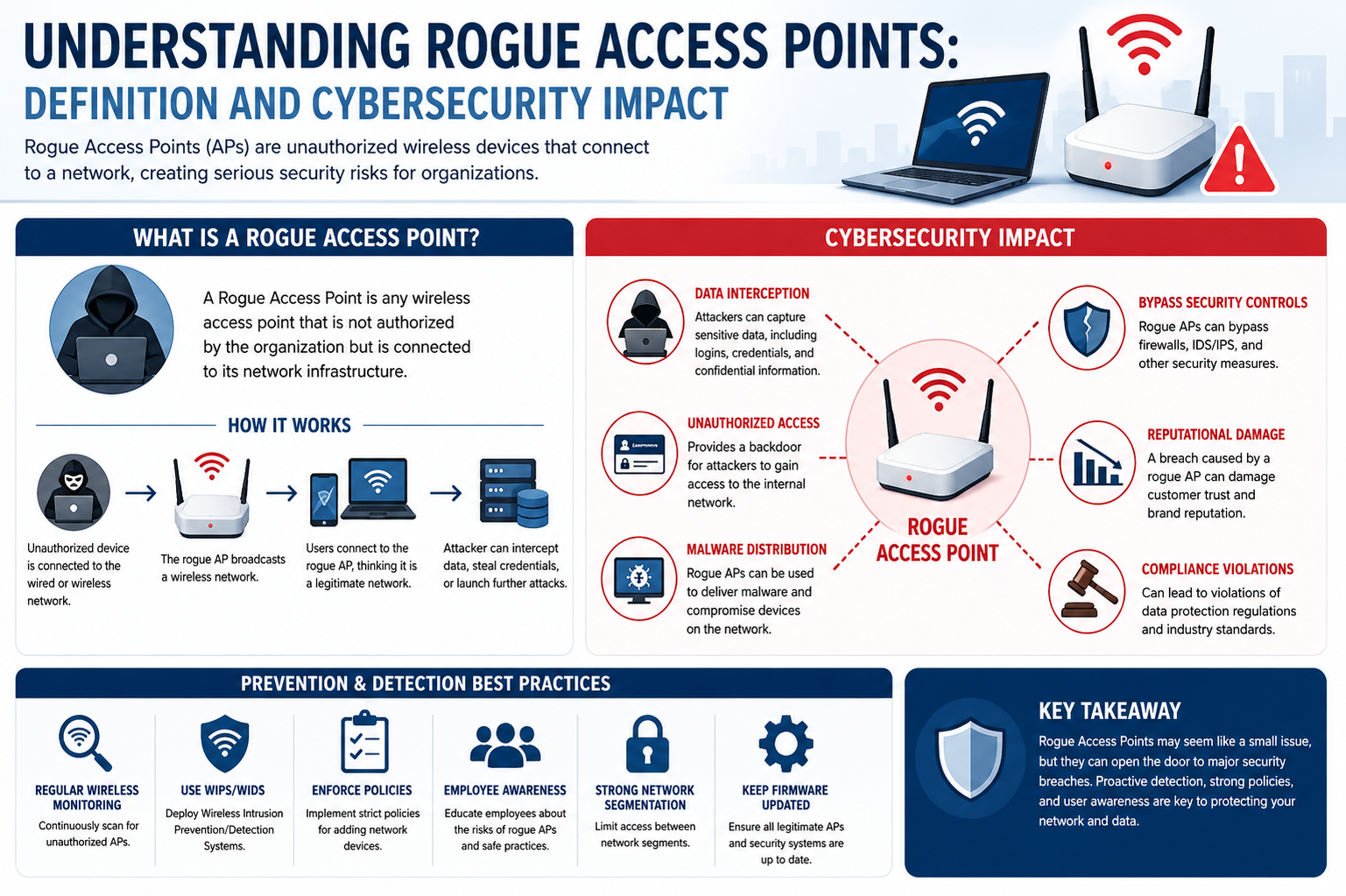
A rogue access point refers to any unauthorized wireless access point that is connected to a secure network without the knowledge or approval of the network administrator. These access points are typically introduced either intentionally by malicious actors or unintentionally by employees or users who seek easier network access. Despite appearing harmless or even useful, they create significant security vulnerabilities by bypassing established network security policies and controls. In modern cybersecurity environments, rogue access points are considered one of the most common and dangerous threats to organizational wireless infrastructure because they provide an uncontrolled gateway into internal systems.
