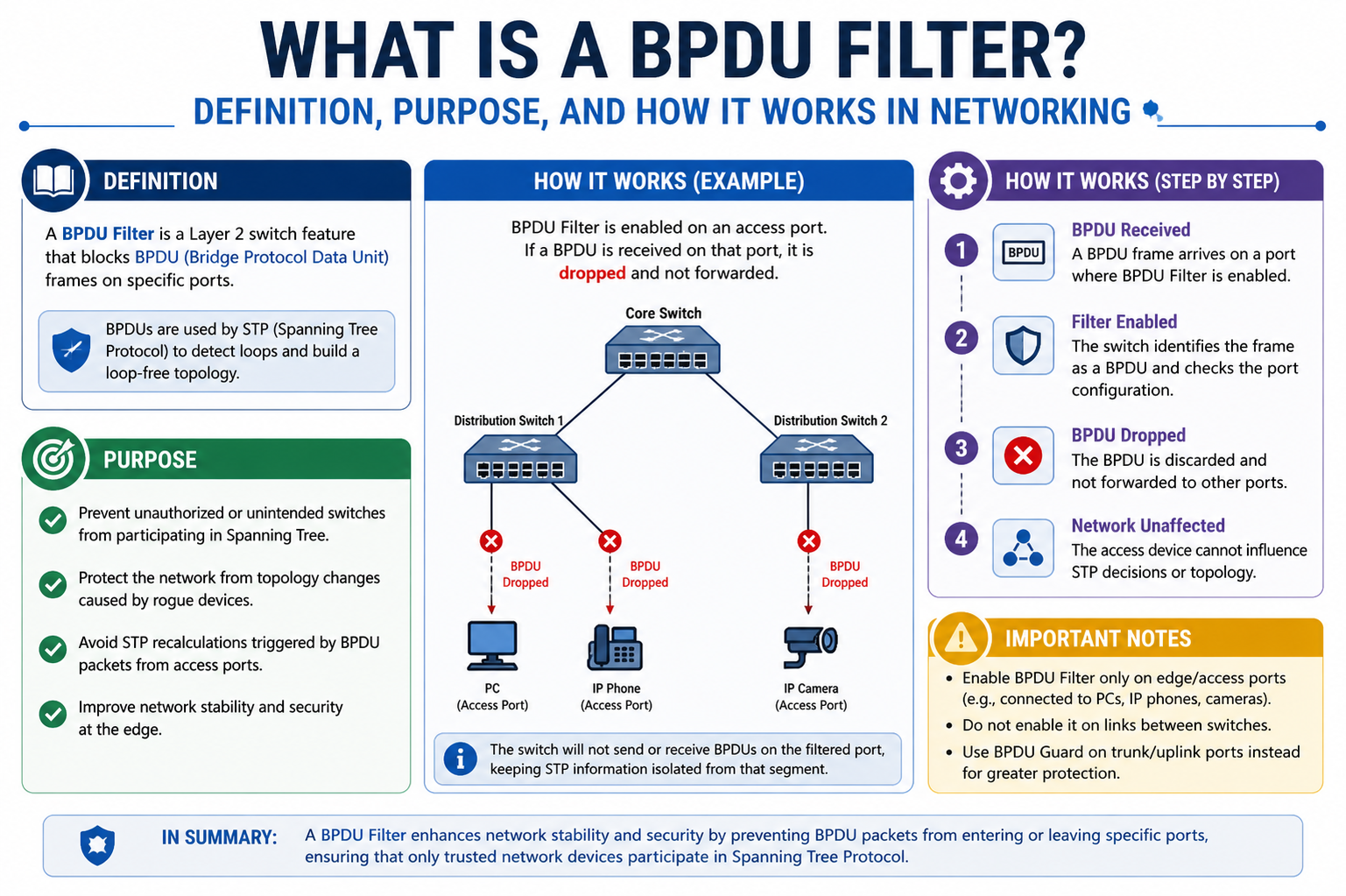
A BPDU Filter is a feature used in modern switching networks to control the behavior of Bridge Protocol Data Units (BPDUs) on specific switch ports. It plays an important role in environments that use the Spanning Tree Protocol (STP), which is responsible for preventing network loops. BPDU Filter allows network administrators to selectively disable the sending or receiving of BPDU messages on certain interfaces, giving more control over how STP operates within a network topology.
