Standard Access Control Lists are one of the most essential building blocks in network traffic control and security enforcement on Cisco routers. They provide a straightforward mechanism to filter traffic based solely on the source IP address of packets passing through a router interface. Despite their simplicity, they play a critical role in controlling access to network resources, limiting unauthorized communication, and supporting basic segmentation strategies within an enterprise or organizational network.
Unlike more advanced filtering methods that inspect multiple fields in a packet, standard ACLs focus only on the origin of traffic. This makes them fast and efficient, but also more generalized in their control. Because they cannot differentiate based on destination address, protocol type, or port number, they are typically used in scenarios where broad-level control is sufficient.
Understanding how to properly configure and apply standard ACLs is an important skill for network engineers, as it forms the foundation for more complex security policies and routing behaviors in Cisco-based infrastructures.
Understanding the Role of ACLs in Network Security
Access Control Lists act as traffic filters that determine whether packets are allowed to pass through a router interface or are denied entry. They function as rule-based decision makers, evaluating each packet against a predefined set of conditions.
In the case of standard ACLs, the decision-making process is based entirely on the source IP address of the packet. If the source matches a permit rule, the packet is forwarded. If it matches a deny rule, the packet is dropped. If no rule matches, an implicit deny action is applied automatically.
This mechanism allows administrators to control which devices or networks can communicate with specific parts of an infrastructure. For example, a standard ACL can prevent an unauthorized subnet from accessing sensitive internal systems while still allowing trusted internal traffic to flow freely.
Structure and Logic of Standard ACLs
A standard ACL is composed of sequential rules that are processed from top to bottom. Each rule contains a condition and an action. The condition specifies the source IP address or range of addresses, while the action determines whether the traffic is permitted or denied.
The order of rules is extremely important. Once a packet matches a rule, no further rules are evaluated. This means that more specific rules should be placed before broader ones to avoid unintended filtering behavior.
At the end of every ACL, there is an implicit deny statement that blocks all traffic not explicitly permitted. This ensures a secure default posture but also requires careful planning to avoid accidental network disruption.
Wildcard Masks and Their Importance
When configuring standard ACLs, wildcard masks are used to define IP address ranges. A wildcard mask is essentially the inverse of a subnet mask and is used to specify which parts of an IP address should be matched exactly and which parts can vary.
