Network Address Translation (NAT) is a fundamental concept in modern networking that plays a crucial role in how devices communicate over the internet. It is widely used in homes, businesses, and large enterprise networks to manage and conserve IP addresses while also adding a layer of security. NAT acts as an intermediary between a private internal network and the public internet, translating private IP addresses into public ones and vice versa. Without NAT, the exhaustion of IPv4 addresses would have become an even more critical issue much earlier.
At its core, NAT enables multiple devices within a private network to share a single public IP address for internet access. This makes it an essential technology for both connectivity and scalability. Understanding NAT types and how they function is important for anyone studying networking, cybersecurity, or IT infrastructure.
What is NAT in Networking
Network Address Translation is a process performed by routers or firewalls that modifies IP address information in packet headers while they are in transit across a routing device. When a device inside a private network sends a request to the internet, NAT changes the private IP address of that device into a public IP address. When the response returns, NAT ensures that the data is sent back to the correct internal device.
Private IP addresses are not routable on the public internet, so NAT allows communication between private networks and external systems without requiring a unique public IP for every device. This has made it possible for organizations to use internal IP addressing schemes freely without worrying about global uniqueness.
NAT also contributes to security by hiding internal network structures from external users. Since external systems only see the public IP address, the internal devices remain protected from direct exposure.
How NAT Works in a Network Environment
NAT operates on a device such as a router or firewall that sits between an internal network and the internet. When a packet leaves an internal device, NAT modifies the source IP address from a private IP to a public IP. It also keeps track of this translation in a table known as a NAT table.
When a response comes back from the internet, NAT checks the destination IP and matches it with the stored entry in the NAT table. It then forwards the packet to the correct internal device using its private IP address.
This translation process happens extremely quickly and is generally transparent to the user. From the user’s perspective, web browsing and online communication appear normal, even though multiple translations are occurring in the background.
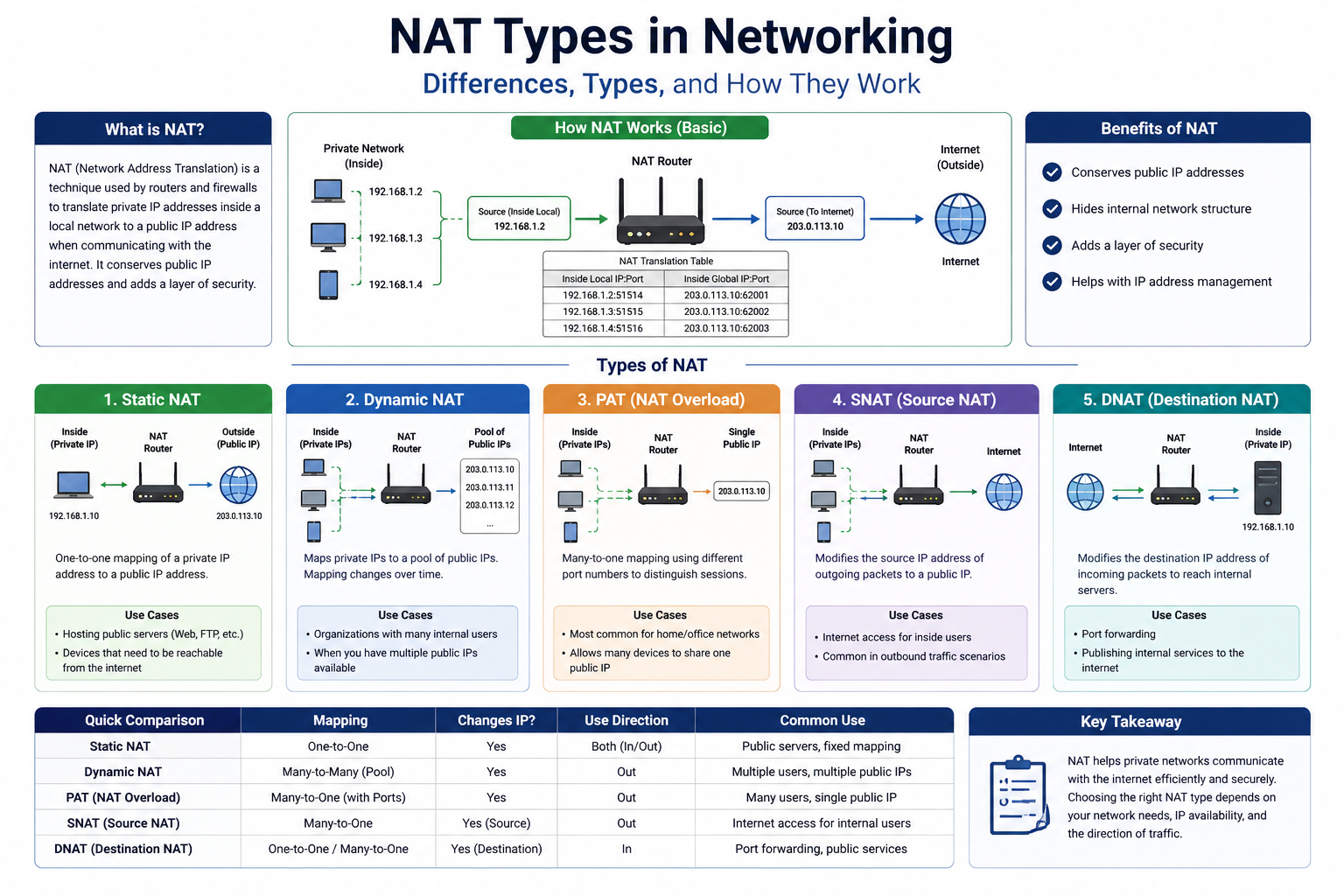
Types of NAT in Networking
There are several types of NAT used in networking, each serving a specific purpose depending on the network size, structure, and requirements. The three main types are Static NAT, Dynamic NAT, and Port Address Translation (PAT), also known as NAT overload.
Each type handles IP translation differently and is chosen based on scalability, security needs, and available public IP addresses.
Static NAT and Its Functionality