BPDUs are special data frames exchanged between switches to share information about network topology and ensure there are no loops. While this process is essential in switch-to-switch communication, it is often unnecessary and sometimes undesirable on ports connected to end devices like computers, printers, or servers. This is where BPDU Filter becomes useful, as it helps restrict unnecessary STP communication on these edge ports.
Understanding the Role of BPDU in STP
To fully understand BPDU Filter, it is important to first understand BPDUs and their role in Spanning Tree Protocol. STP is designed to prevent switching loops in a network by creating a loop-free logical topology. It does this by selecting a root bridge and determining the best path for data traffic.
BPDUs are the messages that switches use to exchange information such as bridge IDs, path costs, and port roles. Through continuous BPDU exchange, switches maintain an updated view of the network and adjust the topology when changes occur. Without BPDUs, STP would not be able to function effectively, and loops could form in redundant network paths.
However, not every port in a network needs to participate in this communication. Edge ports, which connect to end-user devices, typically do not require STP participation. This is why features like BPDU Filter are introduced to reduce unnecessary protocol overhead.
Purpose of BPDU Filter in Network Environments
The primary purpose of BPDU Filter is to provide greater control over how STP behaves on specific ports. In many enterprise networks, administrators want to ensure that only switch-to-switch links participate in STP while access ports remain simple and efficient.
By applying BPDU Filter, administrators can prevent BPDUs from being sent or received on selected interfaces. This reduces unnecessary processing on end devices and simplifies network behavior. It is especially useful in environments where PortFast or edge port configurations are used, as these ports are expected to connect only to end devices and not to other switches.
Another important purpose of BPDU Filter is to help avoid accidental STP participation on ports that should remain isolated from topology calculations. This helps maintain a cleaner and more predictable network design when implemented correctly.
How BPDU Filter Works in Switching Networks
When BPDU Filter is enabled on a switch port, it changes the way that port interacts with STP. Depending on the configuration mode, it can either block outgoing BPDUs, ignore incoming BPDUs, or both. This effectively removes the port from the STP process.
In one common mode, when the port comes up, it temporarily sends BPDUs but then stops after a certain condition is met. In another mode, the port completely suppresses BPDU transmission and reception from the start. The exact behavior depends on the switch operating system and configuration.
When a port is filtered, it no longer participates in STP calculations. This means it will not send or process topology change notifications, and it will not influence root bridge elections or path selection. From the perspective of STP, the port becomes invisible.
However, this behavior comes with a trade-off. Since STP is disabled on that interface, any accidental connection of another switch to that port can create a loop, as the filtering prevents STP from detecting it. This is why BPDU Filter must be used carefully and only in appropriate scenarios.
BPDU Filter vs BPDU Guard
BPDU Filter is often confused with BPDU Guard, but they serve different purposes. While both are used to protect STP behavior on edge ports, their actions are not the same.
BPDU Guard is a protective feature that disables a port if it receives a BPDU. This is used to prevent switches from being connected to access ports. If a BPDU is detected, the port is typically shut down to prevent potential loops.
BPDU Filter, on the other hand, prevents BPDUs from being sent or received in the first place. Instead of shutting down the port, it simply suppresses STP communication. This makes BPDU Filter more about control and suppression, while BPDU Guard is about protection and enforcement.
Understanding the difference is critical because misusing BPDU Filter in place of BPDU Guard can lead to serious network stability issues.
