Trunking is built on a simple but powerful idea: instead of creating separate physical pathways for every network segment, multiple logical paths are carried over a single physical connection. This becomes extremely important in environments where networks are large, dynamic, and constantly expanding. Without trunking, network infrastructure would require a massive number of cables and interfaces, making it inefficient, expensive, and difficult to manage.
At its core, trunking enables logical separation over shared physical infrastructure. This means that while devices may share the same cable or link, they can still behave as if they are operating on separate networks. This separation is achieved through tagging and identification mechanisms that allow network devices to distinguish between different types of traffic.
Difference Between Trunk Ports and Access Ports
In Ethernet-based networks, switch ports typically operate in two main modes: access mode and trunk mode. An access port carries traffic for a single VLAN and is usually connected to end devices such as computers, printers, or IP phones. It does not carry any tagging information because it only belongs to one network segment.
A trunk port, on the other hand, is designed to carry traffic for multiple VLANs simultaneously. It is commonly used between switches or between switches and routers. The trunk port adds or interprets VLAN tags in each frame so that multiple virtual networks can share the same physical link without mixing their traffic.
This distinction is essential for understanding how modern switched networks maintain both efficiency and segmentation at the same time.
How VLAN Tagging Enables Trunking
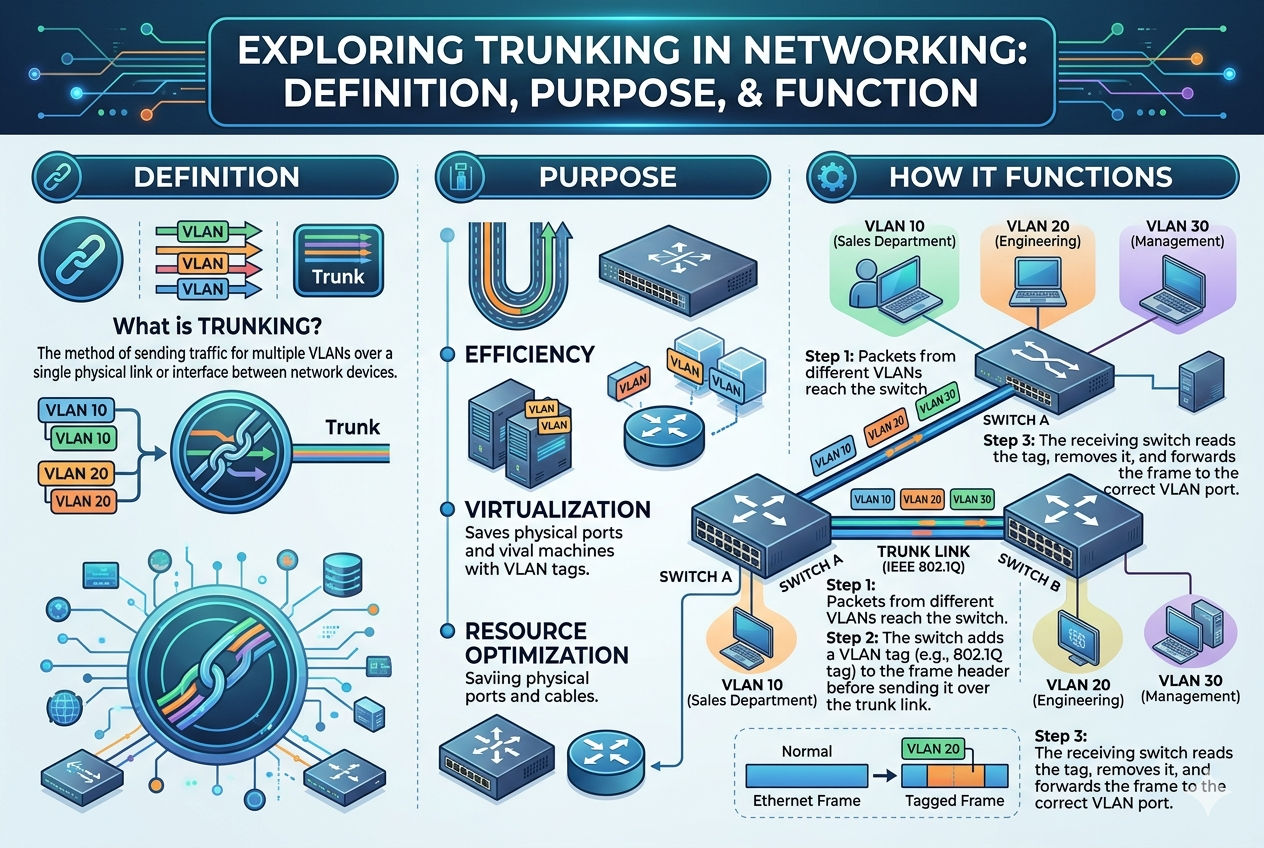
VLAN tagging is the foundation of trunking in Ethernet networks. When data is transmitted across a trunk link, each frame is marked with a VLAN identifier. This identifier tells the receiving device which VLAN the frame belongs to, ensuring proper forwarding and isolation.
