AAA, TACACS+, and SSH form a critical trio in modern network security, each contributing a distinct layer of protection and control. While they are often mentioned together, they are not interchangeable technologies. Instead, they work in coordination to secure access, enforce policies, and protect communication channels. A clear understanding of how these components interact allows network administrators to design systems that are both secure and efficient, minimizing risks while maintaining usability.
The Core Concept Behind AAA
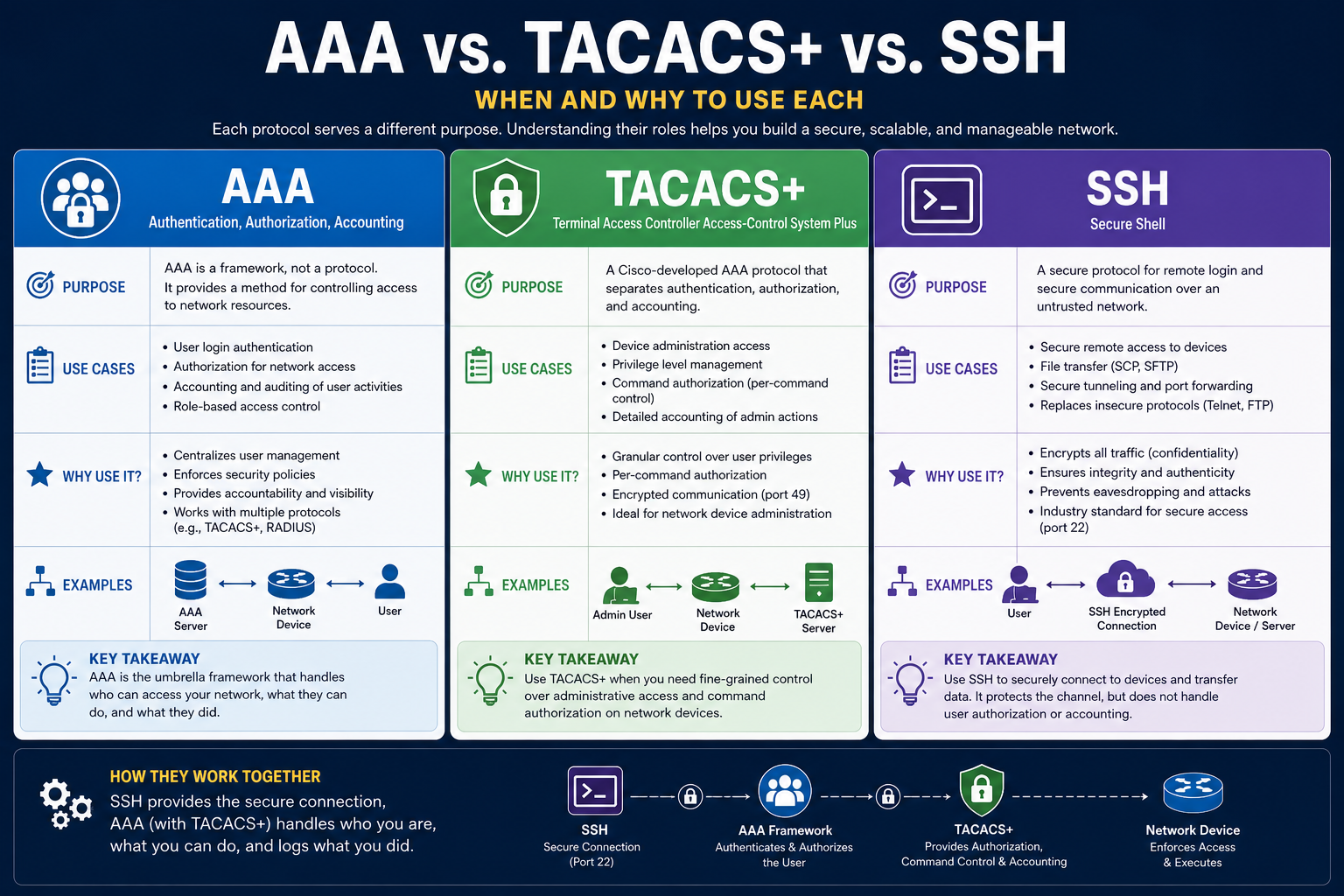
AAA is a foundational security framework that governs how users interact with network resources. It is built around three key principles: authentication, authorization, and accounting. Authentication ensures that users are who they claim to be, typically through credentials like usernames and passwords, tokens, or certificates. Authorization comes next, determining what actions those authenticated users are allowed to perform. Accounting, the final component, logs and tracks user activity for monitoring, auditing, and compliance purposes.
