Kerberos authentication is a foundational security mechanism used in enterprise computing environments to ensure secure identity verification and controlled access to network resources. It is designed to eliminate the need for repeatedly transmitting passwords over the network, reducing the risk of interception and unauthorized access. Instead of relying on direct password validation for every request, it uses a system of encrypted tickets that prove a user’s identity and permissions.
The entire authentication process is based on a trusted third-party model where a centralized authority validates identities and issues time-sensitive credentials. These credentials are then used to access different services within the network without requiring the user to re-authenticate each time. This approach improves both security and efficiency in large-scale systems where users frequently access multiple resources.
Core Components of the Authentication Process
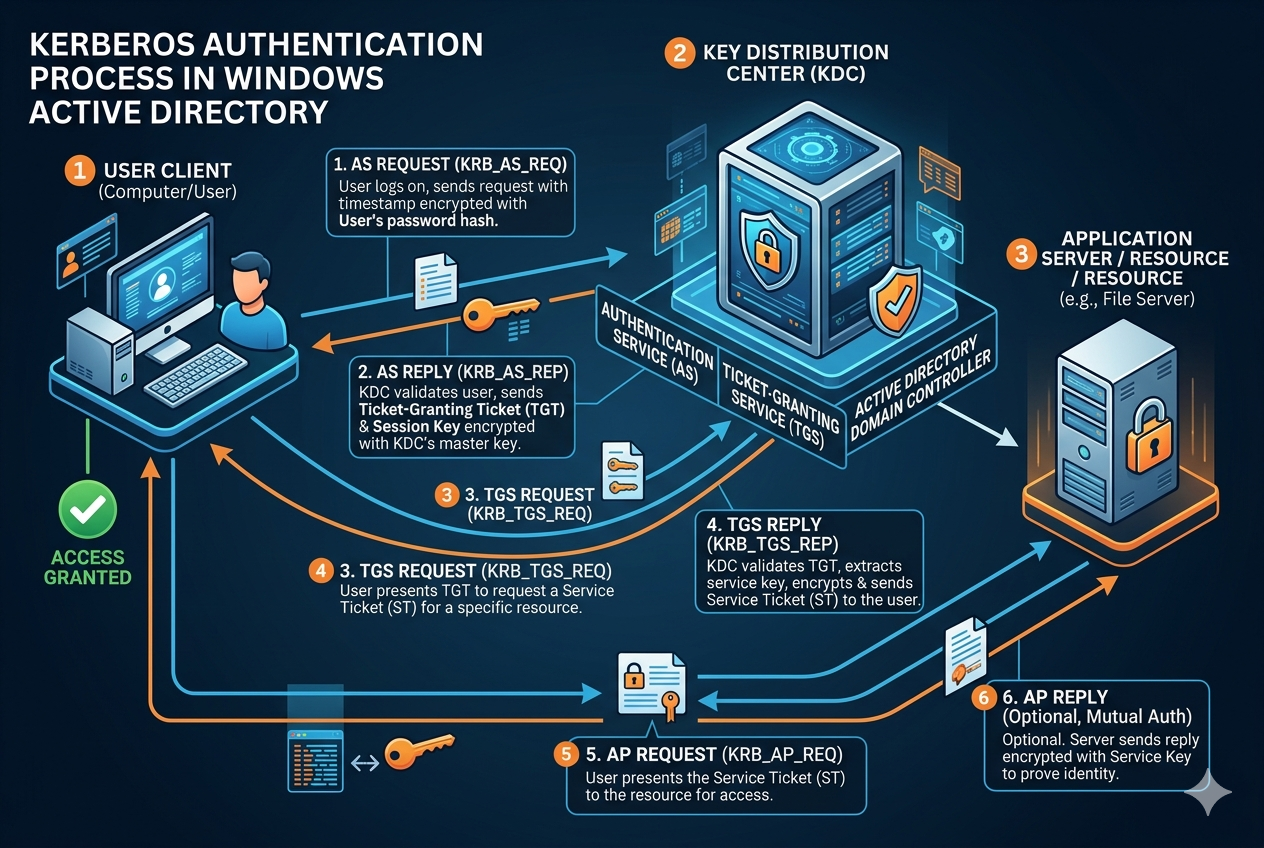
The Kerberos system is built around three main components: the client, the authentication service, and the service that provides access to resources. The client is the user’s device or system initiating the request. The authentication service is responsible for verifying the user’s identity and issuing initial credentials. The service component represents any network resource or application that the user wants to access.
