SMTP is the foundational protocol responsible for sending emails across the internet. Every time an email is delivered from one mailbox to another, SMTP is involved in the background handling the transfer of messages between mail servers. However, SMTP does not operate on a single universal channel. Instead, it relies on different network ports to separate types of communication such as message submission from users and message relay between servers.
The reason multiple ports exist is to improve security, organize traffic flow, and control how emails are authenticated and transmitted. Over time, email systems evolved from open relay environments into strictly controlled and encrypted communication channels. This evolution is why understanding ports like 25 and 587 is essential when configuring email systems today.
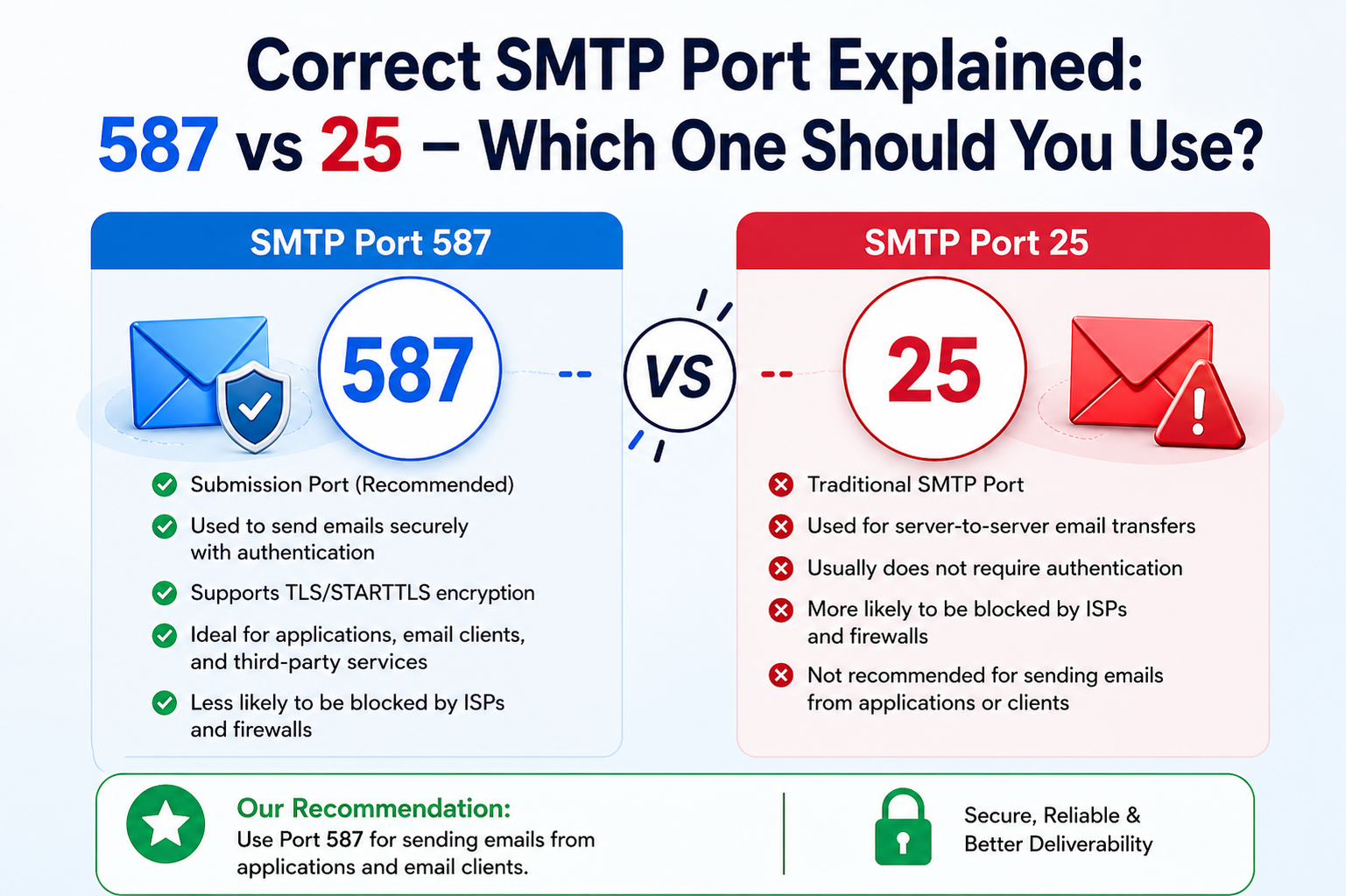
The Original Role of SMTP Port 25 in Email Infrastructure
Port 25 is historically the oldest SMTP port and was originally designed for direct communication between mail servers. In the early architecture of email systems, servers would freely exchange messages over this port without authentication. The internet was much smaller at that time, and security concerns were not as advanced as they are today.