Unlike standalone protocols, AAA is a conceptual structure that depends on supporting technologies to function. It provides consistency across devices and systems, ensuring that access policies are applied uniformly. This becomes especially important in environments with many users and devices, where manual access control would be impractical and error-prone.
Why AAA Matters in Modern Networks
As networks grow in complexity, the need for centralized control becomes more critical. Without AAA, organizations would rely on local user accounts configured individually on each device, leading to inconsistencies and security gaps. AAA eliminates this problem by centralizing authentication and policy enforcement.
Another key advantage of AAA is visibility. The accounting function provides detailed logs of user activity, which can be analyzed to detect unusual behavior, investigate incidents, or meet regulatory requirements. This level of insight is essential in today’s threat landscape, where attacks can be subtle and prolonged.
Deep Dive into Authentication
Authentication is the first checkpoint in the AAA process. It establishes trust by verifying user identity. This can be done through various methods, ranging from simple passwords to multi-factor authentication systems.
Strong authentication mechanisms reduce the risk of unauthorized access. However, authentication alone is not enough. A user may be legitimate but still should not have unrestricted access to all resources. This is where authorization becomes essential.
Understanding Authorization in Detail
Authorization defines what a user can do after being authenticated. It enforces policies that limit access based on roles, responsibilities, or other criteria. For example, a network administrator may have full control over a device, while a junior technician may only have permission to view configurations.
Granular authorization is particularly important in sensitive environments. It prevents accidental or malicious changes by ensuring that users only have the permissions necessary for their tasks. This principle, often referred to as least privilege, is a cornerstone of modern security practices.
The Importance of Accounting
Accounting completes the AAA cycle by recording user actions. These logs can include login times, commands executed, configuration changes, and more.
This information is invaluable for troubleshooting and auditing. If a network issue arises, administrators can review logs to determine what changes were made and by whom. Similarly, in the event of a security breach, accounting data provides a trail that can help identify the source and scope of the problem.
Introduction to TACACS+
TACACS+ is one of the primary protocols used to implement AAA. It is designed to provide centralized authentication, authorization, and accounting services for network devices.
One of its defining characteristics is the separation of AAA functions. Unlike some other protocols, TACACS+ handles authentication, authorization, and accounting independently. This separation allows for more precise control over user actions, making it a preferred choice for environments that require strict security policies.
How TACACS+ Enhances Security
TACACS+ offers several features that strengthen network security. One of the most important is full encryption of communication between the client and the server. This ensures that sensitive information, including usernames, passwords, and command data, is protected from interception.
Another advantage is its support for command-level authorization. Administrators can define exactly which commands a user is allowed to execute on a device. This level of control is particularly useful in large organizations where multiple administrators share responsibilities.
Centralized Management with TACACS+
Centralization is a key benefit of TACACS+. Instead of configuring access controls on each device individually, administrators can manage policies from a single server. This simplifies administration and ensures consistency across the network.
When a user attempts to access a device, the device communicates with the TACACS+ server to verify credentials and determine permissions. This process happens seamlessly, providing both security and convenience.
Exploring SSH and Its Role
SSH, or Secure Shell, serves a different purpose from AAA and TACACS+. It is a protocol designed to provide secure communication over a network.
When a user connects to a device using SSH, the session is encrypted, protecting data from eavesdropping or tampering. This is especially important when managing devices over untrusted networks, such as the internet.
Why SSH Replaced Older Protocols
Before SSH became widely adopted, protocols like Telnet were commonly used for remote access. However, these older methods transmitted data in plain text, making them vulnerable to interception.
SSH addressed this weakness by introducing strong encryption. It ensures that all data exchanged during a session remains confidential and intact. As a result, SSH has become the standard for secure remote management.
Key Features of SSH
SSH provides several important capabilities beyond encryption. It supports secure login, command execution, and file transfer. It also uses key-based authentication, which can be more secure than traditional passwords.
Another advantage of SSH is its ability to establish secure tunnels. These tunnels can be used to protect other types of network traffic, adding an extra layer of security.
Comparing Roles: AAA vs. TACACS+ vs. SSH
Although these technologies are often discussed together, their roles are distinct. AAA defines the overall framework for access control. TACACS+ implements that framework by providing centralized services. SSH, on the other hand, secures the communication channel between users and devices.