This allows administrators to define precise or broad matching conditions depending on the requirement. For example, a wildcard mask can be used to match a single host, an entire subnet, or multiple networks.
Understanding how wildcard masks function is crucial because incorrect configuration can lead to overly permissive or overly restrictive access rules. This directly impacts network availability and security posture.
Basic Configuration Approach
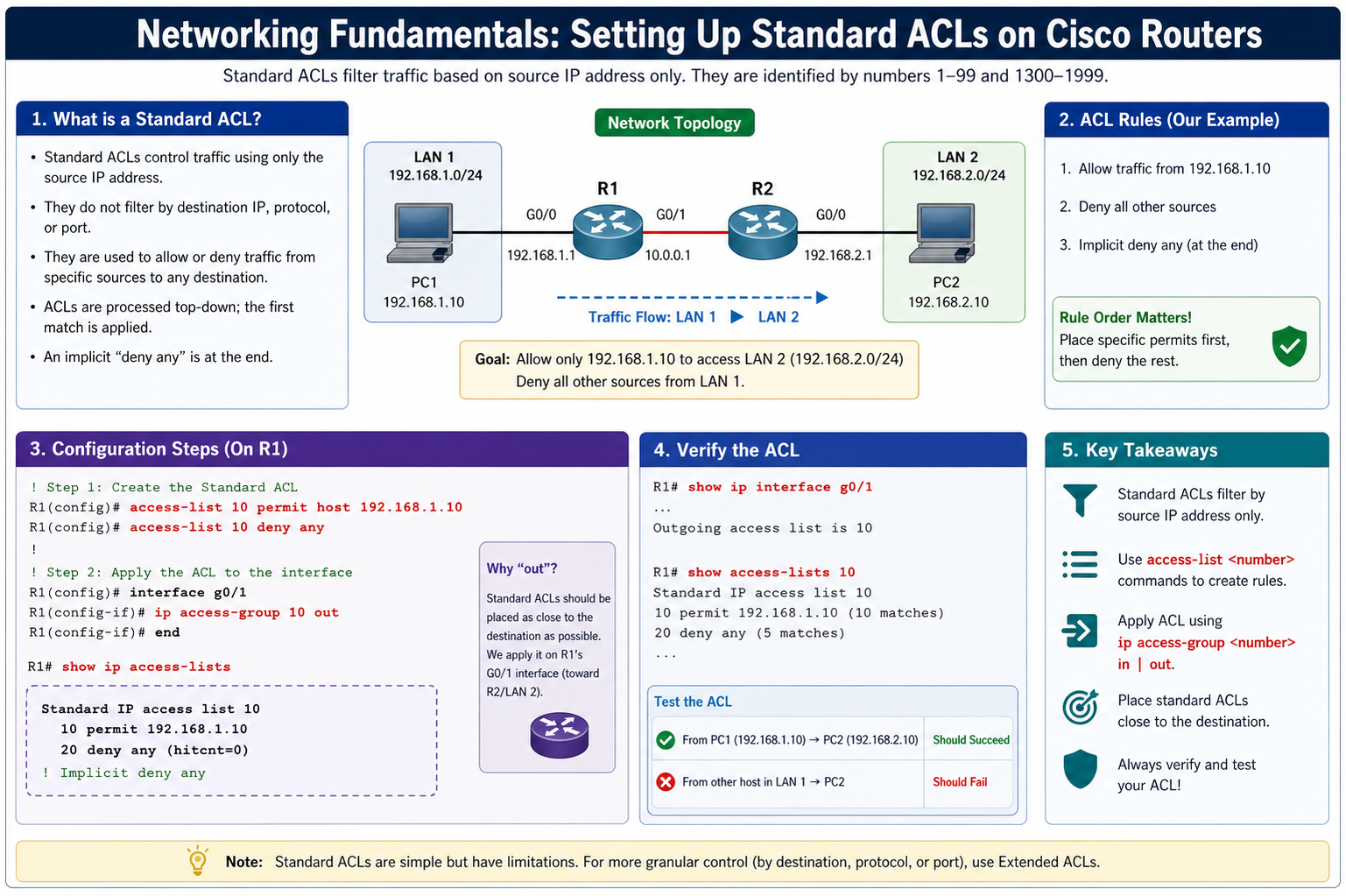
Configuring a standard ACL on a Cisco router involves defining the ACL entries and then applying the ACL to a specific interface. The process typically follows a structured sequence.
First, the ACL is created by assigning it a number within the standard ACL range. Each entry is then added with a permit or deny statement, followed by the source IP address and wildcard mask.
Once the ACL is defined, it must be applied to a router interface. This step determines the direction of traffic filtering, which can be inbound or outbound. The placement of the ACL significantly affects how traffic is controlled within the network.
Inbound ACLs filter traffic as it enters an interface, while outbound ACLs filter traffic as it exits. Choosing the correct direction depends on the desired security policy and network topology.
Inbound vs Outbound Filtering Behavior
Inbound filtering is used when traffic needs to be controlled as soon as it enters the router interface. This approach is often more efficient because it prevents unwanted traffic from being processed further within the router.
Outbound filtering, on the other hand, is applied after routing decisions have been made. This means that traffic is filtered before it leaves the router interface toward its destination network.
Each method has its own advantages. Inbound filtering is generally preferred for conserving router resources, while outbound filtering provides more control over traffic leaving a specific interface.
Practical Application of Standard ACLs
In real-world network environments, standard ACLs are often used to restrict access to sensitive network segments. For instance, an organization may allow only specific internal networks to access a server subnet while blocking all other sources.
They are also used to control administrative access to network devices. By limiting which management stations can connect to routers or switches, administrators can reduce the risk of unauthorized configuration changes.
Another common use case is traffic segmentation, where different departments or user groups are restricted from accessing each other’s network resources based on source IP ranges.
Processing Order and Implicit Deny Concept
One of the most important aspects of ACL behavior is the top-down processing logic. Each incoming or outgoing packet is evaluated against the ACL entries in sequential order.
As soon as a match is found, the corresponding action is executed, and no further evaluation occurs. This makes rule ordering a critical design consideration.
At the end of every ACL, an implicit deny rule automatically blocks any traffic that does not match a permit statement. This ensures that only explicitly allowed traffic is permitted, reinforcing a default-deny security model.