Static NAT is a one-to-one mapping between a private IP address and a public IP address. In this method, a specific private IP is permanently assigned to a specific public IP. This means the same internal device will always use the same public IP address when communicating with external networks.
Static NAT is commonly used when a device inside a private network needs to be accessible from the outside internet, such as a web server, mail server, or remote access system. Because the mapping never changes, external systems can reliably connect to the internal device using the same public IP address.
One advantage of static NAT is its simplicity and predictability. It provides consistent access and is easy to configure. However, it is not efficient in terms of IP address usage because each private device requires a dedicated public IP. This can become costly and impractical when managing large networks.
Despite this limitation, static NAT is still widely used in scenarios where stable and direct communication is necessary.
Dynamic NAT and Its Behavior
Dynamic NAT is a more flexible form of address translation. Instead of assigning a fixed public IP to each private device, dynamic NAT uses a pool of available public IP addresses. When an internal device requests access to the internet, NAT assigns an available public IP from the pool temporarily.
Once the session is complete, the public IP is returned to the pool and can be used by another device. This dynamic allocation allows better utilization of limited public IP addresses compared to static NAT.
Dynamic NAT is useful in environments where there are more internal devices than available public IP addresses, but where not all devices require simultaneous external communication.
However, dynamic NAT still has limitations. If all public IP addresses in the pool are in use, additional devices cannot access the internet until an address becomes available. Also, because mappings are temporary, external systems cannot reliably initiate communication with internal devices.
Despite these constraints, dynamic NAT is widely used in medium to large networks where efficient IP usage is important.
Port Address Translation and Its Importance
Port Address Translation, often referred to as PAT or NAT overload, is the most commonly used form of NAT in modern networks. It allows multiple internal devices to share a single public IP address by distinguishing each session using port numbers.
In PAT, not only the IP address is translated, but also the port number associated with each connection. This enables thousands of devices to access the internet simultaneously using just one public IP address.
For example, two devices inside a network may both be accessing a website at the same time. PAT will assign different port numbers to each session so that responses from the internet are correctly routed back to the appropriate device.
The major advantage of PAT is its extremely efficient use of public IP addresses. It significantly reduces the need for multiple public IPs, making it ideal for home networks, small businesses, and even large enterprises.
