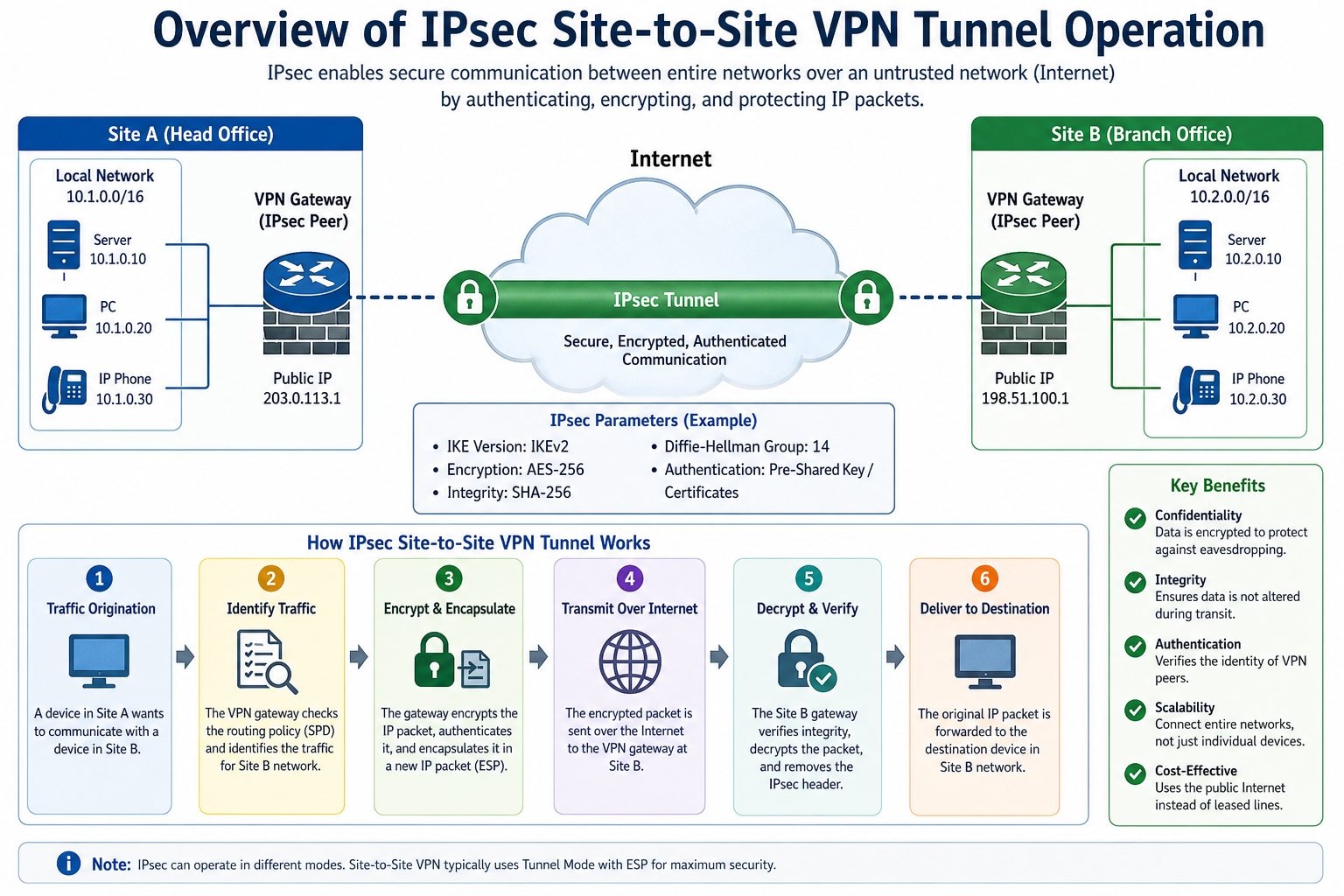
An IPsec site-to-site VPN tunnel is a secure communication method used to connect two separate private networks over an untrusted public network. Its primary purpose is to ensure that data exchanged between the networks remains confidential, unchanged, and authenticated throughout its journey. Unlike simple encrypted communication between individual devices, a site-to-site VPN operates at the network level, allowing entire subnets to communicate securely as if they were part of the same internal infrastructure. This makes it especially useful for connecting branch offices, data centers, and remote enterprise locations.
Fundamental Architecture
The architecture of an IPsec site-to-site VPN is built around VPN gateways placed at each participating network boundary. These gateways can be physical appliances or software-based security devices configured to handle encryption, decryption, and secure routing. Each gateway is responsible for protecting traffic leaving its local network and ensuring that only authorized encrypted traffic is allowed into the internal network from the remote site.
The system relies on the IPsec framework, which is a suite of protocols designed to secure Internet Protocol communication. It operates at the network layer and can protect all traffic passing between the two endpoints without requiring changes to individual applications or services. This makes it transparent to users within both networks.