However, this also means that failing to include proper permit statements can unintentionally block legitimate network traffic.
Best Practices for Configuration and Management
Effective implementation of standard ACLs requires careful planning and documentation. Network administrators should clearly define the purpose of each ACL before configuration to avoid conflicts or overlapping rules.
It is also important to apply ACLs as close to the destination as possible when using standard ACLs. Since they only filter based on source address, placing them too close to the source may unintentionally block traffic that should be allowed to reach other destinations.
Regular review of ACL configurations is essential to ensure that outdated or unnecessary rules do not remain in place. Over time, network changes can make older ACL entries irrelevant or even harmful to current operations.
Consistency in naming conventions, documentation practices, and rule structure also helps maintain clarity and reduces the risk of configuration errors.
Troubleshooting Standard ACL Issues
When network connectivity issues arise, ACLs are often one of the first areas to investigate. Misconfigured rules can easily lead to unexpected traffic blocking.
Common issues include incorrect wildcard masks, improper rule ordering, or applying the ACL in the wrong direction on an interface. Each of these can result in legitimate traffic being denied.
Troubleshooting typically involves reviewing ACL entries, checking interface assignments, and verifying packet flow against expected behavior. Careful analysis helps identify whether the ACL is functioning as intended or interfering with normal communication.
Security Implications of Standard ACL Usage
Although standard ACLs are simple in design, they still provide an important layer of network security. By controlling traffic at the router level, they help enforce organizational policies and reduce exposure to unauthorized access.
However, because they rely only on source IP addresses, they should not be considered a complete security solution. They are most effective when combined with other security mechanisms that provide deeper inspection and control.
Their simplicity makes them less resource-intensive, which is beneficial in environments where performance is a concern, but it also limits their precision.
Advanced Concepts in Standard Access Control Lists
As network environments grow more complex, the use of standard Access Control Lists also becomes more strategic. While the basic function of filtering traffic based on source IP remains the same, advanced implementation focuses on how ACLs are positioned, optimized, and integrated into broader network policies. Understanding these deeper concepts allows network engineers to design more efficient and secure routing infrastructures.
Standard ACLs, despite their simplicity, can significantly influence traffic flow when used thoughtfully. Their effectiveness depends not only on correct syntax but also on placement, direction, and interaction with routing decisions. In larger networks, even a small misconfiguration can lead to unintended access restrictions or traffic inefficiencies.
Strategic Placement in Network Design
One of the most important advanced considerations is where to place a standard ACL within the network topology. Because standard ACLs only examine the source IP address, they do not differentiate between different destinations. This limitation means that placement must be carefully planned to avoid overblocking traffic.
In practice, standard ACLs are often placed closer to the destination network rather than the source. This allows the same source to communicate with other permitted networks while restricting access only where necessary. Poor placement near the source can unintentionally restrict access to multiple destinations, reducing network flexibility.
Strategic placement requires a clear understanding of traffic flow patterns. Network engineers must analyze how data moves between subnets, devices, and services before applying ACL rules.
Impact on Routing and Packet Flow
Standard ACLs do not change routing decisions, but they directly affect whether routed packets are forwarded or dropped. When a packet enters a router, it is first checked against the routing table to determine the outgoing interface. After this decision, ACL rules are applied depending on whether they are configured inbound or outbound.
This interaction between routing and filtering means that ACLs effectively act as a control layer on top of routing logic. Even if a valid route exists, a packet can still be dropped if it does not meet ACL conditions.
Understanding this relationship is essential for troubleshooting and optimization. It ensures that network engineers can differentiate between routing issues and access control restrictions.
Efficient Rule Design and Optimization
In larger configurations, efficiency becomes a key concern. Although standard ACLs are relatively simple, poorly designed rule sets can still impact performance and manageability.
Rules should be written in a way that minimizes unnecessary processing. Since ACLs are evaluated sequentially, placing frequently matched rules at the top can reduce evaluation time. This helps improve overall router performance, especially in high-traffic environments.
Redundant or overlapping rules should be avoided, as they increase complexity without adding value. Each rule should serve a clear purpose and contribute to the overall security or traffic management objective.
Use of Host and Network-Based Filtering
Standard ACLs support both individual host filtering and broader network-based filtering. This flexibility allows administrators to control access at different levels of granularity.