In its intended design, port 25 functions as a relay channel where one mail server sends email to another mail server. For example, when an email is sent from one domain to another, the sending mail server connects to the receiving mail server using port 25 to deliver the message. This process is known as server-to-server communication.
However, because port 25 did not require authentication in its original form, it quickly became a target for abuse. Spammers exploited open relay configurations to send large volumes of unsolicited emails. As email security standards improved, restrictions were gradually introduced to limit how port 25 could be used, especially for end-user email submission.
Why Port 25 Is No Longer Suitable for Modern Email Sending
In modern email environments, port 25 is rarely used for client-side email submission. Many internet service providers actively block outbound traffic on this port to prevent spam and unauthorized email activity. This means that even if a user configures their email application to use port 25, messages may fail to send depending on network restrictions.
Another limitation is that port 25 does not enforce authentication by default. Without authentication, any system could potentially send email through a server, creating serious security risks. To combat this, email service providers have moved away from relying on port 25 for user-driven email sending.
Additionally, modern email standards require encryption to protect sensitive data. Port 25 does not inherently guarantee secure transmission, which makes it less suitable for today’s privacy and compliance requirements.
The Rise of Port 587 as the Standard for Email Submission
Port 587 was introduced to solve the limitations of port 25 by creating a dedicated channel for authenticated email submission. Unlike port 25, this port is specifically designed for users and applications that need to send emails securely through a mail server.
When an email client connects using port 587, it is required to authenticate using valid credentials such as a username and password. This ensures that only authorized users can send emails through the server. This authentication layer significantly reduces the risk of spam and unauthorized usage.
Another important feature of port 587 is its support for encryption through STARTTLS. This mechanism allows the connection to begin in an unencrypted state and then upgrade to a secure encrypted channel before any sensitive data is transmitted. This ensures that login credentials and email content are protected during transmission.
Because of these features, port 587 has become the default recommendation for most modern email systems, including business applications, websites, and email clients.
Difference Between Email Relay and Email Submission
To fully understand why port 25 and port 587 are different, it is important to distinguish between email relay and email submission.
Email relay refers to the process where one mail server sends emails to another mail server. This is typically done using port 25. It is part of the backend infrastructure of email delivery and does not involve direct user interaction.
Email submission, on the other hand, refers to the process where a user or application sends an email to a mail server for delivery. This is where port 587 plays a critical role. It acts as the entry point for outgoing emails from clients before they are relayed to their final destination.
By separating these two functions, email systems become more secure, organized, and resistant to abuse.
Authentication and Why It Matters in Modern SMTP
Authentication is one of the most important aspects of modern email communication. Without it, servers would be vulnerable to misuse, allowing unauthorized users to send emails freely.
Port 587 requires authentication before any email can be submitted. This means the email server verifies the identity of the sender before accepting messages. Once verified, the server allows the email to be processed and delivered to its destination.
This process helps ensure accountability. Every email sent through an authenticated connection can be traced back to a valid user or system. It also helps reduce spam, phishing attempts, and email spoofing.
Port 25, in contrast, was never designed with authentication as a core requirement, which is why it is no longer suitable for modern email submission tasks.
Encryption and Secure Transmission Using STARTTLS
Security is another major reason why port 587 is preferred over port 25. Email messages often contain sensitive information, including personal data, business communications, and login credentials. Without encryption, this data could be intercepted during transmission.
Port 587 supports STARTTLS, which is a protocol extension that upgrades an insecure connection into a secure encrypted one. When an email client connects to the server, it first establishes a basic connection. After that, STARTTLS is initiated to encrypt the communication channel.
This ensures that all subsequent data exchanged between the client and server is protected from interception or tampering. It is one of the most widely adopted encryption methods in modern SMTP systems.
Port 25 may support encryption in some configurations, but it is not consistently enforced, making it less reliable for secure communication.
