A deeper understanding of Kubernetes cluster setup security is essential because the control plane represents the brain of the entire system. Securing it requires careful configuration of every core component including the API server, scheduler, controller manager, and key-value data store. The API server must be protected with strict authentication mechanisms such as client certificates, token-based authentication, and integration with external identity providers where applicable. Authorization must be tightly controlled using fine-grained policies that ensure users and system components only access the resources they are explicitly permitted to interact with.
The etcd database, which stores all cluster state data, is one of the most sensitive components and must be secured through encryption and restricted network access. Direct exposure of etcd to external networks can lead to catastrophic compromise of the entire cluster. Secure communication channels using TLS encryption between all control plane components are mandatory to ensure confidentiality and integrity of data in transit. In addition, audit logging plays an important role in tracking all interactions with the control plane, allowing administrators to trace unauthorized or suspicious activities back to their source.
Another important aspect is ensuring that the control plane runs with minimal privileges and unnecessary services are disabled. Any unused ports or debug interfaces should be closed to reduce attack surfaces. Regular patching of Kubernetes components is also critical because vulnerabilities in control plane software can be exploited if not updated in time.
Node and Operating System Hardening Practices
Worker nodes form the execution layer where containers run, making them a frequent target for attackers. Securing nodes begins at the operating system level. This includes disabling unused kernel modules, restricting root access, and enforcing strict user permissions. System-level services that are not required for Kubernetes operations should be removed or disabled to reduce potential vulnerabilities.
Kernel security parameters should be tuned to restrict process capabilities and network behavior. Security modules such as mandatory access control systems help enforce additional restrictions on processes, ensuring that even if a container is compromised, its ability to affect the host system remains limited. SSH access to nodes must be carefully controlled, ideally restricted to key-based authentication and limited administrative users only.
File system security is another important aspect. Sensitive directories such as those containing configuration files, secrets, and certificates must have restricted permissions. Writable directories should be minimized to prevent unauthorized modification of system files. Additionally, regular system updates are critical to patch known vulnerabilities in the operating system and runtime environment.
Secure Container Runtime Configuration
The container runtime is responsible for executing workloads, and its configuration plays a significant role in overall cluster security. Ensuring that the runtime is properly isolated from the host system is essential. Containers should run with the least privileges possible, avoiding root user execution whenever feasible.
Security profiles such as seccomp, AppArmor, or SELinux should be applied to restrict system calls and enforce mandatory access controls. These profiles help reduce the risk of container escape attacks by limiting the actions a container process can perform on the host system.
Container images should be executed in read-only mode where possible to prevent runtime modification of application files. Privileged containers should be avoided unless absolutely necessary, as they bypass many security restrictions and can pose significant risks. Resource limits should also be enforced to prevent denial-of-service conditions caused by resource exhaustion.
Another important practice is ensuring proper isolation between containers using namespaces. Each container should have its own isolated view of processes, networking, and file systems to prevent cross-container interference.
Workload Isolation and Pod-Level Security Controls
Securing workloads at the pod level is a critical part of Kubernetes security. Pods should be configured with strict security contexts that define privilege levels, user IDs, and access capabilities. Running containers as non-root users is a fundamental security requirement that reduces the impact of potential compromises.
Capabilities granted to containers should be explicitly defined and minimized. Instead of granting full privileges, only specific capabilities required for the application should be enabled. This reduces the attack surface significantly.
Pod Security Standards help enforce baseline, restricted, and privileged levels of security policies across namespaces. These standards ensure that workloads adhere to predefined security requirements without manual enforcement for every pod.
Volume security is also important because improperly configured volumes can expose sensitive host data to containers. Access to host paths should be tightly restricted, and sensitive directories should never be mounted unless absolutely necessary. Secrets should be handled carefully, ensuring they are not exposed in environment variables or logs.
Container Image and Supply Chain Security
One of the most overlooked areas in Kubernetes security is the software supply chain. Every container image introduced into a cluster represents a potential risk if not properly validated. Ensuring image integrity begins with using trusted base images and verifying their authenticity before deployment.