A rogue access point can be a standalone wireless router, a mobile hotspot, or even a compromised device configured to share network connectivity. Once connected, it allows external users to connect to the internal network without authentication mechanisms enforced by enterprise security systems. This creates an invisible entry point that bypasses firewalls, intrusion detection systems, and other protective layers. Because these access points often operate outside the visibility of network monitoring tools, they can remain undetected for long periods, allowing attackers to exploit them for data theft, surveillance, or system compromise.
How Rogue Access Points Are Introduced
Rogue access points are introduced into networks in several ways, each presenting different levels of risk. One common scenario involves employees who connect personal wireless routers or mobile hotspots to the corporate network to improve convenience or network coverage. While this may seem harmless, it unintentionally extends the organization’s internal network beyond its secured boundaries. Another scenario involves attackers physically or remotely installing unauthorized devices within network range. These devices are often disguised to blend in with legitimate network infrastructure, making detection more difficult.
In some cases, attackers use a method known as “evil twin” attacks, where they create a wireless access point that mimics a legitimate network’s name and configuration. Unsuspecting users connect to this fake network, believing it to be safe. Once connected, attackers can intercept sensitive data, including login credentials, financial information, and internal communications. This technique is especially dangerous in environments where employees frequently use mobile devices or work remotely.
Security Risks Associated with Rogue Access Points
The presence of rogue access points introduces a wide range of cybersecurity risks. One of the most significant threats is unauthorized access to sensitive data. Since these access points often bypass authentication protocols, attackers can gain unrestricted access to internal systems. This can lead to data breaches, intellectual property theft, and exposure of confidential business information.
Another major risk is network monitoring evasion. Because rogue access points operate outside the official network infrastructure, traditional security tools such as firewalls and intrusion detection systems may not detect traffic passing through them. This allows attackers to operate stealthily within the network environment without triggering alerts. Over time, they can map the internal structure of the network, identify valuable assets, and exploit vulnerabilities.
Rogue access points also increase the risk of malware distribution. Once connected to the internal network, attackers can use these access points to spread malicious software across multiple devices. This can result in system corruption, data loss, and operational disruptions. In enterprise environments, such infections can spread rapidly, affecting critical systems and causing widespread downtime.
Additionally, rogue access points can be used for man-in-the-middle attacks. In this scenario, attackers intercept communication between users and network services. This allows them to capture sensitive data or even modify information in transit without detection. Such attacks are particularly dangerous in financial, healthcare, and government sectors where data integrity is crucial.
Impact on Organizational Security and Operations
The impact of rogue access points extends beyond technical vulnerabilities and directly affects organizational operations. One of the most immediate consequences is the compromise of network integrity. Once unauthorized access is established, the trust model of the entire network becomes unreliable. Security teams can no longer guarantee that internal communications or data transfers are secure.
Operational disruption is another significant impact. When rogue access points are discovered, organizations often need to conduct extensive network audits and shutdown procedures to isolate the threat. This can lead to downtime, reduced productivity, and delays in business operations. In industries where continuous system availability is essential, such disruptions can result in financial losses and reputational damage.
Rogue access points also contribute to compliance violations. Many industries are governed by strict data protection regulations that require organizations to maintain secure and monitored network environments. The presence of unauthorized access points can result in non-compliance, leading to penalties, legal consequences, and loss of customer trust. Even if no data breach occurs, the mere existence of such vulnerabilities can be considered a serious compliance failure.