However, because all traffic is multiplexed through a single IP, troubleshooting can sometimes be more complex. Also, some applications that require direct inbound connections may face limitations unless specific configurations are applied.
Differences Between NAT Types in Practical Use
Each NAT type serves a different purpose depending on network requirements. Static NAT is best suited for devices that need permanent external access. Dynamic NAT is ideal for temporary and flexible internet access where IP conservation is important. PAT is the most efficient and widely used method, especially in environments where many devices must share a limited number of public IPs.
The choice between these NAT types depends on factors such as network size, cost considerations, security requirements, and the nature of applications being used. Large organizations may use a combination of all three types depending on different departments or services.
Role of NAT in Modern Networking
NAT has become an essential component of modern networking infrastructure. One of its most important contributions is the conservation of IPv4 addresses. Since IPv4 has a limited address space, NAT allows millions of devices to access the internet without requiring unique public IPs for each one.
Another key role of NAT is improving network security. By hiding internal IP addresses from external networks, NAT reduces the exposure of internal systems to direct attacks. While it is not a full security solution on its own, it adds an additional layer of protection.
NAT also simplifies network management by allowing internal IP addressing schemes to remain independent of external ISP assignments. Organizations can freely design their internal networks without worrying about global IP conflicts.
NAT Table and Translation Process in Depth
Every NAT-enabled device maintains a structure called a NAT translation table. This table is the core mechanism that allows address mapping between private and public networks. Whenever an internal device initiates communication with an external system, the router creates an entry in this table that stores details such as the private IP address, public IP address, port numbers, and connection state.
The NAT table works like a dynamic lookup system. When a packet leaves the internal network, the router replaces the private source IP with a public IP and assigns a unique port number if needed. This combination of IP address and port number ensures that multiple sessions can be tracked simultaneously without conflict.
When a response returns from the external server, the router checks the destination port and IP against the NAT table entries. Once a match is found, the router translates the public IP back into the correct private IP and forwards the packet to the internal device.
This process is extremely fast and optimized within networking hardware. However, the size of the NAT table is limited by device memory and processing power. In high-traffic environments, inefficient NAT table management can lead to dropped connections or delays.
Port Forwarding and Manual NAT Configuration
Port forwarding is a technique used alongside NAT to allow external devices to initiate communication with specific internal devices. Since NAT normally blocks unsolicited inbound traffic, port forwarding creates a rule that maps a specific external port to an internal IP address and port.
For example, if a web server is running inside a private network, port forwarding can be configured so that requests coming to a public IP on port 80 are directed to the internal server. This allows external users to access internal services securely.
Port forwarding is commonly used in hosting game servers, remote desktop connections, CCTV systems, and web hosting environments. While it improves accessibility, it also requires careful configuration because incorrect rules can expose internal systems to security risks.
Manual NAT configuration gives network administrators full control over how traffic is translated and routed. However, it also increases complexity, especially in large-scale networks where multiple services require different mappings.
Carrier-Grade NAT in Large Networks
Carrier-Grade NAT (CGNAT) is an advanced form of NAT used by internet service providers to manage IPv4 address exhaustion on a large scale. In CGNAT, multiple customers share a single public IP address provided by the ISP.
Instead of each home or business receiving a unique public IP, the ISP assigns private IP addresses to customers and then uses a large-scale NAT system to translate them into shared public IPs.
This approach significantly reduces the demand for IPv4 addresses, but it introduces certain limitations. Since many users share the same public IP, direct inbound connections become difficult or impossible without additional configuration. This affects applications like peer-to-peer services, online gaming, and remote access systems.
CGNAT also complicates network troubleshooting because identifying a specific user behind a shared IP requires deeper logging and tracking mechanisms.
Despite these challenges, CGNAT is widely used because it helps ISPs continue operating despite the global shortage of IPv4 addresses.
NAT Traversal and Connectivity Challenges
One of the major limitations of NAT is that it breaks end-to-end connectivity. Since NAT modifies IP addresses, devices outside the private network cannot directly initiate connections to internal devices. This creates challenges for applications that require real-time or peer-to-peer communication.