Host-based filtering is used when specific devices need to be allowed or denied access. This is useful in scenarios such as restricting administrative access or isolating compromised systems.
Network-based filtering, on the other hand, applies rules to entire subnets. This approach is more scalable and is commonly used in enterprise environments where large groups of devices share similar access requirements.
Choosing between host and network filtering depends on the security policy and the level of control required.
Role in Segmentation and Policy Enforcement
Standard ACLs play an important role in enforcing network segmentation policies. By controlling which source networks can access certain areas of the infrastructure, they help maintain logical separation between departments, systems, or user groups.
This segmentation is essential for maintaining security boundaries. For example, development networks can be restricted from accessing production systems, while still allowing controlled communication for specific services.
Although more advanced technologies exist for segmentation, standard ACLs provide a simple and effective layer of control that can be implemented quickly and efficiently.
Integration with Other Network Features
In modern network environments, ACLs are rarely used in isolation. They are often combined with other features such as routing protocols, NAT configurations, and security policies.
When integrated properly, ACLs can enhance the effectiveness of these systems. For example, they can be used to limit which internal networks are translated by NAT, or to restrict routing updates between specific segments.
This integration requires careful coordination to avoid conflicts. Misaligned configurations between ACLs and other features can lead to connectivity issues or unintended access restrictions.
Scalability Considerations in Larger Networks
As networks expand, managing ACLs becomes more challenging. A small number of rules may work efficiently in a simple network, but large-scale environments require more structured approaches.
Scalability concerns include rule duplication, management overhead, and troubleshooting complexity. Without proper organization, ACLs can become difficult to maintain and prone to configuration errors.
To address this, administrators often adopt standardized naming conventions, structured documentation, and centralized management practices. These approaches help ensure that ACLs remain manageable as the network grows.
Security Limitations and Risk Awareness
Although standard ACLs provide valuable filtering capabilities, they also have inherent limitations. Because they only examine source IP addresses, they cannot detect malicious activity based on content, destination, or application behavior.
This limitation means that they should not be relied upon as the sole security mechanism. Instead, they should be part of a layered security model that includes firewalls, intrusion detection systems, and encryption technologies.
Understanding these limitations is critical for designing realistic and effective security strategies.
Troubleshooting Advanced ACL Scenarios
In more complex environments, troubleshooting ACL issues requires a systematic approach. Engineers must verify not only the ACL configuration but also routing paths, interface assignments, and network policies.
Common advanced issues include conflicts between multiple ACLs, unexpected interactions with routing protocols, and incorrect application direction. These problems can be difficult to identify without detailed analysis of traffic flow.
Tools such as packet tracing and interface monitoring are often used to isolate issues and confirm whether ACLs are functioning as intended.
Performance Considerations in High-Traffic Networks
Although standard ACLs are lightweight, they can still impact performance in high-traffic environments if not optimized properly. Each packet must be evaluated against ACL rules, which introduces processing overhead.
To minimize impact, rules should be kept concise and logically structured. Reducing the number of entries and eliminating unnecessary conditions helps maintain efficient processing.
Proper placement also contributes to performance optimization, as early filtering reduces the amount of traffic processed by the router.
Operational Maintenance and Long-Term Management
Over time, network requirements change, and ACL configurations must evolve accordingly. Regular maintenance ensures that rules remain relevant and effective.
This includes reviewing existing entries, removing outdated rules, and updating configurations to reflect new network structures. Failure to maintain ACLs can result in security gaps or unnecessary restrictions.
Documentation plays a key role in long-term management. Clear records of rule purpose, changes, and dependencies help ensure consistency across network operations.
Advanced Verification and Troubleshooting of Standard ACLs
Once standard access control lists are deployed on Cisco routers, verifying their correct operation becomes just as important as the configuration itself. Without proper validation, even a well-written ACL can silently block legitimate traffic or allow unwanted access. Verification begins with observing how the ACL interacts with live network traffic. The router provides built-in commands that display which rules are being matched and how frequently they are triggered. These match counters are critical because they reveal whether specific entries are actually being used or are simply sitting idle due to incorrect placement or logic.
A common issue encountered during verification is the mismatch between intended behavior and actual packet flow. This often happens when administrators assume traffic follows a certain path, but routing decisions send it through a different interface. Since standard ACLs filter traffic based only on source IP addresses, applying them in the wrong location can unintentionally affect multiple destinations. Careful observation of packet flow, combined with command-line verification, helps ensure that ACLs are positioned optimally.