Challenges in Detecting Rogue Access Points
Detecting rogue access points is a complex task due to their hidden and adaptive nature. One of the primary challenges is distinguishing between legitimate and unauthorized devices. In large organizations with multiple departments and network segments, the number of wireless devices can be extensive, making manual identification nearly impossible.
Another challenge is signal overlap. Rogue access points often operate on similar frequencies as legitimate networks, making them difficult to differentiate using basic scanning tools. Attackers may also configure these devices to reduce signal strength or limit broadcast visibility, further complicating detection efforts.
Dynamic network environments also contribute to the difficulty. With employees frequently connecting new devices, using mobile hotspots, and working remotely, network baselines are constantly changing. This makes it harder for security systems to identify anomalies that indicate the presence of rogue access points.
Techniques Used for Detection and Mitigation
To combat rogue access points, organizations rely on a combination of monitoring technologies and security policies. Wireless intrusion detection systems play a key role in identifying unauthorized devices by continuously scanning network environments for unknown or suspicious access points. These systems compare detected devices against a known list of authorized hardware to identify discrepancies.
Network segmentation is another important strategy. By dividing the network into isolated segments, organizations can limit the potential impact of unauthorized access. Even if a rogue access point is introduced, segmentation ensures that attackers cannot freely move across the entire network infrastructure.
Regular audits and physical inspections also help in identifying unauthorized devices. Security teams often conduct scheduled scans of physical locations to ensure that no unauthorized hardware has been connected to network ports. This is particularly important in office environments where employees may inadvertently introduce personal devices.
Employee awareness and training are equally important. Many rogue access points are introduced unintentionally due to lack of awareness about security policies. Educating employees about the risks associated with unauthorized devices helps reduce the likelihood of accidental network exposure.
Long-Term Cybersecurity Implications
The long-term implications of rogue access points are significant for any organization that relies on wireless connectivity. As networks become more complex and interconnected, the potential attack surface continues to grow. Rogue access points exploit this expansion by introducing uncontrolled entry points that weaken overall security architecture.
Over time, repeated exposure to such threats can erode trust in network systems and require organizations to invest heavily in advanced security infrastructure. This includes continuous monitoring systems, artificial intelligence-based anomaly detection, and stricter access control mechanisms.
In addition, the evolving nature of cyber threats means that rogue access points may become more sophisticated. Future implementations may involve stealthier hardware, encrypted communication channels, and automated attack mechanisms that make detection even more challenging. This reinforces the need for proactive security strategies rather than reactive responses.
Advanced Attack Methods Involving Rogue Access Points
Rogue access points are not limited to simple unauthorized network extensions; they are frequently used as part of more sophisticated cyberattacks. Attackers often combine them with social engineering, credential harvesting, and network reconnaissance techniques to maximize their effectiveness. One of the most common advanced methods is the creation of deceptive wireless networks that closely resemble legitimate organizational access points. These cloned networks are designed to trick users into connecting without suspicion, enabling attackers to silently intercept sensitive information.
In more targeted attacks, rogue access points are deployed within physical proximity of high-value environments such as corporate offices, research facilities, or financial institutions. Once deployed, they serve as persistent entry points into internal systems. Attackers may leave these devices hidden in ceilings, network closets, or even disguised as harmless office equipment. Once operational, they can maintain long-term access without requiring repeated physical presence.
Another advanced tactic involves the use of automated scripts running on rogue devices. These scripts can continuously scan for connected devices, collect credentials, and probe internal systems for vulnerabilities. Over time, this allows attackers to build a detailed map of the network structure, including identifying critical servers, databases, and administrative systems.
Role of Rogue Access Points in Data Exfiltration
One of the most damaging uses of rogue access points is data exfiltration. Once attackers gain access to a network through an unauthorized access point, they can begin silently extracting sensitive information. This process often occurs gradually to avoid detection. Instead of transferring large volumes of data at once, attackers may siphon small amounts over extended periods.
