In modern network security and data communication systems, protecting information while it travels across networks is a critical requirement. Whether data is moving between internal systems inside an organization or across public networks like the internet, encryption and secure encapsulation play a major role in ensuring confidentiality, integrity, and authenticity. Two commonly used approaches for securing data at the IP layer are transport mode and tunnel mode. Both are widely used in secure communication protocols, but they serve different purposes and operate in distinct ways.
Understanding the difference between these two modes is essential for network engineers, cybersecurity professionals, and system architects. Choosing the right mode depends on the environment, security requirements, and how data is expected to move between endpoints.
This discussion explores both modes in depth, explains how they work, compares their strengths and limitations, and helps you determine which one is more suitable for different scenarios.
Understanding Transport Mode
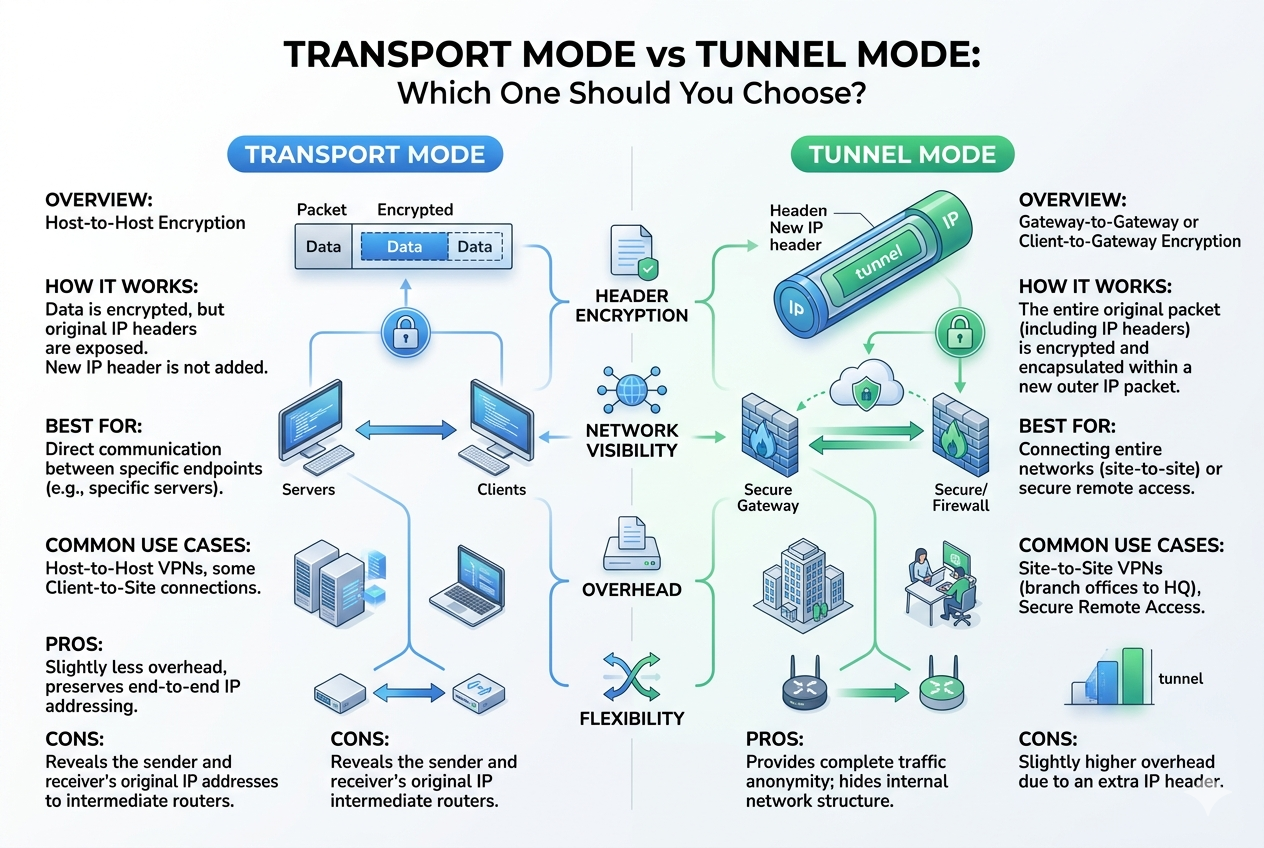
Transport mode is a method of securing communication where only the payload of the IP packet is encrypted or authenticated, while the original IP header remains intact. This means that the actual data being transmitted is protected, but the routing information is visible to intermediate devices.