Common Problems When Using Port 25
One of the most common issues users face when using port 25 is email delivery failure. Many networks block this port by default, especially residential and commercial internet providers. This is done to prevent spam originating from compromised systems.
Another issue is inconsistent behavior across different hosting environments. Some servers may allow port 25 usage internally but block external access, leading to confusion during configuration.
Even when port 25 is available, emails sent through it are more likely to be flagged as suspicious by receiving servers due to the lack of authentication and encryption enforcement.
Why Port 587 Improves Email Deliverability
Email deliverability refers to the ability of an email to successfully reach the recipient’s inbox instead of being rejected or marked as spam. Port 587 plays a key role in improving deliverability because it enforces authentication and encryption.
When emails are sent through an authenticated connection, receiving mail servers can verify that the message comes from a legitimate source. This reduces the chances of the email being flagged as spam.
In addition, many email providers prioritize or trust messages sent through properly authenticated submission channels. This makes port 587 a more reliable choice for businesses, applications, and professional communication systems.
Role of Email Clients and Applications
Email clients such as desktop mail applications, mobile email apps, and automated systems all rely on SMTP ports to send messages. When configured correctly, these clients use port 587 to submit outgoing emails securely.
For example, when a user sends an email from an application, the message is first submitted to the mail server using port 587. The server then processes the message and uses server-to-server communication to deliver it to the recipient.
This separation of responsibilities ensures that email submission and delivery are handled efficiently and securely.
Server Configuration and Best Practices
When setting up an email server or configuring an email service, choosing the correct SMTP port is essential for performance and security. Port 587 should always be configured for client submission because it supports authentication and encryption by default.
Administrators should also ensure that proper authentication mechanisms are in place, such as username-password verification and secure token-based access where applicable. This further strengthens the security of the email system.
It is also important to monitor server logs and email traffic to detect any unusual activity that may indicate abuse or misconfiguration.
Troubleshooting SMTP Port Issues
When email sending fails, one of the first things to check is the SMTP port configuration. If port 25 is being used, switching to port 587 often resolves the issue immediately.
Other common problems include incorrect authentication credentials, disabled STARTTLS support, or firewall restrictions blocking outgoing connections. Ensuring that port 587 is open and properly configured usually resolves most email sending issues.
Testing email delivery after configuration changes is also important to confirm that messages are being transmitted securely and successfully.
Why Port 587 Is the Recommended Standard Today
The modern email ecosystem is built around security, authentication, and reliability. Port 587 aligns perfectly with these requirements by providing a secure and authenticated method for email submission.
It reduces spam, improves deliverability, supports encryption, and ensures compliance with modern email standards. As a result, it has become the globally accepted standard for sending emails from clients and applications.
Port 25 still exists for legacy server-to-server communication, but it is no longer suitable for general email sending purposes. Using port 587 ensures that email systems operate efficiently, securely, and in line with current internet best practices.
SMTP Security Evolution and the Shift Toward Encrypted Communication
As email usage expanded globally, security concerns became increasingly important. Early SMTP systems were designed for simplicity and open communication, but they lacked strong protections against interception, impersonation, and abuse. This led to a gradual evolution in how SMTP ports are used and secured.
Modern email systems are no longer just about sending messages from one point to another. They now involve strict verification, encryption, and policy enforcement at multiple levels. This transformation is one of the main reasons port 587 became the preferred standard, as it aligns with modern security expectations.
Encryption and authentication are no longer optional in most environments. They are required to ensure that email data remains confidential and that only legitimate users can send messages through a server. This shift has significantly reduced spam and improved trust in email communication overall.
Understanding STARTTLS and How It Secures SMTP Connections
STARTTLS is a critical mechanism in modern SMTP communication. It allows an initially unencrypted connection to be upgraded into an encrypted one using Transport Layer Security. This ensures that sensitive information such as login credentials and message content is protected during transmission.
When a client connects to an SMTP server using port 587, the communication typically begins in plain text. However, before any authentication or message transfer occurs, the STARTTLS command is issued. This triggers the encryption process, converting the connection into a secure channel.
Once encryption is active, all subsequent communication is protected from interception. This includes usernames, passwords, email content, and any attachments being sent. Without this layer of protection, email data could potentially be exposed to network attackers or unauthorized monitoring.
