Address Resolution Protocol (ARP) is one of the core protocols used in IPv4 networks to enable communication between devices at the local network level. Its primary role is to translate logical IP addresses into physical MAC addresses so that data can be delivered accurately within a local broadcast domain. While IP addresses help identify devices across different networks, actual data transfer on Ethernet networks depends on MAC addresses. ARP acts as the bridge between these two addressing systems, making seamless communication possible.
Fundamental Concept Behind ARP
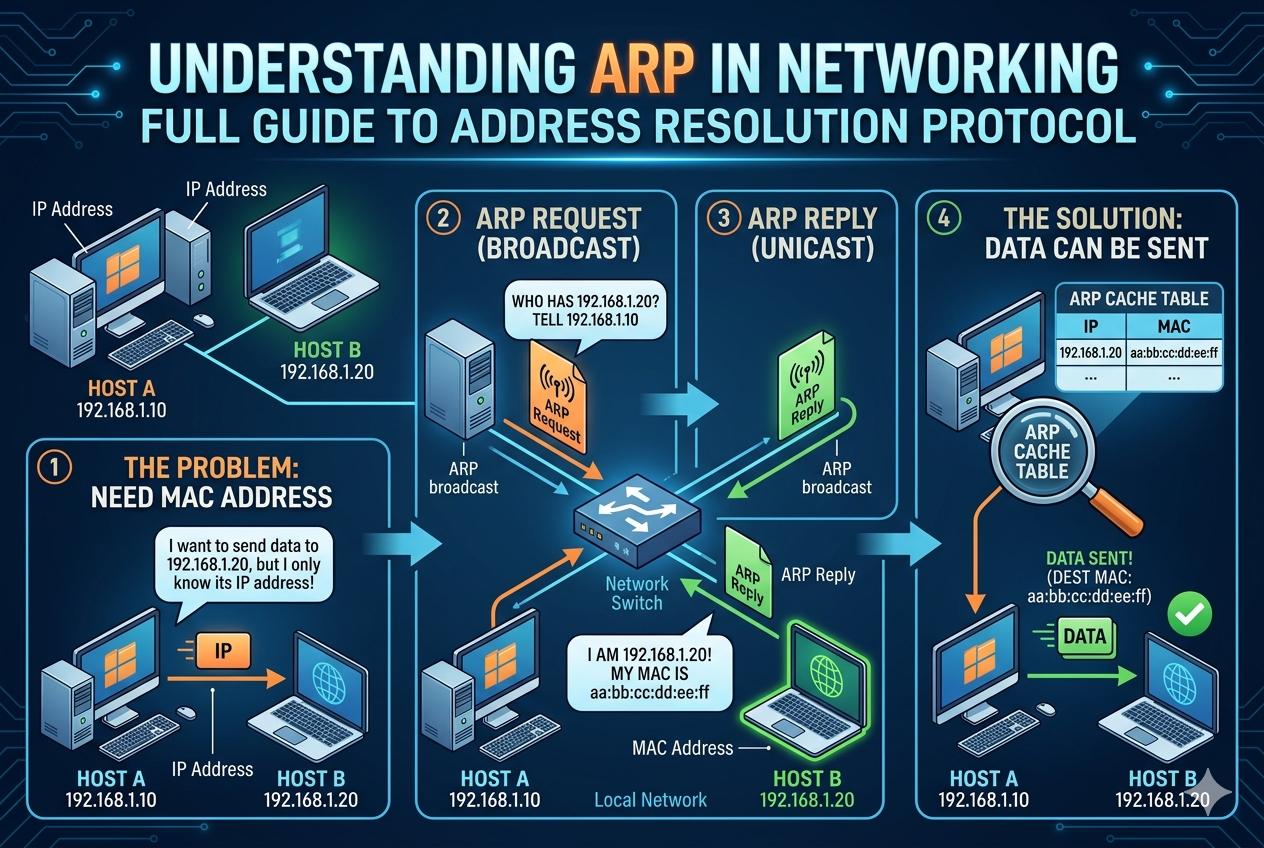
At its core, ARP exists because devices need a way to discover the hardware address of another device when only its IP address is known. When a computer prepares to send data, it must encapsulate that data into frames that contain destination MAC information. If the MAC address is unknown, ARP is triggered to resolve it. This process ensures that communication does not rely on manual configuration of hardware addresses, making networking dynamic and scalable.