NAT traversal techniques are used to overcome this limitation. These techniques allow devices behind NAT to establish direct or semi-direct communication with other devices across the internet.
Common NAT traversal methods include STUN, TURN, and ICE protocols. These systems help devices discover their public-facing IP addresses and negotiate communication paths through NAT devices.
NAT traversal is essential for technologies like voice over IP, video conferencing, and online gaming. Without these methods, many modern communication systems would not function effectively behind NAT networks.
However, NAT traversal is not always perfect. In complex NAT environments, especially with multiple layers of NAT or CGNAT, establishing stable connections can still be difficult.
Security Aspects of NAT in Networking
NAT is often considered a security-enhancing feature, although it is not a replacement for dedicated security systems like firewalls. By hiding internal IP addresses, NAT makes it harder for external attackers to directly target internal devices.
Since external systems only see the public IP address, internal network topology remains concealed. This reduces exposure and limits the attack surface.
However, NAT does not inspect packet content or block malicious traffic by itself. It simply translates addresses. For this reason, NAT is typically used in combination with firewalls and intrusion detection systems for stronger security.
One misconception is that NAT alone provides full protection. In reality, if a malicious connection is initiated from inside the network, NAT will still allow it unless additional security rules are applied.
Despite its limitations, NAT remains an important part of layered security architecture in modern networks.
Performance Impact of NAT on Networks
Although NAT is highly efficient, it does introduce some processing overhead. Every packet that passes through a NAT device must be inspected, translated, and recorded in the NAT table. In small networks, this overhead is negligible, but in large-scale environments, it can become significant.
High-performance routers and firewalls are designed with hardware acceleration to handle NAT processing efficiently. These devices use specialized chips to reduce latency and improve throughput.
However, when NAT is overloaded with too many active connections, performance issues such as packet delay, jitter, or connection drops may occur. This is especially relevant in environments with heavy video streaming, gaming, or cloud services.
Optimizing NAT performance often involves tuning timeouts, increasing table capacity, and distributing traffic across multiple devices.
NAT and IPv6 Transition
The introduction of IPv6 was designed to solve the IP address exhaustion problem that NAT was originally created to address. IPv6 provides a vastly larger address space, allowing every device to have a unique global IP address.
In an ideal IPv6 environment, NAT would not be necessary because end-to-end connectivity would be restored. However, in practice, NAT is still used in many hybrid networks where IPv4 and IPv6 coexist.
Techniques such as NAT64 are used to allow communication between IPv6-only and IPv4-only systems. This ensures compatibility during the transition period between the two protocols.
Even though IPv6 reduces the need for NAT, many organizations continue to use NAT due to existing infrastructure, security policies, and operational familiarity.
Double NAT and Complex Network Structures
Double NAT occurs when two NAT devices are placed in sequence within a network. This often happens in home networks where a router is connected to another router provided by an ISP.
In a double NAT scenario, traffic is translated twice before reaching the internet. While this setup can still function, it often causes issues with port forwarding, gaming connectivity, and remote access applications.
Troubleshooting double NAT requires identifying each NAT layer and adjusting configuration to reduce conflicts. In some cases, switching one device to bridge mode helps eliminate unnecessary translation layers.
Complex enterprise networks may also use multiple NAT layers for segmentation and security purposes, but this requires careful planning to avoid connectivity problems.
Application of NAT in Real-World Systems
NAT is used extensively in real-world systems ranging from small home routers to large enterprise data centers. In home environments, NAT enables all household devices such as phones, laptops, and smart TVs to access the internet using a single ISP-provided IP address.
In corporate environments, NAT helps manage internal networks while maintaining controlled internet access for employees. It also allows internal services to remain hidden from external users.
Cloud environments also use NAT to manage communication between virtual machines and external services. Virtual private clouds often rely on NAT gateways to provide internet access without exposing internal resources.
In addition, NAT is used in security architectures where sensitive systems must remain isolated from direct internet exposure while still requiring controlled outbound communication.
Limitations and Challenges of NAT Systems
Despite its usefulness, NAT introduces several limitations. One major issue is the loss of true end-to-end connectivity. Because IP addresses are modified, direct peer-to-peer communication becomes more complex.