This technique makes detection significantly more difficult, especially in organizations that do not actively monitor outbound traffic patterns. Sensitive data such as customer records, financial transactions, intellectual property, and internal communications can all be targeted. In many cases, organizations remain unaware of the breach until the stolen data is later used or sold on underground markets.
Rogue access points also facilitate lateral movement within networks. After gaining initial access, attackers can move from one system to another, escalating privileges and gaining deeper control over the infrastructure. This increases the scale of potential data theft and makes remediation more complex.
Impact on Wireless Network Security Architecture
The existence of rogue access points forces organizations to rethink their entire wireless security architecture. Traditional perimeter-based security models are no longer sufficient because rogue devices operate inside the perimeter itself. This shifts the focus toward zero-trust security models, where no device is automatically trusted, even if it is connected to the internal network.
Wireless environments become particularly vulnerable because they rely on radio signals that extend beyond physical boundaries. This makes it easier for unauthorized devices to interact with internal systems from outside controlled spaces. As a result, organizations must implement stronger authentication mechanisms, encryption protocols, and continuous monitoring systems.
The integration of rogue access point detection into broader cybersecurity frameworks is also essential. Security systems must correlate wireless activity with network behavior, user authentication logs, and endpoint security data to identify inconsistencies. Without this integration, rogue devices can easily blend into normal network traffic.
Human Factors and Insider Threats
Human behavior plays a significant role in the proliferation of rogue access points. In many cases, employees unknowingly create security vulnerabilities by connecting personal devices to corporate networks. These actions are often driven by convenience, lack of awareness, or attempts to improve connectivity in poorly covered areas.
However, insider threats can also be intentional. Disgruntled employees or contractors may introduce rogue access points to gain unauthorized access or sabotage internal systems. Because these individuals already have legitimate access to physical premises, their actions are harder to detect and prevent.
Social engineering techniques further amplify this risk. Attackers may persuade employees to connect to unauthorized devices by posing as IT support staff or offering seemingly legitimate network improvements. Once trust is established, the rogue access point can be deployed without resistance.
Wireless Encryption and Its Limitations
While wireless encryption protocols such as WPA2 and WPA3 provide strong protection for legitimate networks, they do not fully eliminate the risk posed by rogue access points. This is because encryption primarily protects data in transit between authorized devices and access points, but it does not prevent users from connecting to unauthorized networks.
If a rogue access point is configured to mimic a legitimate network, users may unknowingly enter their credentials into a compromised system. Once credentials are captured, attackers can bypass encryption entirely by authenticating as legitimate users. This highlights the importance of not relying solely on encryption as a security measure.
Additionally, some older devices and legacy systems may not support modern encryption standards, creating further vulnerabilities. Attackers often exploit these weak points to establish unauthorized connections through rogue access points.
Network Monitoring and Behavioral Analysis
Modern cybersecurity systems increasingly rely on behavioral analysis to detect rogue access points. Instead of focusing solely on known device signatures, these systems analyze patterns of network activity to identify anomalies. For example, sudden changes in traffic flow, unusual authentication attempts, or unexpected device behavior can indicate the presence of unauthorized access points.
Machine learning techniques are also being used to improve detection accuracy. By training models on normal network behavior, systems can identify deviations that may indicate rogue activity. This approach is particularly useful in large and dynamic environments where manual monitoring is impractical.
However, attackers are also evolving their techniques to evade detection. Some rogue access points are programmed to mimic normal traffic patterns, making them harder to distinguish from legitimate devices. This ongoing adaptation creates a continuous challenge for cybersecurity professionals.
Physical Security and Environmental Controls
Physical security is a critical but often overlooked aspect of preventing rogue access points. Since these devices must be physically connected to a network or placed within wireless range, controlling physical access to infrastructure is essential. Secure server rooms, restricted access areas, and surveillance systems all play a role in reducing the risk of unauthorized device installation.