In transport mode, the security protocol is inserted between the IP header and the transport layer protocol. As a result, the original IP address of the sender and receiver remains unchanged throughout the transmission process. This makes transport mode more efficient in terms of processing overhead since only the data portion is handled for encryption or authentication.
Transport mode is typically used for end-to-end communication between two hosts. For example, when two servers communicate directly and need to secure their data exchange without altering routing information, transport mode is often preferred.
Because the IP header is not encrypted, network devices such as routers can still read it and forward packets normally. However, this also means that some metadata about the communication is exposed, such as source and destination addresses.
Understanding Tunnel Mode
Tunnel mode, on the other hand, provides a more comprehensive level of protection. In this mode, the entire original IP packet, including both the header and payload, is encapsulated within a new IP packet. The original packet becomes completely hidden from intermediate devices.
A new IP header is added to route the encapsulated packet between tunnel endpoints. These endpoints are typically security gateways such as firewalls, VPN concentrators, or routers configured for secure communication.
Tunnel mode is widely used in scenarios where data must travel securely between two networks rather than between individual hosts. For example, it is commonly used in virtual private network configurations where entire networks need to communicate securely over the internet.
Since the original IP packet is fully encapsulated, tunnel mode provides stronger privacy and hides internal network structures from external observers. This makes it especially useful for site-to-site secure connections.
Key Differences Between Transport Mode and Tunnel Mode
The main difference between transport mode and tunnel mode lies in how much of the original packet is protected and how routing information is handled.
In transport mode, only the data portion is encrypted or authenticated, while the IP header remains visible. This allows for more efficient communication but provides less privacy regarding network structure.
In tunnel mode, the entire original packet is encapsulated, meaning both header and data are protected. A new outer header is added for routing, which hides internal addressing information.
Transport mode is generally used for direct host-to-host communication, while tunnel mode is used for network-to-network communication.
Another important distinction is overhead. Transport mode introduces less processing overhead because it modifies only part of the packet. Tunnel mode introduces more overhead due to encapsulation and additional headers, but it provides stronger security.
Security Considerations
From a security perspective, tunnel mode offers stronger protection because it hides both the data and the original IP structure. This makes it harder for attackers to analyze traffic patterns or identify internal network architecture.
Transport mode, while still secure in terms of payload encryption, exposes IP addressing information. This can potentially allow attackers to perform traffic analysis or identify communication endpoints.
However, transport mode still ensures data integrity and confidentiality, making it suitable for trusted environments where endpoints are already secure.
Tunnel mode is often preferred in untrusted or public network environments where additional protection is required to shield internal systems.
Performance and Efficiency
Performance is another major factor when choosing between these two modes. Transport mode is generally more efficient because it involves less processing overhead. Since only the payload is encrypted or authenticated, packet handling is faster, and latency is reduced.
Tunnel mode requires additional processing to encapsulate and decapsulate packets, which can introduce some performance overhead. However, modern hardware and optimized security appliances have significantly reduced this impact.
In environments where high throughput and low latency are critical, transport mode may be more suitable. In contrast, tunnel mode is preferred when security is prioritized over performance.
Use Cases of Transport Mode
Transport mode is commonly used in scenarios where end-to-end security is required between two specific devices. Some typical use cases include:
It is used for securing communication between two servers within a trusted network environment. It is also used in applications where direct host communication must be protected without changing routing behavior.
Another use case is in secure application-level communication where encryption is required only for payload data while preserving network routing efficiency.
Transport mode is often chosen in internal enterprise networks where devices already exist within a controlled infrastructure.
Use Cases of Tunnel Mode
Tunnel mode is widely used in scenarios where entire networks need to communicate securely over untrusted networks such as the internet.
One of the most common applications is virtual private networking, where two different office locations are connected securely. In this case, all traffic between the networks is encapsulated and encrypted.
Tunnel mode is also used in scenarios where remote users connect securely to a corporate network through a secure gateway. It ensures that all traffic passing through the tunnel is protected from external interception.
Additionally, tunnel mode is useful in cloud networking, where secure communication between different virtual networks is required.