Another challenge is application compatibility. Some applications embed IP address information inside payloads, which NAT cannot modify. This can cause failures unless special protocols or application-layer gateways are used.
NAT also adds complexity to network troubleshooting. Identifying the source of an issue can be difficult when multiple translations are occurring simultaneously.
In addition, NAT introduces state dependency. If the NAT table is cleared or corrupted, active sessions may be disrupted.
Scalability can also become a concern in very large networks where thousands of simultaneous translations must be maintained.
Advanced NAT Configurations in Enterprise Networks
Large enterprises often implement advanced NAT configurations to handle complex networking needs. These configurations may include policy-based NAT, where translation rules are applied based on specific conditions such as source address, destination address, or application type.
Another advanced technique is NAT overload balancing, where multiple public IPs are distributed across internal devices to improve performance and reduce congestion.
Some networks also use destination NAT, which modifies the destination IP address of incoming packets instead of the source IP. This is commonly used in load balancing and reverse proxy systems.
These advanced configurations require careful planning and monitoring to ensure reliability and efficiency across the entire network infrastructure.
NAT Behavior in Virtualized and Cloud Environments
In virtualized environments, NAT plays a crucial role in connecting virtual machines to external networks. Hypervisors often implement built-in NAT services that allow virtual machines to share the host machine’s network connection.
Cloud platforms use NAT gateways to manage outbound internet traffic from private subnets. This allows cloud resources to access external services while remaining inaccessible from the public internet.
These implementations are essential for maintaining security boundaries in cloud architectures. They allow organizations to design isolated environments while still enabling controlled internet access.
Virtual NAT systems are highly scalable and can handle dynamic workloads efficiently, making them suitable for modern cloud-native applications.
NAT Troubleshooting in Real Network Environments
Troubleshooting NAT-related issues requires understanding how translation, routing, and session tracking interact. Many connectivity problems that appear as “internet not working” are actually caused by incorrect NAT behavior or misconfigured translation rules. The first step in diagnosing NAT issues is usually checking whether the NAT table is being populated correctly. If entries are missing or incomplete, it indicates that traffic is not being translated properly.
One common issue is session timeout, where NAT removes an entry from the translation table too early. When this happens, returning packets no longer match any active session, causing connection drops. This is especially noticeable in applications like video calls or online gaming where continuous data flow is required.
Another frequent problem is asymmetric routing. This occurs when outbound and inbound traffic take different paths through the network. Since NAT relies on consistent mapping, any mismatch can cause packets to be dropped or misrouted.
Network administrators also often face issues related to overloaded NAT tables. When too many simultaneous connections are active, older entries may be removed prematurely to make space for new ones. This leads to random disconnections that are difficult to reproduce.
Packet capture tools are commonly used to analyze NAT behavior. By inspecting packet headers before and after translation, administrators can verify whether NAT is functioning correctly. Log analysis from routers and firewalls also helps identify translation failures or conflicts.
NAT Behavior in Online Gaming and Real-Time Applications
Online gaming is one of the most sensitive use cases for NAT because it requires low latency and stable peer-to-peer connectivity. Many multiplayer games rely on direct connections between players, but NAT often prevents this by blocking inbound traffic.
This is why gamers frequently encounter NAT type classifications such as open, moderate, or strict NAT. These classifications describe how easily a device can communicate with others through NAT restrictions.
A restrictive NAT type limits matchmaking capabilities and can cause lag or disconnection issues. This happens when the NAT device does not allow inbound connections or when multiple layers of NAT are present.
Voice chat applications and real-time communication platforms also face similar challenges. These systems often rely on NAT traversal techniques to establish connections between users. If traversal fails, communication may become unstable or completely blocked.
To improve performance, some users configure port forwarding or enable specific NAT rules on their routers. However, improper configuration can expose devices to unwanted external access, so careful setup is required.
Symmetric, Full Cone, Restricted, and Port-Restricted NAT Behavior
Beyond the general NAT types like static, dynamic, and PAT, there are also behavioral classifications of NAT that describe how strictly the translation system handles external communication.
Symmetric NAT is one of the most restrictive forms. In this type, each request to a different destination receives a unique mapping. This means that even if the same internal device communicates with multiple external servers, each connection is treated separately. This improves security but makes peer-to-peer communication very difficult.