Environmental controls such as radio frequency monitoring can also help detect unauthorized wireless signals within a facility. These systems continuously scan for unknown access points and alert security teams when suspicious activity is detected. In high-security environments, such monitoring is often mandatory.
Regular inspections of network ports, wiring closets, and office spaces further reduce the likelihood of hidden rogue devices. Even simple physical checks can be effective in identifying unauthorized hardware before it becomes a major security issue.
Evolving Threat Landscape
The threat landscape surrounding rogue access points continues to evolve as technology advances. The increasing use of Internet of Things devices, remote work environments, and bring-your-own-device policies has expanded the potential attack surface significantly. Each new connected device introduces a potential entry point that can be exploited if not properly secured.
Attackers are also leveraging automation and artificial intelligence to enhance rogue access point attacks. Automated deployment tools allow them to quickly set up multiple unauthorized access points across different locations. AI-driven systems can also optimize attack strategies by identifying the most vulnerable targets within a network.
As organizations adopt more cloud-based and hybrid infrastructures, the boundaries of traditional networks continue to blur. This makes it even more challenging to maintain visibility over all connected devices and access points.
Mitigation Strategies and Defense Frameworks Against Rogue Access Points
Defending against rogue access points requires a layered security approach that combines technology, policy enforcement, and continuous monitoring. No single solution is sufficient because these threats operate at both physical and network levels. Effective mitigation begins with establishing strong visibility over all wireless activity within the organization. Without complete awareness of what is connected, where it is connected, and how it behaves, rogue access points can remain undetected for long periods.
A strong defense framework starts with centralized network management. By maintaining a complete inventory of all authorized access points, security teams can continuously compare detected wireless signals against a trusted baseline. Any device that does not match this approved list is flagged for investigation. This process must be continuous rather than periodic because rogue devices can be introduced at any time and may operate only briefly to avoid detection.
Another critical defense layer involves real-time wireless monitoring. Continuous scanning of radio frequency activity helps identify unauthorized transmissions within the network environment. Advanced monitoring systems can detect subtle anomalies such as unusual signal patterns, duplicate network identifiers, or unexpected changes in access point behavior. These indicators often reveal the presence of rogue devices even when they attempt to disguise themselves as legitimate infrastructure.
Strengthening Authentication and Access Control
One of the most effective ways to reduce the impact of rogue access points is to enforce strict authentication mechanisms. Multi-factor authentication adds an additional layer of security by requiring users to verify their identity through multiple methods before gaining network access. Even if credentials are intercepted through a rogue access point, attackers cannot easily bypass secondary authentication factors.
Network access control systems also play a vital role in restricting unauthorized connections. These systems evaluate each device attempting to connect to the network and determine whether it meets predefined security policies. Devices that fail compliance checks are either blocked or placed in restricted network segments with limited access. This reduces the risk of rogue access points being used as entry points into critical systems.
Strong encryption protocols further enhance security by ensuring that even if data is intercepted, it cannot be easily read or modified. However, encryption alone is not sufficient because rogue access points can still trick users into connecting to malicious networks before encryption becomes effective.
Role of Endpoint Security in Detection
Endpoint security solutions contribute significantly to identifying and mitigating rogue access point threats. Devices such as laptops, smartphones, and tablets often serve as the first point of interaction with wireless networks. By installing security agents on these devices, organizations can monitor connection behavior and detect suspicious network activity.
If a device connects to an unauthorized access point, endpoint security systems can trigger alerts or automatically disconnect from the suspicious network. These systems can also enforce policies that prevent devices from connecting to unknown wireless networks altogether. This reduces the likelihood of accidental exposure to rogue access points.
In addition, endpoint monitoring allows security teams to track historical connection patterns. If a device repeatedly connects to unknown networks, it may indicate either user negligence or malicious activity, both of which require investigation.