Where BPDU Filter Is Typically Used
BPDU Filter is generally used on edge ports in access-layer switches. These are ports that connect directly to end-user devices such as desktops, printers, IP phones, and servers. Since these devices do not participate in STP, there is no need for BPDU exchange on these ports.
In some cases, BPDU Filter is used in controlled environments where network administrators are confident that no switches will ever be connected to a particular port. It is also sometimes used in virtualization environments where virtual switch configurations require isolated behavior.
However, in modern best practices, BPDU Filter is used sparingly because of the risks involved. Many network engineers prefer BPDU Guard combined with PortFast instead, as it provides safer protection against misconfigurations.
Advantages of Using BPDU Filter
One of the main advantages of BPDU Filter is reduced unnecessary STP processing on edge ports. Since end devices do not need to participate in spanning tree calculations, disabling BPDU exchange can improve efficiency slightly.
It also helps simplify network behavior in large environments where thousands of access ports exist. By limiting STP interaction to only necessary links, the overall network becomes easier to manage and troubleshoot.
Another advantage is greater administrative control. Network engineers can fine-tune exactly where STP should and should not operate, which is useful in specialized network designs.
Risks and Disadvantages of BPDU Filter
Despite its advantages, BPDU Filter carries significant risks if not configured properly. The biggest risk is the potential for switching loops. Since STP is disabled on filtered ports, any accidental connection of a switch to that port can create a loop that the network cannot detect or prevent.
Another disadvantage is loss of STP protection. Normally, STP helps maintain a stable and loop-free network. By filtering BPDUs, this safety mechanism is partially or fully removed on that interface.
It can also make troubleshooting more complex. When BPDU Filter is enabled, certain STP-related diagnostics become unavailable on that port, making it harder to detect misconfigurations.
Because of these risks, BPDU Filter should only be used in environments where the physical topology is tightly controlled and well understood.
Best Practices for BPDU Filter Configuration
When implementing BPDU Filter, careful planning is essential. It should only be applied to ports that are guaranteed to connect to end devices. Using it on uplinks or inter-switch connections is highly dangerous and should be avoided.
Many network engineers prefer combining PortFast with BPDU Guard instead of BPDU Filter, as it provides safer behavior. PortFast allows quick port activation for end devices, while BPDU Guard ensures that any unexpected switch connection shuts down the port.
If BPDU Filter is used, it should be documented clearly and regularly reviewed. Network changes can introduce new risks, and previously safe configurations may become dangerous over time.
It is also important to test configurations in a controlled environment before deploying them in production networks. This helps ensure that BPDU Filter does not interfere with network stability.
Impact of BPDU Filter on Network Stability
BPDU Filter has a direct impact on network stability because it modifies how STP behaves on selected ports. In a well-designed network, STP ensures redundancy without loops. When BPDU Filter is applied correctly, it does not affect stability significantly.
However, if misused, it can introduce instability by disabling loop detection mechanisms. This can lead to broadcast storms, high CPU usage on switches, and network outages.
Therefore, BPDU Filter should always be used with a clear understanding of the network topology and potential risks. It is not a feature to be enabled globally but rather selectively applied where absolutely necessary.
BPDU Filter is a powerful but sensitive feature in network switching that allows administrators to control STP behavior on specific ports. It works by suppressing BPDU transmission and reception, effectively removing a port from spanning tree participation.
While it offers advantages such as reduced overhead and simplified edge port management, it also introduces risks related to loop prevention. For this reason, it must be used carefully and only in appropriate environments.
In modern networking, BPDU Filter is often replaced or supplemented by safer alternatives like BPDU Guard and PortFast. However, understanding how it works remains important for network professionals who manage STP-based infrastructures.
BPDU Filter Configuration Modes
BPDU Filter can operate in different configuration modes depending on the switch platform and how the administrator applies it. These modes determine whether BPDU processing is completely disabled or only partially restricted on a port. Understanding these modes is important because each one behaves differently under network changes.