Each of these components plays a specific role in ensuring that authentication is secure and seamless. The communication between them is encrypted and time-sensitive, which prevents replay attacks and unauthorized reuse of credentials. The system is designed to operate in a way that even if network traffic is intercepted, the sensitive information remains protected.
Initial Authentication and Credential Verification
The authentication process begins when a user logs into the system. At this stage, the client collects the user’s credentials, typically in the form of a username and password. Instead of sending the password directly across the network for every request, the system uses it only once to initiate the authentication process.
The authentication service verifies these credentials by comparing them against stored secure records. If the credentials are valid, the system generates a temporary authentication response. This response does not contain the password itself but instead includes a secure token that confirms the user’s identity. This step ensures that the password is never repeatedly exposed during subsequent interactions.
Generation of the Initial Authentication Ticket
After successful verification, the system issues an initial authentication ticket that serves as proof of identity. This ticket is encrypted and contains important information such as the user’s identity and a timestamp indicating when the ticket was issued. The ticket is stored securely on the client device and used for future authentication requests.
This initial ticket has a limited validity period, which helps reduce security risks. If the ticket expires, the user must re-authenticate to obtain a new one. This time-based mechanism ensures that even if a ticket is compromised, it cannot be used indefinitely.
Requesting Access to Network Services
Once the user has the initial authentication ticket, they can request access to various network services without re-entering credentials. When the user attempts to access a specific service, the client sends a request to the authentication system along with the existing ticket.
This request does not include the user’s password. Instead, it relies on the previously issued ticket to prove that the user has already been authenticated. This reduces the exposure of sensitive information and improves overall system security.
Issuance of Service-Specific Credentials
After verifying the initial ticket, the system generates a service-specific credential known as a service ticket. This ticket is created specifically for the requested resource and cannot be reused for other services. It includes encrypted data that confirms the user’s identity and their permission to access the requested service.
The service ticket also contains time-based restrictions, ensuring that it remains valid only for a limited period. This prevents unauthorized reuse and strengthens the security model by ensuring that access rights are continuously validated.
Secure Communication Between Client and Service
Once the service ticket is issued, the client presents it to the target service. The service decrypts the ticket and verifies its authenticity. If the ticket is valid and has not expired, the service grants access to the user.
This step ensures mutual trust between the client and the service. The service does not need to store or manage user passwords, and the client does not need to repeatedly authenticate. All communication is secured using encrypted tickets, which prevents interception or tampering.
Role of Time Synchronization in Security
One of the critical aspects of this authentication process is time synchronization. All tickets issued in the system are time-sensitive, meaning they are valid only within a specific time window. If the system clocks between different components are not synchronized, authentication failures may occur.
This time-based validation helps prevent replay attacks, where an attacker attempts to reuse intercepted authentication data. By ensuring that tickets expire quickly and are tied to specific timeframes, the system significantly reduces security vulnerabilities.
Session Management and Ticket Renewal
Once authentication is successful, a session is established between the client and the service. During this session, the service ticket allows continuous access without repeated authentication requests. However, if the session lasts longer than the ticket’s validity period, the ticket must be renewed.
Ticket renewal is handled seamlessly by the system using the initial authentication ticket, as long as it remains valid. This ensures that users can maintain long-running sessions without compromising security or repeatedly entering credentials.
Mutual Authentication Between Client and Service
An important feature of this authentication model is mutual verification. Not only does the service verify the client’s identity, but the client can also verify the authenticity of the service. This prevents impersonation attacks where a malicious entity might try to pose as a legitimate service.
Both sides rely on encrypted ticket data and shared secrets established during the authentication process. This mutual trust mechanism strengthens the overall security of the environment and ensures that both parties are legitimate.
