SNMPv3 is the most advanced version of the Simple Network Management Protocol, designed specifically to overcome the security limitations of earlier versions. It is used for monitoring and managing devices in a network environment such as routers, switches, firewalls, servers, and printers. The main goal of SNMPv3 is to provide a secure and reliable communication mechanism between network management systems and managed devices. It achieves this by introducing strong authentication, encryption, and access control mechanisms that were not present in previous versions.
SNMPv3 is widely adopted in enterprise and service provider networks because modern infrastructures require strict security policies. Unlike earlier versions that transmitted data in plain text, SNMPv3 ensures that sensitive management information cannot be easily intercepted or modified by unauthorized users. This makes it suitable for environments where data integrity and confidentiality are critical.
SNMPv3 Architecture and Design Principles
The architecture of SNMPv3 is built around a modular and flexible design that separates different functions into distinct components. This separation allows better scalability and security management. The main components include the message processing subsystem, security subsystem, and access control subsystem.
The message processing subsystem is responsible for preparing and interpreting SNMP messages. It ensures that messages are properly formatted and routed between the management station and network devices. The security subsystem handles authentication and encryption, ensuring that only authorized users can access the system and that data remains protected during transmission. The access control subsystem determines what level of access each user has, controlling which data can be viewed or modified.
This layered architecture ensures that SNMPv3 is not only secure but also highly adaptable to different network environments.
Security Model in SNMPv3
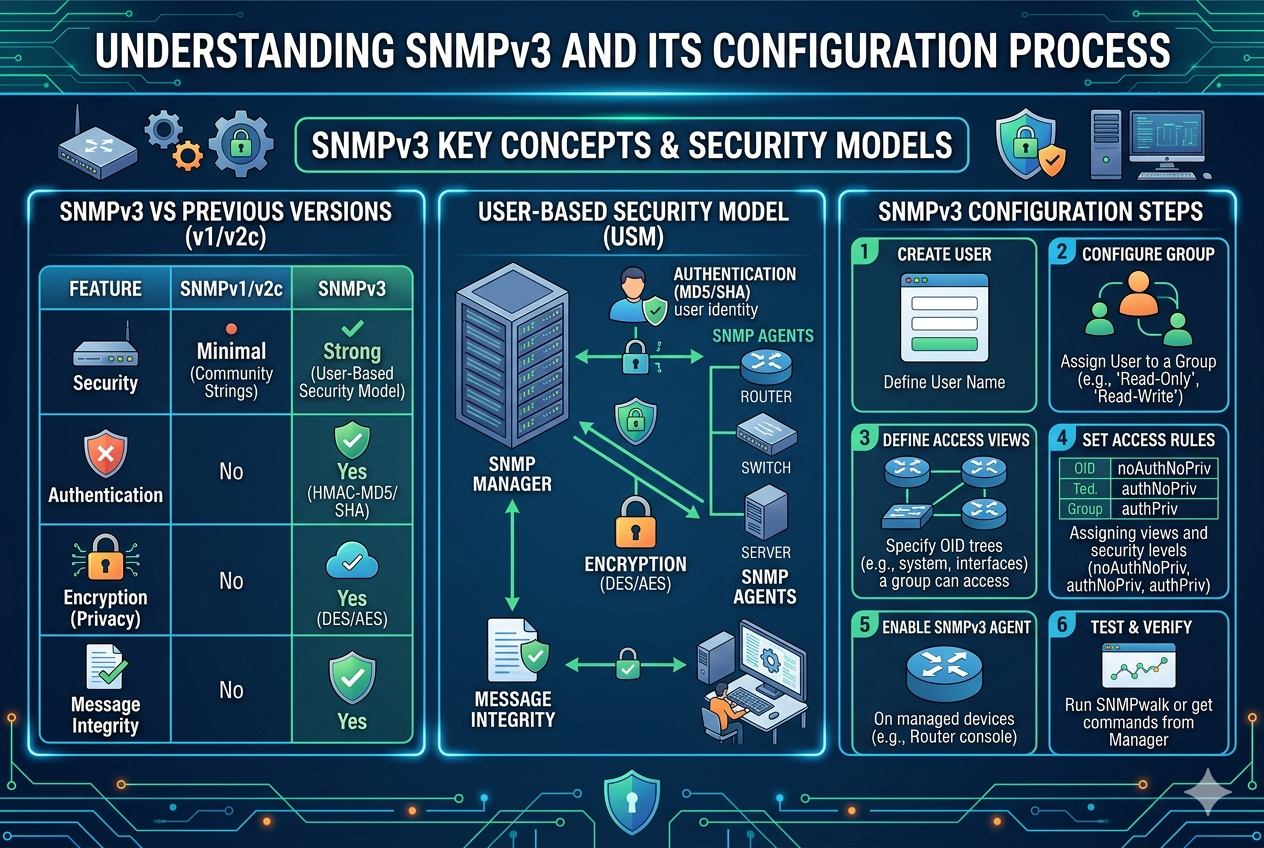
The security model of SNMPv3 is one of its most important features. It introduces a User-Based Security Model that provides authentication and privacy services at the user level. This model ensures that each user is uniquely identified and granted specific permissions.