Understanding this distinction is crucial. Treating them as interchangeable can lead to misconfigurations and security gaps. Instead, they should be seen as complementary components of a comprehensive security strategy.
When AAA Becomes Essential
AAA is indispensable in environments where multiple users access shared resources. It ensures that access is controlled, monitored, and consistent.
In small networks, local authentication might be sufficient. However, as the number of users and devices increases, centralized management becomes necessary. AAA provides the structure needed to handle this complexity effectively.
Ideal Use Cases for TACACS+
TACACS+ is particularly well-suited for administrative access to network devices. Its ability to provide detailed authorization and full encryption makes it a strong choice for secure environments.
Organizations that require strict control over administrator actions often rely on TACACS+. It allows them to enforce policies at a granular level, reducing the risk of errors or misuse.
Situations Where SSH Is Critical
SSH should be used whenever secure remote access is required. It is the standard method for managing servers, routers, switches, and other devices.
Even in internal networks, SSH is important. Threats are not always external, and unencrypted communication can still be exploited. Using SSH ensures that sensitive data remains protected at all times.
How These Technologies Work Together
In a typical setup, SSH provides the secure connection to a device. Once the connection is established, AAA policies determine whether the user can log in and what actions they can perform. TACACS+ facilitates this process by handling the communication between the device and the authentication server.
This layered approach enhances security. Even if one component is compromised, the others continue to provide protection. For example, encrypted communication prevents interception, while centralized authentication ensures that only authorized users gain access.
Building a Secure Access Strategy
Combining AAA, TACACS+, and SSH allows organizations to build a robust access control system. Each component addresses a different aspect of security, creating a comprehensive solution.
A well-designed strategy begins with defining access policies. These policies should align with organizational needs and follow best practices, such as least privilege. TACACS+ can then be used to enforce these policies, while SSH ensures secure communication.
Common Mistakes to Avoid
One common mistake is relying solely on SSH without implementing AAA. While SSH secures the connection, it does not provide centralized control or detailed logging.
Another mistake is using weak authentication methods. Even with AAA and TACACS+, poor credential management can undermine security. Strong passwords, multi-factor authentication, and regular audits are essential.
Scalability and Future Growth
As networks continue to expand, scalability becomes increasingly important. AAA frameworks supported by protocols like TACACS+ are designed to handle growth efficiently.
Centralized systems can easily accommodate new devices and users, reducing administrative overhead. This makes them ideal for organizations planning for future expansion.
The Bigger Picture
AAA, TACACS+, and SSH are not just technical tools; they are part of a broader approach to security. Together, they help create an environment where access is controlled, actions are monitored, and communication is protected.
By understanding their roles and using them effectively, organizations can significantly reduce their risk exposure. This layered approach is essential in a world where cyber threats are constantly evolving.
As technology advances, the principles behind AAA, TACACS+, and SSH remain relevant. While new tools and protocols may emerge, the need for authentication, authorization, accounting, and secure communication will continue to be fundamental.
Adapting these technologies to modern environments, such as cloud and hybrid networks, ensures that security keeps pace with innovation. Organizations that invest in understanding and implementing these concepts are better positioned to protect their systems and data.
Advanced Policy Design with AAA
Designing effective AAA policies requires more than simply enabling authentication and logging. It involves carefully defining who should have access, under what conditions, and to what extent. Policies should reflect real operational needs while minimizing unnecessary privileges. A well-structured policy framework ensures that users only interact with the systems and commands relevant to their responsibilities. This not only improves security but also reduces the risk of human error.
In advanced environments, policies often incorporate contextual elements such as time of access, location, and device type. For example, administrative access may be restricted to specific hours or limited to trusted networks. These refinements enhance control without significantly impacting usability.
Role-Based Access Control in Practice
Role-Based Access Control, often abbreviated as RBAC, is a common approach used within AAA systems. Instead of assigning permissions individually to each user, roles are created based on job functions. Users are then assigned to these roles, inheriting the associated permissions.
This method simplifies management, especially in large organizations. When responsibilities change, administrators can simply update role assignments rather than reconfiguring permissions across multiple systems. RBAC also improves consistency, ensuring that users with similar roles have the same level of access.
Command-Level Authorization with TACACS+
One of the standout features of TACACS+ is its ability to enforce command-level authorization. This means that even after a user successfully logs in, every command they attempt to execute can be evaluated against predefined policies.