Security Benefits of Ticket-Based Authentication
The ticket-based system provides multiple security advantages over traditional password-based authentication methods. Since passwords are not repeatedly transmitted across the network, the risk of interception is significantly reduced. Additionally, the use of encrypted and time-limited tickets ensures that even if data is captured, it cannot be reused.
Another major benefit is reduced password fatigue for users. Once authenticated, users can access multiple services without re-entering credentials. This improves productivity while maintaining strong security controls.
Handling Authentication Failures and Expired Tickets
If any part of the authentication process fails, access is denied. This may occur due to invalid credentials, expired tickets, or mismatched encryption keys. When a ticket expires, the user must re-authenticate to obtain a new one.
The system is designed to handle these failures gracefully while maintaining strict security standards. No partial or uncertain authentication is allowed, ensuring that only fully verified users gain access to resources.
Importance of Centralized Authentication Control
Centralized authentication ensures that all identity verification is managed by a single trusted authority. This simplifies security management and ensures consistent enforcement of access policies across the entire network.
It also allows administrators to control permissions, revoke access, and monitor authentication activities from a centralized point. This reduces complexity and improves overall security governance in large environments.
Service Ticket Presentation and Verification Process
After a service-specific ticket is issued, the client system presents it directly to the target service when access is requested. This ticket acts as a secure credential that confirms the user’s identity and their authorization to access the requested resource. The service does not need to ask for the user’s password or contact the central authentication system again for validation.
When the service receives the ticket, it decrypts the information using its own secret key that is shared with the authentication system. This decryption process ensures that the ticket is genuine and has not been altered. If the ticket is valid, the service extracts important details such as the user identity, session information, and validity period.
Once verified, the service grants access to the user, establishing a secure session between the client and the resource. This method ensures that authentication is both efficient and secure, reducing repeated authentication overhead while maintaining strict identity validation.
Role of Encryption in Securing Authentication Data
Encryption is a fundamental part of the Kerberos authentication process. Every ticket issued during authentication is encrypted using strong cryptographic algorithms. This ensures that even if the data is intercepted during transmission, it cannot be read or modified by unauthorized users.
The system uses different encryption keys for different stages of the process. The initial authentication ticket is encrypted in a way that only the authentication service can decrypt it. Similarly, service tickets are encrypted so that only the intended service can validate them.
This layered encryption approach ensures that sensitive data remains protected at all times. It also prevents attackers from impersonating users or services, as they would not have access to the required cryptographic keys.
Ticket Validity and Expiration Mechanism
A key feature of this authentication system is the use of time-limited tickets. Every ticket issued has a specific validity period after which it automatically becomes invalid. This prevents long-term misuse of authentication credentials in case they are compromised.
When a ticket expires, the client must request a new one using the previously obtained authentication credentials, provided they are still valid. This process ensures that authentication remains dynamic and continuously verified rather than static and permanent.
The expiration mechanism also reduces the risk of replay attacks, where an attacker attempts to reuse intercepted authentication data. Since expired tickets are no longer accepted, such attempts are automatically rejected by the system.
Mutual Trust Between Client and Service
The authentication system is designed to establish mutual trust between the client and the service. Not only does the service verify the identity of the client, but the client can also verify that it is communicating with a legitimate service.
This is achieved through encrypted ticket exchanges and shared cryptographic keys. When the service responds to the client, it can include encrypted data that only a legitimate client can decrypt. This ensures that both sides of the communication are authentic and trusted.
This mutual verification helps prevent man-in-the-middle attacks, where an attacker tries to intercept or impersonate communication between two parties.
Session Key Generation and Secure Communication
During the ticket issuance process, a session key is often generated. This session key is used to encrypt further communication between the client and the service during the active session. It ensures that all data exchanged after authentication remains secure.
The session key is unique to each session and is derived during the authentication process. It is not reused for other sessions or services. This isolation ensures that even if one session is compromised, it does not affect others.
By using session keys, the system avoids repeatedly using long-term credentials for communication, significantly improving security.
Handling Multiple Service Access Requests
In real-world environments, users often need access to multiple services within a short period. Instead of requiring full authentication each time, the system allows reuse of the initial authentication ticket to request multiple service tickets.