In one mode, BPDU Filter is applied globally along with PortFast. In this case, the port starts in a forwarding state without participating in STP and does not send or receive BPDUs. However, if a BPDU is detected, the behavior may change depending on the switch implementation.
In another mode, BPDU Filter is applied per interface. This gives more precise control because the administrator can enable it only on selected ports. In this case, the port completely suppresses BPDU transmission and reception, making it fully isolated from STP behavior.
The difference between global and interface-level configuration is critical. Global settings are easier to apply but can introduce unexpected behavior if not carefully managed. Interface-level configuration is more controlled and safer in structured environments.
Interaction of BPDU Filter with PortFast
BPDU Filter is often used together with PortFast, a feature that allows switch ports to transition quickly into the forwarding state. PortFast is designed for access ports that connect to end devices, reducing the time it takes for a device to gain network connectivity.
When BPDU Filter and PortFast are used together, the port becomes highly optimized for end-user connections. It skips normal STP listening and learning states and avoids BPDU processing. This combination improves connection speed and reduces unnecessary protocol overhead.
However, this combination must be used carefully. While PortFast assumes the port connects to an end device, BPDU Filter removes STP protection entirely. If a switch is mistakenly connected to such a port, the network will not detect the loop condition.
Because of this risk, many network designs prefer replacing BPDU Filter with BPDU Guard when used with PortFast. BPDU Guard provides a safer approach by shutting down the port if a BPDU is detected.
Behavior of a Port with BPDU Filter Enabled
When a port has BPDU Filter enabled, its behavior changes significantly compared to a normal STP-enabled port. The port no longer participates in STP topology updates. It does not send BPDU messages to other switches, and it does not process incoming BPDU frames.
As a result, the port operates as if STP does not exist on that interface. It remains in a forwarding state for end devices without considering network topology changes. This can improve performance in edge environments but removes loop detection capability.
If the network topology changes elsewhere, the filtered port will not react to those changes. This is why BPDU Filter is considered a static configuration feature rather than a dynamic STP participant.
Security Implications of BPDU Filter
BPDU Filter also has important security implications in network design. By disabling STP communication, it prevents external switches from influencing the local spanning tree topology through that port. This can be useful in controlled environments where administrators want to isolate edge devices.
However, it can also create vulnerabilities if not properly managed. An attacker who gains physical access to a BPDU-filtered port could potentially connect a rogue switch. Since STP is disabled, the network would not detect loop formation, leading to instability or denial of service conditions.
This is why BPDU Filter is generally not recommended in environments where physical security is not guaranteed. Instead, BPDU Guard and other protective features are preferred because they actively respond to unauthorized switch connections.
BPDU Filter in Enterprise Network Design
In enterprise networks, BPDU Filter is rarely used as a default configuration. Modern network design follows a structured approach where STP is carefully controlled across all switching layers.
Access layer switches typically use PortFast and BPDU Guard rather than BPDU Filter. Distribution and core layers rely on standard STP operation to maintain redundancy and loop prevention.
However, BPDU Filter may still be used in specific enterprise scenarios where network engineers require complete isolation of STP on certain ports. For example, in lab environments, test networks, or specialized appliances that do not support STP.
Even in these cases, its usage is heavily documented and restricted to prevent accidental misconfiguration.
Difference Between BPDU Filter and STP Disablement
It is important to understand that BPDU Filter is not the same as disabling STP globally or on a switch. When STP is disabled entirely, the entire switching domain loses loop protection. BPDU Filter, however, only affects selected ports.
This selective control allows administrators to maintain STP functionality across the network while isolating specific interfaces. However, from a behavior perspective, a filtered port behaves similarly to a port with STP disabled, which is why caution is necessary.
The key difference is scope: BPDU Filter is per-port, while STP disablement is global or VLAN-based.