Full cone NAT is the least restrictive behavior. Once an internal device is mapped to a public IP and port, any external system can send packets to it using that mapping. While this allows easier connectivity, it is less secure because it exposes internal devices more openly.
Restricted NAT allows external communication only if the internal device has previously sent a request to that external IP. This creates a balance between security and accessibility.
Port-restricted NAT goes a step further by requiring both the external IP and port to match a previous outbound request. This provides stricter control over incoming traffic while still allowing limited peer-to-peer functionality.
These behavioral types are especially important in applications like VoIP, video conferencing, and gaming, where NAT traversal success depends heavily on the NAT type being used.
NAT Hairpinning and Internal Loopback Communication
NAT hairpinning, also known as NAT loopback, is a feature that allows internal devices to access each other using the external public IP address of the network. Without this capability, internal requests to the public IP may fail because NAT does not recognize them as internal traffic.
For example, if a user inside a network tries to access a server hosted within the same network using its public IP, NAT hairpinning ensures the request is correctly looped back to the internal server.
This feature is particularly useful in home servers, small business setups, and testing environments. However, not all routers support hairpinning, and in such cases, alternative DNS configurations are often required.
Implementing NAT loopback requires careful routing logic because the system must recognize that the traffic originates internally even though it is addressed externally.
NAT in Load Balancing and High Availability Systems
In enterprise environments, NAT is often integrated with load balancing systems to distribute traffic across multiple servers. Destination NAT can be used to redirect incoming traffic to different backend servers based on predefined rules.
This ensures that no single server becomes overloaded and that system performance remains stable even under high traffic conditions.
High availability systems also rely on NAT to reroute traffic in case of server failure. If one server becomes unavailable, NAT rules can automatically redirect traffic to a backup server without user intervention.
This setup is commonly used in data centers, cloud infrastructures, and large-scale web applications where downtime must be minimized.
However, maintaining such systems requires precise synchronization between NAT rules and server health monitoring systems. Any mismatch can lead to traffic being sent to inactive or overloaded servers.
NAT Logging and Monitoring Mechanisms
NAT logging is an essential part of network monitoring because it provides visibility into how IP addresses are being translated over time. Each NAT entry typically logs information such as source IP, destination IP, port numbers, timestamps, and session duration.
These logs are useful for troubleshooting connectivity issues, analyzing traffic patterns, and identifying security incidents. In some cases, NAT logs are also required for compliance and auditing purposes.
However, NAT logging can generate large amounts of data in high-traffic environments. Efficient storage and log rotation strategies are required to prevent performance degradation.
Monitoring tools often visualize NAT behavior in real time, allowing administrators to see active connections and translation mappings. This helps in detecting anomalies such as unusual traffic spikes or unauthorized access attempts.
Security Limitations and Misconceptions of NAT
Although NAT provides a level of obscurity, it is not a full security solution. One common misconception is that NAT acts as a firewall. In reality, NAT only modifies IP addresses and does not inherently block malicious traffic.
If a connection is initiated from inside the network, NAT will allow it unless additional firewall rules are in place. This means that malware or compromised devices inside the network can still communicate externally.
Another limitation is that NAT does not provide encryption or data integrity protection. It simply translates network addresses without inspecting payload content.
Relying solely on NAT for security can create a false sense of protection. For this reason, modern networks use a combination of NAT, firewalls, intrusion detection systems, and endpoint security solutions.
Despite these limitations, NAT remains valuable as part of a layered security model, especially in reducing direct exposure of internal systems.
NAT and Internet Service Provider Architectures
Internet service providers use NAT extensively to manage large-scale user networks. Due to the limited availability of IPv4 addresses, ISPs often assign private IP addresses to customers and use NAT systems at their infrastructure level.
This allows thousands of users to share a smaller pool of public IP addresses efficiently. The ISP’s NAT system handles translation for all outbound and inbound traffic across its customer base.
However, this model introduces challenges for users who require direct inbound connectivity. Hosting servers, remote access, and peer-to-peer applications may be affected unless special arrangements or static public IPs are provided.