Network Segmentation as a Containment Strategy
Network segmentation is a powerful strategy for limiting the damage caused by rogue access points. By dividing a network into isolated segments, organizations can ensure that even if one segment is compromised, attackers cannot easily move laterally across the entire infrastructure.
Sensitive systems such as databases, financial applications, and administrative tools are placed in highly restricted segments with strict access controls. Even if a rogue access point provides entry into a less secure segment, attackers are prevented from reaching critical assets without additional authentication barriers.
Segmentation also improves visibility because it allows security teams to monitor traffic flows between different parts of the network. Unusual communication patterns between segments can indicate unauthorized access or lateral movement attempts.
Importance of Continuous Security Auditing
Regular security audits are essential for maintaining long-term protection against rogue access points. These audits involve systematic reviews of network configurations, access point inventories, and wireless activity logs. The goal is to identify inconsistencies, outdated devices, or unauthorized changes in network infrastructure.
Audits also help ensure compliance with internal security policies and external regulatory requirements. Many industries require organizations to maintain strict control over wireless access points, and failure to do so can result in penalties or loss of certification.
Physical audits complement digital monitoring by verifying that no unauthorized hardware has been installed in sensitive areas. This includes checking network closets, office spaces, and remote locations where rogue devices may be deployed unnoticed.
User Awareness and Behavioral Defense
Human awareness remains one of the most important defenses against rogue access points. Many security breaches occur not because of technological failure, but due to user behavior. Employees who are unaware of security risks may unknowingly connect to unauthorized networks or install personal devices that create vulnerabilities.
Security training programs help address this issue by educating users about the risks associated with rogue access points. Employees are taught how to recognize suspicious networks, avoid connecting to unknown Wi-Fi sources, and report unusual network behavior. Over time, this builds a culture of security awareness within the organization.
Behavioral policies also help reduce risk. For example, restricting the use of personal hotspots, limiting unauthorized device connections, and enforcing strict IT approval processes all contribute to reducing the likelihood of rogue access point introduction.
Advanced Detection Techniques Using Artificial Intelligence
Artificial intelligence and machine learning are increasingly being used to enhance rogue access point detection. These technologies analyze large volumes of network data to identify patterns that would be impossible for humans to detect manually. By learning what normal network behavior looks like, AI systems can quickly identify deviations that suggest unauthorized activity.
For example, if a new access point appears in an unusual location or begins transmitting at abnormal power levels, AI-based systems can flag it as suspicious. Over time, these systems become more accurate as they are exposed to more data and evolving attack patterns.
However, attackers are also using AI to improve stealth techniques. Some rogue access points are designed to mimic legitimate network behavior, making them harder to distinguish from authorized devices. This creates an ongoing competition between defensive and offensive technologies.
Integration with Zero Trust Architecture
The concept of zero trust security has become increasingly important in addressing threats like rogue access points. In a zero trust model, no device or user is automatically trusted, even if they are inside the network perimeter. Every access request must be continuously verified based on identity, device health, and contextual factors.
This approach significantly reduces the impact of rogue access points because even if a device connects to the network, it cannot access resources without proper authentication and authorization. Continuous verification ensures that trust is never assumed, only evaluated.
Zero trust architecture also emphasizes micro-segmentation, where access is granted only to specific resources rather than entire networks. This limits the potential damage caused by unauthorized access.
Long-Term Strategic Defense Planning
Protecting against rogue access points is not a one-time effort but an ongoing strategic process. As wireless technologies evolve, new vulnerabilities continue to emerge. Organizations must therefore adopt adaptive security strategies that evolve alongside emerging threats.
Investment in advanced monitoring tools, employee training, and infrastructure hardening is essential for maintaining long-term security. Regular updates to security policies ensure that new types of devices and attack methods are accounted for.
Collaboration between IT teams, security analysts, and management is also important. Effective defense requires coordination across all levels of the organization to ensure that security policies are properly implemented and enforced.