Each service ticket is specific to a particular resource, ensuring that access rights are strictly controlled. This means that even though the user is authenticated once, access to each service is individually verified and authorized.
This mechanism improves efficiency while maintaining strict security boundaries between different services.
Delegation and Impersonation Control
In some cases, a service may need to act on behalf of a user to access another service. This is known as delegation. The authentication system allows controlled delegation, where a service can use a user’s credentials under specific conditions.
However, this process is tightly controlled and requires explicit permissions. Without proper authorization, services cannot impersonate users or access resources on their behalf. This prevents unauthorized actions and ensures that user identity is not misused.
Delegation adds flexibility to the system while maintaining strict security controls.
Error Handling in Authentication Failures
If any part of the authentication process fails, the system immediately denies access. Failures can occur due to invalid tickets, expired credentials, incorrect encryption, or mismatched service keys.
When such failures happen, no partial authentication is allowed. The system ensures that access is either fully granted or completely denied, with no intermediate states.
This strict approach prevents security loopholes and ensures consistent enforcement of authentication policies.
Importance of Central Key Management
A critical part of the authentication system is secure key management. The central authentication service is responsible for generating, distributing, and managing cryptographic keys used throughout the process.
These keys are never exposed directly to users or services. Instead, they are used internally to encrypt and decrypt tickets and session data. Proper key management ensures that even if part of the system is compromised, the overall authentication framework remains secure.
Regular key rotation and secure storage practices further strengthen system security.
Scalability of the Authentication System
One of the strengths of this authentication model is its scalability. It is designed to handle large numbers of users and services without significant performance degradation. Since authentication is ticket-based, most operations do not require repeated communication with the central authentication service.
This reduces network load and allows the system to efficiently support enterprise-level environments with thousands of users and services operating simultaneously.
Security Advantages Over Traditional Authentication Methods
Compared to traditional password-based authentication systems, this model offers significantly higher security. Passwords are not repeatedly transmitted, reducing the risk of interception. Tickets are time-limited and service-specific, reducing the risk of misuse.
Additionally, mutual authentication and encryption ensure that both users and services can trust each other. These combined features make the system highly resistant to common network-based attacks.
Authentication Flow
The authentication process operates as a layered and highly secure system where identity verification is handled through encrypted tickets instead of direct password exchanges. Each stage of the process builds upon the previous one, starting from initial login verification, followed by ticket issuance, service-specific authentication, and secure session communication.
This structured approach ensures that users can seamlessly access multiple resources while maintaining strong security controls. The use of encryption, time-based validity, session keys, and mutual authentication makes the system both efficient and highly resistant to attacks in complex network environments.
Renewal of Tickets and Long-Running Sessions
In enterprise environments, users often remain logged in for extended periods while continuously accessing multiple services. Since Kerberos tickets have limited lifetimes, the system provides a controlled mechanism for ticket renewal without requiring the user to re-enter credentials repeatedly.
When the initial authentication ticket is still valid, it can be used to request new service tickets even after previous ones expire. This ensures continuity of access while maintaining strict security boundaries. However, once the authentication ticket itself expires, the user must perform a fresh login to obtain a new one.
This renewal system strikes a balance between usability and security by allowing uninterrupted workflows while ensuring that authentication remains time-sensitive and regularly validated.
Forwarding and Cross-Network Authentication
In complex network environments, users may need to access resources across multiple interconnected systems. The authentication process supports ticket forwarding, allowing a user’s authentication credentials to be securely passed to another system without exposing the original password.
This mechanism ensures that identity can be verified across different systems while maintaining encryption and trust boundaries. The forwarded ticket remains protected and retains its time-based restrictions, preventing unauthorized reuse in external environments.
Cross-network authentication also allows organizations with multiple connected environments to maintain a unified identity system, reducing the need for separate credentials in each system.
Replay Attack Prevention Mechanisms
One of the major security threats in authentication systems is replay attacks, where an attacker intercepts and attempts to reuse valid authentication data. The Kerberos process includes several built-in protections to prevent this.
