802.1Q port tagging is a fundamental mechanism used in Ethernet networking to support Virtual Local Area Networks, commonly known as VLANs. It enables multiple logical networks to operate over a single physical network infrastructure. This technology is widely implemented in enterprise environments, data centers, and service provider networks where efficient traffic segmentation and network scalability are required.
At its core, 802.1Q tagging introduces a method of identifying which VLAN a particular Ethernet frame belongs to. This is achieved by inserting a small VLAN tag into the frame itself as it travels across network devices such as switches. This tag allows network equipment to correctly forward traffic only to the intended VLAN, ensuring proper separation and organization of data streams.
Concept of VLANs and Logical Segmentation
Before understanding 802.1Q tagging in detail, it is important to understand VLANs. A VLAN is a logical grouping of devices within a network, regardless of their physical location. Devices in the same VLAN behave as if they are connected to the same physical switch, even if they are spread across different switches or locations.
Without VLANs, all devices in a network belong to a single broadcast domain. This can lead to performance issues, security risks, and inefficient traffic management. VLANs solve this problem by dividing a single physical network into multiple isolated logical networks.
802.1Q tagging is the mechanism that makes communication between these VLANs possible over shared infrastructure.
Structure of an 802.1Q Tagged Frame
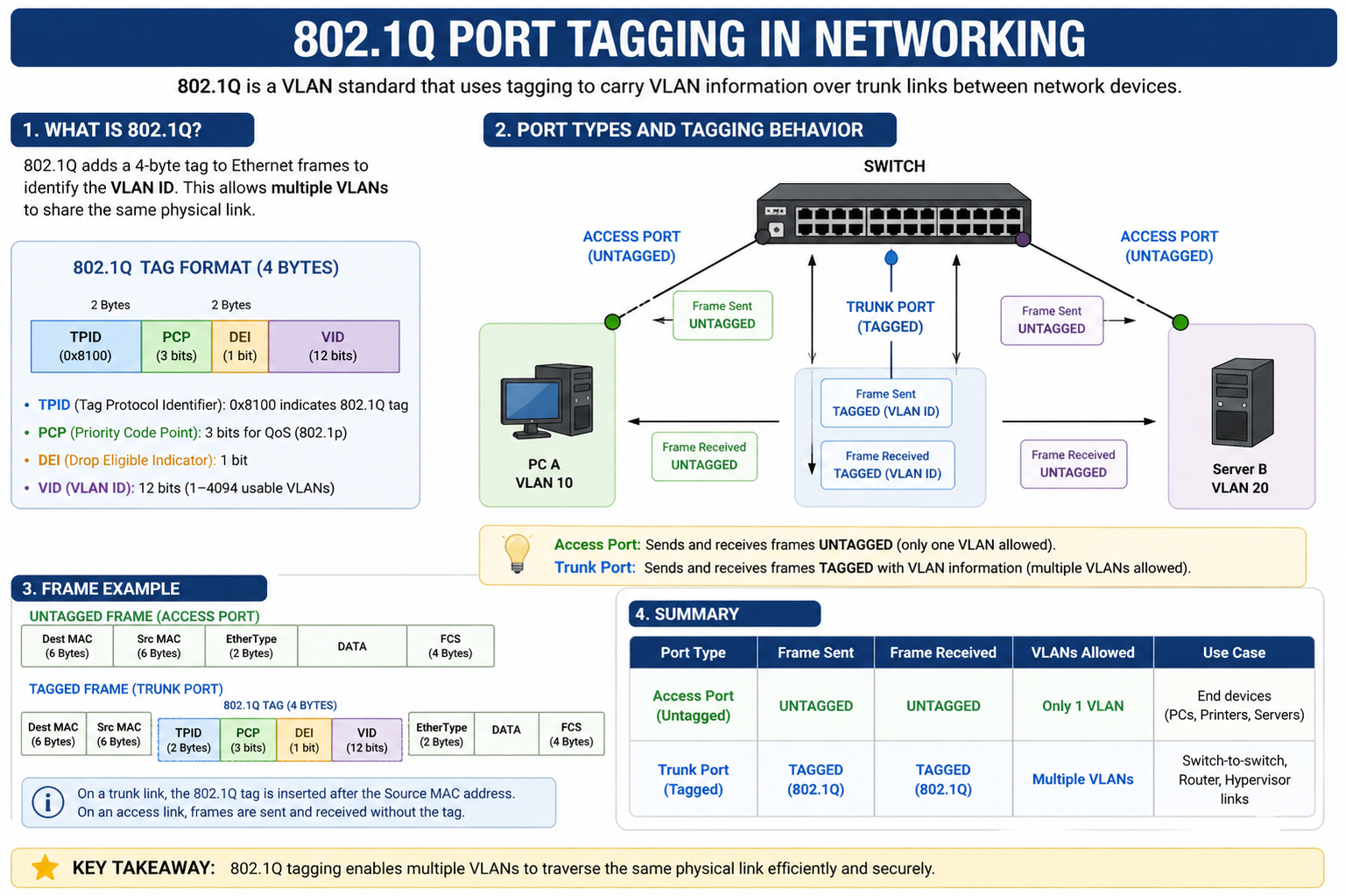
When a standard Ethernet frame is modified for VLAN tagging, a 4-byte VLAN tag is inserted into the frame header. This tag contains key information, including the VLAN identifier (VID), which specifies the VLAN to which the frame belongs.