Troubleshooting BPDU Filter Issues
When issues arise in networks using BPDU Filter, troubleshooting can be more complex than in standard STP environments. Since BPDUs are not exchanged on filtered ports, traditional STP diagnostics do not provide useful information for those interfaces.
Common issues include unexpected network loops, broadcast storms, or connectivity instability. These problems often occur when a switch is mistakenly connected to a BPDU-filtered port.
To troubleshoot such issues, network engineers typically check physical connections first, then review configuration settings on affected ports. Identifying where BPDU Filter is applied is critical in resolving loop-related problems.
In many cases, removing BPDU Filter and replacing it with BPDU Guard resolves stability issues and improves visibility into network behavior.
Real-World Scenarios Where BPDU Filter Can Be Problematic
In real-world networks, BPDU Filter can cause serious issues if applied incorrectly. One common scenario is when a user accidentally connects a small unmanaged switch to an access port that has BPDU Filter enabled.
Since STP is disabled on that port, the switch creates a loop with no protection. This can quickly escalate into a broadcast storm affecting multiple network segments.
Another scenario involves network expansion. If a port initially intended for a PC is later used for a switch connection, the existing BPDU Filter configuration can create hidden risks.
These situations highlight why careful documentation and change management are essential when using BPDU Filter.
Alternative Approaches to BPDU Filter
Modern network design often avoids BPDU Filter in favor of safer alternatives. The most common alternative is BPDU Guard, which actively protects against unauthorized switch connections by shutting down the port when a BPDU is detected.
Another alternative is Root Guard, which prevents external switches from becoming root bridges. Loop Guard is also used to prevent unidirectional link failures from causing loops.
Together, these features provide a more dynamic and secure approach to STP management compared to BPDU Filter.
In many enterprise environments, the combination of PortFast and BPDU Guard is considered the best practice for access ports.
Performance Considerations of BPDU Filter
From a performance perspective, BPDU Filter has minimal impact on modern network hardware. It reduces BPDU processing on selected ports, which slightly decreases CPU utilization on switches.
However, in most networks, this performance gain is negligible because modern switches are designed to handle STP efficiently. The real benefit is not performance but control over STP behavior.
Therefore, performance should not be the primary reason for using BPDU Filter. Stability and safety considerations are far more important.
BPDU Filter Role in Networking
BPDU Filter is a specialized feature that provides control over STP behavior by suppressing BPDU transmission and reception on selected ports. It is primarily used on edge interfaces where end devices connect and STP participation is not required.
While it offers configuration flexibility and slight performance optimization, it also removes critical loop prevention mechanisms from those ports. Because of this, it must be used with extreme caution.
In modern networking, BPDU Filter is gradually being replaced by safer and more intelligent STP protection mechanisms. However, understanding its behavior remains essential for network engineers managing complex switching environments.
Advanced Use Cases of BPDU Filter
In advanced network environments, BPDU Filter is sometimes used in highly controlled and specialized scenarios where precise control over Spanning Tree Protocol behavior is required. These use cases are not common in standard enterprise networks but appear in labs, testing environments, and isolated infrastructure segments.
One such use case is in network simulation or staging environments where engineers test device behavior without STP interference. By filtering BPDUs, they can observe how devices operate in a flat Layer 2 environment without spanning tree influence.
Another scenario involves certain legacy systems or appliances that are not designed to participate in STP. In such cases, BPDU Filter helps ensure these devices operate without unnecessary protocol interaction that could interfere with their normal function.
In virtualization-heavy environments, BPDU Filter may also be used to isolate virtual switching domains where STP is managed internally rather than on physical switches.
BPDU Filter in Data Center Networks
In modern data centers, network design is highly structured and typically relies on advanced architectures such as leaf-spine topologies. In these environments, STP is often minimized or eliminated in favor of Layer 3 routing and other loop-prevention mechanisms.
However, BPDU Filter may still appear in certain edge cases within data centers, especially where legacy systems or hybrid environments exist. It can be applied to specific access ports that connect to servers or storage devices where STP participation is unnecessary.