STARTTLS is widely supported and has become the standard encryption method for SMTP submission. It provides flexibility while maintaining compatibility with older systems that may not support fully encrypted connections from the start.
Port 465 and Its Role in Encrypted SMTP Communication
In addition to ports 25 and 587, another port often mentioned in SMTP configuration is port 465. This port was originally introduced for SMTP over SSL, which provides encryption from the very beginning of the connection.
Unlike STARTTLS, which upgrades a plain connection, SSL-based SMTP on port 465 encrypts the connection immediately upon establishment. This means there is no unencrypted phase, making it inherently secure from the start.
However, port 465 was initially deprecated in favor of STARTTLS on port 587. Later, it was reintroduced as an official submission port due to continued demand for implicit encryption methods. Today, both port 465 and port 587 are considered valid, but port 587 remains more widely recommended due to its flexibility and compatibility.
The choice between these ports often depends on server configuration and organizational security policies. Some systems prefer port 465 for strict SSL enforcement, while others rely on port 587 for STARTTLS-based encryption.
Why Port 587 Became the Global Standard for Email Submission
The adoption of port 587 as the primary email submission port is the result of several practical and security-driven decisions. One of the most important reasons is its ability to separate user authentication from server-to-server communication.
By design, port 587 ensures that only authenticated users can submit emails. This prevents unauthorized access and reduces the risk of email abuse. It also allows email service providers to enforce strict identity verification policies.
Another reason for its popularity is its compatibility with modern encryption standards. STARTTLS support ensures that communication can be securely upgraded without requiring a completely separate secure port from the beginning.
Port 587 also avoids many of the network restrictions commonly applied to port 25. Since it is not used for direct mail relay between servers, it is less likely to be blocked by ISPs or firewalls. This improves reliability and ensures consistent email delivery across different environments.
Common Misconfigurations in SMTP Port Setup
One of the most frequent issues in email system configuration is selecting the wrong SMTP port. Many users mistakenly attempt to use port 25 for client-side email sending, which often results in failed delivery or blocked connections.
Another common mistake is using port 587 without enabling authentication. Since this port is designed specifically for authenticated submission, disabling login requirements can lead to rejection by the mail server.
Incorrect encryption settings also cause problems. For example, attempting to use STARTTLS on a server that only supports SSL, or vice versa, can prevent successful email transmission. Proper alignment between port selection and encryption method is essential for stable operation.
Firewall restrictions can also interfere with SMTP communication. If outgoing traffic on port 587 is blocked, email sending will fail even if all other settings are correct. Ensuring that network configurations allow SMTP traffic is an important part of troubleshooting.
Email Deliverability and How SMTP Ports Influence Inbox Placement
Email deliverability is a critical factor for businesses, developers, and organizations that rely on email communication. It determines whether an email reaches the recipient’s inbox or gets filtered into spam or rejected entirely.
Using the correct SMTP port plays an important role in improving deliverability. Emails sent through authenticated and encrypted channels are more likely to be trusted by receiving mail servers. Port 587, in particular, signals that the message was submitted securely and legitimately.
Receiving servers evaluate multiple factors when deciding whether to accept an email. These include sender reputation, authentication status, and encryption methods. Proper use of port 587 helps strengthen all of these signals.
In contrast, emails sent through insecure or unauthenticated channels are more likely to be flagged as suspicious. This can negatively impact business communication, marketing campaigns, and automated notifications.
Enterprise Email Systems and Port Configuration Strategies
Large organizations often operate complex email infrastructures involving multiple servers, gateways, and security layers. In these environments, proper SMTP port configuration is essential for maintaining stability and compliance.
Port 587 is typically used for all internal and external email submission from clients and applications. This ensures that all outgoing messages pass through a controlled and authenticated gateway.
Server-to-server communication may still rely on port 25 within internal networks, but external exposure is usually restricted. This layered approach helps organizations maintain control over email traffic while reducing security risks.
Some enterprises also implement additional security measures such as IP whitelisting, rate limiting, and advanced spam filtering. These systems work alongside SMTP ports to create a secure and efficient email ecosystem.
Firewall Rules and Network-Level Restrictions
Firewalls play a significant role in controlling SMTP traffic. Many networks block port 25 by default to prevent unauthorized email relay activity. This is a common security practice across residential and corporate environments.