The most widely used tagging method is IEEE 802.1Q. This standard inserts a small tag into the Ethernet frame that carries VLAN information. When a switch receives a tagged frame, it reads the VLAN ID and forwards it only to ports that belong to that VLAN. If the frame reaches a device that does not understand tagging, the tag is removed or ignored depending on configuration.
This process allows multiple VLANs to coexist on a single physical link without interference.
IEEE 802.1Q and Its Role in Modern Networks
IEEE 802.1Q is the dominant protocol used for VLAN trunking today. It defines how VLAN information is inserted into Ethernet frames and how devices should interpret that information. The standard introduced the concept of a “tagged” frame, which includes a VLAN identifier within the Ethernet header.
One of the key advantages of 802.1Q is its compatibility with almost all modern networking equipment. It allows seamless communication between devices from different manufacturers while maintaining consistent VLAN behavior.
Another important feature is the concept of a native VLAN. Frames belonging to the native VLAN are sent without tagging. This is useful for backward compatibility but must be configured carefully to avoid security risks or misrouting issues.
Trunking Between Switches in Enterprise Networks
In enterprise environments, trunk links are most commonly used to connect switches. Instead of creating separate physical connections for each VLAN between switches, a single trunk link carries all VLAN traffic. This dramatically reduces cable complexity and improves scalability.
For example, if a company has multiple departments such as HR, Finance, and IT, each department may have its own VLAN. Instead of connecting each VLAN separately between switches, a trunk link carries all VLAN traffic simultaneously. The receiving switch then separates the traffic based on VLAN tags.
This design makes it easier to expand networks because adding a new VLAN does not require new physical connections—only configuration changes.
Trunking in Router and Switch Communication
Trunking is also used between routers and switches, especially in scenarios involving inter-VLAN routing. In such setups, a single physical connection between a router and a switch can carry traffic for multiple VLANs.
The router uses logical subinterfaces, each assigned to a different VLAN. When traffic arrives from the switch, the router reads VLAN tags and forwards packets appropriately between networks. This allows communication between VLANs without requiring multiple physical router interfaces.
This method is often referred to as “router-on-a-stick” because a single physical interface handles multiple logical connections.
Role of Trunking in Network Scalability
One of the most important advantages of trunking is scalability. As organizations grow, their network requirements also expand. Without trunking, each new VLAN would require dedicated physical links, quickly becoming impractical.
Trunking solves this by allowing new VLANs to be added logically without changing physical infrastructure. This makes network expansion faster, cheaper, and easier to manage. It also allows administrators to restructure networks without physically rewiring devices.
In large data centers and enterprise environments, this scalability is essential for maintaining performance and flexibility.
Security Considerations in Trunking
While trunking provides efficiency and flexibility, it also introduces potential security risks if not configured properly. One common issue is VLAN hopping, where unauthorized traffic attempts to move between VLANs through misconfigured trunk ports.
To prevent this, network administrators often disable unused trunk ports, explicitly define allowed VLANs on trunk links, and avoid using default configurations. Proper segmentation and strict control over trunk interfaces are essential for maintaining network security.
Another important practice is ensuring that native VLANs are not used for sensitive traffic, as untagged frames can sometimes be exploited in poorly configured networks.
Spanning Tree Protocol and Trunk Links
The Spanning Tree Protocol (STP) plays a crucial role in preventing network loops in switched environments. When trunk links are used, STP ensures that redundant paths do not create broadcast storms or looping traffic.
In networks with multiple trunk connections between switches, STP selects the most efficient path while blocking redundant links. If a primary link fails, STP automatically activates a backup path, ensuring network resilience.
This interaction between trunking and STP is essential for maintaining stable and loop-free network topologies.
Link Aggregation and Trunking Concepts
Although often confused with VLAN trunking, link aggregation is a different concept that also involves combining multiple physical links. Technologies such as LACP (Link Aggregation Control Protocol) bundle multiple physical connections into a single logical link to increase bandwidth and provide redundancy.