Role of IPsec in Secure Communication
IPsec provides the foundation for secure communication by combining multiple security functions. It ensures data confidentiality through encryption, integrity through hashing algorithms, and authentication through identity verification mechanisms. These functions work together to prevent unauthorized access, tampering, and impersonation during data transmission.
IPsec primarily uses two core protocols: Encapsulating Security Payload (ESP) and Authentication Header (AH). ESP is more commonly used because it provides both encryption and authentication, while AH provides only authentication and integrity protection. In most modern implementations, ESP is preferred due to its ability to secure data more comprehensively.
Security Association and Its Importance
A critical concept in IPsec operation is the Security Association (SA). An SA is a set of agreed-upon parameters that define how two endpoints will secure their communication. These parameters include encryption algorithms, authentication methods, session keys, and lifetime values. Each direction of communication typically requires a separate SA, meaning that inbound and outbound traffic are handled independently.
Security Associations are established dynamically through a negotiation process. Once created, they govern how data packets are processed, ensuring both sides use consistent security rules. Without properly established SAs, secure communication cannot take place.
Internet Key Exchange Process
The establishment of a VPN tunnel begins with the Internet Key Exchange (IKE) process. IKE is responsible for negotiating and managing security parameters between the two gateways. It operates in two stages, commonly referred to as Phase 1 and Phase 2.
During Phase 1, the two gateways authenticate each other and establish a secure, encrypted channel for further negotiation. This phase ensures that both parties are legitimate and trusted before any sensitive information is exchanged. Authentication can be performed using pre-shared keys or digital certificates, depending on the security configuration.
Once Phase 1 is complete, Phase 2 begins. In this stage, the actual IPsec Security Associations are negotiated. The gateways agree on encryption algorithms, hashing methods, and key lifetimes that will be used to protect data traffic. After successful negotiation, the secure tunnel is fully established and ready for data transmission.
Encapsulation and Encryption Process
When data is sent from one network to another through a site-to-site VPN, it undergoes a process called encapsulation. The original data packet is wrapped inside another packet that is encrypted and protected using IPsec protocols. This ensures that even if the packet is intercepted during transmission, its contents remain unreadable.
The encryption process converts readable data into ciphertext using cryptographic algorithms. Only the receiving gateway, which holds the correct decryption keys, can restore the original information. This ensures confidentiality across the entire communication path. In addition to encryption, integrity checks are performed to ensure that the data has not been altered in transit.
Packet Flow Through the Tunnel
When a device in one network sends data to a device in the remote network, the packet first reaches the local VPN gateway. The gateway examines the packet and determines whether it matches predefined security policies. If the traffic is authorized, it is processed for secure transmission.
The gateway then encapsulates the packet with a new IP header and encrypts its contents using IPsec protocols. This encrypted packet is sent across the public network toward the remote gateway. Upon arrival, the remote gateway decrypts the packet, removes the outer encapsulation, and forwards the original data to its intended destination within the internal network.
This entire process happens seamlessly and is transparent to end users, who are unaware that their data is being securely transmitted over an external network.
Tunneling Mode Operation
IPsec site-to-site VPNs typically operate in tunnel mode. In this mode, the entire original IP packet is encrypted and encapsulated within a new IP packet. The new packet contains the public IP addresses of the VPN gateways, while the original private IP addresses remain hidden inside the encrypted payload.
This approach not only protects the data but also conceals the internal network structure from external observers. It enhances security by preventing attackers from gaining insight into the private addressing scheme of the connected networks.
Handling Network Address Translation Compatibility
In many real-world environments, network address translation may exist between VPN endpoints and the internet. IPsec is designed to handle such scenarios using mechanisms that allow encrypted packets to traverse NAT devices without breaking the tunnel. This is achieved by encapsulating IPsec traffic in a way that preserves its integrity while allowing it to pass through modified network headers.
This compatibility ensures that VPN tunnels remain functional even in complex network environments where private addressing and NAT are widely used.
Routing and Traffic Selection
Routing plays an important role in determining which traffic should pass through the VPN tunnel. Each VPN gateway is configured with rules that define which destination networks are reachable through the secure tunnel. When a packet matches these rules, it is directed into the VPN instead of being sent through the regular internet route.
This selective routing ensures that only intended traffic is encrypted and transmitted through the tunnel, while other traffic continues to use standard network paths. It also helps optimize performance by avoiding unnecessary encryption overhead for non-sensitive communication.
Rekeying and Session Management
To maintain long-term security, IPsec tunnels periodically refresh their encryption keys. This process, known as rekeying, ensures that even if a key is compromised, its usability is limited to a short time window. During rekeying, new Security Associations are negotiated while the existing ones are gradually replaced without disrupting active communication.
Session management also involves monitoring tunnel health. VPN gateways continuously check connectivity to ensure the tunnel remains active. If a disruption occurs due to network failure or configuration issues, the gateways attempt to re-establish the secure connection automatically.