This tagging process occurs at the switch level. When a frame enters a switch port configured for VLAN tagging, the switch adds the VLAN identifier. When the frame exits another trunk port, the tag remains intact so that downstream devices can continue to process it correctly.
The VLAN ID allows up to 4096 possible VLANs, although some are reserved for special purposes. This provides significant flexibility for large and complex networks.
Access Ports and Trunk Ports
In 802.1Q networking, switch ports are typically categorized into two types: access ports and trunk ports.
Access ports are used to connect end devices such as computers, printers, and servers. These ports belong to a single VLAN and do not carry tagged traffic. When a frame enters an access port, it is assumed to belong to the VLAN configured on that port, and no VLAN tag is added.
Trunk ports, on the other hand, are used to connect switches to other switches or networking devices. These ports carry traffic for multiple VLANs simultaneously. To differentiate between VLANs, trunk ports use 802.1Q tagging. Each frame sent over a trunk port includes a VLAN tag so that the receiving device knows how to handle it.
This distinction between access and trunk ports is essential for proper VLAN operation in any network.
Native VLAN Concept
In many 802.1Q implementations, there is a concept known as the native VLAN. The native VLAN is the VLAN whose traffic is transmitted without a tag on a trunk port. This means that frames belonging to the native VLAN are not modified with a VLAN identifier when they traverse the trunk link.
The purpose of the native VLAN is to maintain compatibility with devices that do not understand VLAN tagging. However, improper configuration of the native VLAN can lead to security risks and network miscommunication. For this reason, careful planning is required when designing VLAN architectures.
How VLAN Tagging Enables Communication
When a device sends data, the Ethernet frame is received by a switch. If the port is configured as an access port, the switch assigns the frame to a VLAN internally. If the frame is sent across a trunk link, the switch adds an 802.1Q tag that identifies the VLAN.
As the frame moves through the network, each switch reads the VLAN tag and forwards the frame only to ports that belong to the same VLAN. This ensures that devices in different VLANs remain isolated unless routing is explicitly configured between them.
At the final destination, if the frame reaches an access port, the VLAN tag is removed before it is delivered to the end device.
Advantages of 802.1Q Port Tagging
One of the primary benefits of 802.1Q tagging is efficient use of physical infrastructure. Instead of requiring separate switches or cables for each network segment, multiple VLANs can coexist on the same hardware.
It also enhances network security by isolating traffic between different departments or user groups. For example, guest users can be placed in a separate VLAN from internal corporate systems, reducing the risk of unauthorized access.
Another advantage is improved network performance. By reducing broadcast traffic within each VLAN, network congestion is minimized, leading to more stable and predictable performance.
Scalability is also a major benefit. Organizations can easily add new VLANs without changing the physical network layout.
Limitations and Challenges
Despite its advantages, 802.1Q tagging also has some limitations. Misconfiguration of VLANs or trunk ports can lead to network issues that are difficult to diagnose. For example, incorrect native VLAN settings can result in traffic leaks between VLANs.