While VLAN trunking focuses on carrying multiple logical networks over one link, link aggregation focuses on increasing performance and reliability by combining multiple links. In many modern networks, both technologies are used together to optimize performance and scalability.
Trunking in Telecommunication Systems
Outside traditional Ethernet networks, trunking also plays a major role in telecommunication systems. In voice communication networks, trunking refers to the sharing of a limited number of communication channels among a large number of users.
Instead of assigning a dedicated line to each user, a pool of lines is shared dynamically. When a user initiates a call, the system assigns an available channel from the trunk group. Once the call ends, the channel is returned to the pool.
This concept significantly improves efficiency and reduces infrastructure costs in voice networks.
MPLS and Advanced Trunking Concepts
In more advanced networking environments, technologies like MPLS (Multiprotocol Label Switching) extend the idea of trunking across wide-area networks. MPLS allows multiple types of traffic to be carried over a single infrastructure while maintaining separation through labels.
Although MPLS is more complex than traditional VLAN trunking, the underlying principle remains similar: multiple logical paths sharing a single physical or virtual transport system.
This makes MPLS widely used in service provider networks and large-scale enterprise WANs.
Quality of Service in Trunked Networks
Quality of Service (QoS) is another important consideration in trunked networks. Since multiple types of traffic share the same physical link, some traffic may require higher priority than others.
For example, voice and video traffic require low latency, while file transfers can tolerate delays. QoS mechanisms ensure that time-sensitive traffic is prioritized even when multiple VLANs are sharing the same trunk link.
This helps maintain performance consistency in busy network environments.
Troubleshooting Trunking Issues
Trunking issues can cause significant network problems if not diagnosed correctly. Common issues include mismatched VLAN configurations, incorrect tagging, or trunk negotiation failures.
Network administrators often check whether trunk ports are properly configured, verify allowed VLAN lists, and ensure that both ends of a trunk link are using compatible settings. Misalignment between devices can result in traffic loss or VLAN isolation issues.
Proper documentation and monitoring tools are essential for quickly identifying and resolving trunking problems.
Best Practices for Implementing Trunking
Effective trunking requires careful planning and configuration. One best practice is to explicitly define which VLANs are allowed on each trunk link, rather than allowing all VLANs by default. This reduces unnecessary traffic and improves security.
Another important practice is consistent VLAN naming and numbering across the entire network. This prevents confusion and simplifies troubleshooting.
Regular monitoring of trunk links also helps ensure optimal performance and early detection of issues before they impact users.
Trunking in Large-Scale Data Centers
In modern data centers, trunking is a fundamental design element that supports high-density connectivity and massive data flow. Thousands of servers, storage systems, and virtual machines operate within a single environment, all requiring segmented yet efficient communication. Trunk links allow multiple VLANs to move through a limited number of high-speed connections between switches, aggregation layers, and core network devices.
Without trunking, data centers would require an impractical number of physical cables, making infrastructure bulky and inefficient. Instead, trunking enables a streamlined architecture where logical separation replaces physical separation. This is especially important in virtualized environments where workloads are frequently moved between servers and networks must adapt dynamically.
Virtualization and Trunking Integration
Virtualization has significantly increased the importance of trunking in modern IT environments. Virtual machines often reside on the same physical server but belong to different VLANs. Trunking allows a single physical network interface card (NIC) to carry traffic for multiple virtual networks simultaneously.
Hypervisors such as VMware ESXi or Hyper-V rely on trunk configurations to assign VLAN tags to virtual network adapters. This ensures that each virtual machine communicates only within its designated network segment, even though they share the same physical hardware.
This integration of trunking and virtualization improves resource utilization and simplifies network design in cloud and enterprise systems.
Trunking in Cloud Networking Environments
Cloud computing environments heavily depend on trunking to maintain multi-tenant isolation and efficient resource sharing. In cloud infrastructure, multiple customers share the same physical hardware while maintaining logically separated networks.
Trunking ensures that each tenant’s traffic remains isolated through VLAN tagging or similar encapsulation techniques. This allows cloud providers to deliver scalable networking services without dedicating separate physical infrastructure to each client.
In hybrid cloud systems, trunking also enables secure communication between on-premises networks and cloud environments, supporting seamless data exchange across different infrastructures.
Dynamic VLAN Assignment and Trunking Efficiency
Advanced network systems use dynamic VLAN assignment in combination with trunking to improve flexibility. Instead of manually assigning VLANs to each port, authentication systems can dynamically place devices into appropriate VLANs based on user identity or role.