Working Mechanism of ARP in Detail
When a device wants to communicate with another device on the same network, it first checks its ARP cache for an existing mapping between the IP address and MAC address. If no entry exists, the device generates an ARP request message. This request is broadcast to all devices in the local network segment. Every device receives the request, but only the device with the matching IP address responds. That device sends an ARP reply containing its MAC address, which is then stored in the requester’s ARP cache for future use.
Once the MAC address is obtained, the sender can encapsulate the data into an Ethernet frame and send it directly to the destination device. This entire process happens within milliseconds, ensuring smooth communication without user intervention.
Structure of ARP Communication
ARP communication is built around simple message formats. The ARP request includes the sender’s IP address, sender’s MAC address, and the target IP address. The target MAC address field remains empty because it is unknown at the time of the request. The ARP reply reverses this process by filling in the target MAC address and confirming the association between IP and MAC addresses. This exchange ensures that both devices can update their ARP caches accordingly.
Role and Function of ARP Cache
The ARP cache is a temporary storage table maintained by each device on the network. It holds recently resolved IP-to-MAC address mappings. This cache significantly improves network efficiency by reducing the need for repeated ARP requests. Entries in the ARP cache are not permanent; they expire after a certain period to ensure that outdated information does not cause communication errors. This dynamic nature allows networks to adapt to changes such as device reboots or IP reassignment.
Types of ARP Operations
Several variations of ARP exist to handle different networking scenarios. Standard ARP is used for basic IP-to-MAC resolution within a local network. Gratuitous ARP is a special case where a device announces its own IP-to-MAC mapping to the network without being asked. This helps detect duplicate IP addresses and update ARP caches across devices.
Proxy ARP is another variation where a router responds to ARP requests on behalf of another device. This is useful when two devices are on different physical networks but still need to communicate as if they are on the same local network. In this case, the router acts as an intermediary, forwarding packets appropriately.
Importance of ARP in Network Communication
ARP is essential for the functioning of Ethernet-based networks. Without ARP, devices would not be able to determine where to send data at the hardware level. Even though IP routing determines the path between networks, actual data delivery within a local segment depends on MAC addresses. ARP ensures that this final step of delivery is accurate and efficient.
It also supports scalability by eliminating the need for manual configuration of MAC addresses. As devices join or leave a network, ARP dynamically updates mappings, ensuring continuous communication without administrative overhead.
ARP in Switches, Routers, and Network Segmentation
Switches and routers interact with ARP differently based on their roles. A switch operates at the data link layer and uses MAC addresses to forward frames within the same network. It relies indirectly on ARP because devices connected through a switch must still resolve MAC addresses before communication.
Routers, on the other hand, operate at the network layer and separate broadcast domains. When a device needs to communicate with a device on another network, ARP is first used to find the router’s MAC address (default gateway). After that, the router takes responsibility for forwarding the packet to the destination network, potentially using ARP again on the destination side.
ARP Broadcast Domain Behavior
ARP requests are broadcast messages, meaning they are sent to all devices within the same local network segment. However, these broadcasts do not cross routers. This limitation ensures that ARP traffic remains contained within a single broadcast domain, preventing unnecessary network congestion across larger networks. Each network segment maintains its own ARP activity independently.
Security Risks Associated with ARP
Although ARP is essential for communication, it has no built-in authentication mechanism, making it vulnerable to attacks. One of the most common threats is ARP spoofing or ARP poisoning. In this type of attack, a malicious device sends false ARP messages to associate its MAC address with another device’s IP address. As a result, traffic intended for the legitimate device may be intercepted or redirected.
This can lead to serious issues such as data interception, session hijacking, or denial of service. Since ARP trusts all responses without verification, it becomes relatively easy for attackers to exploit this weakness in unsecured networks.
Methods to Reduce ARP Vulnerabilities
To mitigate ARP-related risks, networks often implement security measures such as static ARP entries, dynamic ARP inspection, and network segmentation. Static ARP entries manually define IP-to-MAC mappings, preventing unauthorized changes. Dynamic ARP inspection validates ARP packets against trusted databases before allowing them into the network.
Segmentation using VLANs also reduces the attack surface by limiting the range of broadcast domains, making it harder for malicious ARP traffic to spread across the entire network.