For instance, a user might be allowed to view system configurations but not modify them. If they attempt to run a restricted command, the TACACS+ server can deny the request in real time. This level of granularity is particularly valuable in environments where strict control over administrative actions is required.
Command-level authorization also supports accountability. Since each command is verified and logged, it becomes easier to trace actions back to specific users, reinforcing responsible behavior.
Enhancing Accountability Through Detailed Logging
Accounting within AAA systems provides a rich source of data for monitoring and analysis. Detailed logs can reveal patterns in user behavior, highlight inefficiencies, and uncover potential security threats.
For example, repeated failed login attempts may indicate a brute-force attack, while unusual command sequences could signal unauthorized activity. By analyzing these logs, organizations can respond proactively to emerging risks.
Effective logging also supports compliance efforts. Many industries require organizations to maintain records of user activity, particularly when dealing with sensitive data. AAA accounting ensures that these requirements are met with minimal effort.
Integrating Multi-Factor Authentication
Multi-Factor Authentication adds an extra layer of security to the authentication process. Instead of relying solely on passwords, it requires users to provide additional verification, such as a one-time code or biometric data.
When integrated with AAA systems, multi-factor authentication significantly reduces the likelihood of unauthorized access. Even if credentials are compromised, attackers would still need the additional factor to gain entry.
This approach is becoming increasingly important as cyber threats grow more sophisticated. It is especially recommended for administrative accounts and remote access scenarios.
SSH Key-Based Authentication
SSH supports key-based authentication, which is often considered more secure than traditional password-based methods. In this approach, a pair of cryptographic keys is used: a private key kept by the user and a public key stored on the device.
When a connection is initiated, the device verifies the user’s identity using these keys. Since the private key is never transmitted over the network, the risk of interception is minimized.
Key-based authentication also improves convenience. Users can access systems without repeatedly entering passwords, while administrators maintain strong security controls.
Securing SSH Configurations
While SSH is inherently secure, improper configuration can weaken its effectiveness. Best practices include disabling outdated protocol versions, enforcing strong encryption algorithms, and limiting access to trusted users.
Another important measure is restricting login attempts and implementing timeout policies. These controls help prevent brute-force attacks and reduce the risk of unauthorized access.
Administrators should also monitor SSH logs regularly. This ensures that any suspicious activity is detected and addressed promptly.
High Availability for TACACS+ Servers
In critical environments, relying on a single TACACS+ server can create a point of failure. If the server becomes unavailable, users may be unable to authenticate, disrupting operations.
To address this, organizations often deploy multiple TACACS+ servers in a redundant configuration. Devices can be configured to fall back to secondary servers if the primary one is unreachable.
This approach ensures continuous access while maintaining centralized control. It is an essential consideration for networks that require high availability.
Fallback Mechanisms and Local Authentication
Even with centralized systems in place, fallback mechanisms are necessary. In the event that TACACS+ servers are unreachable, devices can revert to local authentication methods.
This ensures that administrators can still access devices during outages. However, fallback access should be carefully controlled and monitored to prevent misuse.
Balancing convenience and security is key. While fallback mechanisms are important, they should not become a loophole that bypasses centralized policies.
Performance Considerations
Implementing AAA and TACACS+ introduces additional communication between devices and servers. While this overhead is typically minimal, it can become noticeable in large-scale deployments.
Optimizing performance involves ensuring that servers are properly sized and network latency is minimized. Caching mechanisms can also help reduce the need for repeated authentication requests.
Regular testing and monitoring ensure that the system continues to perform efficiently as the network grows.
Encryption Strength and Cryptographic Standards
Encryption is a fundamental aspect of both TACACS+ and SSH. Ensuring that strong cryptographic standards are used is critical for maintaining security.
Outdated algorithms should be avoided, as they may be vulnerable to modern attacks. Regular updates and configuration reviews help ensure that systems remain aligned with current best practices.
Organizations should also stay informed about emerging threats and adjust their configurations accordingly.
Audit and Compliance Strategies
AAA systems play a central role in meeting audit and compliance requirements. By providing detailed records of user activity, they enable organizations to demonstrate accountability and transparency.
Auditors often look for evidence of controlled access, proper authorization, and comprehensive logging. AAA frameworks supported by TACACS+ make it easier to meet these expectations.
Regular audits of access policies and logs help identify gaps and ensure ongoing compliance. This proactive approach reduces the risk of penalties and strengthens overall security posture.