Once assigned, trunk links carry this VLAN-specific traffic across the network. This reduces administrative workload and enhances security by ensuring that devices automatically join the correct network segment without manual configuration.
This approach is commonly used in enterprise Wi-Fi networks and large corporate infrastructures where users frequently move between locations.
Trunking in Campus Network Designs
In campus networks, such as universities or corporate campuses, trunking is used to connect multiple buildings and departments. Each building may contain several VLANs for students, staff, administration, and guest users.
Trunk links connect access switches in different buildings to distribution and core switches, carrying all VLAN traffic efficiently. This allows centralized management of the entire campus network while maintaining logical separation between departments.
It also simplifies expansion when new buildings or departments are added, as trunk links can carry additional VLANs without requiring new physical connections.
Redundancy and High Availability with Trunking
Trunking plays a critical role in building redundant and highly available networks. In many enterprise environments, multiple trunk links are established between switches to ensure continuous connectivity in case of link failure.
When combined with redundancy protocols, trunking allows traffic to automatically reroute through alternative paths without service interruption. This ensures that even if one physical connection fails, network communication continues through backup trunk links.
High availability designs often use a combination of trunking, link aggregation, and spanning tree protocols to maintain uninterrupted service.
Bandwidth Utilization in Trunked Networks
One of the major advantages of trunking is improved bandwidth utilization. Instead of dedicating separate links for each VLAN, trunking allows multiple VLANs to share the same high-speed connection.
However, efficient bandwidth usage depends on proper traffic distribution. If one VLAN generates significantly more traffic than others, it may consume most of the trunk’s capacity. Network administrators often use traffic shaping and QoS policies to balance load and prevent congestion.
In high-performance environments, trunk links are often built using fiber connections or multi-gigabit Ethernet to handle large volumes of aggregated traffic.
Security Enhancements in Trunk Configurations
Security is a major concern in trunked networks, especially in environments where multiple VLANs coexist. Misconfigurations can lead to unauthorized access or data leakage between networks.
To enhance security, administrators often restrict allowed VLANs on trunk ports, ensuring only necessary traffic passes through. Disabling unused VLANs and avoiding default configurations also reduces attack surfaces.
Additionally, separating management VLANs from user traffic VLANs helps protect critical network infrastructure from unauthorized access.
Common Misconfigurations in Trunking
Despite its advantages, trunking can introduce issues if not configured correctly. One common problem is VLAN mismatch between connected devices, where one side of a trunk link allows certain VLANs that the other side does not recognize.
Another issue is incorrect native VLAN configuration, which can lead to untagged traffic being misrouted. This often results in communication failures or unexpected network behavior.
Troubleshooting these issues requires careful verification of trunk settings, VLAN consistency, and device compatibility across the network.
Trunk Negotiation Protocols and Automation
Modern network devices often support trunk negotiation protocols that automate the process of establishing trunk links. Protocols such as DTP (Dynamic Trunking Protocol) can automatically determine whether a link should operate as an access or trunk port.
While automation simplifies configuration, it can also introduce security risks if not properly controlled. Many network administrators disable automatic trunk negotiation in favor of manual configuration to maintain full control over network behavior.
Proper understanding of these protocols is essential for designing secure and stable network environments.
Performance Optimization in Trunked Networks
Optimizing performance in trunked networks involves careful planning of VLAN distribution, bandwidth allocation, and link capacity. Overloading a single trunk link with too many VLANs or high-traffic applications can lead to congestion and packet loss.
To prevent performance issues, network designers often use multiple trunk links distributed across different paths. Load balancing techniques ensure that traffic is evenly distributed, improving overall efficiency.
Monitoring tools are also used to analyze trunk utilization and detect potential bottlenecks before they impact users.
Future Trends in Network Trunking
As networking technologies continue to evolve, trunking is also adapting to new requirements. Software-defined networking (SDN) is changing how trunking is implemented by allowing centralized control over network paths and VLAN configurations.
In SDN environments, trunking becomes more dynamic and programmable, enabling networks to adjust automatically based on traffic patterns and application demands. This improves flexibility and reduces manual configuration effort.
Additionally, emerging technologies such as network virtualization overlays are extending the concept of trunking beyond physical infrastructure into fully virtualized environments.
Role of Trunking in Internet Service Providers (ISPs)
Internet service providers rely heavily on trunking to manage large volumes of customer traffic. Trunk links connect core routers, aggregation points, and distribution systems, carrying multiple types of traffic across shared infrastructure.