Advantages of Transport Mode
Transport mode offers several advantages, particularly in terms of efficiency and simplicity. It introduces lower overhead, making it faster and more suitable for high-performance systems.
It is easier to implement in environments where only endpoint security is required. Since it does not modify the original IP header, it works seamlessly with existing routing infrastructure.
Transport mode also reduces complexity in packet handling, making it suitable for lightweight security applications.
Disadvantages of Transport Mode
Despite its advantages, transport mode has limitations. The most significant drawback is that it exposes IP header information, which can be analyzed by attackers.
It is also not suitable for securing entire networks or protecting internal infrastructure details. Its use is limited to host-to-host communication, which restricts its flexibility.
In environments requiring strong privacy and anonymity, transport mode may not provide sufficient protection.
Advantages of Tunnel Mode
Tunnel mode provides a higher level of security by encapsulating the entire original packet. This ensures that both data and addressing information are protected.
It is ideal for connecting separate networks securely over public infrastructure. It also hides internal network topology, which enhances security against targeted attacks.
Tunnel mode supports a wide range of secure communication scenarios, making it more versatile in enterprise and cloud environments.
Disadvantages of Tunnel Mode
The primary disadvantage of tunnel mode is increased overhead. Encapsulation and additional processing can impact performance, especially in high-traffic environments.
It also introduces additional complexity in configuration and management compared to transport mode.
In some cases, troubleshooting network issues can be more difficult due to the extra layer of encapsulation.
How to Decide Between Transport Mode and Tunnel Mode
Choosing between transport mode and tunnel mode depends on several factors, including security requirements, network architecture, and performance needs.
If the communication is between two secure endpoints within the same trusted environment, transport mode is often sufficient. It provides efficient and direct protection for data without unnecessary overhead.
If the communication involves different networks or traverses untrusted environments, tunnel mode is generally the better choice. It ensures complete protection of both data and addressing information.
Security requirements should always be the primary consideration. If confidentiality and network hiding are critical, tunnel mode is preferred. If performance and efficiency are more important, transport mode may be more appropriate.
Common Mistakes in Choosing Modes
One common mistake is using transport mode in environments where network-level protection is required. This can expose sensitive network information.
Another mistake is overusing tunnel mode in scenarios where simple host-to-host encryption would be sufficient. This can lead to unnecessary performance degradation.
Proper evaluation of the network structure and security requirements is essential before selecting a mode.
Deeper Understanding of How Transport Mode Works in Practice
Transport mode operates in a way that focuses strictly on protecting the actual data being transmitted between two endpoints. In real-world implementations, this means that when a packet is created, its payload is encrypted or authenticated while the IP header remains untouched. Because the header is left intact, intermediate networking devices such as routers and switches can still read essential routing information and forward the packet without any additional processing requirements.
This structure makes transport mode particularly efficient in environments where latency and performance matter. Since there is no need to create an additional outer packet layer, the system avoids extra computational overhead. This efficiency is one of the key reasons transport mode is still widely used in controlled and trusted environments.
However, the visibility of the IP header introduces a certain level of exposure. While the data itself is protected, metadata such as source and destination addresses, packet size, and routing behavior can still be observed. In many internal networks, this is acceptable because the infrastructure is already secured and monitored. But in more exposed environments, this limitation becomes more significant.
Transport mode is also tightly coupled with end-to-end security principles. This means that the protection is established directly between the communicating hosts rather than through intermediary devices. As a result, both endpoints must be capable of handling encryption and decryption processes, which places more responsibility on the end systems themselves.
How Tunnel Mode Functions in Real Deployments
Tunnel mode works differently by introducing a layer of encapsulation around the original IP packet. Instead of modifying just the payload, it takes the entire original packet and places it inside a new packet. This process effectively hides all original addressing information from external observers.
When a packet enters a tunnel, it is wrapped with a new IP header that is used solely for routing between tunnel endpoints. These endpoints are typically secure gateways, such as dedicated security appliances or VPN concentrators. Once the packet reaches the destination gateway, the outer header is removed, and the original packet is restored for final delivery.
This method creates a virtual pathway between two points, making it appear as though the communicating networks are directly connected even if they are separated by the public internet. Because of this abstraction, tunnel mode is commonly used to build secure connections between entire networks rather than individual systems.