Another challenge is the increased complexity in network design and management. As the number of VLANs grows, maintaining consistent configurations across all network devices becomes more demanding.
There is also a slight overhead introduced by VLAN tagging, although this is generally minimal and does not significantly affect performance in modern networks.
Practical Applications in Real Networks
802.1Q port tagging is widely used in enterprise environments where multiple departments require isolated network segments. For example, a company might separate finance, human resources, and engineering departments into different VLANs while still using the same physical switches.
In data centers, VLAN tagging allows virtualization platforms to segment traffic between different virtual machines or tenant environments. This is essential for cloud computing environments where multiple customers share the same infrastructure.
Internet service providers also use VLAN tagging to separate customer traffic and manage large-scale broadband networks efficiently.
Network Design Considerations
When implementing 802.1Q tagging, proper network design is critical. Administrators must carefully plan VLAN IDs, trunk configurations, and routing between VLANs.
It is also important to maintain consistent VLAN configurations across all switches in the network. Any mismatch can result in communication failures or unintended traffic flow.
Security considerations should also be taken into account. Best practices include disabling unused VLANs, avoiding the use of VLAN 1 for sensitive traffic, and securing trunk ports to prevent unauthorized access.
Troubleshooting VLAN Tagging Issues
Common issues in 802.1Q networks often arise from misconfigured trunk ports or VLAN mismatches. Symptoms may include devices being unable to communicate, or traffic being sent to incorrect VLANs.
Troubleshooting typically involves checking VLAN assignments, verifying trunk configurations, and ensuring that both ends of a trunk link are configured consistently.
Network monitoring tools can also help identify VLAN-related issues by analyzing traffic patterns and detecting anomalies in frame tagging.
Best Practices for 802.1Q Implementation
To ensure a stable and secure VLAN environment, several best practices should be followed. These include documenting VLAN assignments, using clear naming conventions, and regularly auditing network configurations.
It is also recommended to limit the number of VLANs carried over trunk links to only those that are necessary. This reduces complexity and improves security.
Additionally, enabling security features such as port security and VLAN pruning can help protect the network from unauthorized access and unnecessary traffic.
802.1Q port tagging is a critical technology that enables modern network segmentation and efficient use of infrastructure. By allowing multiple VLANs to operate over a single physical network, it provides flexibility, scalability, and improved security.
Although it introduces some complexity in network design and management, its benefits far outweigh the challenges. With proper configuration and best practices, 802.1Q tagging forms the backbone of efficient and secure enterprise networking environments.
Advanced Structure of 802.1Q VLAN Tag
The 802.1Q VLAN tag is inserted into the Ethernet frame between the source MAC address and the EtherType/length field. This tag is exactly 4 bytes long and contains multiple important components that define how the frame should be processed within a VLAN-aware network.
The first part of the tag is the Tag Protocol Identifier (TPID), which is a fixed value used to indicate that the frame is VLAN-tagged. The second part is the Tag Control Information (TCI), which contains further details such as priority, drop eligibility, and VLAN identifier. This structured approach ensures that switches can quickly interpret and process VLAN information without affecting the core Ethernet frame structure.
Tag Protocol Identifier and Its Role
The Tag Protocol Identifier is a 16-bit field that signals the presence of an 802.1Q tag. It typically uses a standardized value recognized by networking devices to distinguish tagged frames from untagged ones.
When a switch receives a frame, it first checks this field to determine whether VLAN processing is required. If the TPID is present, the switch immediately knows that the frame belongs to a VLAN-aware environment and must be processed accordingly. This mechanism ensures compatibility between legacy Ethernet devices and modern VLAN-capable networks.
Tag Control Information Breakdown
The Tag Control Information field is another 16-bit section that carries three main pieces of information. The first is the Priority Code Point, which defines the quality of service level for the frame. This allows network administrators to prioritize certain types of traffic, such as voice or video, over less critical data.
The second part is the Drop Eligible Indicator, which marks frames that can be discarded in case of network congestion. This helps manage traffic more efficiently during high load conditions.
The third and most important part is the VLAN Identifier, which specifies the exact VLAN to which the frame belongs. This identifier is the key element that enables traffic segmentation within a shared infrastructure.