By using trunking, ISPs can efficiently manage thousands of customers without dedicating separate physical links for each connection. This allows them to scale services while maintaining cost efficiency and performance.
Trunking also supports service differentiation, enabling ISPs to prioritize certain types of traffic such as streaming, voice, or enterprise services.
Integration of Trunking with Modern Network Protocols
Trunking works alongside several modern networking protocols to ensure efficient data transmission. Protocols for routing, switching, and encapsulation all rely on trunk links to carry segmented traffic across the network.
As networks become more complex, trunking continues to serve as a foundational mechanism that supports interoperability between different systems and technologies.
Advanced Trunking Architectures in Modern Networks
As network environments become more complex, trunking is no longer limited to simple switch-to-switch connections. Modern architectures often involve multi-layer trunking designs that span access, distribution, and core layers of enterprise networks. In these layered models, trunk links serve as the backbone that carries aggregated traffic from multiple access switches upward toward central routing systems.
This hierarchical approach allows networks to remain organized even when handling thousands of VLANs and devices. Each layer depends on trunking to maintain separation of traffic while still enabling centralized communication paths. This structure is especially important in large organizations where departments, services, and applications must remain logically isolated but physically interconnected.
Trunking in Software-Defined Networking Environments
Software-Defined Networking (SDN) has transformed how trunking is implemented and managed. Instead of manually configuring VLANs and trunk ports on individual devices, SDN centralizes control in a software controller that dynamically defines how traffic flows through the network.
In SDN-based systems, trunking becomes programmable. VLANs can be created, modified, or removed instantly without physical changes to the infrastructure. The controller determines how trunk links should carry traffic and adjusts configurations in real time based on network demand.
This level of automation improves efficiency, reduces human error, and allows networks to respond quickly to changing workloads, especially in cloud and enterprise environments.
Trunking and Network Virtualization Overlays
Beyond traditional VLAN-based trunking, modern networks also use overlay technologies such as VXLAN (Virtual Extensible LAN). These technologies extend the concept of trunking across wide and distributed environments, including data centers and cloud platforms.
In overlay networks, logical tunnels carry encapsulated traffic across physical infrastructure. This allows networks to scale far beyond traditional VLAN limitations. While VLAN trunking operates within Layer 2 boundaries, overlay trunking extends across Layer 3 networks, enabling global-scale segmentation.
This evolution is critical for multi-cloud environments and large distributed systems where physical distance is no longer a limitation for network design.
Troubleshooting Complex Trunking Issues
Troubleshooting trunking problems in modern networks requires a structured approach. One common issue is inconsistent VLAN propagation, where certain VLANs fail to pass through trunk links correctly. This often results from mismatched allowed VLAN lists or incorrect tagging configurations.
Another frequent problem involves native VLAN mismatches, which can cause untagged traffic to be interpreted incorrectly between connected devices. This leads to communication failures that are often difficult to detect without detailed inspection.
In some cases, spanning tree recalculations can also affect trunk performance by blocking or rerouting links unexpectedly. Network engineers must carefully analyze topology changes and verify that redundancy protocols are functioning correctly.
Tools and Techniques for Diagnosing Trunking Problems
Network administrators use a combination of command-line tools, monitoring systems, and traffic analyzers to diagnose trunking issues. Interface status checks help confirm whether trunk links are active and properly negotiated. VLAN verification commands ensure that expected VLANs are present on each trunk port.
Packet analysis tools provide deeper insight by capturing and decoding VLAN tags in real time. This allows engineers to identify where traffic is being dropped or misrouted. Continuous monitoring systems also alert administrators to anomalies such as sudden drops in VLAN traffic or interface errors.
Effective troubleshooting depends on understanding both the physical and logical behavior of trunk links.
Impact of Trunking on Network Latency and Performance
While trunking improves efficiency, it can also introduce performance considerations if not properly managed. Since multiple VLANs share a single physical link, congestion can occur when traffic demand exceeds available bandwidth.
Latency-sensitive applications such as voice over IP and video conferencing may be affected if trunk links become overloaded. To address this, network engineers implement quality of service policies that prioritize critical traffic over less time-sensitive data.
In high-performance environments, trunk links are often upgraded to higher speeds or distributed across multiple aggregated connections to ensure consistent performance.
Trunking in Hybrid and Multi-Cloud Networks
Hybrid cloud environments, where on-premises infrastructure connects with public cloud platforms, rely heavily on trunking concepts to maintain consistent network segmentation. VLANs from local data centers must often extend into cloud environments through secure tunnels or virtual connections.
