly, preventing traffic blackholing or unnecessary delays.
Because of its efficiency, BFD has become a standard feature in modern service provider architectures, supporting both reliability and service level agreements.
BFD in Data Center Architectures
Data centers require extremely high availability, low latency, and fast recovery from failures. BFD is widely used in these environments to monitor spine-leaf architectures, server-to-switch connectivity, and inter-switch links.
In modern data center designs, traffic flows are highly dynamic, with frequent changes in routing due to virtualization and workload mobility. BFD helps maintain stability by ensuring that any failed link is detected immediately and removed from active forwarding decisions.
It also supports fast failover in leaf-spine topologies, where multiple equal-cost paths exist between devices. When one path fails, BFD ensures that traffic is quickly redirected to an alternate path without noticeable disruption.
In virtualized data centers, BFD is often used to monitor virtual switches and overlay tunnels, ensuring that both physical and virtual connectivity remain intact.
BFD in High Availability and Redundancy Design
High availability networks depend on redundancy at every level, from physical links to routing paths. BFD enhances this design by providing real-time monitoring of all active connections.
In redundant configurations, multiple backup paths are always available. BFD continuously checks the health of each path and ensures that only functional links are used for forwarding traffic. When a primary path fails, BFD triggers an immediate switch to a backup path.
This mechanism significantly reduces downtime and eliminates the need to wait for traditional routing protocol convergence. As a result, services remain available even during unexpected failures.
In mission-critical systems such as healthcare, banking, and emergency services, this level of reliability is essential for continuous operation.
Limitations and Considerations of BFD
Despite its advantages, BFD is not without limitations. One of the primary concerns is the potential for false failure detection if the network is unstable or poorly configured. Excessive packet loss, high latency, or CPU congestion can all cause BFD sessions to flap unnecessarily.
Another limitation is the dependency on correct configuration across both endpoints. If timer values or authentication settings are mismatched, sessions may fail to establish or remain unstable.
BFD also adds some level of control plane overhead, especially in large networks with thousands of sessions. While it is lightweight, improper scaling can still impact device performance.
Additionally, in certain network designs, intermediate devices may not fully support BFD, limiting its effectiveness in multi-hop scenarios.
Understanding these limitations is important for proper deployment and long-term stability.
Security Enhancements in BFD Deployments
As networks become more complex and exposed to external threats, securing BFD sessions has become increasingly important. Unauthorized manipulation of BFD packets could potentially disrupt routing stability or cause false link failures.
To address this, many implementations support authentication mechanisms that ensure only trusted devices can participate in BFD sessions. This prevents malicious actors from injecting fake control packets into the network.
Authentication typically involves shared keys or cryptographic validation of control messages. When enabled, both endpoints must verify each packet before accepting it as valid.
In addition to authentication, network segmentation and access control policies are used to limit where BFD sessions can operate. This reduces exposure and improves overall network security posture.
Security considerations are especially important in multi-tenant environments and service provider networks.
Automation and BFD in Modern Networks
With the rise of network automation and software-defined networking, BFD has become an important component of automated network management systems. It provides real-time feedback that automation tools can use to make intelligent routing decisions.
In automated environments, BFD state changes can trigger scripts or controllers to adjust traffic flows dynamically. This allows networks to respond instantly to failures without human intervention.
BFD also integrates well with orchestration platforms that manage large-scale infrastructures. By providing accurate and fast failure detection, it enables automated systems to maintain optimal performance across distributed networks.
This level of automation improves efficiency and reduces operational overhead, making networks more adaptive and self-healing.
Future of BFD in Networking
As networks continue to evolve toward higher speeds, greater complexity, and increased virtualization, the role of BFD is expected to expand further. Future implementations are likely to focus on even faster detection times, improved scalability, and deeper integration with intelligent network systems.
Emerging technologies such as intent-based networking and AI-driven routing systems may use BFD as a foundational signal for decision-making. Its real-time feedback can help these systems predict failures and adjust configurations proactively.
In addition, enhancements in hardware acceleration and distributed processing will likely improve BFD efficiency in ultra-large-scale environments.
The continued evolution of BFD reflects its importance as a core building block of modern network reliability.
Conclusion
Bidirectional Forwarding Detection has established itself as a fundamental protocol for achieving fast and reliable failure detection in modern networks. By operating independently of routing protocol timers, it dramatically reduces convergence time and ensures that traffic is quickly rerouted in the event of a failure.
Its lightweight design, flexible timer configuration, and ability to integrate with multiple routing protocols make it suitable for a wide range of environments, including service provider networks, enterprise infrastructures, data centers, and cloud systems.
While it requires careful configuration and consideration of scalability and stability, its benefits far outweigh its limitations when properly implemented. It enhances redundancy, improves availability, and supports the high-performance expectations of today’s digital networks.
As networking continues to evolve, BFD will remain a key technology for maintaining resilience, enabling automation, and ensuring uninterrupted connectivity across increasingly complex infrastructures.