Authentication ensures that the message received by a device actually comes from a legitimate source. It prevents unauthorized access by verifying the identity of the sender. SNMPv3 supports authentication protocols such as MD5 and SHA, which generate message digests to verify integrity.
Privacy ensures that the data transmitted between devices is encrypted. This prevents attackers from reading sensitive information even if they intercept the communication. Encryption protocols such as DES and AES are used to secure SNMP messages.
Together, authentication and privacy provide a strong security foundation for network management operations.
User-Based Security Model (USM)
The User-Based Security Model is the core of SNMPv3 security. It defines how users are created, authenticated, and protected. Each user is assigned a security name, authentication protocol, authentication key, privacy protocol, and privacy key.
When a user sends a request, the system checks the authentication credentials to verify identity. If authentication is enabled, the message is validated using the selected hashing algorithm. If privacy is enabled, the message is decrypted using the appropriate encryption method before processing.
USM ensures that each user has a unique security profile, making it difficult for unauthorized users to gain access. It also supports different levels of security depending on organizational requirements.
View-Based Access Control Model (VACM)
The View-Based Access Control Model is responsible for defining what resources a user can access. It works by creating views, which are subsets of the management information base. These views determine which objects a user is allowed to read or modify.
VACM associates users with groups, and each group is assigned specific access rights. This allows administrators to control access at a granular level. For example, a network administrator may have full access to all device settings, while a monitoring user may only have read-only access to performance statistics.
This model enhances security by ensuring that users can only interact with data relevant to their role.
SNMPv3 Engine and Communication Process
The SNMPv3 engine is responsible for processing and managing SNMP messages within a device. Each device that supports SNMPv3 has its own engine ID, which uniquely identifies it in the network.
When a message is sent from a manager to an agent, the engine processes the message by applying security parameters such as authentication and encryption. It then forwards the request to the appropriate subsystem for execution. Once the response is generated, the engine applies the necessary security measures before sending it back to the manager.
This engine-based communication ensures that all SNMP operations are secure and properly managed.
Configuration Process of SNMPv3 in Detail
The configuration of SNMPv3 involves several important steps that must be carefully executed to ensure proper security and functionality. The first step is defining the SNMP engine ID, which uniquely identifies the device in the network. This ID is essential for secure communication.
Next, users are created and assigned security levels. Each user is configured with authentication credentials such as username and password. Depending on security requirements, authentication protocols like SHA or MD5 are selected. After authentication is set, privacy settings can be configured using encryption algorithms such as AES or DES.
Once users are created, access control settings are applied. This involves defining views that determine what parts of the device configuration or monitoring data each user can access. Groups are then created, and users are assigned to these groups based on their roles.
Finally, SNMP services are enabled on the device, and the configuration is saved. Testing is performed to ensure that communication between the SNMP manager and the device is functioning correctly.
Authentication and Encryption Mechanisms
Authentication in SNMPv3 ensures that messages come from legitimate sources. It uses cryptographic hashing algorithms that generate unique message digests. If the received message does not match the expected digest, it is rejected.