Image scanning for vulnerabilities is essential to detect known security issues before they reach production environments. Images should be scanned during the build process as well as before deployment. This layered approach ensures that vulnerabilities are identified early and mitigated effectively.
Image signing and verification mechanisms help ensure that only trusted and unmodified images are deployed. This prevents attackers from injecting malicious code into container images. Additionally, immutable tags should be used instead of floating tags like “latest” to avoid unintended updates or version mismatches.
Reducing image size also contributes to security by minimizing the number of installed packages and potential vulnerabilities. Minimal base images reduce attack surfaces and improve performance simultaneously.
Authentication and Identity Management in Kubernetes
Authentication is the first line of defense in securing Kubernetes environments. It ensures that only verified users and services can interact with the cluster. Kubernetes supports multiple authentication mechanisms, including client certificates, bearer tokens, and external identity providers.
Service accounts play a critical role in allowing workloads to interact with the Kubernetes API. These accounts should be assigned minimal permissions based on the principle of least privilege. Default service accounts should not be used for production workloads, as they often carry unnecessary permissions.
Role-Based Access Control is used to define what actions users and services can perform within the cluster. Roles should be carefully designed to limit access strictly to required resources and operations. Overly permissive roles can lead to privilege escalation and unauthorized access to sensitive data.
Regular auditing of authentication and authorization policies is necessary to ensure that outdated or unnecessary permissions are removed. This helps maintain a clean and secure access control structure over time.
Admission Control and Policy Enforcement Mechanisms
Admission controllers act as gatekeepers that evaluate requests before they are persisted in the cluster. They provide an additional layer of security by enforcing policies during resource creation and modification.
These controllers can be used to enforce security standards such as preventing privileged containers, enforcing resource limits, and restricting the use of certain capabilities. They ensure that even if a user has permission to create resources, those resources must still comply with cluster-wide security policies.
Policy engines can also be used to define custom security rules that go beyond default Kubernetes capabilities. These policies help enforce organizational security standards consistently across all workloads and namespaces.
By combining admission control with proper RBAC configuration, Kubernetes environments can achieve strong defense-in-depth security architecture.
Logging, Auditing, and Threat Detection
Visibility into cluster activity is essential for detecting and responding to security incidents. Kubernetes audit logs provide a detailed record of all API requests, including who performed actions, what resources were accessed, and when events occurred.
These logs should be centrally collected and securely stored to prevent tampering. Monitoring tools can analyze logs in real time to detect unusual patterns such as repeated failed authentication attempts or unauthorized resource modifications.
Runtime security monitoring tools help detect anomalies at the container level, such as unexpected process execution or suspicious network activity. These insights allow administrators to respond quickly to potential threats before they escalate.
Alerting systems should be configured to notify administrators immediately when suspicious activity is detected. This ensures rapid response and minimizes potential damage.
Network Security and Traffic Control
Network security in Kubernetes is enforced primarily through network policies that define how pods communicate with each other and external systems. By default, Kubernetes allows unrestricted communication between pods, which must be restricted using explicit policies.
Ingress and egress rules should be defined to control both incoming and outgoing traffic for each workload. This ensures that only authorized services can communicate with each other, reducing the risk of lateral movement in case of a breach.
Segmentation of network traffic based on namespaces or application tiers helps isolate workloads and improve security boundaries. Sensitive applications should always be placed in restricted network zones with strict access controls.
Encryption of network traffic using TLS is also important to protect data in transit from interception or tampering.
Secrets Management and Secure Data Handling
Secrets in Kubernetes store sensitive information such as passwords, tokens, and certificates. Proper handling of secrets is critical to prevent data exposure. Secrets should always be encrypted at rest and access should be tightly controlled using RBAC policies.
Avoiding hardcoded secrets in application code or configuration files is essential. Instead, secrets should be injected securely at runtime using controlled mechanisms. Logging of secrets must be strictly avoided to prevent accidental exposure.