Difference Between ARP and IPv6 Neighbor Discovery
In IPv6 networks, ARP is replaced by a more advanced mechanism called Neighbor Discovery Protocol (NDP). Unlike ARP, NDP uses ICMPv6 messages and includes additional features such as router discovery, address autoconfiguration, and improved security options. This makes IPv6 networking more efficient and secure compared to traditional ARP-based IPv4 systems.
Real-World Importance of ARP
ARP is used continuously in everyday network operations without users even noticing it. Whether browsing the internet, sending files across a local network, or accessing shared devices like printers, ARP ensures that data reaches the correct hardware destination. It operates silently in the background, making modern networking possible and efficient.
Troubleshooting ARP Issues
Network administrators often use ARP-related tools to diagnose connectivity problems. If a device cannot communicate with another device on the same network, checking the ARP cache is one of the first troubleshooting steps. Missing or incorrect ARP entries often indicate misconfiguration, duplicate IP addresses, or hardware issues. Clearing the ARP cache can also resolve stale or corrupted entries.
Advanced Behavior of ARP in Complex Networks
As networks grow in size and complexity, the behavior of Address Resolution Protocol (ARP) becomes more dynamic and essential for maintaining efficient communication. In small networks, ARP operates in a straightforward request-and-reply model. However, in larger enterprise environments, multiple devices, subnets, routers, and switches interact with ARP in more layered ways. This creates a system where ARP is not just a simple lookup protocol but a continuously active background mechanism supporting nearly all local network traffic.
In complex environments, ARP tables on devices grow rapidly and must be carefully managed to avoid performance issues. Each entry in an ARP table represents a resolved IP-to-MAC mapping, and if these entries are not updated or refreshed, communication delays or failures can occur. Network devices constantly monitor traffic to update ARP caches, ensuring that communication remains accurate even as devices frequently join or leave the network.
ARP Interaction with Default Gateways
One of the most important uses of ARP in real-world networks is communication with default gateways. When a device needs to send data outside its local network, it does not directly resolve the destination device’s MAC address. Instead, it resolves the MAC address of the default gateway. This is because routers handle inter-network communication.
Once the device obtains the MAC address of the gateway using ARP, it sends all external traffic to that router. The router then takes responsibility for forwarding the packet to the appropriate destination network. This process highlights how ARP plays a key role not only in local communication but also in enabling internet-wide connectivity through indirect addressing.
Gratuitous ARP and Its Importance
Gratuitous ARP is a special form of ARP where a device sends an ARP announcement without being asked. It essentially broadcasts its own IP-to-MAC mapping to the network. This process serves multiple important functions in networking.
One key use is duplicate IP detection. When a device announces its IP address and receives a response indicating that another device is already using the same IP, a conflict is identified. This helps prevent network disruptions caused by duplicate addressing.
Another important use is updating ARP caches across the network. When a device changes its MAC address or network interface, gratuitous ARP ensures that all other devices update their records immediately. This prevents communication failures caused by outdated ARP entries.
Proxy ARP in Network Bridging
Proxy ARP is an advanced mechanism used when devices on different subnets need to communicate as if they are on the same network. In this case, a router or gateway responds to ARP requests on behalf of another device. It does this by replying with its own MAC address instead of the actual target device’s MAC address.
When the requesting device sends data to the proxy, the router forwards it to the correct destination network. This technique is useful in environments where network segmentation exists but seamless communication between segments is required without changing device configurations.
However, Proxy ARP can also introduce complexity and potential inefficiencies if overused. It increases reliance on intermediary devices and can make troubleshooting more difficult in large networks.
Dynamic Nature of ARP Tables
ARP tables are not static; they constantly evolve based on network activity. Each entry has a limited lifespan, known as a timeout period. If an entry is not used or refreshed within this period, it is removed automatically. This prevents outdated mappings from causing communication errors.
However, in highly active networks, ARP tables can grow very large, consuming memory and processing resources. To manage this, devices implement optimization techniques such as limiting ARP cache size and prioritizing frequently used entries. These mechanisms ensure that network performance remains stable even under heavy traffic conditions.
ARP and Broadcast Traffic Impact
Because ARP relies on broadcast messages, it inherently contributes to network traffic load. Every ARP request is sent to all devices within a local network segment. In small networks, this is negligible, but in large networks with hundreds or thousands of devices, excessive ARP broadcasts can lead to congestion.