Despite this, most modern data center designs avoid BPDU Filter because deterministic network behavior is preferred. Instead, they rely on controlled STP domains or entirely STP-free Layer 3 designs.
Impact of BPDU Filter on Network Convergence
Network convergence refers to the time it takes for a network to reach a stable state after a topology change. STP plays a key role in this process by recalculating paths when links go up or down.
When BPDU Filter is enabled, the affected port no longer participates in convergence processes. This means it does not react to topology changes in the rest of the network. While this can make the port behave more predictably for end devices, it also isolates it from important network updates.
As a result, BPDU Filter can create situations where part of the network is unaware of changes happening elsewhere. This lack of synchronization can lead to inconsistencies if not carefully managed.
Misconfiguration Risks of BPDU Filter
One of the biggest challenges with BPDU Filter is the risk of misconfiguration. Since it disables a critical safety mechanism, even a small configuration mistake can have serious consequences.
A common misconfiguration occurs when BPDU Filter is applied to a port that later connects to another switch. In this case, STP is not active, and the network cannot detect or block loops. This can result in rapid network degradation.
Another misconfiguration issue arises when administrators assume BPDU Filter behaves like BPDU Guard. In reality, they are fundamentally different, and confusing them can lead to unsafe network designs.
Because of these risks, BPDU Filter should always be applied with strict documentation and clear operational guidelines.
Operational Visibility Challenges with BPDU Filter
When BPDU Filter is active, network visibility into STP behavior on that port is significantly reduced. Since BPDUs are not transmitted or received, network monitoring tools cannot fully analyze STP activity for that interface.
This lack of visibility can make troubleshooting more difficult. Engineers may not immediately realize that BPDU Filter is responsible for missing STP information, especially in large networks with many access ports.
Additionally, network management systems that rely on BPDU data to map topology may produce incomplete or inaccurate diagrams when BPDU Filter is widely used.
BPDU Filter and Network Scalability
In large-scale networks, scalability is a major design consideration. STP itself is not always ideal for very large Layer 2 environments due to convergence delays and complexity.
BPDU Filter can contribute to scalability in a limited way by reducing STP participation on edge ports. However, this benefit is relatively minor compared to modern scalable network architectures that reduce reliance on STP altogether.
In well-designed scalable networks, BPDU Filter is not a primary tool for performance or scalability improvement. Instead, routing-based designs and hierarchical segmentation are preferred.
Behavior During Network Failures
During network failures, BPDU Filtered ports behave differently from normal STP-enabled ports. Since they do not participate in STP, they do not contribute to failover decisions or topology recalculations.
If a failure occurs elsewhere in the network, BPDU Filtered ports remain unchanged and continue forwarding traffic as long as the physical link is up. This can sometimes create a false sense of stability.
However, if a loop exists due to misconfiguration, BPDU Filter prevents STP from correcting the issue, which can worsen failure impact.
BPDU Filter in Virtual Switching Environments
In virtualized environments, such as those using hypervisors and virtual switches, BPDU Filter may be used to control STP behavior between virtual and physical switching layers.
Some virtual switch implementations do not fully support STP, so BPDU Filter helps prevent unexpected interactions between virtual networks and physical infrastructure.
However, modern virtual switching platforms often include their own loop prevention mechanisms, reducing the need for BPDU Filter at all.
Comparison of BPDU Filter and Modern STP Enhancements
Modern networking has introduced several enhancements to Spanning Tree Protocol, such as Rapid STP and Multiple STP variants, which improve convergence speed and stability.
Compared to these enhancements, BPDU Filter is considered a more static and less intelligent control mechanism. While STP enhancements adapt dynamically to network changes, BPDU Filter simply disables participation entirely.
This fundamental difference is why BPDU Filter is increasingly considered a legacy-style configuration in modern networks.