Encryption provides confidentiality by converting data into unreadable formats during transmission. Only authorized users with the correct encryption keys can decrypt and read the data. AES is commonly used because it provides strong security and efficiency.
Together, these mechanisms protect the network from unauthorized access and data breaches.
Operational Workflow of SNMPv3
The operational workflow of SNMPv3 begins when a management station sends a request to a network device. The message is first processed by the SNMP engine, which applies authentication checks. If authentication is successful, the message is decrypted if privacy is enabled.
The request is then forwarded to the appropriate subsystem, which retrieves the required information from the device. Once the data is collected, the response is encrypted and authenticated before being sent back to the manager.
This process ensures that every interaction between devices is secure and reliable.
Advantages of SNMPv3
SNMPv3 offers several advantages over earlier versions. The most significant advantage is its strong security model, which includes authentication and encryption. It also provides granular access control, allowing administrators to define precise permissions for users.
Another advantage is its flexibility and scalability, making it suitable for both small and large networks. It also supports better error handling and message integrity checks, ensuring reliable communication.
Challenges in SNMPv3 Implementation
Despite its advantages, SNMPv3 can be more complex to configure compared to earlier versions. Proper setup requires understanding of security models, encryption methods, and access control mechanisms. Incorrect configuration can lead to communication failures or security vulnerabilities.
Another challenge is performance overhead due to encryption and authentication processes. However, this trade-off is generally acceptable given the security benefits.
Best Practices for SNMPv3 Configuration
To ensure optimal performance and security, it is important to follow best practices during SNMPv3 configuration. Strong authentication and encryption protocols should always be used. Default credentials should be avoided, and unique user accounts should be created for each administrator.
Access control should be carefully designed to follow the principle of least privilege. Regular monitoring and auditing should also be performed to detect any unauthorized access attempts.
SNMPv3 Message Structure and Communication Format
SNMPv3 uses a structured message format that ensures secure and organized communication between network management systems and managed devices. Each message consists of multiple fields that define how the data should be processed, authenticated, and encrypted. The structure is designed to support both security and flexibility, making it suitable for complex network environments.
At the core of SNMPv3 messaging is the separation between the header, security parameters, and data payload. The header contains information such as message version and message processing details. The security parameters section includes authentication and encryption data, which are used to verify the integrity and confidentiality of the message. The data payload contains the actual request or response, such as retrieving system information or modifying device settings.
This structured approach ensures that every message is properly validated before being processed, reducing the risk of unauthorized access or corrupted data.
Engine ID and Time Synchronization in SNMPv3
Each SNMPv3-enabled device is assigned a unique Engine ID, which plays a critical role in secure communication. The Engine ID identifies the source or destination of SNMP messages and ensures that security credentials are correctly associated with the right device.
Time synchronization is another important aspect of SNMPv3 security. The protocol uses time-based mechanisms to prevent replay attacks, where an attacker might attempt to resend previously captured messages. Each message includes time stamps and counters that are validated by the receiving device. If the message is outdated or does not match expected values, it is rejected.
This combination of Engine ID and time synchronization strengthens the overall security framework by ensuring message freshness and authenticity.
Management Information Base (MIB) in SNMPv3
The Management Information Base, commonly known as MIB, is a hierarchical database that stores information about network devices. It defines the structure of managed objects and provides a standardized way to access device data.
In SNMPv3, the MIB plays a central role in organizing network information. Each object in the MIB is identified by an Object Identifier (OID), which represents a specific parameter such as CPU usage, memory utilization, or interface status. The hierarchical structure of OIDs allows efficient navigation and retrieval of network data.
MIBs are essential for monitoring and controlling network devices because they define what information can be accessed and how it is structured. Without MIBs, network management would lack standardization and consistency.
Object Identifiers and Their Role
Object Identifiers are numerical representations that uniquely identify managed objects in the network. They are arranged in a tree-like structure, where each branch represents a different category of network information.
For example, system information, interface statistics, and performance metrics all have their own OID branches. This structured hierarchy allows network administrators to precisely locate and retrieve specific data points.