Port 587 is usually allowed because it is intended for authenticated submission. However, in some restricted environments, even this port may be filtered or monitored to ensure compliance with organizational policies.
Proper firewall configuration is essential for uninterrupted email service. Administrators must ensure that required ports are open and that traffic is correctly routed to the mail server.
Network-level restrictions can sometimes cause confusion when email services fail unexpectedly. In many cases, the issue is not related to SMTP configuration itself but rather to blocked or filtered traffic at the network level.
Common Misconceptions About SMTP Ports
There are several misconceptions surrounding SMTP ports that often lead to incorrect configuration. One common belief is that port 25 is required for all email sending, which is not true in modern systems.
Another misconception is that port 587 and port 465 are interchangeable in all cases. While both support secure email submission, they operate using different encryption methods and may not be compatible with every server configuration.
Some users also assume that changing the SMTP port alone can solve deliverability issues. In reality, email reputation, authentication records, and server configuration all play a role in successful delivery.
Understanding the purpose of each SMTP port helps avoid these misunderstandings and ensures more reliable email system setup.
Troubleshooting SMTP Connection Failures
When email sending fails, diagnosing the issue requires checking multiple components. The first step is verifying that the correct SMTP port is being used based on the server’s requirements.
If port 587 is configured but emails are not sending, authentication settings should be checked. Incorrect credentials are a common cause of failure. Ensuring that username and password details are accurate can often resolve the issue.
Next, encryption settings should be reviewed. STARTTLS must be enabled if required by the server. Mismatched encryption protocols can prevent successful communication.
Network connectivity should also be tested. If the port is blocked by a firewall or ISP, the connection will fail regardless of configuration accuracy. Switching networks or adjusting firewall rules may be necessary in such cases.
Future of SMTP and Evolving Email Standards
Email technology continues to evolve with increasing focus on security, privacy, and automation. While SMTP remains the core protocol for email delivery, its usage is becoming more tightly controlled and standardized.
Ports like 587 are expected to remain central to email submission due to their balance of security and compatibility. However, future developments may introduce stronger encryption requirements and more advanced authentication methods.
There is also growing adoption of technologies such as domain-based authentication systems and email verification frameworks. These enhancements work alongside SMTP to further reduce spam and improve trust in email communication.
Despite these advancements, the fundamental role of SMTP ports will remain essential for ensuring structured and reliable email transmission across the internet.
Advanced SMTP Authentication Methods and Modern Security Layers
Modern email systems rely on more than just a username and password for authentication. While basic credentials are still widely used, advanced authentication mechanisms have been introduced to strengthen security and prevent unauthorized access.
One of the most common enhancements is multi-factor authentication, which requires an additional verification step beyond the password. This may include a time-based code, a mobile approval prompt, or a hardware token. When combined with SMTP submission on port 587, it significantly reduces the risk of account compromise.
Another important layer is application-specific passwords. Many email providers allow users to generate unique passwords for SMTP access, especially when two-factor authentication is enabled. This ensures that even if one password is exposed, the main account remains protected.
Token-based authentication is also becoming more common in enterprise environments. Instead of sending a static password, systems generate temporary access tokens that expire after a short period. This reduces the risk of long-term credential exposure during SMTP sessions.
SMTP Submission Workflow in Modern Email Systems
The process of sending an email today involves several structured steps designed to ensure security and reliability. When an email is submitted using port 587, the client first establishes a connection with the mail server.
After the connection is initiated, the server responds with a greeting message and capability list. The client then initiates encryption using STARTTLS, upgrading the connection into a secure channel before any sensitive data is exchanged.
Once the secure channel is established, the client proceeds with authentication. Credentials are verified against the server’s user database or authentication service. Only after successful verification is the email submission process allowed to continue.
The email is then transmitted to the server, which performs additional validation checks. These may include spam filtering, virus scanning, and policy enforcement. If the message passes all checks, it is queued for delivery.
Finally, the mail server uses server-to-server communication, often via port 25 internally, to deliver the message to the recipient’s mail server. This layered process ensures both security and proper routing.
Role of Mail Transfer Agents in SMTP Communication
Mail Transfer Agents (MTAs) are responsible for handling the routing and delivery of email messages between servers. They act as intermediaries that ensure emails reach their intended destinations.
When an email is submitted through port 587, it is first received by the MTA on the sending server. The MTA then determines the destination domain and initiates a connection to the recipient’s mail server.