Troubleshooting ACLs also requires attention to rule order. Cisco routers process ACL entries sequentially from top to bottom, stopping at the first match. If a general rule appears before a more specific one, it can override the intended logic. For example, permitting a broad network range before denying a single problematic host will render the deny statement ineffective. Adjusting the order of entries or restructuring the ACL resolves such conflicts.
Another key aspect of troubleshooting is recognizing the implicit deny rule present at the end of every ACL. This hidden rule blocks all traffic that does not explicitly match a permit statement. While it enhances security by default, it can also cause unexpected connectivity issues if not properly accounted for. Administrators must ensure that all necessary traffic is explicitly permitted before relying on the implicit deny to block everything else.
Optimizing ACL Placement for Performance and Security
Strategic placement of standard ACLs significantly impacts both network performance and security. Because standard ACLs evaluate only the source IP address, they are generally placed as close to the destination as possible. This approach prevents unnecessary blocking of traffic that may be intended for other destinations. Placing a standard ACL too close to the source can inadvertently restrict legitimate communication across multiple network segments.
Optimizing placement also involves understanding the router’s processing behavior. Each packet entering or leaving an interface is checked against the ACL applied to that interface. If ACLs are unnecessarily complex or applied in multiple locations, they can introduce processing overhead. While modern routers are designed to handle such tasks efficiently, poorly optimized ACLs can still affect performance in high-traffic environments.
Balancing security and performance requires thoughtful design. Administrators should aim to minimize the number of ACL entries while maintaining precise control over traffic. This can be achieved by grouping similar rules and avoiding redundant statements. Efficient ACL design not only improves performance but also simplifies management and troubleshooting.
Another consideration in optimization is the direction in which the ACL is applied. Standard ACLs can be applied inbound or outbound on an interface. Inbound ACLs filter traffic as it enters the router, while outbound ACLs filter traffic as it leaves. Choosing the correct direction depends on the desired control point. In many cases, applying ACLs outbound near the destination provides better control without unnecessarily restricting upstream traffic.
Managing ACL Changes in Live Networks
Making changes to ACLs in a live network environment requires careful planning and execution. Unlike static configurations, ACLs directly influence traffic flow, meaning that even minor modifications can have immediate and widespread effects. Administrators must approach changes with a clear understanding of the current configuration and the potential impact of new rules.
One of the safest methods for updating ACLs is to use a staged approach. Instead of modifying existing entries directly, new rules can be added in a controlled manner, tested, and then integrated fully once verified. This reduces the risk of accidental disruptions. Additionally, maintaining a backup of the current configuration ensures that changes can be rolled back quickly if unexpected issues arise.
Another important practice is documenting every change made to an ACL. Clear documentation helps maintain consistency and provides a reference for future troubleshooting. Without proper records, it becomes difficult to determine why certain rules were implemented or how they interact with other parts of the network.
Timing also plays a critical role in managing ACL changes. Implementing updates during maintenance windows minimizes the impact on users and allows administrators to focus on monitoring the network for any issues. Real-time monitoring during and after changes ensures that any problems are detected and resolved promptly.
Understanding the Limitations of Standard ACLs
While standard ACLs are useful for basic traffic filtering, they have inherent limitations that must be understood. The most significant limitation is their reliance solely on source IP addresses. This means they cannot differentiate traffic based on destination, protocol, or port number. As a result, their ability to enforce granular security policies is limited compared to more advanced filtering mechanisms.
Because of this limitation, standard ACLs are best suited for simple scenarios such as restricting access from specific networks or hosts. For more complex requirements, extended ACLs provide greater flexibility by allowing filtering based on multiple criteria. However, standard ACLs still play an important role due to their simplicity and efficiency.
Another limitation is the potential for unintended consequences when applied incorrectly. Since they do not consider the destination, placing them in the wrong location can block traffic that should be allowed. This reinforces the importance of proper placement and thorough testing.
Despite these limitations, standard ACLs remain a foundational tool in network security. When used appropriately, they provide an effective first layer of defense and help enforce basic access policies without adding unnecessary complexity.