Trunking principles ensure that traffic separation remains intact even when workloads move between different environments. This consistency is essential for applications that require seamless connectivity regardless of location.
Multi-cloud architectures also use similar concepts to maintain interoperability between different cloud providers while preserving network isolation.
Automation and AI in Trunk Management
Artificial intelligence and automation are increasingly being used to manage trunking in large-scale networks. AI-driven systems can analyze traffic patterns and automatically adjust trunk configurations to optimize performance and reduce congestion.
For example, if one VLAN experiences a sudden increase in traffic, the system may redistribute resources or adjust priority levels dynamically. Automation also helps detect misconfigurations before they cause outages, improving overall network reliability.
This shift toward intelligent networking reduces the need for manual intervention and enhances operational efficiency.
Energy Efficiency and Trunking Optimization
Modern networks are also focusing on energy efficiency, and trunking plays a role in reducing power consumption. By consolidating multiple logical connections into fewer physical links, trunking reduces the number of active interfaces required in a network.
Fewer active devices and cables result in lower energy usage and reduced cooling requirements in data centers. This contributes to more sustainable IT infrastructure, especially in large-scale environments where energy costs are significant.
Optimized trunk design can therefore support both performance and environmental goals.
Evolution of Trunking Standards and Technologies
Trunking technologies continue to evolve as networking demands increase. While traditional VLAN-based trunking remains widely used, newer standards are expanding capabilities to support higher scalability and flexibility.
Future developments focus on integrating trunking more deeply with automation frameworks, virtualization platforms, and cloud-native architectures. These advancements aim to make trunking more adaptive, secure, and efficient in highly dynamic environments.
As networks move toward fully software-defined models, trunking will likely become more abstracted and controlled entirely through centralized systems.
Real-World Enterprise Use Cases of Trunking
In real-world enterprise environments, trunking is used across nearly every part of network infrastructure. Corporate headquarters use trunk links to connect floors, departments, and server rooms. Manufacturing facilities rely on trunking to separate operational networks from administrative systems while maintaining shared connectivity.
Financial institutions use trunking to isolate sensitive transaction systems from general user traffic while still maintaining centralized infrastructure. Educational institutions use trunking to manage student, faculty, and guest networks across multiple campuses efficiently.
These examples demonstrate how trunking supports both security and scalability in diverse industries.
Common Design Mistakes in Trunking Deployments
Despite its advantages, trunking can be misconfigured if network design principles are not properly followed. One common mistake is allowing unnecessary VLANs on trunk links, which increases broadcast traffic and reduces efficiency.
Another issue is inconsistent configuration across multiple devices, leading to connectivity problems that are difficult to trace. Poor documentation of VLAN structures can also create confusion during troubleshooting or network expansion.
Avoiding these mistakes requires careful planning, standardized configuration practices, and regular audits of network infrastructure.
Future Role of Trunking in Global Connectivity
As global connectivity continues to expand, trunking will remain a foundational concept in networking. Even as technologies evolve toward virtualization and cloud-native systems, the underlying principle of carrying multiple logical networks over shared infrastructure will persist.
Future networks will likely integrate trunking with more intelligent, adaptive systems capable of self-optimization. This will allow networks to automatically adjust to demand, improve resilience, and reduce operational complexity.
Trunking will continue to evolve but remain essential in ensuring efficient and scalable communication across all types of digital environments.
Trunking as a Backbone of Modern Digital Infrastructure
Trunking has evolved into one of the most essential mechanisms supporting modern digital infrastructure. At its core, it allows multiple logical networks to coexist over shared physical connections, but its real importance becomes visible when viewed at scale. In enterprise systems, cloud environments, and global service provider networks, trunking is not just a convenience but a structural necessity that enables communication between thousands of devices and services without overwhelming physical infrastructure.
As organizations expand their digital operations, the complexity of network traffic increases significantly. Applications such as cloud computing, artificial intelligence, streaming services, and distributed databases require constant and reliable communication between systems. Trunking ensures that this communication can occur efficiently by consolidating multiple data streams into optimized pathways.
Deep Dive into VLAN Architecture and Trunking Relationship
Virtual LANs form the logical foundation upon which trunking operates. VLANs divide a physical network into multiple isolated broadcast domains, allowing administrators to segment traffic based on function, department, or security requirements. However, VLANs alone cannot function effectively without a mechanism to transport their traffic between switches and routing devices.