If the destination server is external, the MTA typically uses port 25 for server-to-server communication. This separation between submission and relay is an important architectural feature of modern email systems.
MTAs also handle retry mechanisms in case of temporary delivery failures. If the recipient server is unavailable, the message is stored and retried after a defined interval. This ensures reliable delivery even under unstable network conditions.
SMTP Relay Restrictions and Anti-Spam Policies
To prevent abuse, modern email systems implement strict relay restrictions. Open relays, where any user can send email through a server without authentication, are no longer allowed in most environments.
Port 587 plays a key role in enforcing these restrictions by requiring authentication before allowing message submission. This ensures that only verified users can send emails through the server.
Anti-spam policies also include rate limiting, content filtering, and reputation monitoring. These systems analyze outgoing email patterns to detect suspicious behavior such as bulk sending or unusual traffic spikes.
Servers that violate these policies may be temporarily or permanently blocked from sending emails. This helps maintain the integrity of global email networks and reduces spam distribution.
Importance of SPF, DKIM, and DMARC in Email Authentication
In addition to SMTP authentication, modern email systems rely on domain-level verification mechanisms to ensure message authenticity. These include SPF, DKIM, and DMARC records.
SPF (Sender Policy Framework) allows domain owners to specify which servers are authorized to send emails on their behalf. This helps prevent spoofing by verifying the sending server’s IP address.
DKIM (DomainKeys Identified Mail) adds a digital signature to outgoing emails. This signature is verified by the receiving server to ensure that the message has not been altered during transmission.
DMARC (Domain-based Message Authentication, Reporting, and Conformance) builds on SPF and DKIM by defining policies for handling failed authentication checks. It also provides reporting mechanisms to monitor email abuse.
While these systems operate independently of SMTP ports, they work closely with submission processes over port 587 to improve email trust and deliverability.
Performance Considerations in SMTP Port Usage
Although SMTP is not typically a high-bandwidth protocol, performance still matters in large-scale email systems. Port selection can influence connection reliability, latency, and server load.
Port 587 is optimized for client submission and is generally lightweight in terms of processing overhead. Because it requires authentication and encryption, it may introduce slight delays during connection setup, but this trade-off improves security significantly.
Port 25, while faster in some cases due to lack of authentication overhead, is not suitable for client use due to restrictions and security limitations. Any performance advantage is outweighed by reliability issues.
In high-volume environments, email systems are often optimized using connection pooling, load balancing, and distributed mail servers to handle large amounts of traffic efficiently.
Email APIs vs Traditional SMTP Submission
Modern applications often use email APIs instead of traditional SMTP configurations. These APIs provide programmatic access to email sending functions without requiring direct SMTP port management.
However, many systems still rely on SMTP internally, often using port 587 for compatibility and fallback purposes. APIs typically abstract the underlying SMTP communication, making it easier for developers to send emails without handling low-level protocol details.
Despite the rise of APIs, SMTP remains a foundational protocol. It ensures compatibility across different systems and continues to serve as the backbone of email communication worldwide.
Common Real-World Scenarios Using Port 587
Port 587 is widely used in various real-world applications. Websites use it to send contact form submissions, password reset emails, and notification messages. Business applications rely on it for transactional emails such as invoices and alerts.
Email marketing platforms also use port 587 to submit messages before distributing them through their infrastructure. This ensures that all outgoing emails are properly authenticated and compliant with security standards.
Even automated systems such as monitoring tools, IoT devices, and server alerts often use SMTP submission over port 587 to communicate status updates and critical notifications.
Impact of ISP Policies on SMTP Port Behavior
Internet Service Providers play a significant role in how SMTP ports function for end users. Many ISPs block port 25 to prevent spam originating from infected devices or poorly configured systems.
Port 587 is generally left open because it is designed for authenticated use. However, some restrictive networks may still impose limitations on SMTP traffic depending on usage patterns or security policies.
These ISP-level restrictions are one of the main reasons why modern email systems rely heavily on port 587. It provides a consistent and reliable way to send emails across different network environments.
Email Logging and Monitoring in SMTP Systems
Monitoring SMTP activity is essential for maintaining system health and security. Email servers typically log all submission attempts, authentication events, and delivery outcomes.
These logs help administrators detect issues such as failed logins, suspicious activity, or delivery bottlenecks. They also provide valuable insights into email performance and user behavior.