Enhancing Security with Combined Techniques
Standard ACLs are most effective when used as part of a broader security strategy. Relying solely on ACLs for network protection is not sufficient in modern environments where threats are increasingly sophisticated. Combining ACLs with other security mechanisms creates a layered defense that is more resilient against attacks.
One common approach is integrating ACLs with authentication and authorization systems. While ACLs control which IP addresses can access certain resources, authentication systems verify the identity of users. Together, they provide both network-level and user-level security.
Firewalls and intrusion detection systems further enhance security by analyzing traffic patterns and detecting anomalies. While ACLs operate at a basic level, these advanced tools provide deeper inspection and real-time threat detection. Using ACLs to filter obvious unwanted traffic reduces the load on these systems, allowing them to focus on more complex analysis.
Network segmentation is another technique that complements ACLs. By dividing the network into smaller segments and applying ACLs between them, administrators can limit the spread of potential threats. This containment strategy is particularly important in large networks where unrestricted access can lead to widespread issues.
Best Practices for Long-Term ACL Maintenance
Maintaining ACLs over time requires discipline and consistency. As networks grow and evolve, ACLs must be updated to reflect new requirements and remove outdated rules. Without regular maintenance, ACLs can become cluttered and difficult to manage, increasing the risk of errors.
One of the most important best practices is periodic review. Administrators should regularly examine ACL configurations to ensure that all entries are still relevant and functioning as intended. Removing unused or redundant rules simplifies the ACL and improves performance.
Consistency in naming and numbering conventions also plays a key role in maintenance. Clear and logical organization makes it easier to understand the purpose of each ACL and reduces confusion during troubleshooting. Whether using numbered or named ACLs, maintaining a consistent structure is essential.
Another best practice is testing changes in a controlled environment before applying them to the production network. This allows administrators to identify potential issues without affecting live traffic. Even small changes should be tested to ensure they behave as expected.
Automation tools can also assist in ACL management by providing centralized control and reducing the likelihood of human error. While manual configuration is still common, automation becomes increasingly valuable in larger networks where consistency and efficiency are critical.
Real-World Scenarios and Practical Insights
In real-world environments, standard ACLs are often used to solve practical problems such as restricting access to sensitive systems or limiting traffic from untrusted networks. For example, an organization might use a standard ACL to block traffic from a specific IP range known to be associated with malicious activity. This simple rule can prevent potential threats from reaching internal resources.
Another scenario involves controlling access between departments within an organization. By applying ACLs at strategic points, administrators can ensure that only authorized networks can communicate with certain systems. This helps enforce organizational policies and protect sensitive data.
Educational institutions and training labs also rely on standard ACLs to create controlled environments where students can learn networking concepts without affecting the broader network. These scenarios highlight the versatility of ACLs and their importance in both production and learning environments.
Practical experience often reveals challenges that are not immediately apparent in theory. For instance, overlapping IP ranges or dynamic addressing can complicate ACL design. Administrators must adapt their strategies to account for these factors, ensuring that ACLs remain effective under changing conditions.
Future Considerations and Evolving Practices
As networking technology continues to evolve, the role of ACLs is also changing. While traditional ACLs remain relevant, new approaches to network security are emerging. Software-defined networking and automation are transforming how networks are managed, allowing for more dynamic and flexible control.
In these environments, ACLs may be implemented through centralized controllers rather than configured manually on individual devices. This shift enables more consistent policy enforcement and simplifies management. However, the fundamental principles of ACL design and placement remain the same.
Another trend is the increasing importance of IPv6. As networks transition to IPv6 addressing, ACL configurations must be updated to accommodate the new format. While the concepts are similar, the larger address space introduces new considerations for rule design and management.
Security threats are also becoming more sophisticated, requiring more advanced filtering techniques. While standard ACLs provide a basic level of protection, they must be supplemented with modern security solutions to address emerging challenges. Staying informed about these developments ensures that network administrators can adapt their strategies accordingly.
Continued Exploration
Standard ACLs on Cisco routers remain a fundamental component of network management and security. Mastering their configuration, verification, and optimization is essential for maintaining reliable and secure network operations. While they have limitations, their simplicity and efficiency make them an invaluable tool when used correctly.
By focusing on proper placement, thorough verification, and ongoing maintenance, administrators can ensure that ACLs perform as intended. Combining them with other security measures further enhances their effectiveness, creating a robust defense against potential threats.