External secret management systems can also be integrated to enhance security by storing sensitive data outside the cluster and retrieving it securely when needed.
Incident Response and Security Troubleshooting
When a security incident occurs, rapid identification and containment are critical. This involves analyzing logs, identifying compromised resources, and isolating affected workloads.
Kubernetes provides tools to inspect running containers, view process activity, and analyze network behavior. These tools help identify the root cause of security issues and guide remediation steps.
Once a threat is contained, affected resources should be replaced or restored from trusted configurations. Post-incident analysis is important to understand vulnerabilities and improve future security posture.
Runtime Security Monitoring and Behavioral Analysis
Runtime security is one of the most critical layers in Kubernetes defense because it focuses on what actually happens while applications are running. Even if cluster setup, image scanning, and access control are properly configured, threats can still emerge at runtime through compromised containers or misconfigured workloads. Runtime monitoring involves continuously observing system calls, process activity, file access, and network connections within running containers.
Behavioral analysis tools are used to establish a baseline of normal activity for workloads and then detect deviations from that baseline. For example, if a container that normally serves web traffic suddenly starts executing shell commands or scanning the network, this may indicate malicious activity. These anomalies must be flagged immediately for investigation.
Kernel-level monitoring techniques provide deep visibility into container behavior by tracking system calls and resource usage. This level of monitoring helps detect container breakout attempts, privilege escalation, or unauthorized file system modifications.
Another important aspect is enforcing runtime policies that automatically block or restrict suspicious behavior. Instead of only detecting threats, modern security approaches aim to prevent them in real time by terminating or isolating compromised containers as soon as abnormal activity is detected.
Advanced Threat Detection and Response Strategies
Threat detection in Kubernetes environments requires combining multiple layers of security telemetry. Logs, metrics, and runtime signals must be correlated to identify complex attack patterns. For example, a single failed login attempt may not be suspicious, but repeated failures across multiple services combined with unusual API activity can indicate a coordinated attack.
Security response strategies involve predefined actions that are triggered when specific threats are detected. These actions may include isolating pods, revoking credentials, or scaling down affected services. Automation plays a key role here because manual response is often too slow to contain fast-moving threats.
Another important concept is threat intelligence integration, where known malicious IPs, domains, or behaviors are used to enhance detection capabilities. By comparing runtime activity against known attack signatures, systems can identify and block threats earlier in the attack chain.
Incident response plans should also include forensic capabilities, allowing security teams to reconstruct events after an attack. This includes capturing container states, logs, and network traffic for detailed analysis.
Kubernetes API Security and Access Control Hardening
The Kubernetes API server is the central point of interaction for all cluster operations, making it a high-value target. Securing API access involves multiple layers of protection, starting with strong authentication mechanisms such as certificates and token-based identity validation.
Once authenticated, users must be restricted through fine-grained authorization policies. Role-Based Access Control ensures that users and service accounts can only perform actions that are explicitly allowed. Overly broad permissions must be avoided because they can lead to privilege escalation attacks.
API rate limiting and request throttling are also important to prevent denial-of-service attacks against the control plane. Attackers may attempt to overwhelm the API server with excessive requests, and rate limiting helps mitigate this risk.
Audit logging of API requests provides visibility into all interactions with the cluster. These logs are essential for detecting unauthorized access attempts and understanding user behavior patterns over time.
Another critical security practice is disabling anonymous access and removing unused API endpoints. Reducing the exposed surface of the API server significantly lowers the risk of exploitation.
Secrets Encryption and Key Management Practices
Protecting sensitive data within Kubernetes requires strong encryption and key management strategies. Secrets stored in etcd should always be encrypted using strong encryption algorithms. Without encryption, anyone with access to etcd backups could retrieve sensitive credentials in plain text.
Key management systems play a central role in controlling encryption keys used for securing secrets. These systems ensure that keys are rotated regularly and stored securely outside of the cluster. Proper key rotation reduces the risk of long-term compromise if a key is exposed.