Each ticket includes timestamps and expiration details, ensuring that old or reused tickets are automatically rejected. Additionally, session keys and encrypted authenticators are used to verify that each request is unique and originated from a legitimate client.
Even if an attacker captures a ticket, they cannot reuse it outside its valid time window or without the correct encryption keys. This makes replay attacks ineffective in properly secured environments.
Authenticator Usage for Additional Security
Along with tickets, the system uses a component called an authenticator. This is a small piece of encrypted data generated by the client for each request. It includes time-based information and is used to prove that the request is fresh and not replayed.
The authenticator is encrypted using the session key shared between the client and the service. When the service receives it, it decrypts and verifies that it matches the expected session context. This ensures that even valid tickets cannot be reused maliciously without the corresponding authenticator.
This layered validation adds an extra level of protection beyond ticket verification alone.
Separation of Authentication and Authorization
The authentication process confirms the identity of a user, but it does not directly determine what the user is allowed to do. Authorization is handled separately by the target service or system based on predefined access control rules.
Once a user is authenticated and presents a valid service ticket, the service checks whether the user has permission to access specific resources or perform certain actions. This separation ensures that identity verification and permission management remain independent but complementary processes.
This design improves security by ensuring that even authenticated users can only access resources they are explicitly authorized to use.
Role of the Key Distribution System
At the core of the authentication process is a centralized key distribution mechanism responsible for issuing and managing cryptographic keys used in ticket generation. This system ensures that both clients and services can securely communicate without exposing sensitive credentials.
The key distribution process is highly secure and operates under strict internal controls. Keys are never transmitted in plain form and are only used within encrypted ticket structures. This ensures that even if network traffic is intercepted, the underlying cryptographic material remains protected.
Proper key distribution is essential for maintaining trust across the entire authentication ecosystem.
Security Boundaries Between Services
Each service within the system operates with its own identity and encryption key. This creates strict security boundaries between different services, ensuring that a ticket issued for one service cannot be reused for another.
This separation prevents privilege escalation, where a user might attempt to use access from one service to gain unauthorized access to another. Each service independently validates incoming tickets and enforces its own access policies.
This model ensures that compromise of one service does not automatically compromise the entire system.
Caching of Tickets for Performance Optimization
To improve performance, clients often cache valid tickets locally. This allows them to reuse tickets for multiple requests without repeatedly contacting the authentication service. Cached tickets remain valid until they expire.
While caching improves efficiency, it is carefully controlled to ensure security is not compromised. Expired or invalid tickets are automatically discarded, and sensitive data is stored in protected memory regions.
This balance between caching and security helps maintain high performance in large-scale environments without weakening authentication guarantees.
Error Recovery and Reauthentication Process
When authentication failures occur due to expired tickets, invalid credentials, or network issues, the system requires the user to reauthenticate. This process involves obtaining a new authentication ticket and restarting the access flow.
The system is designed to recover gracefully from such failures without affecting other active sessions unnecessarily. Each authentication request is handled independently, ensuring that issues in one session do not disrupt the entire environment.
This fault-tolerant design improves reliability while maintaining strict security enforcement.
Importance of Secure Time Synchronization
Accurate time synchronization across all participating systems is critical for the authentication process. Since tickets rely heavily on timestamps and expiration times, even small differences in system clocks can cause authentication failures.
All systems must maintain closely synchronized clocks to ensure that ticket validation works correctly. If time discrepancies occur, tickets may be incorrectly rejected or accepted outside their intended validity period.
This dependency on time consistency reinforces the importance of secure and synchronized system infrastructure.
Defense Against Credential Theft
Because passwords are used only during initial authentication and are never transmitted again, the risk of credential theft during network communication is significantly reduced. Attackers cannot easily intercept reusable credentials since tickets replace traditional password-based authentication.
Even if a ticket is intercepted, its encrypted and time-limited nature makes it difficult to exploit. Combined with session keys and authenticators, this significantly reduces the attack surface for credential-based attacks.
This makes the system highly resistant to common security threats such as phishing and network sniffing.
Integration with Enterprise Security Policies
The authentication process can be integrated with broader security policies within an organization. Administrators can define rules for ticket lifetime, access permissions, and authentication strength based on organizational requirements.