In SNMPv3, OIDs are used within secure messages, ensuring that even sensitive data requests are properly authenticated and encrypted before being processed.
SNMPv3 Trap and Inform Mechanisms
SNMPv3 supports two important notification mechanisms: traps and informs. These mechanisms allow devices to send alerts to the management system when specific events occur.
Traps are unsolicited messages sent by network devices to notify the manager about events such as device failures, interface down conditions, or security alerts. They are lightweight and do not require acknowledgment from the receiver.
Informs are similar to traps but include acknowledgment from the management system. This ensures that critical notifications are reliably delivered and confirmed. If acknowledgment is not received, the message can be retransmitted.
Both traps and informs play a vital role in proactive network monitoring and fault detection.
Comparison Between SNMPv1, SNMPv2c, and SNMPv3
SNMP has evolved through multiple versions, each improving upon the limitations of the previous one. SNMPv1 was the original version and provided basic network monitoring capabilities but lacked security features. SNMPv2c introduced improvements in performance and data handling but still used community-based security, which was not secure.
SNMPv3, on the other hand, introduced a complete security framework with authentication, encryption, and access control. Unlike its predecessors, it does not rely on simple community strings, making it significantly more secure for modern networks.
This evolution highlights the importance of SNMPv3 in environments where data protection and secure communication are essential.
Security Levels and Their Practical Usage
SNMPv3 defines three primary security levels that determine how messages are processed. The no authentication and no privacy level provides basic communication without security features, typically used in isolated or test environments.
The authentication without privacy level ensures that messages are verified but not encrypted. This provides integrity protection but does not hide data content.
The authentication with privacy level offers the highest security by combining authentication and encryption. This level is widely used in enterprise environments where sensitive data must be fully protected.
Choosing the correct security level depends on the organization’s security requirements and network design.
Access Control and Role-Based Management
SNMPv3 uses a role-based approach to access control, allowing administrators to define permissions based on user roles. This ensures that each user only has access to the information necessary for their responsibilities.
Roles are typically grouped into categories such as network administrators, monitoring staff, and read-only users. Each role is associated with specific views and permissions that define what data can be accessed or modified.
This approach reduces security risks by limiting unnecessary access to critical network information.
SNMPv3 in Large-Scale Networks
In large-scale enterprise networks, SNMPv3 plays a crucial role in centralized monitoring and management. It allows administrators to monitor thousands of devices from a single management system while maintaining strong security controls.
Scalability is achieved through hierarchical network design and efficient polling mechanisms. SNMPv3 ensures that even in large deployments, communication remains secure and manageable.
However, proper planning is required to avoid performance bottlenecks caused by excessive polling or misconfigured security settings.
Performance Considerations in SNMPv3
While SNMPv3 provides strong security, it introduces additional processing overhead due to encryption and authentication. This can slightly impact performance, especially in devices with limited processing power.
To optimize performance, administrators often balance security requirements with system capabilities. For example, less critical devices may use lower security levels, while critical infrastructure uses full encryption.
Efficient configuration and proper polling intervals also help reduce unnecessary load on the network.
Troubleshooting SNMPv3 Issues
Troubleshooting SNMPv3 can be complex due to its multiple security layers. Common issues include authentication failures, incorrect encryption settings, and mismatched Engine IDs.
Authentication failures usually occur when user credentials or security protocols are incorrectly configured. Encryption issues may arise if different encryption algorithms are used on the manager and agent sides.
Engine ID mismatches can prevent communication entirely, as devices may not recognize each other. Proper logging and diagnostic tools are essential for identifying and resolving these issues.
Logging and Monitoring in SNMPv3
SNMPv3 supports detailed logging and monitoring capabilities that help administrators track network activity. Logs can include authentication attempts, configuration changes, and system alerts.
Monitoring tools use SNMPv3 to collect real-time data about network performance and device health. This information is used to detect anomalies, optimize performance, and ensure system reliability.
Effective logging is essential for maintaining security and identifying potential threats in the network.