In environments using port 587, logs are particularly important because they record authenticated sessions. This helps trace email activity back to specific users or applications, improving accountability.
Advanced monitoring systems may also generate alerts when unusual patterns are detected, such as repeated failed authentication attempts or sudden spikes in email volume.
Scalability Challenges in High-Volume Email Systems
As organizations grow, email systems must handle increasing volumes of traffic without compromising performance or reliability. Scaling SMTP infrastructure involves both hardware and software optimization.
Load balancing is often used to distribute email submission requests across multiple servers. This ensures that no single server becomes overwhelmed by traffic.
Queue management is another important aspect. Emails that cannot be immediately delivered are stored in queues and processed in an orderly manner. Efficient queue handling ensures smooth delivery even during peak loads.
Port 587 remains central in these systems because it provides a standardized and secure entry point for all email submissions, making it easier to scale infrastructure consistently.
Long-Term Outlook of SMTP and Email Communication
Despite the emergence of modern messaging platforms, email remains one of the most widely used communication methods globally. SMTP continues to evolve to meet changing security and performance requirements.
Port 587 is expected to remain the primary submission channel for the foreseeable future due to its balance of security, compatibility, and ease of use. It supports modern encryption standards and integrates well with authentication systems.
Future developments may introduce stronger encryption defaults, improved identity verification, and deeper integration with cloud-based email services. However, the core principles of SMTP communication are likely to remain unchanged.
Email systems will continue to rely on structured protocols, authenticated access, and secure transmission channels to ensure reliable global communication.
Advanced Troubleshooting of SMTP Port and Connection Issues
Even with correct configuration, SMTP systems can sometimes fail due to hidden technical issues. One of the most common problems is DNS misconfiguration. If the mail server’s domain records are not properly set, email clients may fail to locate the correct server even when port 587 is correctly configured.
Another frequent issue is incorrect TLS negotiation. Some servers require STARTTLS explicitly, while others may reject insecure handshakes entirely. If the client attempts to upgrade encryption at the wrong time or in an unsupported way, the connection may fail silently or return authentication errors.
Certificate validation problems can also disrupt SMTP communication. When a server’s SSL/TLS certificate is expired, self-signed without proper trust, or mismatched with the domain name, secure connections over port 587 may be rejected by the client.
In many real-world cases, troubleshooting involves testing connectivity at multiple levels. This includes verifying network access to the port, confirming authentication success, and checking server logs for detailed error messages that explain why the connection failed.
Role of Reverse DNS and Email Reputation in Delivery Success
Reverse DNS, also known as PTR records, plays an important role in email deliverability. When a mail server sends an email, receiving servers often check whether the sending IP address matches a valid domain name through reverse DNS lookup.
If reverse DNS is missing or incorrectly configured, emails may be flagged as suspicious or rejected entirely. This is especially important in server-to-server communication that occurs after submission through port 587.
Email reputation is another critical factor. Each sending server builds a reputation score based on its historical behavior. Factors such as spam complaints, bounce rates, and authentication failures influence this score.
Using authenticated submission through port 587 helps improve reputation because it ensures that emails originate from verified users. Over time, consistent and legitimate usage strengthens trust with receiving servers.
Impact of Cloud-Based Email Services on SMTP Usage
Cloud-based email services have transformed how SMTP is used in modern systems. Instead of managing complex mail servers manually, many organizations now rely on managed email platforms that handle SMTP infrastructure internally.
Even though these services simplify email management, SMTP remains the underlying protocol. Port 587 is still commonly used as the submission interface, even when the backend is fully managed by the cloud provider.
These platforms often provide additional features such as analytics, bounce tracking, and automated deliverability optimization. However, they still rely on SMTP principles for message transmission and routing.
This hybrid approach allows users to benefit from SMTP’s reliability while avoiding the complexity of maintaining their own email infrastructure.
Security Threats Targeting SMTP Systems
SMTP systems are frequent targets of cyberattacks due to their critical role in communication. One common threat is credential stuffing, where attackers attempt to use leaked passwords to gain access to email accounts.
Another threat is email spoofing, where attackers forge sender addresses to impersonate legitimate users. Without proper authentication mechanisms, this can lead to phishing attacks and data breaches.