Quality of Service and Traffic Prioritization
802.1Q tagging also plays an important role in Quality of Service implementation. By using the priority bits in the VLAN tag, network devices can classify traffic into different priority levels.
For example, voice traffic in VoIP systems can be given higher priority compared to regular file transfers. This ensures that time-sensitive applications experience minimal delay and packet loss.
QoS mechanisms work closely with VLAN tagging to ensure that critical applications maintain performance even under heavy network usage conditions. This integration is essential in modern enterprise and cloud environments.
Inter-VLAN Routing Concept
Although VLANs provide logical separation, communication between different VLANs requires a process known as inter-VLAN routing. This is typically handled by a Layer 3 device such as a router or a multilayer switch.
When a device in one VLAN needs to communicate with a device in another VLAN, the frame is sent to a routing device. The router then removes the VLAN tag, determines the destination VLAN, and forwards the packet accordingly after re-encapsulating it with the appropriate VLAN tag.
This process ensures that VLANs remain isolated by default while still allowing controlled communication when necessary.
Security Implications of VLAN Tagging
While VLANs improve security by isolating traffic, improper configuration of 802.1Q tagging can introduce vulnerabilities. One common risk is VLAN hopping, where an attacker attempts to send traffic into unauthorized VLANs.
This can occur if trunk ports are misconfigured or if native VLAN settings are not properly secured. Attackers may exploit these weaknesses to gain access to restricted network segments.
To prevent such issues, network administrators must enforce strict trunk configurations, disable unused ports, and avoid using default VLAN settings for sensitive traffic.
VLAN Hopping Attacks and Prevention
VLAN hopping attacks generally occur in two ways: switch spoofing and double tagging. In switch spoofing, an attacker pretends to be a switch and negotiates a trunk link, gaining access to multiple VLANs.
In double tagging attacks, malicious frames are crafted with multiple VLAN tags, allowing them to bypass standard filtering mechanisms.
Preventing these attacks requires proper security practices such as disabling dynamic trunking protocols, explicitly defining trunk ports, and configuring native VLANs that are not used for sensitive data.
Spanning Tree Protocol Interaction with VLANs
The Spanning Tree Protocol is used to prevent loops in Ethernet networks. When VLANs are introduced, each VLAN can have its own instance of the spanning tree, depending on the network design.
802.1Q tagging ensures that spanning tree information is correctly maintained across trunk links. This allows each VLAN to maintain a loop-free topology independently while still sharing physical infrastructure.
Proper integration between VLAN tagging and spanning tree operation is essential for maintaining network stability.
Encapsulation and De-encapsulation Process
When a frame enters a VLAN-aware switch, the encapsulation process begins. The switch determines the VLAN membership of the incoming port and adds the appropriate 802.1Q tag if the frame is being forwarded over a trunk link.
As the frame travels through the network, each switch reads the VLAN tag to make forwarding decisions. When the frame reaches its destination access port, the de-encapsulation process removes the VLAN tag before delivering the frame to the end device.
This ensures that end devices remain unaware of VLAN structures, simplifying endpoint configuration.
Performance Considerations in VLAN Networks
Although VLAN tagging introduces minimal overhead, large-scale networks must still consider performance impacts. Each switch must process VLAN tags for every frame, which can increase CPU usage in heavily loaded environments.
Efficient switch hardware is designed to handle this processing at wire speed, ensuring that performance is not significantly affected. However, poor network design or excessive VLAN segmentation can still lead to inefficiencies.
Proper planning of VLAN distribution and trunk usage helps maintain optimal performance across the network.
Scalability in Enterprise Networks
One of the strongest advantages of 802.1Q VLAN tagging is its ability to support scalable network designs. Organizations can expand their network by adding new VLANs without changing the physical layout.
This flexibility is particularly important in cloud environments and large enterprises where departments, services, and applications continuously evolve.
By using VLAN tagging, administrators can isolate new services quickly while maintaining centralized control over the network infrastructure.
Real-World Enterprise Deployment
In real-world enterprise networks, 802.1Q tagging is commonly used to separate user traffic, management traffic, voice traffic, and guest access networks.