Incident Response and Containment of Rogue Access Points
When a rogue access point is detected, the speed and structure of the response determine how much damage can be prevented. Incident response in this context is not only about removing the unauthorized device but also about understanding how it was introduced, what it accessed, and whether any data was compromised. A delayed or uncoordinated response can allow attackers to maintain persistence within the network even after the device is physically removed.
The first step in containment is isolation. Once a rogue access point is identified, security teams typically segment or disable the affected network area to prevent further communication. This limits the ability of attackers to move laterally or continue exfiltrating data. At the same time, wireless scanning tools are used to determine the physical location of the device, which may involve tracing signal strength and triangulating its position within a building.
After isolation, forensic analysis becomes critical. Security teams examine logs from wireless controllers, authentication systems, and endpoint devices to reconstruct the timeline of events. This helps determine when the rogue access point first appeared, which devices connected to it, and whether any credentials were compromised during its operation. Without this analysis, organizations risk overlooking deeper compromises that may persist even after the device is removed.
Forensic Investigation and Evidence Collection
Digital forensics plays a central role in understanding rogue access point incidents. Investigators analyze packet captures, authentication logs, and traffic flows to identify abnormal patterns. For example, repeated failed login attempts followed by successful connections may indicate credential harvesting through a malicious access point.
Investigators also examine endpoint devices that connected to the rogue network. These devices may contain cached credentials, malware, or configuration changes introduced during the connection. By analyzing these artifacts, security teams can determine whether attackers gained deeper access beyond initial network entry.
Preserving evidence is also important for legal and compliance reasons. Proper chain-of-custody procedures ensure that collected data can be used in regulatory investigations or legal proceedings if necessary. This is especially important in industries handling sensitive personal or financial information.
Business and Financial Consequences
The impact of rogue access points extends beyond technical damage and often results in significant financial and operational consequences. One of the most immediate costs is incident response itself, which includes investigation, remediation, system restoration, and security upgrades. These activities require specialized expertise and can be resource-intensive.
Downtime is another major cost factor. When rogue access points are discovered, organizations may need to shut down parts of their network to prevent further compromise. This can disrupt business operations, delay services, and reduce productivity. In industries that rely heavily on real-time systems, even short interruptions can lead to substantial financial losses.
There is also the potential cost of data breaches. If sensitive information is stolen through a rogue access point, organizations may face legal liabilities, regulatory fines, and compensation claims. In addition, reputational damage can have long-term effects on customer trust and business relationships.
Regulatory and Compliance Implications
Many regulatory frameworks require organizations to maintain strict control over network access points. The presence of unauthorized wireless devices can lead to violations of these requirements, even if no actual data breach occurs. Compliance standards often emphasize continuous monitoring, access control, and documented security procedures.
When rogue access points are discovered, organizations may be required to report the incident to regulatory authorities, depending on the severity and type of data involved. Failure to do so can result in additional penalties. Regular audits and documentation help demonstrate that appropriate security measures were in place, even if a breach occurred.
Compliance also drives improvements in security practices. Organizations that operate in regulated environments are often required to implement stronger monitoring systems, employee training programs, and incident response plans specifically designed to address wireless threats.
Evolving Role of Wireless Security Policies
Wireless security policies form the foundation of preventing rogue access points. These policies define what types of devices are allowed to connect to the network, how authentication should be handled, and what monitoring mechanisms must be in place. However, static policies are no longer sufficient in dynamic environments where devices and users change frequently.
Modern wireless security policies are increasingly adaptive. They incorporate real-time risk assessments that evaluate each connection attempt based on device behavior, location, and historical activity. This allows organizations to respond more effectively to potential rogue access point activity.
Policy enforcement must also be automated to be effective at scale. Manual enforcement is not practical in large organizations with thousands of connected devices. Automated systems ensure that security rules are consistently applied across all network segments.