To reduce this impact, modern network designs use techniques such as subnetting and VLAN segmentation. By dividing a large network into smaller broadcast domains, ARP traffic is contained and becomes more manageable. This improves overall network efficiency and reduces unnecessary load on devices.
ARP Spoofing and Attack Mechanisms
One of the most serious vulnerabilities of ARP is its lack of authentication. Because ARP trusts all incoming responses, it is vulnerable to spoofing attacks. In an ARP spoofing attack, a malicious device sends fake ARP replies to associate its MAC address with another legitimate device’s IP address.
This allows the attacker to intercept, modify, or block network traffic. In many cases, attackers use this method to perform man-in-the-middle attacks, where they secretly monitor communication between two devices without their knowledge.
Such attacks can lead to data theft, session hijacking, and service disruption. Since ARP operates at a fundamental level of networking, these attacks can be difficult to detect without specialized monitoring tools.
Techniques to Prevent ARP-Based Attacks
To protect networks from ARP spoofing, several security measures are implemented. One approach is using static ARP entries, where IP-to-MAC mappings are manually configured and cannot be changed dynamically. While this method is secure, it is not practical for large or frequently changing networks.
Another method is dynamic ARP inspection, where network devices verify ARP messages against trusted databases before allowing them to pass. This ensures that only valid ARP responses are accepted.
Network segmentation also plays an important role in limiting the impact of ARP attacks. By isolating devices into smaller groups, attackers are restricted to a limited portion of the network, reducing potential damage.
Role of ARP in Network Troubleshooting
ARP is also an important tool in diagnosing network problems. When communication issues occur within a local network, checking ARP tables is often one of the first troubleshooting steps. If a device cannot find the correct MAC address for a given IP, it will be unable to send data properly.
Network administrators often clear ARP caches to remove incorrect or outdated entries. This forces devices to rebuild fresh mappings, which can resolve connectivity issues. Monitoring ARP traffic can also help identify unusual behavior, such as duplicate IP addresses or unauthorized devices on the network.
ARP in Virtualized and Cloud Environments
In modern virtualized environments, ARP behaves slightly differently due to the presence of virtual machines and software-defined networking. Multiple virtual machines may share the same physical hardware, requiring efficient ARP handling within virtual switches.
Cloud environments further abstract networking layers, often relying on virtual networking systems that manage ARP internally. Despite this abstraction, the fundamental concept of IP-to-MAC resolution remains unchanged. ARP continues to operate behind the scenes, ensuring seamless communication between virtual and physical resources.
Relationship Between ARP and Other Network Protocols
ARP does not operate in isolation; it works closely with other network protocols. For example, it supports IP by enabling packet delivery at the data link layer. It also interacts with DHCP during network configuration, as devices often use ARP to verify assigned IP addresses.
Additionally, ARP complements routing protocols by ensuring that once a packet reaches the correct network, it can be delivered to the final destination device. Without ARP, higher-level protocols would not be able to complete their communication tasks effectively.
Limitations of ARP in Modern Networking
Despite its importance, ARP has several limitations. It is limited to IPv4 networks and does not support IPv6, where it has been replaced by Neighbor Discovery Protocol. ARP also lacks built-in security features, making it vulnerable to attacks.
Another limitation is scalability. In extremely large networks, ARP broadcast traffic can become inefficient. This has led to the development of more advanced networking techniques that reduce reliance on traditional ARP mechanisms.
ARP in Modern High-Speed Networks
In modern networking environments, Address Resolution Protocol (ARP) continues to function as a foundational mechanism even as network speeds and architectures evolve. High-speed Ethernet, cloud computing, and virtualized infrastructures have not replaced ARP but have instead adapted it to work within more complex and scalable systems. Although the core principle remains the same—mapping IP addresses to MAC addresses—the way ARP operates under heavy traffic conditions has become more optimized and controlled.
In high-speed networks, ARP efficiency is critical because even small delays in address resolution can affect performance-sensitive applications. Devices often rely heavily on cached ARP entries to avoid repeated broadcasts. Network hardware such as advanced switches and routers are also designed to process ARP requests quickly to minimize latency and maintain smooth communication.