For example, employees may be assigned to a corporate VLAN, while visitors connect to a guest VLAN with restricted internet-only access. Voice systems such as IP telephony are often placed in dedicated VLANs to ensure high-quality communication.
This structured approach improves both security and performance across the entire organization.
Data Center Virtualization and VLAN Usage
In modern data centers, virtualization technologies rely heavily on VLAN tagging. Virtual machines running on the same physical server can belong to different VLANs, allowing secure isolation between tenants.
This is essential for cloud service providers who host multiple customers on shared infrastructure. VLAN tagging ensures that each customer’s traffic remains separate, even when using the same physical hardware.
It also allows dynamic provisioning of network resources as virtual environments scale up or down.
Network Design Challenges with VLANs
Despite its advantages, VLAN design requires careful planning. Poorly structured VLAN architectures can lead to complexity, difficulty in troubleshooting, and increased risk of misconfiguration.
One common challenge is VLAN sprawl, where too many VLANs are created without proper documentation or organization. This can make network management difficult and increase the chance of errors.
Another challenge is maintaining consistency across multiple switches and locations, especially in large distributed networks.
Troubleshooting VLAN Tagging Issues in Depth
When VLAN-related problems occur, they often manifest as connectivity issues between devices that should otherwise communicate.
Troubleshooting involves verifying VLAN assignments on access ports, checking trunk configurations, and ensuring that VLANs are allowed across trunk links.
It is also important to verify that native VLAN settings match on both ends of a trunk connection, as mismatches can cause unexpected traffic behavior.
Advanced troubleshooting may involve analyzing packet captures to inspect VLAN tags directly and identify where issues are occurring.
Best Practices for Large-Scale VLAN Deployment
In large networks, best practices become critical for maintaining stability and security. Administrators should follow a structured VLAN numbering scheme and maintain clear documentation of VLAN purposes.
Unused VLANs should be disabled or removed to reduce security risks. Trunk links should be configured to carry only necessary VLANs, minimizing unnecessary traffic exposure.
Regular audits and monitoring help ensure that VLAN configurations remain consistent and secure over time.
Advanced VLAN Tagging Concepts
802.1Q port tagging is a foundational technology that enables modern network segmentation, security, and scalability. Its structured approach to embedding VLAN information into Ethernet frames allows multiple logical networks to coexist efficiently over shared physical infrastructure.
Through its support for QoS, inter-VLAN routing, security mechanisms, and large-scale virtualization, 802.1Q remains essential in enterprise and data center environments.
Proper understanding and implementation of VLAN tagging principles ensure that networks remain efficient, secure, and capable of supporting evolving digital demands.
802.1Q in Large-Scale Carrier and ISP Networks
In large-scale carrier and Internet Service Provider environments, 802.1Q tagging is a core mechanism for traffic separation across massive infrastructures. These networks handle thousands or even millions of users, making logical segmentation essential for scalability and control. VLAN tagging allows service providers to deliver multiple customer services over a shared backbone while keeping traffic isolated.
In such environments, VLANs are often used to separate residential, business, voice, and managed services. Each service type is assigned to a different VLAN, enabling strict control over traffic flow. This ensures that high-priority services such as voice or enterprise connectivity are not impacted by lower-priority residential traffic.
Role of 802.1Q in Multi-Tenant Environments
Multi-tenant architectures, commonly used in cloud platforms and hosting environments, depend heavily on VLAN tagging for isolation. Each tenant is assigned one or more VLANs that act as a secure boundary within shared infrastructure.
This approach ensures that one tenant cannot access or interfere with another tenant’s data, even though they may be running on the same physical servers and switches. VLAN tagging provides the logical separation required to maintain security and privacy in shared systems.
In combination with virtualization technologies, VLANs help create isolated virtual networks that behave like independent physical networks.
Integration with Network Virtualization Technologies
While 802.1Q VLAN tagging is effective, modern networks often combine it with advanced virtualization techniques such as VXLAN and NVGRE. These technologies extend VLAN concepts beyond traditional limits, especially in large cloud data centers.
VXLAN, for example, encapsulates Layer 2 frames inside Layer 3 packets, allowing networks to scale far beyond the 4096 VLAN limit. However, 802.1Q remains essential at the access layer, where devices initially connect to the network.