ISPs also use advanced NAT systems to manage traffic shaping, bandwidth control, and routing optimization across their networks.
NAT Scalability Challenges in Large Networks
As networks grow, NAT scalability becomes a critical concern. Each active session consumes memory and processing resources in the NAT table. In extremely large networks, millions of simultaneous translations may be required.
To handle this, high-performance networking devices use optimized hardware acceleration and distributed NAT architectures. These systems split translation workloads across multiple devices to avoid bottlenecks.
However, scaling NAT introduces complexity in synchronization and failover handling. If one NAT device fails, session continuity must be preserved to avoid widespread disconnections.
Large organizations often implement redundant NAT gateways to ensure reliability. These gateways share session state information to maintain continuity during failover events.
NAT Interaction with Modern Internet Protocols
Modern internet protocols are designed with NAT limitations in mind. Many applications now include built-in NAT traversal support to ensure connectivity even in restrictive environments.
Protocols such as WebRTC rely heavily on NAT traversal techniques to enable real-time communication in browsers. These systems automatically detect NAT behavior and adapt connection methods accordingly.
Cloud-based applications also design their networking layers around NAT constraints, ensuring that services remain accessible regardless of underlying network translation.
Despite advancements, NAT continues to influence how protocols are designed and deployed across the internet ecosystem.
Advanced NAT Security Considerations in Modern Networks
In modern network environments, NAT is often integrated into broader security frameworks rather than being treated as a standalone mechanism. While NAT provides basic obscurity by hiding internal IP addresses, advanced security design focuses on controlling traffic behavior, not just address translation. This is why NAT is commonly paired with stateful firewalls that track connection states more deeply than simple translation tables.
One important consideration is that NAT can sometimes interfere with intrusion detection systems if not properly configured. Since NAT modifies packet headers, security tools must be aware of translation rules to correctly interpret traffic origin and destination. Without this alignment, security alerts may become inaccurate or misleading.
Another security concern arises when NAT rules are too permissive. Overly broad port forwarding or unrestricted NAT mappings can expose internal services to external threats. This is especially risky in environments where multiple services are hosted behind a single public IP address.
Modern networks address these risks by implementing strict access control lists alongside NAT configurations. These rules define exactly which traffic is allowed to pass through translation layers, reducing the chance of unauthorized access.
Encryption also plays a critical role. Since NAT does not encrypt data, secure protocols such as TLS are necessary to protect information while it passes through NAT devices. Without encryption, translated traffic remains vulnerable to interception.
NAT and Quality of Service in Network Traffic Management
Quality of Service (QoS) is another area where NAT interacts with network performance. In many enterprise and service provider environments, NAT must work alongside traffic prioritization systems to ensure critical applications receive sufficient bandwidth.
For example, voice and video communication traffic often requires low latency. NAT devices must ensure that translation processes do not introduce delays that degrade call quality. This is achieved by prioritizing certain types of traffic in the NAT processing queue.
However, QoS and NAT can sometimes conflict. Since NAT modifies packet headers, QoS rules based on IP addresses or ports may need to be adjusted dynamically. If NAT mappings change frequently, maintaining consistent QoS policies becomes more complex.
To solve this, advanced networking systems use classification methods that identify traffic types before NAT translation occurs. This ensures that priority handling remains consistent even after address modification.
Scalability Improvements Through NAT Optimization Techniques
As networks grow larger, optimizing NAT performance becomes essential. One common technique is connection pooling, where multiple sessions are grouped and managed efficiently to reduce NAT table overhead.
Another optimization approach is session timeout tuning. By adjusting how long inactive sessions remain in the NAT table, administrators can balance resource usage with application stability. Short timeouts free resources quickly but may disrupt long-lived connections, while longer timeouts improve stability but consume more memory.
Hardware acceleration is also widely used in modern routers and firewalls. Dedicated processing chips handle NAT translation independently from the main CPU, significantly improving throughput and reducing latency.
Load balancing across multiple NAT gateways is another scalability strategy. Instead of relying on a single device, traffic is distributed across several NAT systems, ensuring no single point becomes a bottleneck.
These techniques are especially important in cloud data centers, telecom networks, and large enterprise infrastructures where millions of simultaneous connections are common.