Best Practices for Long-Term Network Stability
For long-term network stability, BPDU Filter should be used sparingly and only in clearly defined scenarios. Network engineers should prioritize dynamic protection mechanisms that respond automatically to changes.
It is recommended to use BPDU Guard on edge ports instead of BPDU Filter, as it provides both protection and visibility. PortFast should be enabled where appropriate to improve device connectivity speed.
Regular audits of switch configurations are also important to ensure BPDU Filter is not applied unintentionally or left on ports where it is no longer needed.
BPDU Filter Concepts
BPDU Filter is a specialized network feature that offers control over STP behavior by suppressing BPDU exchange on selected ports. While it can be useful in controlled environments and specific use cases, it also removes critical loop prevention capabilities.
In modern network design, its usage is limited due to the availability of safer and more dynamic alternatives. Understanding its behavior, risks, and operational impact is essential for network engineers working with Layer 2 switching environments.
When used correctly and in the right context, BPDU Filter can provide targeted control over STP. However, when misused, it can introduce serious network instability, making careful planning and documentation essential.
BPDU Filter in Troubleshooting Network Loops
When a network experiences a loop, BPDU Filter can often be one of the hidden causes that makes the problem worse or harder to detect. Since BPDU Filter disables the exchange of Bridge Protocol Data Units, the normal loop-prevention mechanism of Spanning Tree Protocol cannot function on affected ports.
In troubleshooting scenarios, engineers typically look for symptoms such as broadcast storms, high CPU usage on switches, or sudden network slowdowns. If BPDU Filter is enabled on any access port, it may prevent STP from identifying the root cause of the loop, allowing the issue to persist longer than expected.
A key step in troubleshooting is to identify whether any edge ports have BPDU Filter applied. Once discovered, removing or modifying the configuration often restores STP visibility and helps the network stabilize again.
Behavior of BPDU Filter in Redundant Network Paths
In networks with redundant links, STP normally ensures that only one active path is used while others remain blocked. This prevents loops while still maintaining backup paths for failover.
When BPDU Filter is enabled on certain ports, those ports no longer participate in the decision-making process of STP. As a result, redundancy calculations may become incomplete or inaccurate.
If a redundant path includes a BPDU-filtered port, the network may treat it as a normal forwarding interface rather than part of a controlled spanning tree topology. This can unintentionally create multiple active forwarding paths, increasing the risk of loops.
Because of this, BPDU Filter should never be used on links that are part of redundancy or inter-switch connectivity.
BPDU Filter and Network Design Philosophy
Modern network design follows a philosophy of controlled automation and dynamic response. Features like STP, Rapid STP, and Layer 3 routing are designed to automatically adapt to changes in topology.
BPDU Filter, in contrast, is a static configuration tool. It removes dynamic behavior from selected ports and forces them into a fixed operational state. This makes it fundamentally different from modern adaptive network design principles.
As a result, BPDU Filter is generally considered a legacy or niche feature rather than a core design component. It is only used when strict control over a port’s behavior is more important than dynamic adaptability.
Effects of BPDU Filter on VLAN Environments
In VLAN-based networks, STP operates within or across VLANs depending on the configuration mode, such as PVST or Rapid PVST. BPDUs are essential in maintaining loop-free behavior across these VLANs.
When BPDU Filter is applied to a port carrying multiple VLANs, it affects all VLAN traffic passing through that interface. Since STP is disabled on that port, none of the VLANs benefit from loop prevention mechanisms on that specific link.
This can create inconsistent behavior in multi-VLAN environments if the filtered port is part of a larger switching structure. VLANs may appear stable until traffic patterns change or additional switches are connected.
BPDU Filter in Campus Network Environments
In campus networks, which typically include access, distribution, and core layers, BPDU Filter is most commonly found at the access layer. These are the edge switches that connect end-user devices such as PCs, printers, and VoIP phones.