In many designs, VLANs act as the foundation, while overlay technologies expand scalability across distributed environments.
Traffic Engineering Using VLAN Segmentation
Network engineers use VLANs not only for separation but also for traffic engineering. By strategically assigning VLANs to different types of applications, administrators can control how traffic flows through the network.
For example, storage traffic, backup traffic, and user data traffic can each be assigned to separate VLANs. This prevents congestion and ensures predictable performance for critical applications.
Traffic engineering with VLANs also allows easier monitoring and troubleshooting, as each VLAN represents a distinct traffic category.
802.1Q and Network Redundancy Design
Redundancy is a key requirement in modern networks, and VLAN tagging plays an important role in redundant topologies. Multiple trunk links can carry the same VLANs between switches, ensuring that a failure in one link does not disrupt connectivity.
Protocols like link aggregation often work alongside VLAN tagging to provide both redundancy and increased bandwidth. VLANs ensure that traffic remains properly segmented even when multiple physical paths are used.
Careful design is required to avoid loops and ensure consistent forwarding behavior across redundant links.
Load Balancing Across VLANs
In some network architectures, VLANs are used as a method of load distribution. Different VLANs may be assigned to different uplinks or paths within a network to balance traffic load.
This approach prevents congestion on a single link and ensures more efficient use of available bandwidth. Load balancing with VLANs is especially useful in environments with high traffic variability, such as enterprise campuses or data centers.
Switching devices can distribute VLAN traffic intelligently based on configuration policies.
Impact of VLAN Design on Network Latency
Although VLAN tagging itself does not significantly increase latency, poor VLAN design can indirectly affect network performance. Over-segmentation or inefficient routing between VLANs can introduce delays.
For example, if too much inter-VLAN routing is required, traffic must pass through Layer 3 devices more frequently, increasing processing time. Similarly, poorly optimized trunk links can create bottlenecks.
Proper VLAN planning helps minimize unnecessary routing and ensures that traffic flows along the most efficient paths.
802.1Q in Industrial and IoT Networks
In industrial environments and Internet of Things deployments, VLAN tagging is used to separate operational technology networks from corporate IT networks. This separation is critical for security and stability.
Industrial devices such as sensors, controllers, and monitoring systems are often placed in dedicated VLANs to prevent interference from general network traffic. This ensures that critical systems remain operational even during network congestion or external attacks.
IoT environments also benefit from VLAN segmentation to isolate large numbers of connected devices.
Security Hardening Through VLAN Architecture
A well-designed VLAN architecture significantly enhances network security. By isolating sensitive systems into separate VLANs, organizations reduce the attack surface available to potential threats.
For example, administrative systems can be placed in a restricted VLAN that is not accessible from general user networks. Similarly, guest networks can be isolated from internal resources entirely.
Security policies can then be applied at VLAN boundaries, enforcing strict access control rules between different segments.
Common Misconfigurations in VLAN Networks
Despite its benefits, VLAN implementation is often prone to misconfiguration. One common issue is inconsistent VLAN IDs across switches, which can lead to communication failures.
Another frequent problem is incorrect trunk configuration, where certain VLANs are not allowed on specific links. This results in partial connectivity or isolated devices.
Native VLAN mismatches are also a common source of network instability, causing unexpected traffic behavior or security vulnerabilities.
Monitoring and Visibility in VLAN Environments
Effective monitoring is essential in VLAN-based networks. Administrators must have visibility into how traffic flows across different VLANs to detect performance issues or security threats.
Network monitoring tools can track VLAN usage, bandwidth consumption, and error rates. This data helps identify bottlenecks and optimize network performance.
Deep packet inspection can also be used to analyze VLAN-tagged traffic for troubleshooting and security analysis.
Evolution of VLAN Technology
Since its introduction, 802.1Q has remained a stable and widely adopted standard. However, networking requirements have evolved significantly, leading to enhancements and complementary technologies.
Modern networks increasingly rely on automation, software-defined networking, and virtualization. While these technologies add complexity, VLAN tagging continues to serve as the foundational mechanism for traffic segmentation.
Its simplicity and compatibility ensure that it remains relevant even in highly advanced networking environments.