This flexibility allows the system to adapt to different security environments, from highly restricted networks to more open enterprise infrastructures. Policy-based controls ensure that authentication behavior aligns with organizational security standards.
Final Extension Summary of the Authentication Flow
The extended authentication process demonstrates a highly structured and layered security model built around encrypted tickets, time-based validation, and mutual trust between systems. It ensures secure identity verification, controlled service access, and efficient session management without exposing sensitive credentials.
Through mechanisms like ticket renewal, replay protection, session keys, and strict service boundaries, the system maintains both strong security and operational efficiency. It is designed to function reliably in large, complex environments while minimizing risk and reducing authentication overhead.
Role of Pre-Authentication in Strengthening Security
Pre-authentication is an important step that ensures a user is legitimate before any authentication ticket is issued. Instead of allowing a system to request authentication blindly, the client must first prove knowledge of the correct credentials in a controlled way.
During this stage, the client sends encrypted information derived from the user’s password. The authentication system verifies this encrypted data without ever exposing or transmitting the actual password. If the verification succeeds, the system proceeds with issuing authentication credentials.
This step significantly reduces the risk of brute-force attacks, since attackers cannot repeatedly request tickets without first proving valid knowledge of credentials.
Protection Against Offline Password Attacks
One of the key security advantages of the authentication process is its resistance to offline password attacks. Since passwords are not transmitted directly and are instead used to derive cryptographic keys, attackers cannot easily capture usable password data from network traffic.
Even if encrypted authentication data is intercepted, it cannot be easily reversed into the original password due to strong encryption algorithms. Additionally, pre-authentication timestamps and session-specific data make repeated guessing attempts extremely difficult.
This design ensures that password-based attacks are significantly limited in effectiveness compared to traditional authentication methods.
Secure Exchange of Session Information
Once authentication is successful, session-related information is securely exchanged between the client and service. This includes session keys and encrypted identifiers that allow both parties to maintain a trusted communication channel.
The session key is especially important because it is used to encrypt all further communication within that session. This ensures that even after authentication is complete, data exchanged between client and service remains protected from interception or modification.
Each session key is unique, meaning that compromise of one session does not affect others.
Limited Scope of Service Tickets
Service tickets are intentionally designed to have a limited scope. Each ticket is valid only for a specific service and cannot be reused across different services. This ensures strict separation of access rights and prevents unauthorized privilege escalation.
Even if a ticket is intercepted, it cannot be used to access unrelated services. This design enforces strong boundaries between different resources in the system and reduces the impact of potential security breaches.
Ticket Encryption Layers and Key Hierarchy
The authentication process uses multiple layers of encryption to secure tickets. At the top level, a central authentication authority manages key distribution and ticket issuance. Below this, each service has its own unique key used to decrypt incoming service tickets.
This hierarchical key structure ensures that no single key compromise can expose the entire system. Instead, security is distributed across multiple layers, limiting the scope of potential attacks.
Each layer of encryption adds additional protection, making it extremely difficult for attackers to manipulate or forge valid authentication data.
Client-Side Ticket Management
On the client side, tickets are managed in a secure local cache. This cache stores authentication and service tickets temporarily for reuse during active sessions. Proper security measures ensure that this cached data is protected from unauthorized access.
The client system automatically tracks ticket expiration and removes invalid or expired tickets. This helps maintain a clean and secure authentication state without requiring user intervention.
Efficient ticket management also improves system performance by reducing the need for repeated authentication requests.
Service-Side Ticket Validation Process
When a service receives a ticket, it performs several validation steps before granting access. First, it decrypts the ticket using its own secret key. Then it checks the timestamp, expiration time, and authenticity of the ticket data.
The service also verifies that the ticket was issued specifically for it and not for another service. If any validation step fails, access is immediately denied.
This strict validation process ensures that only properly authenticated and authorized requests are accepted.
Role of Trust Relationships in Multi-System Environments
In environments where multiple systems are connected, trust relationships allow authentication to extend across different systems. These relationships enable a user authenticated in one system to access resources in another without needing separate credentials.