As networks continue to grow and evolve, the principles learned from working with standard ACLs provide a strong foundation for understanding more advanced technologies. Whether in small networks or large enterprise environments, these concepts remain relevant and continue to play a vital role in modern networking.
Integrating Standard ACLs into Complex Network Architectures
As networks expand in size and complexity, standard Access Control Lists (ACLs) must be integrated thoughtfully into broader architectural designs. In small networks, ACLs are often applied in straightforward ways, but in enterprise environments, their role becomes more strategic. They are no longer just simple filters; they become part of a coordinated system that governs how traffic flows between multiple segments, departments, and services.
In complex architectures, routers often connect diverse network zones such as internal user segments, data centers, and external connections. Standard ACLs can be used to enforce baseline restrictions between these zones, particularly when the requirement is to allow or deny traffic from specific source networks. Even though they lack the granularity of extended ACLs, they still provide a lightweight and efficient mechanism for controlling access at key points.
Careful planning is required to ensure that ACLs do not conflict with routing policies or other security controls. When multiple routers and interfaces are involved, consistency becomes critical. A poorly placed ACL in one part of the network can disrupt communication across several segments. This is why administrators often design ACL strategies alongside overall network topology, ensuring that traffic filtering aligns with routing paths and organizational policies.
Another important aspect of integration is redundancy. In high-availability environments, multiple routers may handle the same traffic paths. ACL configurations must be synchronized across these devices to maintain consistent behavior during failover scenarios. Without this alignment, traffic that is allowed through one path might be blocked on another, leading to unpredictable connectivity issues.
Standard ACLs in Conjunction with Routing Protocol Behavior
Routing protocols determine how packets travel through a network, while ACLs determine whether those packets are allowed to pass. Understanding how these two elements interact is essential for effective network management. Standard ACLs can influence routing indirectly by controlling which sources are permitted to communicate across certain paths.
In some scenarios, ACLs are used to restrict routing updates themselves. By filtering which devices can send or receive routing information, administrators can protect the integrity of routing tables. This prevents unauthorized or misconfigured devices from introducing incorrect routes into the network, which could otherwise lead to traffic misdirection or outages.
Another interaction occurs when ACLs are applied to interfaces that handle dynamic routing traffic. If not carefully configured, an ACL might block legitimate routing protocol messages, causing neighbors to lose connectivity. This highlights the importance of understanding both the data plane and the control plane when implementing ACLs. Traffic filtering should never interfere with essential network operations unless explicitly intended.
Standard ACLs can also be used to influence path selection in certain designs. By restricting traffic from specific sources on one path, administrators can effectively guide it toward alternative routes. While this is not the primary purpose of ACLs, it demonstrates their flexibility when combined with routing strategies.
Security Policy Enforcement Using Standard ACLs
Security policies define what is allowed and what is prohibited within a network. Standard ACLs serve as one of the enforcement mechanisms for these policies, translating high-level rules into actionable configurations on network devices. Even though they operate at a basic level, they are often used to implement foundational security controls.
One common use case is restricting access to sensitive resources. By allowing only trusted source networks to reach critical systems, administrators can reduce the attack surface. This is particularly useful in environments where certain servers should only be accessed by specific departments or applications.
Standard ACLs are also effective for blocking known malicious sources. When an IP address or network is identified as a threat, it can be quickly denied at the router level. This immediate response helps mitigate potential attacks before they reach internal systems. While more advanced security tools provide deeper analysis, ACLs offer a fast and efficient first line of defense.
Another aspect of policy enforcement involves compliance. Many organizations are required to follow regulatory standards that mandate controlled access to data and systems. Standard ACLs can help meet these requirements by ensuring that only authorized sources can communicate with protected resources. Proper documentation and regular audits of ACL configurations support compliance efforts and demonstrate adherence to security policies.
Common Mistakes and How to Avoid Them
Despite their simplicity, standard ACLs are often misconfigured, leading to network issues that can be difficult to diagnose. One of the most common mistakes is incorrect placement. Applying a standard ACL too close to the source can block traffic that should be allowed to reach other destinations. This is why the general guideline is to place them near the destination whenever possible.
Another frequent error is misunderstanding wildcard masks. Since wildcard masks use inverse logic compared to subnet masks, it is easy to make mistakes when defining address ranges. A small miscalculation can result in either overly permissive or overly restrictive rules. Double-checking mask values and testing configurations helps prevent such issues.