Integration with Enterprise Security Ecosystems
Rogue access point detection is most effective when integrated into a broader enterprise security ecosystem. This includes coordination between wireless monitoring systems, endpoint protection platforms, identity management systems, and security information and event management systems.
By correlating data from multiple sources, security teams can gain a more complete understanding of potential threats. For example, if a device connects to a rogue access point and simultaneously exhibits unusual login behavior, this combined signal can indicate a higher likelihood of compromise.
Integration also enables faster response times. When multiple systems share threat intelligence in real time, automated responses can be triggered immediately, such as disconnecting affected devices or blocking suspicious traffic.
Challenges in Large and Distributed Networks
Large organizations with distributed networks face additional challenges in managing rogue access points. Remote offices, branch locations, and mobile workforces increase the number of potential entry points for unauthorized devices. Maintaining consistent security policies across all locations becomes significantly more complex.
In such environments, centralized visibility is critical. Security teams must be able to monitor wireless activity across all locations from a single control system. Without this visibility, rogue access points may go undetected in remote or less monitored areas.
Cloud-based network management solutions are increasingly used to address this challenge. They provide centralized oversight while enabling local enforcement of security policies. However, they also introduce new dependencies on internet connectivity and external infrastructure.
Future Trends in Rogue Access Point Threats
The future of rogue access point threats is closely tied to the evolution of wireless technology. As new standards emerge and connectivity becomes faster and more widespread, attackers gain more opportunities to exploit wireless environments. The expansion of smart devices, industrial IoT systems, and edge computing increases the number of potential vulnerabilities.
One emerging trend is the use of highly portable and low-cost rogue devices. These devices can be easily concealed and deployed in high-traffic areas without detection. Combined with advanced encryption bypass techniques, they present a growing challenge for traditional security systems.
Another trend involves automated attack frameworks that can deploy and manage multiple rogue access points simultaneously. These systems can dynamically adjust behavior based on detection risk, making them harder to identify and neutralize.
Strategic Importance of Continuous Adaptation
Defending against rogue access points requires continuous adaptation rather than static defense strategies. As attackers refine their techniques, organizations must also evolve their detection and prevention capabilities. This includes adopting new technologies, updating security policies, and improving employee awareness.
Security is no longer a one-time configuration but an ongoing process of monitoring, analysis, and improvement. Organizations that fail to adapt risk falling behind increasingly sophisticated attack methods.
Conclusion
Rogue access points represent one of the most deceptive and high-impact threats in modern wireless cybersecurity environments. Although they often appear as simple unauthorized devices, their implications extend far deeper into network integrity, data security, and organizational trust. By creating hidden entry points into secure systems, they bypass conventional perimeter defenses and expose internal networks to external exploitation.
The severity of this threat lies in its invisibility and persistence. Unlike many cyberattacks that rely on direct intrusion or malware deployment, rogue access points operate quietly within or near trusted environments. This makes them difficult to detect using traditional monitoring tools alone. Once established, they can facilitate unauthorized access, data interception, credential theft, and long-term surveillance of internal communications.
Across all aspects of cybersecurity—prevention, detection, response, and recovery—rogue access points challenge the assumption that internal networks are inherently safe. They highlight the reality that trust must be continuously verified rather than assumed. This shift in mindset has become central to modern security strategies, particularly in environments where wireless connectivity is essential for daily operations.
The impact of these threats is not limited to technical systems. They influence business continuity, financial stability, regulatory compliance, and organizational reputation. A single unauthorized access point, if left undetected, can lead to widespread consequences ranging from operational disruption to long-term data exposure. This makes proactive defense not optional, but essential.
Effective protection requires a layered and adaptive security approach. Continuous monitoring of wireless environments, strict access control policies, endpoint protection, and real-time behavioral analysis all play a vital role in reducing risk. Equally important is human awareness, as many rogue access points are introduced unintentionally through careless or uninformed actions.