This is where trunking becomes essential. Trunk links act as transport highways for VLAN traffic, carrying multiple segmented networks across a single physical link while preserving their isolation. Each VLAN remains logically independent even though they share the same infrastructure.
This relationship between VLANs and trunking allows networks to achieve both segmentation and scalability simultaneously, which is a critical requirement in modern network design.
Encapsulation Mechanisms in Trunking Systems
Encapsulation is the process that makes trunking possible. When data travels across a trunk link, it must carry identifying information so that receiving devices can determine which VLAN the data belongs to. This is achieved through frame tagging, where additional information is inserted into the data packet structure.
The most widely used method, IEEE 802.1Q, introduces a small tag within Ethernet frames. This tag includes a VLAN identifier that allows switches and routers to correctly process and forward traffic. Once the frame reaches its destination, the tag is removed if it is no longer needed.
Encapsulation ensures that multiple data streams remain distinct even when they share the same transmission medium. Without this mechanism, trunking would not be possible in Ethernet-based networks.
Trunking in High-Density Enterprise Environments
In large enterprise environments, trunking is used extensively to manage high-density network traffic. Organizations with thousands of employees often operate multiple VLANs for departments such as finance, human resources, engineering, guest access, and management systems.
Trunk links connect access layer switches to distribution and core switches, carrying all VLAN traffic across the network backbone. This allows enterprises to maintain structured segmentation while still enabling communication where necessary.
High-density environments rely heavily on trunking efficiency because even small configuration errors can impact large numbers of users. As a result, trunk design is treated as a critical component of enterprise architecture planning.
Trunking and Network Convergence
Network convergence refers to the integration of multiple types of communication services—such as voice, video, and data—over a single network infrastructure. Trunking plays a key role in enabling this convergence.
Instead of using separate physical networks for each service type, trunking allows all traffic types to share the same infrastructure while remaining logically separated. Voice traffic can be assigned to one VLAN, video to another, and data to another, all traveling over the same trunk links.
This approach simplifies infrastructure design and reduces operational costs while maintaining performance requirements for different types of traffic.
Trunking in Service Provider Networks
Internet service providers operate some of the largest and most complex networks in the world, and trunking is fundamental to their architecture. ISP networks must handle massive volumes of traffic from millions of users while maintaining service quality and isolation between customers.
Trunk links connect core routers, aggregation points, and distribution nodes, carrying multiple customer networks simultaneously. Each customer’s traffic is separated using VLANs or similar encapsulation technologies.
This structure allows ISPs to scale efficiently while maintaining performance and security across their entire infrastructure.
Load Distribution and Traffic Engineering in Trunked Networks
One of the most important aspects of trunking in large-scale systems is traffic engineering. Since multiple VLANs share the same physical link, traffic must be carefully balanced to avoid congestion and performance degradation.
Load distribution techniques ensure that no single trunk link becomes a bottleneck. In many systems, traffic is distributed across multiple trunk connections using hashing algorithms or dynamic load balancing protocols.
Traffic engineering also involves prioritizing certain types of traffic. For example, real-time applications such as voice and video may be given higher priority than background data transfers. This ensures consistent performance even under heavy network load.
Trunking and Network Redundancy Strategies
Redundancy is a critical requirement in modern networks, and trunking plays an important role in achieving it. Redundant trunk links are often deployed between switches and routers to ensure that network communication continues even if one link fails.
In redundant designs, multiple trunk paths exist between devices, but only one path may be active at a time depending on spanning tree calculations or load balancing configurations. If a failure occurs, traffic is automatically rerouted through an alternate trunk link.
This redundancy ensures high availability and minimizes downtime in mission-critical environments.
Role of Spanning Tree Protocol in Trunk Environments
The Spanning Tree Protocol is essential in preventing loops in networks that use multiple trunk links. Without loop prevention, redundant paths could cause broadcast storms and network instability.
STP works by analyzing network topology and disabling certain links to create a loop-free structure. If an active trunk link fails, STP recalculates the topology and activates a previously blocked link.
This dynamic adjustment ensures network resilience while maintaining stability in complex trunked environments.
Trunking in Virtualized Network Functions (VNF)
Virtualized Network Functions represent a shift away from traditional hardware-based networking toward software-based systems. In these environments, trunking is used to connect virtual network components running on shared physical infrastructure.
VNFs such as virtual firewalls, load balancers, and routers rely on trunk links to communicate across multiple virtual networks. This allows service providers and enterprises to deploy flexible, scalable network services without relying on dedicated hardware appliances.