Software-Defined Networking and VLAN Control
In Software-Defined Networking environments, VLAN configuration is often centralized and automated. Instead of manually configuring switches, administrators define VLAN policies through a centralized controller.
This approach reduces configuration errors and improves scalability. VLAN tagging still occurs at the data plane level, but the control logic is managed dynamically.
SDN enhances the flexibility of VLAN-based networks by allowing real-time adjustments based on traffic conditions.
Hybrid Network Architectures
Many modern networks use hybrid architectures that combine traditional VLANs with overlay technologies. In such environments, 802.1Q operates at the edge, while overlays handle large-scale segmentation across data centers.
This hybrid approach allows organizations to maintain compatibility with existing infrastructure while adopting modern scalability solutions.
VLANs continue to serve as the entry point for traffic before it is encapsulated into more advanced transport mechanisms.
Performance Optimization Techniques
Optimizing VLAN performance involves careful planning of switch capacity, trunk utilization, and routing efficiency. Reducing unnecessary VLAN propagation across trunk links helps minimize overhead.
Additionally, grouping related VLANs and limiting broadcast domains improves overall efficiency. High-performance switches are often used in core networks to handle large volumes of VLAN-tagged traffic.
Proper hardware selection is essential to ensure that VLAN processing does not become a performance bottleneck.
Future of 802.1Q in Networking
Despite the emergence of newer technologies, 802.1Q is expected to remain a core networking standard for the foreseeable future. Its simplicity, reliability, and widespread adoption make it indispensable in both enterprise and service provider environments.
Future developments are likely to focus on better integration with automation systems, improved security features, and tighter integration with virtualization platforms.
However, the fundamental concept of VLAN tagging is unlikely to change, as it continues to provide an efficient method for logical network segmentation.
Advanced VLAN Concepts
802.1Q VLAN tagging remains one of the most important technologies in modern networking. It enables scalable, secure, and efficient communication across complex infrastructures by logically separating traffic over shared physical networks.
From enterprise environments to global service provider systems, VLAN tagging supports a wide range of applications including security segmentation, traffic engineering, virtualization, and performance optimization.
Even as networking technologies evolve, the principles of VLAN tagging continue to form the backbone of structured network design, ensuring that data flows efficiently and securely across interconnected systems.
802.1Q in Cloud-Native and Modern Hybrid Networks
In cloud-native architectures, 802.1Q VLAN tagging still plays an important foundational role, even though many higher-level abstraction technologies are used today. Cloud environments often rely on a combination of VLANs and overlay networks to achieve both physical and logical separation of traffic.
At the physical layer, VLAN tagging is used to segment traffic within data center switches before it is encapsulated into virtual networks. This ensures that workloads belonging to different tenants, applications, or environments remain isolated at the hardware level. Even in highly automated cloud platforms, VLANs provide the first layer of traffic organization and security enforcement.
Hybrid cloud systems, which combine on-premises infrastructure with public cloud services, also depend on VLANs for secure connectivity. VLAN tagging helps maintain consistent segmentation policies across different environments, ensuring that data flows remain controlled and predictable.
Automation and VLAN Management
Modern networks increasingly rely on automation tools to manage VLAN configurations at scale. Instead of manually configuring each switch, administrators use centralized systems that automatically assign VLANs based on predefined policies.
This automation reduces human error, improves deployment speed, and ensures consistency across large infrastructures. In dynamic environments where devices and services are constantly changing, automated VLAN assignment ensures that network segmentation remains accurate and up to date.
Network orchestration systems can also dynamically create or remove VLANs based on workload requirements, making networks more adaptive and efficient.
VLAN Role in Zero Trust Security Models
Zero Trust security frameworks assume that no device or user should be trusted by default, even if they are inside the network perimeter. In this model, VLANs play an important role in enforcing micro-segmentation.
By dividing the network into small, isolated VLANs, organizations can limit lateral movement between systems. Even if an attacker gains access to one VLAN, they cannot easily move to another without passing through security controls.
This layered segmentation approach strengthens overall security and reduces the impact of potential breaches.
Challenges in Scaling VLAN Architectures
As networks grow larger, managing VLANs becomes increasingly complex. One major challenge is maintaining consistent VLAN mapping across hundreds or thousands of switches.