Training and Operational Awareness
Technology alone is not enough to ensure security. Administrators and users must understand how to use these systems effectively. Training programs should cover best practices for authentication, authorization, and secure access.
Awareness also extends to recognizing potential threats, such as phishing attempts or unauthorized access requests. Educated users are less likely to make mistakes that could compromise security.
Continuous learning is essential, as both technology and threats evolve over time.
Adapting to Cloud and Hybrid Environments
Modern networks often extend beyond traditional on-premises infrastructure. Cloud and hybrid environments introduce new challenges for access control and security.
AAA principles remain relevant in these settings, but implementation may تختلف depending on the platform. Integration with cloud-based identity services can provide centralized control across diverse environments.
SSH continues to play a role in secure access, particularly for managing virtual machines and other resources. TACACS+ may also be adapted or supplemented with other protocols to meet the needs of cloud-based systems.
Zero Trust and the Evolution of Access Control
The concept of Zero Trust is gaining traction as a modern security model. It assumes that no user or device should be trusted by default, even if they are within the network perimeter.
AAA frameworks align well with this approach, as they enforce strict authentication and authorization at every step. TACACS+ supports granular control, while SSH ensures secure communication.
Implementing Zero Trust requires a shift in mindset, focusing on continuous verification rather than one-time authentication.
Incident Response and Forensics
In the event of a security incident, AAA logs become a critical resource. They provide detailed information about user actions, helping investigators understand what happened and how to respond.
TACACS+ logs, in particular, can reveal which commands were executed and when. This level of detail is invaluable for identifying the root cause of an issue and preventing recurrence.
Effective incident response plans should include procedures for analyzing these logs and taking appropriate action.
Balancing Security and Usability
One of the ongoing challenges in network security is finding the right balance between protection and convenience. Overly restrictive policies can hinder productivity, while overly permissive ones increase risk.
AAA, TACACS+, and SSH provide the tools needed to strike this balance. By carefully designing policies and configurations, organizations can achieve strong security without compromising efficiency.
Regular feedback from users and administrators helps refine this balance over time.
Future Trends in Secure Access
As technology continues to evolve, new approaches to authentication and access control are emerging. Passwordless authentication, biometric verification, and adaptive security measures are becoming more common.
Despite these advancements, the core principles of AAA remain unchanged. Authentication, authorization, and accounting will continue to form the foundation of secure access.
TACACS+ and SSH may also evolve, incorporating new features and stronger encryption methods to address emerging threats. Staying informed about these developments is essential for maintaining a secure environment.
Successfully implementing AAA, TACACS+, and SSH requires careful planning, ongoing management, and continuous improvement. These technologies are most effective when used together, each addressing a specific aspect of security.
By leveraging their strengths, organizations can create a layered defense that protects against a wide range of threats. This approach not only secures systems but also builds confidence in the integrity and reliability of the network.
Operational Deployment Strategies
Deploying AAA, TACACS+, and SSH in a real-world environment requires a structured approach that aligns with organizational goals and technical requirements. The process typically begins with assessing the existing infrastructure, identifying critical assets, and defining access requirements. From there, administrators can design a centralized authentication architecture that integrates seamlessly with current systems.
A phased deployment is often the most effective method. Starting with a small group of devices allows teams to test configurations, identify potential issues, and refine policies before scaling across the network. This gradual rollout reduces disruption and ensures a smoother transition to centralized access control.
Standardizing Configuration Across Devices
Consistency is essential when implementing AAA and TACACS+. Network devices should follow standardized configuration templates to ensure uniform behavior. These templates define how devices communicate with authentication servers, handle fallback mechanisms, and enforce access policies.
Standardization minimizes configuration errors and simplifies troubleshooting. When every device follows the same structure, administrators can quickly identify and resolve issues without needing to analyze unique configurations for each system.
Automation tools can further enhance this process by applying configurations programmatically, reducing manual effort and improving accuracy.
User Lifecycle Management
Managing user accounts effectively is a critical component of AAA. This includes provisioning new users, updating permissions as roles change, and deactivating accounts when they are no longer needed.
Centralized systems make this process more efficient by allowing administrators to manage accounts from a single interface. Changes are applied consistently across all connected devices, reducing the risk of orphaned accounts or outdated permissions.
Regular reviews of user access ensure that permissions remain aligned with current responsibilities. This ongoing maintenance is essential for maintaining security over time.