One of the most important aspects of tunnel mode is its ability to conceal internal network structure. External observers cannot easily determine how many devices exist within the protected network or how they are organized. This significantly enhances security posture by reducing exposure to reconnaissance attacks.
Tunnel mode also enables centralized security enforcement. Since traffic passes through defined tunnel endpoints, security policies can be applied consistently at these points. This makes it easier to manage encryption, authentication, and access control at scale.
Architectural Differences in Packet Handling
The difference in packet structure between transport and tunnel mode leads to different architectural behaviors in networks. In transport mode, the packet retains its original structure with minimal modification. Only the payload section is altered for security purposes, while routing remains unchanged.
In tunnel mode, however, the packet is fully encapsulated. This means there are effectively two layers of IP headers: an outer header used for routing between gateways, and an inner header that remains hidden until the packet reaches its destination endpoint. This layered structure introduces additional processing steps at both encapsulation and decapsulation stages.
Because of this difference, tunnel mode is more resource-intensive. Each packet must be processed twice—once when entering the tunnel and once when exiting it. Despite this, modern networking hardware and optimized encryption engines have made this process efficient enough for large-scale deployment.
Transport mode, by contrast, avoids this dual processing model. It modifies the packet in place and forwards it directly through the network, resulting in lower latency and reduced CPU usage. This makes it more suitable for high-speed environments where performance is a priority.
Security Depth and Exposure Levels
Security depth varies significantly between the two modes. Transport mode provides encryption for the data itself but does not obscure communication patterns. This means that while attackers cannot easily read the content of the message, they may still analyze traffic flow, timing, and endpoint relationships.
Tunnel mode provides a deeper level of security by hiding both content and structure. Because the original packet is fully encapsulated, external observers cannot see internal IP addresses or determine communication patterns within the protected network. This makes traffic analysis significantly more difficult.
In environments where privacy and anonymity are critical, tunnel mode offers a clear advantage. It reduces the attack surface by hiding internal network architecture and making it harder for attackers to map systems.
However, this does not mean transport mode is insecure. It still provides strong encryption for the payload and ensures that data cannot be tampered with during transmission. Its limitation lies in visibility rather than data protection.
Scalability and Network Design Considerations
From a network design perspective, tunnel mode offers greater flexibility in connecting multiple networks across different geographic locations. It allows organizations to extend their internal network across public infrastructure without exposing internal systems directly.
This makes it highly scalable for enterprise environments that operate across multiple regions or rely on cloud-based infrastructure. By creating secure tunnels between different locations, organizations can maintain a unified network experience.
Transport mode, however, is more limited in scalability when it comes to inter-network communication. Since it is designed primarily for host-to-host communication, it does not naturally extend to multi-network architectures. It works best within a single controlled environment where endpoints are known and managed.
Despite this limitation, transport mode can still scale effectively within internal systems. It is often used in microservices architectures, where secure communication between individual services is required without introducing unnecessary network complexity.
Impact on Network Visibility and Monitoring
Transport mode allows for greater visibility into network traffic because the IP header remains intact. This can be beneficial for monitoring, logging, and troubleshooting purposes. Network administrators can analyze traffic flows more easily and detect anomalies based on routing information.
Tunnel mode reduces visibility because the original packet is hidden inside an outer packet. While this improves security, it can make monitoring more challenging. Network tools may only see encrypted tunnel traffic without insight into the actual communication inside.
To address this, organizations often implement monitoring at tunnel endpoints rather than within the tunnel itself. This ensures that security visibility is maintained without compromising encryption.
Reliability and Fault Handling
Both modes are generally reliable, but their behavior in fault conditions differs. In transport mode, because there is no encapsulation layer, packet loss or errors are handled in a straightforward manner by the underlying network protocols.
In tunnel mode, issues can sometimes be more complex to diagnose because problems may occur either in the outer transport layer or within the encapsulated payload. This requires more advanced troubleshooting techniques and better visibility at tunnel endpoints.
However, tunnel mode also provides resilience in multi-network environments by allowing secure communication paths to remain stable even when underlying routing paths change.
Hybrid Usage in Modern Networks
In many modern systems, transport mode and tunnel mode are not used in isolation. Instead, they are often combined depending on specific requirements. For example, transport mode may be used within internal systems for efficient host-to-host communication, while tunnel mode is used for external or cross-network connections.