Even in this environment, its usage is decreasing. Most modern campus designs prefer using PortFast and BPDU Guard instead of BPDU Filter. This combination provides fast connectivity while maintaining strong protection against loops.
However, in older or manually managed campus networks, BPDU Filter may still exist on legacy configurations, especially where network policies were designed before modern STP best practices were widely adopted.
Administrative Challenges of BPDU Filter
From an administrative perspective, BPDU Filter introduces additional complexity in network management. Since it suppresses STP communication, it reduces the amount of information available for monitoring tools and network diagnostics.
Administrators must maintain accurate records of where BPDU Filter is applied, because forgetting its presence can lead to confusion during troubleshooting or network upgrades.
Additionally, when network teams change or grow, undocumented BPDU Filter configurations can become hidden risks that are difficult to detect until a problem occurs.
Impact on Network Resiliency
Network resiliency depends on the ability of the network to recover from failures quickly and safely. STP contributes to resiliency by recalculating paths when links fail or recover.
BPDU Filter reduces resiliency on affected ports because it removes them from STP participation. These ports do not adjust dynamically when the network topology changes.
As a result, while BPDU Filter may simplify behavior for end devices, it also reduces the overall adaptability of the network. This trade-off must be carefully considered in any design decision.
Security and Isolation Considerations
One of the reasons BPDU Filter is sometimes used is to isolate edge ports from STP influence. This can be useful in environments where administrators want to ensure that external devices cannot affect spanning tree calculations.
However, this isolation is incomplete because it only affects BPDU exchange, not other types of network traffic. Therefore, it should not be considered a full security control mechanism.
Stronger security approaches, such as port security, BPDU Guard, and network segmentation, are generally preferred over BPDU Filter for protecting network integrity.
Modern Replacement Trends for BPDU Filter
In modern networking, there is a clear trend away from BPDU Filter and toward more intelligent and self-protecting features. Network engineers prefer solutions that automatically detect and respond to misconfigurations.
Features like BPDU Guard, Loop Guard, and Root Guard provide more dynamic protection while maintaining visibility into STP behavior. These tools allow networks to remain both flexible and safe.
Because of this evolution, BPDU Filter is increasingly seen as a specialized tool rather than a standard configuration option.
Understanding of BPDU Filter Role
BPDU Filter is a powerful but sensitive feature that directly affects how Spanning Tree Protocol operates on selected switch ports. By suppressing BPDU transmission and reception, it removes those ports from STP participation entirely.
While this can be useful in very controlled environments, it also introduces risks related to loop detection, network visibility, and resiliency. For this reason, it is no longer considered a default best practice in modern network design.
Understanding BPDU Filter is still important for network engineers, especially when working with legacy systems or troubleshooting complex Layer 2 environments. However, its use should always be carefully evaluated against safer and more adaptive alternatives.
Conclusion
BPDU Filter is a specialized feature in switching networks that controls how Bridge Protocol Data Units are handled on selected ports. By suppressing BPDU transmission and reception, it effectively removes those interfaces from Spanning Tree Protocol participation. This gives network administrators tighter control over edge ports where STP is not typically required, especially those connected to end devices like computers, printers, and other non-switching equipment.
While BPDU Filter can simplify behavior in certain controlled environments, it also eliminates an important safety mechanism that helps prevent network loops. Because of this, improper or excessive use can lead to serious network instability, including broadcast storms and connectivity outages. It is not designed for inter-switch links or redundant paths, and it should never be applied without a clear understanding of the network topology.
In modern networking practices, BPDU Filter is used less frequently as more reliable and adaptive features like BPDU Guard, PortFast, and advanced STP variants provide better protection and visibility. These alternatives maintain loop prevention while still supporting fast and efficient network access for end devices.
Overall, BPDU Filter remains a useful but limited tool. When applied correctly and in the right context, it can help refine STP behavior on access ports. However, its risks mean it must be used carefully, with proper documentation and strict adherence to network design principles.