Use Cases of SNMPv3 in Real Environments
SNMPv3 is widely used in data centers, enterprise networks, and cloud environments. It is used for monitoring server performance, managing network devices, and ensuring system availability.
In security-sensitive environments such as financial institutions and government networks, SNMPv3 is preferred due to its strong encryption and authentication features. It helps ensure that sensitive operational data remains protected.
It is also used in telecommunications networks to manage large-scale infrastructure and ensure service reliability.
Limitations of SNMPv3
Despite its advantages, SNMPv3 has certain limitations. Its configuration complexity can be challenging for beginners. It also requires careful management of security credentials and encryption keys.
Additionally, its performance overhead may not be suitable for extremely resource-constrained devices. However, these limitations are generally outweighed by its security benefits.
Future of SNMPv3 and Network Management
The future of SNMPv3 lies in its continued integration with modern network management systems. As networks become more complex and distributed, secure monitoring protocols will remain essential.
While newer technologies such as API-based monitoring and automation frameworks are emerging, SNMPv3 continues to play a foundational role in network management. Its stability, reliability, and security ensure that it remains relevant in evolving IT environments.
Extended Concepts
SNMPv3 is a comprehensive and secure network management protocol that addresses the limitations of earlier versions. Its architecture, security model, and operational mechanisms make it suitable for modern enterprise networks. By combining authentication, encryption, and access control, it ensures that network communication remains both secure and efficient.
Through its structured design and wide applicability, SNMPv3 continues to be a critical component in managing and monitoring complex network infrastructures.
Advanced SNMPv3 Security Mechanisms
SNMPv3 introduces advanced security mechanisms that go beyond basic authentication and encryption. One of the most important aspects is message integrity checking, which ensures that data has not been altered during transmission. This is achieved through cryptographic hash functions that generate a fixed output based on the message content. If even a single character is changed, the hash value will differ, and the message will be rejected.
Another important mechanism is timeliness verification. SNMPv3 uses time windows and message counters to ensure that old or replayed messages cannot be reused by attackers. This protects the network from replay attacks, which are common in unsecured communication protocols. By validating both time and sequence information, SNMPv3 ensures that every message is fresh and legitimate.
These mechanisms work together to provide a multi-layered security approach that significantly strengthens network protection.
Cryptographic Algorithms Used in SNMPv3
SNMPv3 relies on well-established cryptographic algorithms to secure communication. For authentication, algorithms such as SHA are commonly used because they provide strong resistance against collision attacks. SHA-based authentication ensures that messages cannot be forged without knowledge of the correct secret key.
For encryption, algorithms like AES are widely used due to their balance of security and performance. AES encrypts SNMP messages in such a way that only authorized devices with the correct key can decrypt and read the information. Older algorithms like DES may still be supported in some environments, but they are considered less secure and are gradually being replaced.
The use of standardized cryptographic algorithms ensures that SNMPv3 remains compatible with modern security requirements and industry best practices.
Key Management in SNMPv3
Key management is a critical part of SNMPv3 security. Each user has associated authentication and privacy keys, which are used to secure communication. These keys must be carefully generated, stored, and maintained to prevent unauthorized access.
In many implementations, keys are derived from passwords using key localization techniques. This ensures that even if the same password is used across multiple devices, the actual cryptographic keys remain unique for each device. This approach reduces the risk of widespread compromise if a single device is exposed.
Proper key management also involves periodic updates and rotation of credentials to maintain long-term security.
SNMPv3 Configuration Workflow in Enterprise Environments
In enterprise environments, SNMPv3 configuration follows a structured workflow to ensure consistency and security across all devices. The process typically begins with defining global SNMP settings on network devices, including engine IDs and security policies.
Next, administrators create users with defined authentication and privacy settings. These users are then assigned to security groups based on their roles within the organization. Each group is mapped to specific views that determine accessible data.
After user and group configuration, access control rules are applied using VACM policies. These rules define which users can access specific parts of the MIB structure.
Finally, SNMP services are enabled, and centralized management systems are configured to communicate with all devices using secure credentials. Testing and validation are performed to ensure that all components function correctly.