Segmentation and Access Control Boundaries
Network segmentation plays an important role in enhancing security. By dividing the network into distinct zones, organizations can control access more effectively and limit the impact of potential breaches.
AAA policies can be tailored to each segment, ensuring that users only access the resources relevant to their roles. TACACS+ supports this approach by enforcing granular authorization rules, while SSH provides secure access within and across segments.
This layered structure creates multiple barriers for attackers, making it more difficult to move laterally within the network.
Monitoring and Continuous Improvement
Security is not a one-time implementation but an ongoing process. Continuous monitoring of AAA logs, TACACS+ activity, and SSH sessions provides valuable insights into system performance and potential threats.
Administrators should establish regular review cycles to analyze logs, identify anomalies, and update policies as needed. This proactive approach helps detect issues early and ensures that the system adapts to changing conditions.
Feedback from these monitoring efforts can also guide improvements in configuration and policy design, leading to a more resilient security posture.
Handling Privileged Access
Privileged accounts, such as those used by network administrators, require special attention. These accounts have extensive permissions and can significantly impact system integrity if misused.
AAA frameworks allow organizations to implement stricter controls for privileged users, including enhanced authentication methods and detailed logging. TACACS+ can enforce command-level restrictions, ensuring that even administrators operate within defined boundaries.
Limiting the use of shared accounts and assigning unique credentials to each administrator improves accountability and reduces risk.
Integration with Identity Systems
Modern environments often rely on centralized identity systems to manage user information. Integrating AAA with these systems streamlines authentication and ensures consistency across platforms.
This integration allows users to access multiple systems using a single set of credentials, simplifying the user experience while maintaining strong security controls. It also enables administrators to manage identities more efficiently, reducing duplication and administrative overhead.
Such integration is particularly valuable in large organizations with diverse infrastructure, including on-premises and cloud-based resources.
Managing Device Access at Scale
As networks grow, the number of devices requiring secure access increases significantly. Managing this scale requires efficient tools and strategies.
Centralized AAA systems supported by TACACS+ enable administrators to handle large numbers of devices without sacrificing control. Policies can be applied globally, ensuring consistent enforcement across the network.
SSH remains the primary method for secure device access, providing a reliable and encrypted channel for management tasks. Automation and orchestration tools can further enhance scalability by streamlining repetitive tasks.
Resilience and Disaster Recovery
Ensuring that access control systems remain operational during disruptions is critical. Redundant TACACS+ servers, backup configurations, and failover mechanisms help maintain availability in the event of failures.
Disaster recovery plans should include procedures for restoring AAA services and verifying system integrity. Regular testing of these plans ensures that they remain effective and up to date.
Maintaining secure backups of configurations and logs is also important, as they provide essential information for recovery and analysis.
Addressing Insider Threats
While external attacks often receive significant attention, insider threats can be equally damaging. Employees or contractors with legitimate access may intentionally or unintentionally compromise security.
AAA systems help mitigate this risk by enforcing strict access controls and maintaining detailed activity logs. TACACS+ enhances this protection by monitoring command execution, while SSH ensures secure communication channels.
Regular audits and behavioral analysis can help identify unusual activity patterns, enabling organizations to respond before significant damage occurs.
Policy Enforcement and Governance
Strong governance ensures that security policies are consistently applied and aligned with organizational objectives. This includes defining clear rules for access, monitoring compliance, and enforcing consequences for violations.
AAA frameworks provide the tools needed to implement and enforce these policies effectively. TACACS+ supports detailed authorization controls, while accounting functions ensure that all actions are recorded for review.
Establishing clear governance structures helps maintain accountability and ensures that security remains a priority across the organization.
Optimizing User Experience
While security is the primary focus, user experience should not be overlooked. Systems that are difficult to use may lead to workarounds that compromise security.
AAA and SSH can be configured to provide a seamless experience, such as through single sign-on and key-based authentication. These features reduce friction while maintaining strong protection.
Balancing usability and security requires careful planning and ongoing feedback from users. Adjustments should be made as needed to ensure that systems remain both secure and practical.
Evolving Threat Landscape
The threat landscape continues to evolve, with attackers developing new techniques to bypass security measures. Staying ahead of these threats requires continuous adaptation and improvement.
AAA, TACACS+, and SSH must be regularly updated and reviewed to ensure they remain effective. This includes applying patches, updating configurations, and adopting new security practices as they emerge.