ARP Optimization Techniques in Enterprise Networks
Large-scale networks use several optimization techniques to manage ARP traffic effectively. One common approach is increasing the ARP cache timeout in stable environments, allowing devices to retain address mappings longer and reduce repeated lookups. However, this must be balanced carefully because overly long cache times can lead to outdated information if devices change their network interfaces.
Another optimization method is ARP suppression, commonly used in virtualized and data center environments. Instead of allowing every device to broadcast ARP requests, network infrastructure handles requests centrally and responds on behalf of devices. This reduces broadcast traffic significantly and improves scalability.
Load balancing systems also integrate ARP behavior into their operations. When multiple servers share the same service IP, ARP responses may be controlled to distribute traffic efficiently across backend systems, ensuring balanced resource utilization.
ARP Behavior in Virtual Machines and Containers
In virtualized environments, ARP plays a slightly different but still essential role. Multiple virtual machines may exist on a single physical host, each with its own virtual network interface. These interfaces still require ARP to resolve MAC addresses within the virtual network layer.
Hypervisors manage ARP traffic internally using virtual switches. These switches handle ARP requests and replies between virtual machines without always sending broadcast traffic to the physical network. This internal handling improves performance and reduces unnecessary network load.
Containers also rely on ARP when connected through virtual bridges. Even though containers are lightweight compared to full virtual machines, they still require MAC address resolution to communicate within and outside their host environment. ARP ensures that container networking remains functional and consistent with traditional networking principles.
ARP and Network Address Translation Interaction
ARP and Network Address Translation (NAT) often work together in real-world networks. When devices inside a private network communicate externally, ARP is used to resolve the MAC address of the default gateway. Once the packet reaches the gateway, NAT modifies the IP address information to enable communication across the public network.
Although NAT operates at the IP level, it still depends on ARP for local delivery. Without ARP resolving the gateway’s MAC address, NAT would not receive the packet in the first place. This interdependence highlights how ARP supports broader networking functions beyond simple local communication.
Impact of ARP in Wireless Networks
In wireless networks, ARP behaves similarly to wired networks but must account for additional complexity such as signal variability and mobility. When devices move between access points, their MAC addresses may remain the same, but their network paths change dynamically. ARP must quickly adapt to these changes to maintain uninterrupted communication.
Wireless access points often assist in managing ARP traffic by maintaining updated client mappings. This helps reduce delays when devices roam across different areas of a wireless network. In dense environments like offices or campuses, efficient ARP handling is essential for maintaining stable connectivity.
ARP Cache Poisoning in Advanced Attacks
ARP cache poisoning is a more advanced form of ARP spoofing that targets multiple devices simultaneously. Instead of attacking a single host, attackers send false ARP messages across the network, corrupting multiple ARP tables at once. This can lead to widespread traffic interception or denial of service.
In some cases, attackers position themselves between entire communication paths, capturing sensitive information such as login credentials or session data. Because ARP operates without verification, these attacks can be difficult to detect without specialized monitoring systems.
Modern security systems often use anomaly detection to identify unusual ARP activity. Sudden changes in MAC address associations or frequent ARP updates can indicate malicious behavior, prompting further investigation.
Role of ARP in Network Redundancy and Failover Systems
In high-availability systems, ARP plays an important role in ensuring network continuity during failures. When a primary device fails, backup systems often take over its IP address. Gratuitous ARP is used in these scenarios to quickly inform the network of the new MAC address associated with the IP.
This rapid update ensures that traffic is redirected to the backup device without requiring manual intervention. In mission-critical systems such as financial networks or data centers, this behavior is essential for maintaining uninterrupted service.
ARP in Software-Defined Networking (SDN)
Software-defined networking introduces a more centralized approach to network control. In SDN environments, ARP traffic is often managed by a central controller rather than individual network devices. This allows for better visibility, control, and optimization of address resolution processes.
The controller can decide how ARP requests are handled, whether they should be broadcast, suppressed, or responded to directly. This reduces unnecessary network traffic and improves overall efficiency, especially in large-scale cloud infrastructures.
Evolution Toward ARP Alternatives
Although ARP is still widely used, modern networking is gradually evolving toward more secure and efficient alternatives in certain environments. In IPv6 networks, ARP is replaced by Neighbor Discovery Protocol, which offers additional features such as built-in security and improved scalability.