Role of SNMPv3 in Network Monitoring Systems
SNMPv3 plays a central role in modern network monitoring systems. It enables continuous observation of device performance, availability, and health status. Monitoring tools use SNMPv3 to collect data such as bandwidth usage, CPU load, memory consumption, and interface errors.
This information is used to generate alerts when abnormal conditions are detected. For example, if a router interface goes down or a server experiences high CPU usage, SNMPv3-based systems can immediately notify administrators.
Because of its secure communication model, SNMPv3 is especially important in environments where monitoring data itself is sensitive and must be protected from unauthorized access.
Scalability Challenges and Optimization Techniques
As networks grow in size, SNMPv3 deployments must be carefully optimized to maintain performance. One common challenge is excessive polling, where management systems frequently request data from a large number of devices. This can lead to increased network traffic and processing overhead.
To address this, administrators often implement optimized polling intervals and distribute monitoring loads across multiple management servers. Hierarchical monitoring architectures are also used, where regional systems collect data locally and forward summarized information to central systems.
Another optimization technique involves using event-driven monitoring through traps and informs instead of constant polling. This reduces unnecessary communication and improves scalability.
SNMPv3 in Hybrid and Cloud Environments
Modern IT infrastructures often include hybrid and cloud-based environments, where traditional network devices coexist with virtualized resources. SNMPv3 is still widely used in these environments for infrastructure monitoring.
In cloud environments, SNMPv3 is often used to monitor virtual machines, virtual networks, and storage systems. It provides a consistent method for tracking performance across both physical and virtual components.
However, integration with cloud-native monitoring tools is sometimes required to achieve full visibility. SNMPv3 remains valuable as a foundational protocol that complements newer monitoring technologies.
Security Risks and Mitigation Strategies
Although SNMPv3 is significantly more secure than earlier versions, it is not completely immune to risks. Misconfiguration is one of the most common security issues. Weak passwords, improper access control settings, or incorrect encryption configurations can create vulnerabilities.
Another risk involves unauthorized access to SNMP management interfaces. If devices are exposed to untrusted networks without proper filtering, attackers may attempt to exploit them.
To mitigate these risks, organizations should implement strong configuration policies, use secure authentication methods, and restrict SNMP access to trusted management networks only. Regular audits and configuration reviews are also essential.
SNMPv3 and Network Automation Integration
SNMPv3 is increasingly being integrated into network automation systems. Automation tools use SNMPv3 to collect real-time data and make intelligent decisions about network configuration and optimization.
For example, automated systems can detect high traffic loads and dynamically adjust routing policies or allocate additional resources. SNMPv3 provides the secure data exchange needed for these automated processes to function reliably.
This integration helps organizations reduce manual intervention and improve operational efficiency.
Debugging SNMPv3 Communication Issues
Debugging SNMPv3 issues requires a systematic approach due to its layered security structure. Common problems include mismatched security levels, incorrect user credentials, and encryption incompatibilities.
When communication fails, administrators typically begin by verifying engine IDs and ensuring that both manager and agent are using the same security parameters. Authentication failures are checked by reviewing username and hashing configurations.
If encryption is enabled, compatibility between algorithms must also be confirmed. Logging tools and diagnostic commands are essential for identifying where the communication breakdown occurs.
Impact of SNMPv3 on Network Performance
While SNMPv3 improves security, it introduces additional processing overhead due to encryption and authentication. This can slightly impact device performance, especially in older or low-powered hardware.
However, in most modern systems, this impact is minimal and acceptable compared to the security benefits. Proper tuning of polling intervals and efficient configuration can further reduce performance overhead.
In large-scale deployments, performance monitoring tools are often used to balance security requirements with system efficiency.
Vendor Implementation Differences
Although SNMPv3 is a standardized protocol, different vendors may implement it with slight variations. These differences can appear in configuration syntax, default security settings, or supported encryption algorithms.
As a result, administrators must carefully review device documentation when configuring SNMPv3 in multi-vendor environments. Ensuring compatibility across devices is essential for maintaining consistent network management.