Access to secrets must be strictly controlled using RBAC policies. Only workloads that absolutely require access should be granted permission to read secrets. Even within a namespace, access should be minimized to reduce exposure risk.
Secrets should also be injected into containers at runtime instead of being hardcoded into application images or configuration files. This reduces the chance of accidental exposure through version control systems or logs.
Multi-Tenancy Security and Namespace Isolation
In environments where multiple teams or applications share the same cluster, multi-tenancy security becomes essential. Namespace isolation is the primary mechanism used to separate workloads and enforce boundaries between different tenants.
Each namespace should have its own set of resource quotas, network policies, and access controls. This ensures that one tenant cannot consume excessive resources or interfere with another tenant’s workloads.
Strict Role-Based Access Control must be applied at the namespace level to ensure users can only interact with resources within their assigned boundaries. Cross-namespace access should be explicitly defined and tightly controlled.
Network policies further enhance isolation by controlling communication between namespaces. By default, all namespaces should be isolated unless specific communication is required.
Resource limits and quotas also play an important role in preventing noisy neighbor problems, where one workload consumes disproportionate resources and impacts others.
Secure Configuration Management and Policy Enforcement
Configuration management is a key area in Kubernetes security because misconfigurations are one of the most common causes of vulnerabilities. Secure configuration practices involve defining and enforcing consistent policies across all cluster resources.
Policy enforcement tools ensure that all deployed resources comply with security standards. For example, policies can prevent the deployment of containers running as root or enforce mandatory resource limits.
Configuration drift detection is also important. Over time, manual changes or updates may cause configurations to deviate from intended security baselines. Detecting and correcting this drift helps maintain consistent security posture.
Infrastructure as code practices improve security by allowing configurations to be version-controlled and reviewed before deployment. This reduces human error and ensures repeatability across environments.
Supply Chain Attacks and Dependency Security
Modern applications rely heavily on external dependencies, which introduces supply chain risks. Attackers may compromise upstream libraries or container base images to inject malicious code into applications.
Securing the supply chain involves verifying the integrity of all dependencies before use. This includes checking digital signatures, validating checksums, and using trusted registries for container images.
Dependency scanning tools help identify vulnerabilities in third-party libraries used within container images. These vulnerabilities must be patched or mitigated before deployment.
Build pipelines should also be secured to prevent unauthorized modifications. Only trusted build systems should be allowed to produce deployable artifacts. Any compromise in the build process can lead to widespread cluster compromise.
Cluster Upgrade Security and Patch Management
Keeping Kubernetes clusters up to date is a fundamental security requirement. Each new release often includes critical security patches that address known vulnerabilities. Delaying upgrades increases the risk of exploitation.
Upgrade processes must be carefully planned to avoid service disruption. This includes testing updates in staging environments before applying them to production clusters.
Node operating systems, container runtimes, and supporting tools must also be updated regularly. Security is not limited to Kubernetes components alone but extends to the entire infrastructure stack.
Automated patch management systems can help ensure timely updates, reducing the window of exposure to known threats.
Policy as Code and Security Automation
Policy as code allows security rules to be defined programmatically rather than manually enforced. This ensures consistency and scalability across large environments.
Security automation plays a major role in maintaining compliance. Automated systems can continuously evaluate cluster configurations and immediately flag or correct violations.
For example, if a workload is deployed without required security settings, automation can either block the deployment or apply corrective configurations automatically.
This approach reduces reliance on manual audits and ensures that security policies are enforced consistently across all environments.
Advanced Kubernetes Hardening Techniques
Advanced hardening techniques include restricting kernel capabilities, disabling unused features, and minimizing attack surfaces at every layer. This includes limiting container capabilities, enforcing strict seccomp profiles, and isolating workloads at the system level.
Reducing the number of running services within the cluster also contributes to better security. Each additional service increases potential vulnerabilities and attack vectors.