Man-in-the-middle attacks are also a concern, especially if encryption is not properly enforced. Attackers can intercept unencrypted SMTP traffic and potentially capture sensitive information.
Using port 587 with enforced authentication and STARTTLS significantly reduces these risks by ensuring that both identity verification and encryption are mandatory during email submission.
Comparison of SMTP Ports in Real-World Usage
In practical environments, each SMTP port serves a distinct purpose. Port 25 is primarily used for server-to-server communication and is often restricted for end users due to security concerns.
Port 587 is the standard for authenticated email submission and is widely used across applications, email clients, and automated systems. It provides secure and reliable communication with encryption and authentication built in.
Port 465 is used in some systems for implicit SSL encryption, offering immediate secure connections without upgrading from plain text. However, its usage depends on server compatibility and configuration preferences.
Among these, port 587 is the most universally supported and recommended option for modern email systems due to its balance of flexibility and security.
Email Queue Processing and Delivery Reliability
When an email is submitted through SMTP, it does not always get delivered instantly. Instead, it enters a queue within the mail server. This queue system ensures that messages are processed in an organized and reliable manner.
If the recipient server is unavailable, the message remains in the queue and is retried periodically. This retry mechanism can continue for hours or even days depending on server configuration.
Queue processing also allows servers to manage high traffic efficiently. During peak usage periods, emails are temporarily stored and gradually delivered without overwhelming the system.
Port 587 plays an important role in this process by acting as the entry point for queued messages originating from authenticated users.
Scenarios Where Port 25 Is Still Used Today
Although port 25 is no longer recommended for client use, it still serves an important role in backend email infrastructure. One of its primary uses is server-to-server mail exchange between different domains.
It is also used internally within organizations where mail servers communicate with each other in controlled environments. In such cases, authentication may not be required because the network is trusted.
Some legacy systems still rely on port 25 due to older configurations that have not been updated. However, most modern systems are gradually migrating away from it in favor of more secure alternatives.
Despite its limited role, port 25 remains part of the global email ecosystem due to backward compatibility requirements.
Why Proper SMTP Configuration Is Critical for Businesses
For businesses, email is a critical communication channel used for customer interaction, transaction notifications, and internal coordination. Any misconfiguration in SMTP settings can lead to serious operational disruptions.
Using the correct port, especially port 587, ensures that emails are delivered reliably and securely. It also reduces the risk of messages being marked as spam or failing to reach recipients.
Incorrect configurations can result in lost communications, missed transactions, and reduced customer trust. This makes proper SMTP setup an essential part of IT infrastructure management.
Businesses also benefit from improved analytics and tracking when using authenticated SMTP submission, allowing them to monitor email performance more effectively.
Future Enhancements in Email Security Protocols
Email security continues to evolve as new threats emerge. Future enhancements are expected to focus on stronger encryption standards, more advanced authentication methods, and improved anti-spoofing protections.
There is growing interest in replacing or augmenting traditional SMTP authentication with modern identity frameworks. These systems aim to reduce reliance on static credentials and improve resistance to phishing attacks.
Stronger enforcement of domain-level authentication policies will also play a major role in future email systems. This will further improve trust between sending and receiving servers.
Despite these advancements, SMTP will continue to serve as the backbone of email transmission, with port 587 remaining central to secure submission processes.
Conclusion
Understanding SMTP ports is essential for anyone working with email systems, whether for personal use, business applications, or server administration. Among the available options, port 25, 587, and 465 each serve different roles within the email ecosystem.
Port 25 is primarily reserved for server-to-server communication and is no longer suitable for direct email submission due to security restrictions and ISP limitations. Its use is largely confined to backend infrastructure where trusted communication occurs between mail servers.
Port 587 has become the global standard for email submission because it combines authentication, encryption, and broad compatibility. It ensures that only verified users can send emails while protecting data through STARTTLS encryption. This makes it the most reliable and secure option for modern email communication.
Port 465 also provides secure email transmission through implicit SSL, but its usage depends on specific server configurations and is less universally standardized compared to port 587.
In modern environments, port 587 is the recommended choice for almost all email sending scenarios. It improves deliverability, strengthens security, and ensures compliance with current email standards. By using proper authentication and encryption, it helps maintain trust in global email communication systems.
Ultimately, selecting the correct SMTP port is not just a technical decision but a foundational step in building secure, reliable, and efficient communication infrastructure.