Standardization efforts help reduce these differences, but some variation is still common in real-world deployments.
Evolution of Network Management Beyond SNMPv3
While SNMPv3 remains widely used, newer network management approaches are emerging. These include API-based monitoring, telemetry systems, and cloud-native observability platforms.
These modern systems often provide more real-time and granular data compared to traditional SNMP polling. However, SNMPv3 continues to play an important role due to its simplicity, reliability, and widespread support across network devices.
In many environments, SNMPv3 is used alongside newer technologies rather than being replaced entirely.
Best Deployment Practices for Large Networks
In large networks, proper deployment of SNMPv3 requires careful planning. Administrators should design a hierarchical monitoring structure to distribute load efficiently. Security policies should be standardized across all devices to avoid inconsistencies.
It is also important to document all SNMP configurations, including user accounts, security levels, and access policies. Regular audits should be conducted to ensure compliance with security standards.
Backup configurations should be maintained to allow quick recovery in case of device failure or misconfiguration.
Final Understanding of SNMPv3 Importance
SNMPv3 represents a mature and secure solution for network management in modern IT environments. Its combination of authentication, encryption, and access control makes it suitable for securing sensitive network operations.
Despite the emergence of newer monitoring technologies, SNMPv3 continues to be a foundational protocol due to its stability and universal support. When properly configured and managed, it provides a reliable and secure way to monitor and control complex network infrastructures.
SNMPv3 Troubleshooting Methodology
Troubleshooting SNMPv3 requires a structured and methodical approach because of its layered security design. Unlike earlier SNMP versions, issues in SNMPv3 can originate from authentication, encryption, access control, or even time synchronization mismatches. Therefore, identifying the exact layer where failure occurs is essential for quick resolution.
The first step in troubleshooting is verifying basic connectivity between the management station and the target device. If the device is unreachable, SNMP-related checks become irrelevant until network connectivity is restored. Once connectivity is confirmed, attention shifts to SNMP configuration parameters.
Authentication issues are among the most common problems. These usually occur when the username, authentication protocol, or authentication key does not match between the SNMP manager and the agent. Even a minor mismatch in configuration leads to message rejection. Similarly, privacy-related errors arise when encryption algorithms or keys are inconsistent on both ends.
Another critical factor is Engine ID synchronization. If the SNMP manager does not recognize the device’s Engine ID or if it changes unexpectedly, communication fails. Time synchronization is equally important because SNMPv3 uses time-based checks to prevent replay attacks. If system clocks are not properly aligned, valid messages may be rejected.
Effective troubleshooting relies on detailed logging and diagnostic output from both the management system and the device. By analyzing error messages, administrators can isolate whether the issue is related to authentication, encryption, or access control.
SNMPv3 in Security Compliance and Auditing
SNMPv3 plays a significant role in meeting modern security compliance requirements. Many regulatory frameworks require encryption and secure authentication for network communication, especially in enterprise and critical infrastructure environments. SNMPv3 satisfies these requirements by providing built-in security features.
In auditing scenarios, SNMPv3 logs can be used to track access attempts, configuration changes, and system alerts. These logs help organizations maintain accountability and detect unauthorized activity. Because every SNMPv3 request is associated with a specific user identity, it becomes easier to trace actions back to individual administrators.
This level of traceability is essential for compliance with security standards and internal governance policies. It also helps organizations demonstrate that proper access control mechanisms are in place and functioning correctly.
SNMPv3 and Fault Management Systems
Fault management is one of the core functions of network monitoring systems, and SNMPv3 plays a vital role in this process. Devices continuously monitor their own status and report issues through SNMP traps or informs.
When a fault occurs, such as a link failure or hardware malfunction, SNMPv3-enabled devices immediately generate notifications. These alerts are securely transmitted to the management system, where they are processed and analyzed. Depending on severity, the system may trigger automated responses or notify network administrators.
Because SNMPv3 ensures message integrity and confidentiality, fault notifications cannot be altered or intercepted by unauthorized entities. This increases reliability in mission-critical environments where timely and accurate fault detection is essential.