Security benchmarking tools can be used to evaluate cluster configurations against industry standards and best practices. These benchmarks help identify weaknesses and guide remediation efforts.
Defense-in-depth strategies are essential, meaning multiple overlapping security controls must be implemented so that if one layer fails, others still provide protection.
Advanced Kubernetes Network Defense and Micro-Segmentation
Network security in Kubernetes goes far beyond basic traffic filtering. In advanced environments, micro-segmentation is used to create fine-grained isolation between services, even within the same cluster. This approach ensures that each workload communicates only with explicitly approved peers, significantly reducing lateral movement in case of compromise.
Network policies must be carefully designed to define both ingress and egress rules. Ingress controls determine what traffic can enter a pod, while egress rules control what external services a pod can access. Many security incidents occur due to unrestricted egress traffic, which allows compromised workloads to communicate with external malicious servers.
DNS traffic is another critical area that must be controlled. Attackers often exploit DNS resolution to exfiltrate data or establish command-and-control channels. Restricting DNS access and monitoring DNS queries helps detect abnormal behavior early.
Service meshes can also enhance network security by enforcing mutual TLS encryption between services. This ensures that all service-to-service communication is authenticated and encrypted, reducing the risk of interception or impersonation attacks.
Kubernetes Runtime Isolation and Sandboxing Techniques
Runtime isolation is a key defense mechanism that prevents compromised containers from affecting the host system or other workloads. Traditional container isolation relies on namespaces and cgroups, but advanced security requires additional sandboxing layers.
Sandboxing technologies provide stronger isolation boundaries by running containers inside lightweight virtual environments. This reduces the risk of container escape vulnerabilities, where an attacker breaks out of the container and gains access to the host system.
Seccomp profiles play an important role by restricting the system calls that containers can make to the kernel. By limiting system calls to only those required for application functionality, the attack surface is significantly reduced.
Mandatory Access Control systems enforce additional security constraints at the kernel level. These systems define strict rules about what processes can access specific files, network resources, or system capabilities. Even if a container is compromised, these controls limit its ability to perform harmful actions.
Advanced RBAC Design and Privilege Minimization
Role-Based Access Control in Kubernetes must be designed with extreme care to avoid privilege escalation risks. One of the most common security failures in clusters is over-permissioned roles that grant unnecessary access to sensitive resources.
A secure RBAC design follows the principle of least privilege, where each user or service account is granted only the permissions required for its specific function. Cluster-wide roles should be avoided unless absolutely necessary.
Role bindings must be carefully audited to ensure they are not granting unintended access across namespaces. In large environments, role sprawl can occur over time, making periodic reviews essential.
Another advanced technique involves separating duties between different identities. For example, deployment permissions should be separated from monitoring or debugging permissions to reduce the risk of abuse.
Service accounts used by applications should never have elevated privileges unless required for specific operational needs. Default service accounts should be disabled or heavily restricted.
Advanced Secrets Security and Ephemeral Credentials
Managing secrets securely requires more than just encryption. Advanced security models focus on reducing the lifetime and exposure of credentials. Ephemeral credentials are temporary secrets that expire after a short period, reducing the risk of long-term compromise.
Instead of storing static credentials inside the cluster, dynamic secret generation can be used. This approach generates credentials on demand and revokes them automatically after use.
Secrets injection should be handled carefully to avoid exposing sensitive data through environment variables or logs. Volume-mounted secrets with restricted permissions provide a safer alternative in many cases.
Audit logging for secret access is also important. Tracking who accessed which secrets and when helps detect suspicious behavior and potential insider threats.
External secret management systems provide an additional layer of security by storing sensitive information outside the cluster and retrieving it securely at runtime. This reduces the attack surface within Kubernetes itself.
Advanced Container Image Hardening and Minimal Base Images
Container image security plays a major role in preventing vulnerabilities from entering the cluster. Advanced hardening involves building images with the smallest possible footprint.