Organizations should also invest in threat intelligence and security research to better understand potential risks and prepare accordingly.
Automation and Infrastructure as Code
Automation is becoming an integral part of network management. Infrastructure as Code allows administrators to define configurations in a programmable format, enabling consistent and repeatable deployments.
AAA and TACACS+ configurations can be integrated into these workflows, ensuring that access control policies are applied automatically as new devices are added.
This approach reduces manual errors, improves efficiency, and supports rapid scaling of infrastructure. SSH continues to play a role in secure automation processes, providing encrypted communication for scripts and tools.
Cross-Team Collaboration
Effective security implementation requires collaboration between multiple teams, including network engineers, security professionals, and system administrators.
AAA frameworks serve as a common foundation for these teams, providing a unified approach to access control. TACACS+ and SSH complement this by enabling secure and controlled interactions with network devices.
Clear communication and shared responsibility ensure that security measures are consistently applied and maintained across the organization.
Long-Term Maintenance and Review
Maintaining a secure environment requires ongoing effort. Regular reviews of AAA policies, TACACS+ configurations, and SSH settings help ensure that they remain aligned with current needs and best practices.
This includes removing outdated accounts, updating permissions, and refining policies based on operational changes. Continuous improvement is key to sustaining a strong security posture.
Documentation also plays an important role, providing a reference for administrators and supporting knowledge transfer within teams.
Strategic Importance of Layered Security
The combination of AAA, TACACS+, and SSH يمثل a layered security approach that addresses multiple aspects of access control. Each component contributes to a comprehensive defense strategy, reducing the likelihood of successful attacks.
By integrating these technologies, organizations can achieve a balance between control, visibility, and protection. This layered model is essential for managing modern networks, where threats are diverse and constantly evolving.
AAA, TACACS+, and SSH are more than just technical solutions; they are fundamental building blocks of secure network operations. Their effectiveness lies in how they are implemented, managed, and continuously improved.
Organizations that invest in understanding and optimizing these technologies are better equipped to protect their systems, support their users, and adapt to future
Security Hardening Best Practices
Strengthening the implementation of AAA, TACACS+, and SSH requires a deliberate focus on hardening every layer of access control. This begins with enforcing strict authentication rules, such as complex password policies, multi-factor authentication, and regular credential rotation. Weak or reused credentials remain one of the most common entry points for attackers, making this a critical area of focus.
Hardening also includes minimizing exposure. Only necessary services should be enabled on network devices, and unused access methods must be disabled. For example, if SSH is the designated management protocol, all insecure alternatives should be turned off to eliminate unnecessary risk.
Another key practice is limiting access by source. Restricting which IP addresses or networks can initiate management connections significantly reduces the attack surface. Combined with AAA policies, this creates a strong barrier against unauthorized access attempts.
Fine-Tuning Authorization Policies
Authorization should evolve alongside organizational needs. Over time, roles change, responsibilities shift, and new systems are introduced. Regularly reviewing and refining authorization rules ensures that access remains appropriate and secure.
Granularity is essential in this process. Instead of broad permissions, policies should define specific actions that users can perform. TACACS+ makes this possible by enabling detailed command-level control, ensuring that even privileged users operate within clearly defined boundaries.
Testing authorization policies is equally important. Simulated scenarios can help verify that users have the correct level of access and that restrictions function as intended. This proactive approach prevents issues before they impact real operations.
Strengthening Accounting and Log Management
Logs generated by AAA systems and TACACS+ servers are valuable only if they are properly managed and analyzed. Centralizing log collection ensures that data from multiple devices is stored in a consistent and accessible manner.
Retention policies should be defined based on organizational and regulatory requirements. Keeping logs for an appropriate duration allows for effective auditing and forensic analysis when needed.
Equally important is real-time monitoring. Automated alerts can be configured to notify administrators of suspicious activity, such as repeated failed login attempts or unauthorized command execution. This enables rapid response to potential threats.
SSH Hardening in Depth
Although SSH is inherently secure, additional measures can further enhance its resilience. Disabling password-based authentication in favor of key-based methods is one of the most effective steps. This reduces the risk of brute-force attacks and credential theft.
Changing default settings, such as port numbers and timeout values, can also improve security. While these changes alone do not stop determined attackers, they add an extra layer of complexity that can deter automated attacks.
Limiting user access to SSH services is another important measure. Only authorized personnel should have the ability to initiate remote sessions, and their activities should be closely monitored through AAA accounting.