Rule ordering is another area where mistakes occur. Because ACLs are processed sequentially, placing a general rule before a specific one can override the intended behavior. Administrators must carefully ترتیب their entries to ensure that the most specific conditions are evaluated first.
Neglecting the implicit deny rule is also a common problem. Failing to include necessary permit statements can lead to unintended traffic blocking. Being aware of this default behavior and explicitly defining allowed traffic ensures that the ACL functions as expected.
Finally, lack of documentation can create long-term challenges. Without clear records of why certain rules were implemented, future administrators may struggle to understand or modify the configuration. Maintaining detailed documentation helps preserve clarity and continuity.
Monitoring and Auditing ACL Effectiveness
Once ACLs are in place, ongoing monitoring is essential to ensure they continue to meet network requirements. Traffic patterns can change over time, and rules that were once appropriate may become outdated. Regularly reviewing ACL performance helps identify areas for improvement and ensures that security policies remain effective.
Monitoring involves analyzing which ACL entries are being matched and how frequently they are used. Entries that never receive matches may indicate redundant or unnecessary rules. Removing these entries simplifies the configuration and improves efficiency.
Auditing is another important practice, especially in environments with strict security requirements. Periodic audits verify that ACLs align with organizational policies and compliance standards. This process often involves cross-referencing configurations with documented requirements and making adjustments as needed.
Automation tools can assist with monitoring and auditing by providing detailed reports and alerts. These tools help administrators quickly identify anomalies or potential issues, reducing the time required for manual analysis. While automation enhances efficiency, human oversight remains crucial for interpreting results and making informed decisions.
Adapting ACL Strategies for Modern Networks
Modern networks are evolving rapidly, driven by trends such as cloud computing, virtualization, and remote connectivity. These changes require administrators to adapt their ACL strategies to new environments. While the fundamental principles remain the same, their application must evolve to address emerging challenges.
In cloud-based environments, traditional router-based ACLs may be supplemented or replaced by virtual network controls. However, the concept of filtering traffic based on source addresses still applies. Understanding standard ACLs provides a foundation for working with these newer technologies.
Remote work has also increased the importance of secure access controls. With users connecting from various locations, ACLs can help restrict access to trusted networks and prevent unauthorized connections. Combining ACLs with authentication mechanisms ensures that both the source and the user are verified.
Virtualized networks introduce additional complexity, as multiple virtual devices may share the same physical infrastructure. In such cases, ACLs must be carefully designed to maintain isolation between different virtual environments. This prevents unauthorized communication and enhances overall security.
As networks continue to grow, scalability becomes a key consideration. ACL configurations must be designed to accommodate expansion without becoming overly complex. This often involves using structured addressing schemes and consistent policies that can be easily extended.
Conclusion
Standard Access Control Lists on Cisco routers remain a vital component of network management and security. Despite their simplicity, they provide powerful capabilities when applied with careful planning and a clear understanding of their behavior. From controlling basic traffic flow to supporting broader security policies, standard ACLs serve as an essential tool in both small and large network environments.
Throughout their implementation, several key principles stand out. Proper placement ensures that traffic is filtered effectively without causing unintended disruptions. Accurate rule ordering guarantees that the desired conditions are applied correctly. Awareness of the implicit deny rule prevents accidental blocking of legitimate traffic. Together, these practices form the foundation of reliable ACL configuration.
Equally important is the ongoing process of verification, monitoring, and maintenance. Networks are dynamic, and ACLs must evolve alongside them. Regular reviews, thorough documentation, and careful change management help maintain their effectiveness over time. Avoiding common mistakes and learning from real-world scenarios further strengthens an administrator’s ability to manage ACLs წარმატ.
While standard ACLs have limitations, particularly in their lack of granularity, they remain highly relevant. When combined with other security measures such as firewalls, authentication systems, and advanced filtering techniques, they contribute to a layered defense strategy that enhances overall network protection.
Looking ahead, the role of ACLs will continue to adapt as networking technologies evolve. Whether in traditional infrastructures or modern cloud environments, the principles behind standard ACLs provide a strong foundation for understanding traffic control and security enforcement. Mastering these concepts equips network professionals with the skills needed to design, implement, and maintain secure and efficient networks in an ever-changing technological landscape.