Trunking ensures that these virtual systems can operate efficiently while maintaining isolation between different network functions.
Security Challenges in Large-Scale Trunk Deployments
As trunking becomes more widespread, security considerations become increasingly important. Misconfigured trunk ports can expose networks to vulnerabilities such as unauthorized VLAN access or traffic interception.
One of the most common risks is VLAN hopping, where attackers exploit configuration weaknesses to access restricted networks. Preventing such attacks requires strict configuration policies, including limiting allowed VLANs and disabling unnecessary trunk ports.
Network segmentation must also be carefully maintained to ensure that sensitive systems remain isolated from general traffic.
Advanced Monitoring and Analytics in Trunk Networks
Modern networks rely heavily on monitoring and analytics tools to manage trunk performance. These systems track bandwidth usage, VLAN activity, latency, and error rates across trunk links.
By analyzing this data, administrators can identify congestion points, detect anomalies, and optimize traffic flow. Predictive analytics can even forecast potential network issues before they occur, allowing proactive adjustments.
This level of visibility is essential in large-scale environments where manual monitoring would be impractical.
Trunking in Edge Computing Architectures
Edge computing brings processing closer to data sources, reducing latency and improving performance for real-time applications. In these environments, trunking is used to connect edge nodes with central data centers.
Edge devices often handle multiple types of traffic simultaneously, including IoT data, video streams, and control signals. Trunk links ensure that all these traffic types can be transmitted efficiently while maintaining separation.
As edge computing continues to grow, trunking will play a key role in supporting distributed network architectures.
Impact of 5G Networks on Trunking Concepts
The introduction of 5G technology has expanded the need for advanced trunking mechanisms. 5G networks support massive device connectivity and require highly efficient traffic management systems.
Trunking principles are applied in 5G core networks to separate different types of services such as enhanced mobile broadband, ultra-reliable low-latency communication, and massive IoT connectivity.
These services share infrastructure but require strict isolation and performance guarantees, making trunking essential for maintaining service quality.
Automation and Intent-Based Networking Evolution
Intent-based networking represents the next stage in network evolution, where administrators define desired outcomes rather than manual configurations. Trunking is managed automatically based on these high-level intents.
For example, instead of manually configuring VLANs and trunk links, an administrator might specify that certain departments should remain isolated while sharing bandwidth efficiently. The network system then automatically configures trunking to meet these requirements.
This approach reduces complexity and improves adaptability in dynamic environments.
Trunking and Future Network Scalability Challenges
As networks continue to grow in size and complexity, trunking must evolve to handle increasing demands. Future challenges include managing higher traffic volumes, supporting more virtual networks, and maintaining security across distributed systems.
Scalability will depend on integrating trunking with advanced technologies such as AI-driven optimization, software-defined control, and automated orchestration systems.
These advancements will ensure that trunking remains relevant in next-generation network architectures.
Conclusion
Trunking is one of the most important concepts in modern networking because it enables efficient communication between multiple logical networks over a single physical connection. Instead of relying on separate links for each network segment, trunking consolidates traffic and allows different VLANs to coexist while remaining isolated and organized. This balance between efficiency and segmentation is what makes trunking essential in both small-scale and large-scale environments.
Across enterprise networks, data centers, cloud systems, and service provider infrastructures, trunking ensures that network resources are used effectively without sacrificing performance or scalability. It supports high-density environments where thousands of devices must communicate simultaneously, while also reducing physical complexity and infrastructure costs. By using tagging and encapsulation techniques, trunking maintains clarity in traffic flow even when multiple networks share the same pathway.
In addition to improving efficiency, trunking plays a major role in network flexibility. It allows administrators to expand networks, add new VLANs, and restructure systems without requiring major physical changes. This adaptability is especially important in modern IT environments where workloads are dynamic and constantly evolving.
Security, performance, and reliability are also closely tied to proper trunking design. When configured correctly, trunking supports secure segmentation, optimized bandwidth usage, and high availability through redundancy and failover mechanisms. However, misconfigurations can lead to serious issues, which is why careful planning and management are essential.
As networking technologies continue to evolve toward virtualization, cloud computing, automation, and software-defined architectures, trunking remains a foundational element. Even though implementation methods may change, the core principle of carrying multiple logical networks over shared infrastructure will continue to be central to network design.
Ultimately, trunking is not just a technical feature but a structural necessity in modern networking, enabling the scalable, efficient, and interconnected systems that power today’s digital world.