Impact of NAT on Internet Architecture Evolution
NAT has had a significant influence on the evolution of internet architecture. Originally, the internet was designed around the idea of end-to-end connectivity, where every device could directly communicate with any other device using a unique IP address.
However, the rapid growth of internet-connected devices led to IPv4 exhaustion, making NAT a necessary workaround. This shift fundamentally changed how networks are designed, moving away from direct addressing toward layered connectivity models.
As a result, many modern applications are now built with NAT awareness in mind. Instead of relying on direct connections, they use intermediary servers, signaling systems, and relay mechanisms to establish communication.
This architectural shift has also contributed to the rise of cloud computing. Centralized services often act as intermediaries between devices, reducing the need for direct peer-to-peer connectivity.
Even though IPv6 aims to restore end-to-end connectivity, NAT continues to play a role in transitional and hybrid environments where both protocols coexist.
Future of NAT in IPv6-Dominated Networks
With the gradual adoption of IPv6, the long-term necessity of NAT is expected to decrease. IPv6 provides a vastly larger address space, allowing every device to have a globally unique IP address without translation.
In an ideal IPv6 environment, NAT would no longer be required, restoring direct communication between devices. However, the transition is not immediate, and NAT will continue to exist for many years due to compatibility requirements.
Many networks operate in dual-stack mode, supporting both IPv4 and IPv6 simultaneously. In such environments, NAT is still used for IPv4 traffic while IPv6 traffic flows without translation.
Some specialized forms of NAT, such as NAT64, will continue to exist to bridge communication between IPv4 and IPv6 systems. This ensures interoperability during the transition period.
Even in a fully IPv6 world, concepts inspired by NAT may still persist in the form of traffic filtering, privacy extensions, and address abstraction techniques.
Operational Challenges in Large-Scale NAT Deployment
Deploying NAT at scale introduces several operational challenges that require careful management. One major challenge is maintaining session consistency across distributed systems. If NAT devices are not synchronized, active sessions may break during failover events.
Another challenge is logging and traceability. In large-scale NAT environments, multiple users may share the same public IP address. This makes it difficult to trace specific user activity without detailed logs that map internal and external sessions.
Regulatory compliance can also become complex in such scenarios, especially in environments that require user activity tracking for security or legal purposes.
Performance monitoring is another critical operational aspect. Administrators must continuously monitor NAT table usage, CPU load, and session distribution to ensure system stability.
Automation tools are increasingly used to manage these challenges. They can dynamically adjust NAT rules, balance traffic loads, and detect anomalies in real time.
Real-World Dependence on NAT in Everyday Internet Use
In everyday internet usage, NAT operates silently in the background without user awareness. Whether browsing websites, streaming videos, or using mobile apps, NAT is constantly translating network traffic.
Home routers typically use PAT to allow all devices in a household to share a single public IP address provided by the internet service provider. This enables smartphones, laptops, smart TVs, and IoT devices to operate simultaneously without IP conflicts.
In business environments, NAT helps isolate internal systems from external exposure while still allowing controlled internet access. Employees can browse the web, use cloud services, and communicate externally while internal systems remain protected.
Even mobile networks rely heavily on NAT systems. Cellular providers assign private IPs to mobile devices and use large-scale NAT systems to manage traffic across millions of users.
This widespread dependency highlights how essential NAT has become in maintaining global internet functionality.
Conclusion
NAT remains one of the most important foundational technologies in modern networking. It enables efficient use of limited IPv4 addresses, supports large-scale connectivity, and provides a basic level of network isolation. Across different implementations such as static NAT, dynamic NAT, and PAT, it adapts to various operational needs ranging from simple home networks to complex enterprise infrastructures.
Despite its limitations in breaking end-to-end connectivity and introducing complexity in certain applications, NAT continues to play a critical role in ensuring global internet accessibility. Even as IPv6 adoption increases, NAT’s influence remains deeply embedded in current networking systems, hybrid architectures, and transitional technologies.
Its continued use in security frameworks, cloud systems, ISP infrastructures, and real-time communication platforms demonstrates that NAT is not just a temporary solution but a long-standing component of how modern networks function and evolve.