This hybrid approach allows organizations to balance performance and security effectively. Critical internal services benefit from the efficiency of transport mode, while sensitive cross-network communication is protected using tunnel mode.
This layered strategy is especially common in cloud-native environments, where services are distributed across multiple infrastructure zones.
Final Insight on Selection Strategy
Choosing between transport mode and tunnel mode is not simply a technical preference but a strategic decision based on risk, architecture, and operational requirements. Transport mode emphasizes speed and efficiency, making it suitable for controlled environments with trusted endpoints. Tunnel mode emphasizes security and isolation, making it ideal for distributed systems and untrusted networks.
A well-designed network often incorporates both modes to achieve an optimal balance. Understanding when and where to apply each mode ensures better performance, stronger security, and more efficient network design overall.
Performance Trade-offs in Real-World Environments
When comparing transport mode and tunnel mode in practical deployments, performance differences become more noticeable under heavy network load. Transport mode generally delivers faster packet processing because it avoids additional encapsulation steps. Each packet is modified only at the payload level, which reduces CPU usage and minimizes latency. This makes it particularly suitable for environments where high-speed communication is essential, such as internal application clusters or real-time data systems.
Tunnel mode introduces extra processing overhead due to the encapsulation and decapsulation of entire IP packets. Every packet must be wrapped with a new header before transmission and then unwrapped at the destination. While this adds computational work, modern hardware acceleration and optimized security appliances have significantly reduced the impact. Still, at scale, tunnel mode may require more resources compared to transport mode.
Despite the overhead, tunnel mode is often justified in scenarios where security requirements outweigh performance concerns. The trade-off is intentional: additional processing is accepted in exchange for stronger isolation and confidentiality.
Role of Transport Mode in Secure Endpoints Communication
Transport mode is most effective when both communication endpoints are fully trusted and securely managed. In such cases, there is no need to hide routing information because the network itself is considered safe. The focus is on protecting the integrity and confidentiality of the data being exchanged.
This makes transport mode ideal for applications such as secure database connections, internal API communication, and service-to-service encryption within a controlled environment. Since both endpoints are known and verified, exposing IP header information does not typically introduce significant risk.
Another advantage in endpoint communication is simplicity. Transport mode does not require additional infrastructure such as VPN gateways or tunneling devices. This reduces configuration complexity and simplifies network architecture.
Role of Tunnel Mode in Network Interconnection
Tunnel mode plays a critical role in connecting entire networks across untrusted or public infrastructure. Instead of focusing on individual devices, it secures communication between network gateways. This allows multiple devices within one network to communicate securely with another network without requiring individual encryption sessions for each device.
This approach is widely used in enterprise environments where branch offices need to connect securely to a central headquarters. It ensures that all internal communication between networks remains encrypted and protected from external interception.
Tunnel mode also supports dynamic and distributed environments. As organizations move toward cloud-based infrastructure, tunnel mode provides a reliable method for connecting virtual networks across different regions and providers.
Impact on Network Architecture Design
Transport mode encourages a flatter security model where protection is applied directly between endpoints. This simplifies architecture but requires that every communicating system be individually secured. As a result, transport mode is often used in environments where system boundaries are clearly defined and controlled.
Tunnel mode supports a more layered architecture. Security is applied at network entry and exit points rather than at each individual device. This allows centralized control over security policies and reduces the need for individual configuration on every host.
From an architectural perspective, tunnel mode enables segmentation of networks into secure zones. Each zone can communicate with others through controlled and encrypted tunnels, reducing exposure and improving overall security posture.
Encryption Scope Differences
One of the most important distinctions between the two modes is the scope of encryption. In transport mode, encryption is limited to the payload of the packet. This ensures that the message content remains secure while leaving routing information visible.
In tunnel mode, encryption extends to the entire original packet, including both header and payload. This provides a higher level of confidentiality because even metadata about communication is protected.
This difference has significant implications in environments where metadata sensitivity is high. For example, in industries where communication patterns themselves must remain confidential, tunnel mode provides stronger protection.
Compatibility with Network Devices
Transport mode is generally more compatible with existing network infrastructure because it does not alter the original IP header. Routers and intermediate devices can process packets normally without requiring special handling.