Trust relationships are carefully configured and rely on shared cryptographic understanding between systems. This allows secure cross-system authentication while maintaining strict control over identity verification.
Such configurations are commonly used in large enterprise environments where multiple authentication boundaries exist.
Handling Simultaneous Authentication Requests
The authentication system is designed to handle multiple simultaneous requests efficiently. Since most operations rely on ticket validation rather than repeated authentication checks, the system can scale to support a large number of users without performance degradation.
Each authentication request is processed independently, ensuring that heavy load on one part of the system does not affect others. This makes the system suitable for high-demand environments where thousands of users may be accessing services at the same time.
Security Benefits of Stateless Authentication Design
A major advantage of this authentication approach is its stateless design on the service side. Services do not need to store user credentials or maintain long-term session states. Instead, they rely entirely on ticket validation for each request.
This reduces memory overhead and improves security by minimizing stored sensitive data. Since services do not retain passwords or persistent authentication data, the attack surface is significantly reduced.
Stateless design also improves scalability and simplifies service architecture.
Protection Against Impersonation Attacks
Impersonation attacks occur when an attacker attempts to act as a legitimate user. The authentication system prevents this through encrypted tickets, session keys, and authenticators that bind identity to specific sessions.
Even if an attacker gains partial access to network data, they cannot successfully impersonate a user without the correct cryptographic keys and valid session context. Mutual authentication between client and service further strengthens protection against impersonation attempts.
Importance of Secure Ticket Lifecycles
Every ticket follows a defined lifecycle that includes issuance, usage, renewal, and expiration. This lifecycle ensures that authentication remains controlled and time-bound.
Once a ticket reaches the end of its lifecycle, it becomes invalid and cannot be reused. This prevents long-term exploitation of authentication data and ensures that access rights are continuously refreshed.
The lifecycle-based design also improves security auditing and monitoring capabilities.
Auditability and Security Monitoring
The authentication process supports detailed auditing of authentication events. Each ticket issuance, validation, and failure can be logged for security monitoring purposes.
This allows administrators to track unusual activity, detect potential attacks, and enforce compliance policies. Audit logs provide visibility into authentication behavior without exposing sensitive credentials.
Security monitoring plays an important role in identifying and responding to potential threats in real time.
Resilience in Distributed Network Environments
The authentication system is highly resilient in distributed environments where multiple systems operate across different locations. Since authentication is based on tickets rather than continuous communication with a central authority, it reduces dependency on constant connectivity.
This allows systems to continue functioning even if parts of the network experience temporary disruptions. Cached tickets and local validation help maintain access during short-term connectivity issues.
Authentication Architecture
The extended architecture of the authentication process demonstrates a highly secure, layered, and scalable identity management system. It combines pre-authentication, ticket-based access control, encryption hierarchies, and session-based security to ensure strong protection against a wide range of threats.
By eliminating repeated password transmission and relying on time-bound encrypted tickets, the system provides both security and efficiency. Its design supports large-scale enterprise environments while maintaining strict authentication integrity and minimizing exposure of sensitive credentials.
Conclusion
The Kerberos authentication process represents a secure and efficient framework for identity verification and access control in enterprise environments. Instead of relying on repeated password transmission, it uses encrypted tickets to confirm user identity and manage access to services. This approach significantly reduces the risk of credential theft and network-based attacks.
Throughout the process, security is maintained through multiple layers, including pre-authentication, time-limited tickets, session keys, and mutual verification between client and service. Each stage is carefully designed to ensure that only authenticated and authorized users can access specific resources, while preventing unauthorized reuse of credentials.
The system also improves performance by reducing authentication overhead. Once a user is initially verified, they can access multiple services using service-specific tickets without repeated logins. This makes the process both user-friendly and scalable for large environments.
Time-based validation plays a critical role in maintaining security, ensuring that all tickets expire after a defined period and cannot be reused indefinitely. Combined with encryption and strict key management, this prevents replay attacks and unauthorized access attempts.
Overall, the Kerberos authentication model provides a strong balance between security, scalability, and efficiency. Its structured ticket-based mechanism, mutual trust design, and centralized key management make it a reliable foundation for secure authentication in complex network systems.