Minimal base images reduce the number of installed packages, which in turn reduces potential vulnerabilities. Each additional package introduces new attack vectors, so keeping images lean is a key security strategy.
Multi-stage builds are commonly used to separate build-time dependencies from runtime environments. This ensures that development tools and unnecessary binaries are not included in production images.
Image provenance tracking ensures that every image can be traced back to its source, including the build process and dependency chain. This is critical for identifying where vulnerabilities may have been introduced.
Immutable image tags help prevent unexpected changes in deployed workloads. Instead of using mutable tags, specific versioned identifiers should always be used to ensure consistency and security.
Advanced Kubernetes Audit Logging and Forensics
Audit logging provides deep visibility into all cluster activities and is essential for forensic investigations. Every API request, authentication attempt, and resource modification should be recorded in a secure and tamper-proof manner.
Logs must be centralized to ensure they cannot be altered or deleted by attackers who may gain partial access to the cluster. Centralized logging also allows correlation of events across multiple nodes and services.
Advanced forensic analysis involves reconstructing the sequence of events leading to a security incident. This includes analyzing API calls, container behavior, network traffic, and system logs.
Time synchronization across all cluster components is essential for accurate log correlation. Without synchronized time, reconstructing attack timelines becomes difficult or unreliable.
Log retention policies must balance storage costs with security needs. Critical logs should be retained for extended periods to support long-term investigations and compliance requirements.
Kubernetes Admission Policies and Preventive Security Controls
Admission control mechanisms act as preventive security gates that validate every request before it is persisted in the cluster. These controls help enforce security policies at the point of resource creation.
Advanced admission policies can enforce rules such as preventing privileged containers, blocking host network access, and ensuring that all workloads define resource limits.
These policies can also enforce compliance standards across the entire cluster. For example, ensuring that all pods include security contexts or that only approved container registries are used.
Dynamic policy enforcement allows rules to be updated without modifying application code. This ensures that security policies evolve independently of workloads.
By combining admission control with RBAC and network policies, Kubernetes environments achieve a layered defense model that significantly reduces the risk of misconfiguration-based attacks.
Advanced Threat Modeling in Kubernetes Environments
Threat modeling is a proactive approach to identifying potential security risks before they are exploited. In Kubernetes environments, this involves analyzing how attackers could move through the cluster and identifying weak points.
Common threat vectors include compromised container images, exposed APIs, misconfigured RBAC roles, and insecure network policies. Each of these areas must be evaluated for potential exploitation paths.
Attack simulation techniques can be used to test cluster resilience against real-world attack scenarios. This helps validate whether existing security controls are effective under pressure.
Understanding attacker behavior patterns is also important. Many attacks follow predictable stages, including reconnaissance, privilege escalation, lateral movement, and data exfiltration.
By modeling these stages, security teams can design defenses that interrupt attacks at multiple points in the kill chain.
Advanced Incident Containment and Recovery Strategies
When a security incident occurs, rapid containment is critical to prevent further damage. This involves isolating affected workloads, revoking credentials, and blocking malicious network traffic.
In Kubernetes environments, affected pods can be quickly terminated and replaced with clean versions. However, proper root cause analysis must be performed before restoration to prevent reinfection.
Credential rotation is an essential part of incident response. Any compromised secrets or tokens must be immediately invalidated and replaced.
Recovery strategies should include restoring workloads from known-good configurations stored in version-controlled systems. This ensures that only verified and secure states are redeployed.
Post-incident reviews help improve future security posture by identifying weaknesses and updating policies accordingly.
Advanced Kubernetes Compliance and Regulatory Security Controls
In enterprise environments, Kubernetes security is not only about preventing attacks but also about meeting strict compliance requirements. Organizations often need to adhere to standards such as data protection laws, internal governance policies, and industry security frameworks. Compliance in Kubernetes is achieved through continuous enforcement of security configurations rather than periodic manual audits.