SNMPv3 Performance Optimization in Real Deployments
Optimizing SNMPv3 performance is important in large and complex networks. Since SNMPv3 uses encryption and authentication, it naturally introduces some processing overhead. However, this overhead can be managed effectively through proper configuration.
One optimization technique is adjusting polling intervals based on device importance. Critical devices may be polled more frequently, while less important devices are monitored at longer intervals. This reduces unnecessary network traffic and system load.
Another method involves using bulk requests instead of multiple individual queries. This reduces communication overhead and improves efficiency. Event-driven monitoring using traps and informs is also preferred in many cases because it eliminates the need for constant polling.
Proper indexing of MIB objects and efficient query design further contribute to performance optimization.
SNMPv3 Deployment in Distributed Networks
In distributed network environments, SNMPv3 is used to monitor devices spread across multiple locations. This includes branch offices, remote data centers, and geographically dispersed infrastructure.
To manage such environments efficiently, distributed monitoring systems are often deployed. Local managers collect SNMP data from nearby devices and forward aggregated information to a central monitoring system. This reduces latency and improves scalability.
Secure communication between distributed components is essential, and SNMPv3 ensures that data remains protected across all communication paths. Proper segmentation and hierarchical design help maintain performance and reliability in large-scale deployments.
SNMPv3 Integration with IT Operations
Modern IT operations rely heavily on integrated monitoring systems that combine SNMPv3 with other data sources. SNMPv3 provides infrastructure-level insights, while other tools may provide application-level or cloud-level data.
By integrating SNMPv3 with centralized IT operations platforms, organizations can achieve a unified view of their entire infrastructure. This enables faster decision-making and improved incident response.
Automation systems often use SNMPv3 data to trigger workflows, such as scaling resources, restarting services, or isolating faulty components. This integration improves operational efficiency and reduces downtime.
Limitations in Complex Environments
Although SNMPv3 is powerful, it has limitations in highly dynamic or modern cloud-native environments. Its polling-based model may not always provide real-time insights compared to streaming telemetry solutions.
Additionally, configuration complexity can become a challenge in environments with thousands of devices. Managing consistent security policies across all devices requires careful planning and automation support.
Despite these limitations, SNMPv3 remains widely used because of its simplicity, stability, and broad vendor support.
Best Practices for Long-Term SNMPv3 Maintenance
Long-term maintenance of SNMPv3 systems requires continuous monitoring and periodic updates. Security credentials should be rotated regularly to reduce the risk of compromise. Outdated encryption methods should be replaced with stronger alternatives wherever possible.
Configuration backups should be maintained to ensure quick recovery in case of system failure. Documentation of all SNMP settings, including users, groups, and access policies, is essential for operational continuity.
Regular audits should be performed to identify misconfigurations or unused accounts. These practices help maintain a secure and efficient SNMPv3 environment over time.
Future Trends in SNMPv3 Usage
Although newer technologies are emerging in network monitoring, SNMPv3 continues to evolve. It is increasingly being used alongside telemetry-based systems to provide a hybrid monitoring approach.
Future implementations are expected to focus on better automation, improved scalability, and tighter integration with cloud-native platforms. SNMPv3 will likely remain an important fallback and foundational protocol for device-level monitoring.
Its simplicity and universality ensure that it will continue to be supported across a wide range of devices and vendors.
Conclusion
SNMPv3 represents a major advancement in network management protocols by combining traditional monitoring capabilities with strong security features. It addresses the weaknesses of earlier versions by introducing authentication, encryption, and access control mechanisms that protect network communication from unauthorized access and tampering.
Throughout its architecture, SNMPv3 ensures that every message is verified, encrypted, and properly authorized before being processed. Its user-based security model and view-based access control system provide fine-grained control over network data access, making it suitable for enterprise and critical infrastructure environments.
Despite its complexity and some performance overhead, SNMPv3 remains a reliable and widely adopted protocol due to its robustness and compatibility. It continues to play a key role in network monitoring, fault detection, and system management across diverse IT environments.
As networks continue to grow in scale and complexity, SNMPv3 will remain an essential component of secure and effective network management strategies.