Another issue is the risk of VLAN sprawl, where too many VLANs are created without proper governance. This leads to operational inefficiency and increases the likelihood of configuration errors.
Scalability limitations of traditional VLAN architecture, such as the 4096 VLAN ID limit, also become a concern in extremely large environments, prompting the use of overlay technologies alongside VLANs.
Troubleshooting Complex VLAN Environments
In large networks, troubleshooting VLAN-related issues requires a structured approach. Problems can arise at multiple layers, including physical connectivity, switch configuration, trunk negotiation, and routing.
Engineers often begin by verifying VLAN membership on access ports, followed by checking trunk configurations between switches. Packet captures are frequently used to inspect VLAN tags and confirm whether frames are being properly tagged and forwarded.
Advanced diagnostic tools help visualize VLAN topology and identify misconfigurations that may not be immediately obvious.
Impact of VLAN Design on Network Reliability
A well-designed VLAN architecture significantly improves network reliability. By isolating traffic into logical segments, failures in one VLAN are less likely to affect others.
Redundant trunk links and properly configured spanning tree protocols further enhance stability by preventing loops and ensuring continuous connectivity even during link failures.
However, poor VLAN design can have the opposite effect, introducing instability and making the network more difficult to maintain.
Operational Best Practices for VLAN Environments
Maintaining a stable VLAN environment requires consistent operational discipline. Clear documentation of VLAN usage is essential for long-term maintainability.
Administrators should regularly review VLAN configurations to ensure they align with current business requirements. Unused VLANs should be removed to reduce complexity and potential security risks.
Standardized naming conventions and configuration templates also help maintain consistency across large networks.
Performance Optimization in High-Traffic Networks
In high-traffic environments, VLAN efficiency depends on careful planning of switch capacity and trunk utilization. Overloading trunk links with unnecessary VLANs can reduce performance and increase latency.
Segmenting traffic logically and minimizing broadcast domains helps improve throughput and reduce congestion. High-performance switching hardware is often required in core network areas to handle large volumes of VLAN-tagged traffic efficiently.
Proper load distribution across network paths also contributes to optimal performance.
Interoperability with Legacy Systems
One of the strengths of 802.1Q is its ability to coexist with legacy Ethernet systems. Devices that do not support VLAN tagging can still operate within a VLAN environment using access ports.
This backward compatibility allows organizations to gradually upgrade their infrastructure without replacing all existing hardware at once. It also ensures smooth integration between older and newer network components.
However, careful configuration is required to prevent mismatches between tagged and untagged traffic.
Future Trends Affecting VLAN Technology
Although VLANs remain essential, networking is gradually shifting toward more advanced models such as intent-based networking and fully software-defined architectures. These systems abstract much of the manual VLAN configuration and automate network behavior based on business intent.
Despite this evolution, VLANs are expected to remain in use for many years because they are deeply embedded in existing infrastructure and continue to provide reliable Layer 2 segmentation.
Future improvements may focus on tighter integration between VLANs and automation platforms, improved security controls, and better scalability solutions.
Long-Term Relevance of 802.1Q
The long-term relevance of 802.1Q lies in its simplicity and universality. It is supported by virtually all modern switches and networking devices, making it a standard component of almost every enterprise network.
Even as new technologies emerge, VLAN tagging continues to serve as the basic building block for network segmentation. Its ability to logically separate traffic while using shared physical infrastructure ensures that it will remain a core part of networking design.
Conclusion
802.1Q port tagging is a foundational networking technology that enables efficient, secure, and scalable communication across modern networks. By allowing multiple VLANs to coexist on a single physical infrastructure, it provides essential traffic segmentation that supports enterprise, cloud, and service provider environments.
Throughout its structure, from VLAN tagging mechanisms to access and trunk port behavior, 802.1Q ensures that data is properly isolated and delivered to the correct destination. Its integration with QoS, security models, virtualization, and automation makes it highly versatile and widely applicable.
Although networking technologies continue to evolve toward more abstract and automated systems, 802.1Q remains a critical component of network architecture. Its reliability, compatibility, and simplicity ensure that it will continue to play a central role in network design for the foreseeable future.