Despite this evolution, ARP remains deeply embedded in IPv4 systems, which still form a large portion of global network infrastructure. This ensures that ARP will continue to be relevant for many years, especially in legacy systems and hybrid environments.
Future Role of ARP in Networking
The future of ARP is closely tied to the continued use of IPv4 and hybrid networking environments. While newer protocols may eventually replace it entirely, ARP will likely remain in use for compatibility and transitional purposes.
In modern networks, ARP is increasingly being enhanced rather than replaced. Security improvements, caching optimizations, and intelligent traffic handling mechanisms are being layered on top of traditional ARP behavior to meet the demands of modern computing environments.
ARP in Large-Scale Internet Service Provider Networks
In internet service provider environments, Address Resolution Protocol operates at a much larger scale than in typical local networks. Even though ARP is technically limited to local broadcast domains, ISPs manage thousands of interconnected segments where ARP activity is constantly occurring. Every customer connection, whether residential or enterprise, still depends on ARP at the final delivery layer where IP packets are converted into MAC-level frames for transmission within local infrastructure.
Service providers often deploy highly optimized networking hardware that processes ARP requests at line speed. This ensures that even during peak traffic conditions, devices can quickly resolve addresses without introducing noticeable latency. In such environments, ARP is not just a background protocol but a critical performance factor that influences overall service quality.
ARP Scaling Challenges in Carrier Networks
As networks scale to millions of devices, ARP introduces several operational challenges. One of the primary issues is ARP table overflow, where devices receive more ARP entries than they can efficiently store. This can lead to memory pressure and slow lookup performance, especially in routers and aggregation switches handling large subscriber bases.
To address this, carriers implement techniques such as ARP rate limiting and hierarchical network design. Rate limiting prevents excessive ARP broadcasts from overwhelming network devices, while hierarchical design ensures that ARP traffic is contained within smaller, manageable segments instead of spreading across the entire infrastructure.
Another scaling issue is ARP storm conditions, where a sudden surge of ARP requests floods the network. This can happen during outages, misconfigurations, or device failures. Modern carrier-grade equipment includes mechanisms to detect and suppress ARP storms automatically to maintain stability.
ARP in Edge Computing Environments
Edge computing has introduced new dynamics to ARP behavior. In edge networks, processing is distributed closer to end users rather than centralized in data centers. This means ARP operations occur across many smaller nodes instead of a single large infrastructure.
Each edge node must handle ARP requests locally to minimize latency and ensure fast response times. Because edge environments often involve real-time applications such as video streaming, gaming, or IoT processing, efficient ARP resolution becomes essential for maintaining performance consistency.
In some edge architectures, ARP is partially offloaded to specialized hardware or virtual network functions. This reduces processing overhead on general-purpose systems and ensures faster packet forwarding.
ARP in Internet of Things (IoT) Networks
IoT environments introduce unique challenges for ARP due to the large number of low-power, resource-constrained devices. Many IoT devices have limited memory and processing capability, which makes maintaining large ARP tables inefficient.
To handle this, IoT networks often rely on simplified or optimized ARP behavior. Devices may frequently re-resolve MAC addresses instead of storing large caches, or rely on centralized gateways that manage ARP resolution on their behalf.
Since IoT devices often communicate intermittently, ARP traffic patterns in these networks are highly irregular. This requires careful network design to avoid unnecessary broadcast overhead that could drain device batteries or congest low-bandwidth connections.
ARP and Network Virtualization Overlays
Modern data centers frequently use network overlays such as VXLAN and GRE tunnels to separate logical networks from physical infrastructure. In these environments, ARP traffic must be carefully managed because broadcast messages are not always directly supported across overlay networks.
To solve this, ARP requests are often encapsulated and forwarded through tunnel endpoints. Some systems replace traditional ARP flooding with centralized mapping services that distribute IP-to-MAC information more efficiently.
This reduces broadcast dependency and improves scalability, especially in environments with thousands of virtual machines or containers communicating across multiple physical hosts.
ARP Convergence and Network Recovery
When network changes occur, such as link failures or device migrations, ARP plays a key role in convergence. Convergence refers to the time it takes for the network to stabilize and update all routing and addressing information after a change.
Gratuitous ARP is especially important during convergence events. It allows devices to immediately advertise new MAC-to-IP mappings, ensuring that other devices update their caches without waiting for timeouts. This significantly reduces downtime and prevents packet loss during transitions.