Policy enforcement tools help ensure that clusters remain aligned with required standards. These policies can mandate encryption for data at rest and in transit, enforce strict access controls, and require secure configuration for all deployed workloads. Any deviation from these rules must be automatically detected and corrected to prevent compliance drift.
Audit readiness is another critical aspect. Every action within the cluster must be traceable, including user activity, system changes, and workload modifications. This ensures that in the event of an audit, organizations can demonstrate full visibility and control over their Kubernetes environment.
Advanced Identity Federation and External Authentication Systems
Modern Kubernetes environments often integrate with external identity providers to manage authentication at scale. This approach allows centralized control of user identities across multiple systems and reduces the complexity of managing internal credentials.
Identity federation enables single sign-on capabilities, allowing users to authenticate once and access multiple systems securely. This reduces the risk of password reuse and improves overall security hygiene.
Role mapping between external identity systems and Kubernetes RBAC must be carefully designed to ensure correct privilege assignment. Misaligned mappings can lead to unintended access to sensitive cluster resources.
Multi-factor authentication adds an additional layer of protection by requiring multiple verification steps before granting access. This significantly reduces the risk of compromised credentials being used for unauthorized access.
Advanced Supply Chain Integrity Verification
Supply chain security continues to be a major concern in Kubernetes environments due to the heavy reliance on external dependencies. Advanced verification techniques ensure that every component entering the cluster is trustworthy.
Binary authorization mechanisms can enforce strict rules about which container images are allowed to run in the cluster. Only images that pass verification checks are permitted for deployment.
Software bill of materials analysis provides visibility into all components included within container images. This helps identify vulnerable dependencies and ensures transparency in the build process.
Continuous scanning of images and dependencies ensures that newly discovered vulnerabilities are detected even after deployment. This ongoing evaluation is essential for maintaining long-term security.
Final Security Posture and Defense-in-Depth Strategy
A strong Kubernetes security posture relies on multiple overlapping layers of defense. No single control is sufficient to protect against all threats, so security must be implemented at every level.