Tunnel mode, however, requires support for encapsulation and decapsulation at designated endpoints. While most modern networking devices support this functionality, it still introduces additional configuration requirements.
This means transport mode can often be deployed more quickly in legacy environments, whereas tunnel mode may require more planning and infrastructure support.
Reliability in Dynamic Networks
In highly dynamic networks where routes frequently change, tunnel mode offers more stability. Since the tunnel endpoints remain fixed, the secure communication path is maintained even if underlying routing changes occur.
Transport mode is more dependent on the stability of the direct path between endpoints. If routing changes affect the communication path, it may impact performance or require re-establishment of secure sessions.
This makes tunnel mode more suitable for distributed systems where network conditions are less predictable.
Scenarios Favoring Transport Mode
Transport mode is preferred in scenarios where communication is strictly between known and trusted systems. It is commonly used in environments where internal traffic must be secured without introducing additional complexity.
It is also suitable for applications requiring low latency and high throughput. Financial systems, real-time analytics platforms, and internal microservice communication often benefit from transport mode due to its efficiency.
In addition, transport mode is often chosen when network transparency is required for monitoring or auditing purposes. Since routing information remains visible, it supports easier diagnostics and traffic analysis.
Scenarios Favoring Tunnel Mode
Tunnel mode is preferred when communication crosses untrusted or public networks. It is especially useful when entire networks need to be securely connected without exposing internal structures.
It is commonly used in remote access solutions, site-to-site connectivity, and cloud interconnectivity. Any scenario where data must traverse external infrastructure benefits from the additional protection tunnel mode provides.
Tunnel mode is also ideal when privacy and anonymity are priorities. By hiding both data and network structure, it significantly reduces exposure to external analysis.
Operational Complexity Considerations
Transport mode is operationally simpler because it requires fewer components and less configuration. It can be implemented directly at the host level without additional infrastructure.
Tunnel mode introduces more operational complexity due to the need for secure endpoints, tunnel management, and potential key exchange mechanisms. However, this complexity is often offset by centralized control and improved security management.
Organizations must balance operational overhead with security requirements when selecting between the two modes.
Hybrid Security Strategies in Practice
In many real-world systems, both transport and tunnel modes are used together to create layered security. Transport mode is applied within internal systems to secure service communication, while tunnel mode is used at network boundaries to protect data in transit between environments.
This layered approach ensures that security is maintained at multiple levels without sacrificing performance where it is not needed. It also allows organizations to adapt security policies based on risk exposure.
Such hybrid designs are common in modern cloud architectures, where workloads are distributed across multiple environments and require different levels of protection.
Real-World Security Strategy Alignment
In practical cybersecurity planning, the choice between transport mode and tunnel mode is rarely made in isolation. Instead, it is aligned with broader security strategies that define how data should move across systems, networks, and administrative boundaries. Organizations typically classify traffic based on sensitivity, trust level of endpoints, and exposure to external networks.
Transport mode is aligned with internal trust-based security models. In these environments, systems are assumed to be part of a controlled domain where identity, access, and behavior are already governed by strict policies. Because of this controlled environment, it becomes acceptable to leave routing information visible while focusing protection on the data itself.
Tunnel mode aligns with perimeter-based or zero-trust-inspired designs where networks cannot inherently trust external pathways. In these cases, every packet is treated as potentially exposed, and full encapsulation becomes necessary to ensure no metadata leakage occurs during transit.
This strategic alignment ensures that both modes are not just technical options but part of a larger security philosophy.
Scalability in Enterprise and Cloud Environments
As organizations scale, the demands on their network security architecture increase significantly. Transport mode scales efficiently within localized environments because it requires minimal additional infrastructure. Each host handles its own encryption, and communication remains direct and lightweight.
However, as systems expand across multiple regions, data centers, or cloud providers, the limitations of transport mode become more apparent. Managing individual secure connections between every endpoint becomes increasingly complex and difficult to maintain.
Tunnel mode addresses this scalability challenge by introducing centralized secure gateways. Instead of securing every individual connection, entire networks are connected through encrypted tunnels. This reduces configuration overhead and simplifies large-scale deployment.
In cloud environments, tunnel mode is especially important because resources are often dynamically created and destroyed. Maintaining secure network boundaries through encapsulated tunnels allows for flexible scaling without compromising security.