Fast convergence is critical in environments such as financial trading systems, cloud services, and real-time communication platforms where even small delays can have significant impact.
ARP Interaction with Load Balancers
Load balancers often manipulate ARP behavior to distribute network traffic across multiple backend servers. In such systems, a single virtual IP address may represent a group of servers. When an ARP request is made for that IP, the load balancer responds with a MAC address that helps direct traffic to the appropriate backend node.
This allows dynamic traffic distribution without requiring changes to client configurations. Depending on the load balancing algorithm, ARP responses may be adjusted to optimize performance, availability, or geographic distribution.
Some advanced load balancing systems use ARP in combination with health checks to ensure that only active servers receive traffic.
ARP in High-Availability Clusters
High-availability clusters rely heavily on ARP for failover mechanisms. When a primary node in a cluster fails, a secondary node takes over its IP address. To ensure uninterrupted communication, the new node sends ARP announcements to update all devices in the network.
This process ensures that traffic is immediately redirected to the active node without requiring manual reconfiguration. Without ARP updates, devices would continue sending packets to the failed node’s MAC address, resulting in service disruption.
Cluster systems often send repeated ARP announcements to ensure that all network devices update their caches consistently.
ARP Monitoring and Network Analytics
Network administrators use ARP monitoring as part of broader network analytics strategies. By analyzing ARP traffic patterns, they can gain insights into device behavior, network topology changes, and potential security threats.
Unusual ARP activity may indicate misconfigured devices, unauthorized connections, or ongoing attacks. For example, frequent changes in IP-to-MAC mappings can signal instability or malicious interference.
Advanced monitoring systems collect ARP logs and correlate them with other network data to provide real-time visibility into network health.
ARP and Quality of Service Considerations
Although ARP itself does not directly handle Quality of Service (QoS), its behavior can indirectly affect network performance. Excessive ARP traffic can compete with application data for bandwidth, especially in congested networks.
To maintain QoS, network devices may prioritize critical traffic over ARP broadcasts or limit the rate at which ARP requests are processed. This ensures that essential services such as voice communication or streaming are not disrupted by background protocol activity.
Efficient ARP handling contributes to overall network stability and predictable performance.
Evolution of ARP in Future Networking Architectures
As networking continues to evolve, ARP is gradually being adapted to fit more automated and intelligent systems. Future networks are expected to rely more heavily on centralized control, machine learning-based optimization, and software-defined architectures.
In such environments, ARP may become less dependent on broadcast mechanisms and more integrated into intelligent lookup services. However, its fundamental role of mapping network addresses to hardware identifiers will remain essential.
Even as new protocols emerge, ARP’s conceptual foundation continues to influence how modern networking systems are designed and optimized.
Conclusion
Address Resolution Protocol remains one of the most essential building blocks of IPv4 networking, acting as the hidden mechanism that enables devices to communicate at the local level. By translating IP addresses into MAC addresses, ARP ensures that data packets are delivered to the correct hardware destination within a network. Without this process, even correctly routed IP traffic would fail to reach its intended device on Ethernet-based systems.
Across all network types—small home setups, enterprise infrastructures, cloud platforms, and large-scale service provider systems—ARP continues to operate quietly in the background. It supports everything from simple file sharing to complex distributed computing by ensuring that devices can locate each other efficiently within local broadcast domains. Its request-and-reply structure, combined with temporary caching, allows communication to remain fast and responsive without requiring constant manual configuration.
Even as networking technologies evolve, ARP has adapted rather than disappeared. It works alongside modern systems such as virtualization platforms, load balancers, and software-defined networks, proving its continued relevance. At the same time, it has inspired more advanced protocols like IPv6 Neighbor Discovery, which address some of its limitations while preserving the same core concept of address resolution.
Despite its importance, ARP is not without weaknesses. Its lack of authentication makes it vulnerable to attacks such as spoofing and poisoning, which can compromise network security if not properly managed. This has led to the development of protective measures like dynamic inspection, monitoring tools, and network segmentation to reduce risks and maintain integrity.
Overall, ARP remains a fundamental protocol that bridges the gap between logical addressing and physical delivery. Its simplicity, efficiency, and universal adoption have made it a lasting component of modern networking, ensuring that communication between devices continues to function smoothly across virtually all IP-based systems.