Defense-in-depth includes securing infrastructure, hardening nodes, enforcing strict access controls, monitoring runtime behavior, and securing the supply chain. Each layer acts as a fallback in case another layer is compromised.
Continuous monitoring and improvement are essential because threat landscapes evolve constantly. Security is not a one-time setup but an ongoing process that requires regular updates and audits.
Ultimately, mastering Kubernetes security requires understanding both offensive and defensive perspectives. By anticipating how attackers operate and designing systems to resist those techniques, environments can achieve strong resilience against modern threats.
Conclusion
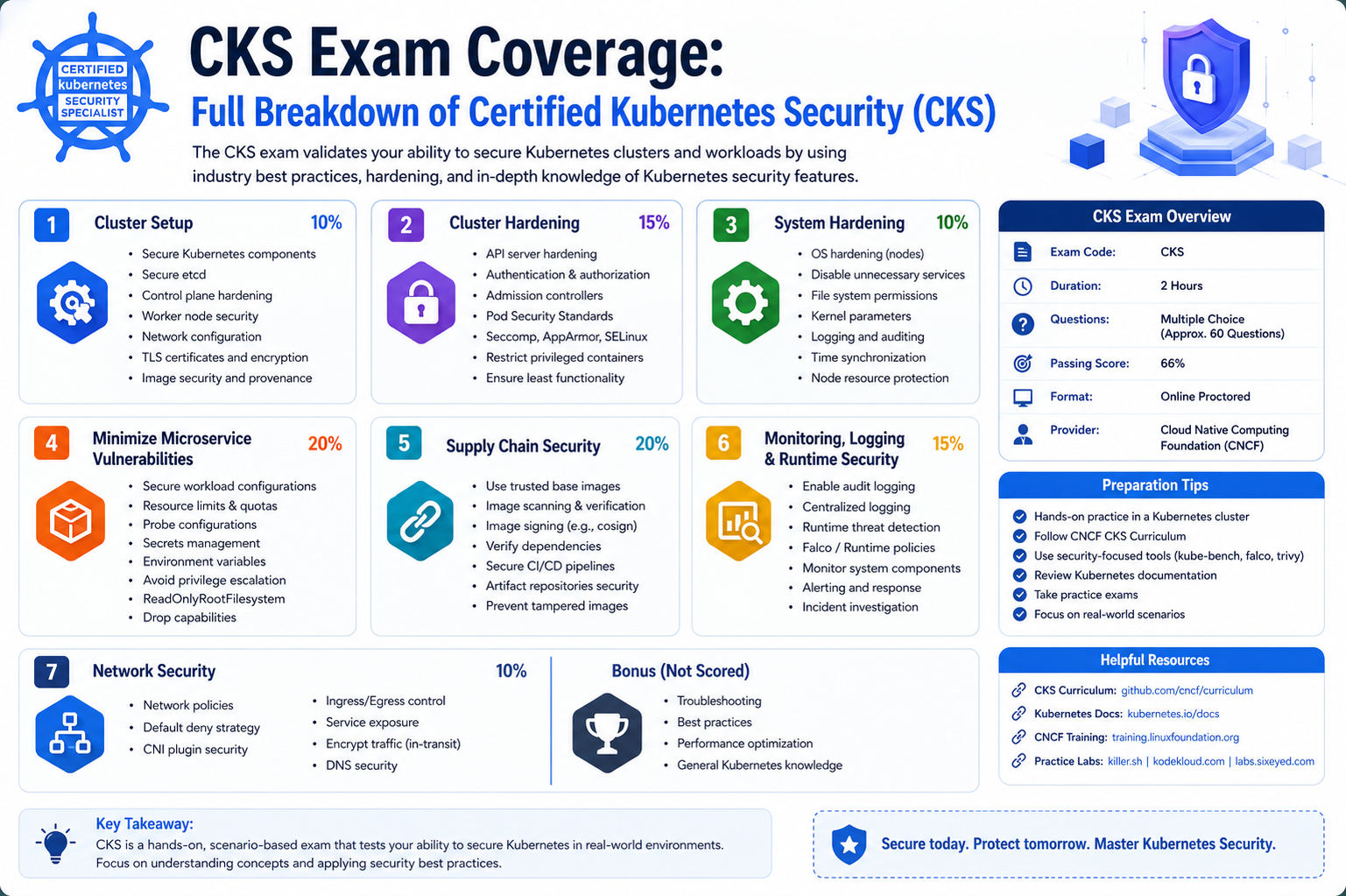
The Certified Kubernetes Security (CKS) exam represents one of the most advanced validations of cloud-native security expertise, focusing on real-world defense strategies rather than theoretical knowledge. It requires a deep understanding of how Kubernetes systems behave across every layer, from infrastructure and cluster setup to workloads, networking, runtime behavior, and supply chain integrity.
Security in Kubernetes is not dependent on a single tool or configuration. Instead, it is built through a layered defense model where each control reinforces the others. Proper cluster hardening reduces exposure at the foundation, while strict identity management ensures only authorized access. Workload isolation, network segmentation, and runtime monitoring collectively strengthen the environment against both internal misconfigurations and external attacks.
A key takeaway is that most Kubernetes security issues arise not from complex exploits but from simple misconfigurations, excessive privileges, and lack of visibility. The CKS framework emphasizes eliminating these risks through disciplined configuration, continuous monitoring, and strict adherence to least privilege principles.
Another important aspect is the shift toward proactive security. Instead of reacting to incidents after they occur, modern Kubernetes security focuses on prevention through policy enforcement, automated controls, and continuous validation. Admission controllers, policy-as-code, and runtime protection tools all contribute to stopping threats before they reach production workloads.
Ultimately, mastering Kubernetes security requires both technical skill and a security-first mindset. It is not just about passing an exam but about understanding how attackers think, how systems fail, and how layered defenses can be designed to withstand real-world threats. Those who develop this depth of understanding are well-prepared to secure complex cloud-native environments in production at scale.