Operational Visibility and Control
Transport mode provides higher operational visibility because routing information remains accessible. This makes it easier for network administrators to monitor traffic flows, diagnose issues, and analyze system performance. Since packets are not fully encapsulated, traditional monitoring tools can inspect communication patterns more effectively.
Tunnel mode reduces visibility at intermediate points because the original packet is hidden inside an encrypted structure. While this enhances security, it shifts monitoring responsibility to tunnel endpoints. This means organizations must implement visibility tools at entry and exit points rather than relying on intermediate network observation.
This shift in visibility model requires careful planning. Security teams must ensure that logging, monitoring, and anomaly detection systems are properly integrated at tunnel boundaries to maintain operational awareness.
Latency Sensitivity and Application Requirements
Different applications have varying sensitivity to latency, and this plays a key role in selecting between transport and tunnel modes. Transport mode introduces minimal delay because it avoids additional encapsulation steps. This makes it suitable for latency-sensitive applications such as voice communication, real-time analytics, and high-frequency transaction systems.
Tunnel mode introduces additional processing delays due to encapsulation and encryption overhead. While this delay is often minimal in modern systems, it can still impact performance in extremely time-sensitive environments.
However, for most business applications, this difference is negligible compared to the security benefits tunnel mode provides. As a result, tunnel mode remains widely used even in performance-sensitive environments where security is a priority.
Flexibility in Network Topology
Transport mode works best in stable and predictable network topologies where endpoints remain constant. It assumes that communication paths are direct and well-defined. This makes it less flexible in environments where devices frequently change location or network configuration.
Tunnel mode offers greater flexibility because it abstracts the underlying network structure. By creating a virtual secure connection between endpoints, it allows communication to continue even when physical or logical network paths change.
This flexibility is especially valuable in modern distributed systems where workloads may move between data centers or cloud regions dynamically. Tunnel mode ensures that secure connectivity is maintained regardless of underlying infrastructure changes.
Administrative Overhead and Maintenance
Transport mode has lower administrative overhead because it requires fewer configuration components. Once endpoints are configured, communication can proceed with minimal ongoing management.
Tunnel mode requires more ongoing maintenance because tunnels must be established, monitored, and occasionally reconfigured. Key management, tunnel health monitoring, and endpoint synchronization all add to administrative workload.
However, this additional complexity also provides more centralized control. Administrators can enforce policies at tunnel endpoints rather than managing each individual connection separately. This centralized approach often improves long-term manageability in large environments.
Security Risk Exposure Comparison
From a risk perspective, transport mode exposes more metadata about communication. While the data remains encrypted, attackers may still analyze traffic patterns, timing, and endpoint relationships. In some threat models, this information alone can be sensitive.
Tunnel mode significantly reduces this risk by hiding both payload and metadata. External observers see only encrypted tunnel traffic without insight into internal communication structure.
This difference becomes critical in environments where even communication patterns must remain confidential. In such cases, tunnel mode provides a stronger security boundary.
Choosing Based on Organizational Needs
The decision between transport and tunnel mode ultimately depends on organizational priorities. If the primary goal is efficiency, low latency, and simplicity within a trusted environment, transport mode is often the best choice.
If the goal is to protect communication across untrusted networks, secure entire network segments, or hide infrastructure details, tunnel mode becomes the preferred solution.
Many organizations adopt a mixed approach, using transport mode internally and tunnel mode externally. This hybrid strategy allows them to optimize both performance and security without compromising either requirement.
Conclusion
Transport mode and tunnel mode represent two fundamental approaches to securing network communication, each designed for different operational needs. Transport mode focuses on efficiency by securing only the data payload while leaving routing information visible. It is best suited for controlled environments where endpoints are trusted and performance is a priority.
Tunnel mode provides comprehensive protection by encapsulating entire packets, including headers and payloads, within a new secure layer. This approach hides both data and network structure, making it ideal for untrusted networks, distributed systems, and cross-network communication.
Neither mode is universally superior. Instead, their effectiveness depends entirely on context. Transport mode excels in simplicity, speed, and endpoint-level security, while tunnel mode excels in privacy, isolation, and network-level protection.
Modern network architectures rarely rely on just one approach. Instead, they combine both modes strategically to balance performance and security requirements. Understanding when to apply each mode is essential for designing secure, scalable, and efficient communication systems in today’s complex digital environments.