Periodic Audits and Validation
Regular audits are essential for maintaining a strong security posture. These audits should review configurations, access policies, and logs to ensure compliance with internal standards and external regulations.
Validation processes can include penetration testing, configuration reviews, and access verification exercises. These activities help identify weaknesses and provide opportunities for improvement.
Audits also reinforce accountability. Knowing that systems are regularly reviewed encourages adherence to established policies and best practices.
Change Management and Control
Changes to network configurations and access policies must be carefully managed. Unauthorized or poorly planned changes can introduce vulnerabilities and disrupt operations.
A structured change management process ensures that all modifications are reviewed, approved, and documented. AAA systems can support this process by logging configuration changes and identifying the individuals responsible.
This level of control not only improves security but also simplifies troubleshooting and rollback procedures when issues arise.
Adapting to Organizational Growth
As organizations expand, their access control requirements become more complex. New users, devices, and services must be integrated into existing frameworks without compromising security.
Scalable AAA architectures supported by TACACS+ allow for seamless growth. Policies can be extended to new systems, ensuring consistent enforcement across the network.
Planning for growth also involves anticipating future needs, such as increased user volume or additional security requirements. Proactive design helps avoid costly redesigns later.
Balancing Flexibility and Control
While strict security measures are necessary, systems must remain flexible enough to support business operations. Overly rigid policies can hinder productivity and lead to workarounds that weaken security.
Finding the right balance involves understanding user needs and aligning them with security objectives. AAA frameworks provide the tools to achieve this balance by enabling precise control over access while maintaining usability.
Regular feedback from users and administrators helps refine policies, ensuring they remain effective and practical.
Emerging Technologies and Integration
New technologies continue to influence how access control is implemented. Automation, artificial intelligence, and advanced analytics are being integrated into security systems to enhance detection and response capabilities.
AAA frameworks can benefit from these advancements by incorporating intelligent monitoring and adaptive policies. For example, systems can adjust access permissions based on user behavior or risk levels, providing dynamic security controls.
Integration with modern platforms ensures that AAA, TACACS+, and SSH remain relevant in evolving environments, including cloud-native and distributed systems.
Resilience Against Advanced Threats
Sophisticated attacks often target multiple layers of a network simultaneously. A well-implemented combination of AAA, TACACS+, and SSH provides resilience by addressing different aspects of security.
Even if one layer is challenged, others continue to provide protection. For instance, encrypted communication prevents interception, while strict authorization policies limit the impact of compromised accounts.
Continuous improvement and adaptation are key to maintaining this resilience. Security is an ongoing process that requires vigilance and commitment.
Building a Security-First Culture
Technology alone cannot ապահով complete protection. A security-first culture within the organization is equally important. This involves promoting awareness, encouraging responsible behavior, and ensuring that all team members understand their role in maintaining security.
Training programs, clear policies, and regular communication help reinforce this culture. When users and administrators are aligned with security goals, the effectiveness of AAA, TACACS+, and SSH is significantly enhanced.
Leadership support is also critical. Strong governance and commitment from management ensure that security remains a priority at all levels.
Long-Term Sustainability
Sustaining a secure access control system requires ongoing effort and investment. Regular updates, continuous monitoring, and periodic reviews ensure that systems remain effective over time.
Documentation plays a vital role in this process. Clear and comprehensive records of configurations, policies, and procedures support maintenance and knowledge transfer.
Planning for long-term sustainability also involves preparing for technological changes and evolving threats. Organizations that remain proactive are better equipped to adapt and maintain strong security.
Conclusion
AAA, TACACS+, and SSH each serve a distinct yet interconnected purpose in securing network environments. AAA provides the framework for managing access, TACACS+ delivers centralized control with granular authorization and detailed accounting, and SSH ensures that communication channels remain secure.
When implemented together, they create a layered defense that addresses authentication, authorization, visibility, and data protection. This integrated approach not only strengthens security but also improves operational efficiency and accountability.
The true value of these technologies lies in thoughtful implementation, continuous refinement, and alignment with organizational goals. By adopting best practices, maintaining strong governance, and fostering a culture of security awareness, organizations can build resilient systems capable of withstanding modern threats.
As networks continue to evolve, the principles behind AAA, TACACS+, and SSH will remain fundamental. Their combined use ensures that access is controlled, actions are monitored, and communication is protected—forming a solid foundation for secure and reliable network operations.