Performance Considerations
While IPsec provides strong security, it also introduces processing overhead due to encryption and decryption operations. This can impact network performance, especially in high-throughput environments. Modern VPN gateways often use hardware acceleration to handle cryptographic tasks more efficiently, reducing latency and improving throughput.
Bandwidth utilization is also affected because encapsulation adds additional header information to each packet. Proper network planning and optimization are therefore important to maintain a balance between security and performance.
Security Strengths and Protective Mechanisms
IPsec site-to-site VPNs provide multiple layers of protection. Encryption ensures that intercepted data cannot be read, while integrity checks prevent unauthorized modifications. Authentication mechanisms verify the identity of both endpoints, preventing impersonation attacks. Additionally, anti-replay protection safeguards against attackers attempting to resend previously captured packets.
These combined mechanisms make IPsec one of the most reliable methods for securing network-to-network communication across untrusted environments.
Operational Reliability and Stability
Once established, IPsec VPN tunnels are designed to operate continuously with minimal intervention. They can automatically recover from temporary network disruptions and re-establish secure communication without requiring manual configuration. This reliability is essential for business-critical applications where consistent connectivity between sites is required.
Tunnel Monitoring and Keepalive Mechanisms
Once an IPsec site-to-site VPN tunnel is established, it is continuously monitored to ensure stable communication between the two networks. VPN gateways use keepalive mechanisms to regularly check whether the remote endpoint is still reachable. These checks involve sending small test packets at defined intervals. If responses are received, the tunnel is considered active and healthy.
If a response is not received after several attempts, the gateway assumes that the tunnel may be down due to network failure, device reboot, or configuration issues. In such cases, the system initiates reconnection procedures automatically. This helps maintain reliability without requiring manual intervention from network administrators.
Failure Detection and Automatic Recovery
In real-world environments, network disruptions are common and can occur due to ISP outages, hardware faults, or routing changes. IPsec VPN systems are designed to handle such disruptions gracefully. When a tunnel fails, the VPN gateway detects the loss of connectivity and attempts to renegotiate the connection using the original or updated security parameters.
This automatic recovery process includes re-establishing IKE Phase 1 and Phase 2 negotiations if necessary. In many cases, recovery is seamless, and traffic resumes without noticeable interruption to end users. This resilience is a key feature of IPsec-based communication.
Redundancy and High Availability Design
To improve reliability further, many organizations implement redundant VPN configurations. This involves setting up multiple tunnels between the same sites or using multiple gateways at each location. If one tunnel or gateway becomes unavailable, traffic is automatically rerouted through an alternate path.
High availability setups often use dynamic routing protocols in combination with IPsec to ensure that traffic always follows the most reliable path. This design reduces downtime and ensures business continuity even during infrastructure failures or maintenance events.
Load Balancing Across Multiple Tunnels
In more advanced deployments, IPsec tunnels can be configured for load balancing. Instead of relying on a single tunnel, traffic is distributed across multiple active tunnels. This helps optimize bandwidth usage and improve performance, especially in environments with high data transfer requirements.
Load balancing can be based on different factors such as source-destination pairs, traffic type, or predefined routing policies. This approach ensures that no single tunnel becomes a bottleneck, resulting in smoother and more efficient communication between sites.
Traffic Encryption Algorithms and Standards
The strength of an IPsec site-to-site VPN largely depends on the cryptographic algorithms used. Common encryption standards include AES (Advanced Encryption Standard), which provides strong protection for data confidentiality. Hashing algorithms such as SHA (Secure Hash Algorithm) are used to verify data integrity and ensure that packets have not been altered during transmission.
Key exchange mechanisms rely on Diffie-Hellman groups, which allow secure generation of shared encryption keys over an insecure channel. The choice of algorithm and key length significantly impacts both security strength and system performance, requiring a balance between protection and efficiency.
Policy-Based vs Route-Based VPN Operation
IPsec site-to-site VPNs can operate using either policy-based or route-based configurations. In policy-based VPNs, traffic selection is determined by predefined rules that specify which source and destination networks should be encrypted. Only matching traffic is sent through the tunnel.
In route-based VPNs, a virtual tunnel interface is created, and routing decisions determine which traffic enters the tunnel. This approach is more flexible and scalable, especially in complex networks where dynamic routing protocols are used. It also simplifies configuration when multiple subnets or changing network topologies are involved.
NAT Traversal Handling in VPN Communication
In many network environments, devices are located behind NAT devices that modify IP addresses for internet communication. IPsec traffic can sometimes face challenges in such scenarios because encryption may interfere with address translation. To address this, NAT traversal techniques are used.
NAT traversal encapsulates IPsec packets in UDP packets, allowing them to pass through NAT devices without being blocked or corrupted. This ensures that secure communication remains functional even in environments where private addressing and NAT are widely used.
Session Lifetimes and Rekey Intervals
Each IPsec session has a defined lifetime, after which the security associations must be renewed. This lifetime is typically based on either time duration or amount of data transferred. When the threshold is reached, the system automatically initiates a rekeying process to generate new encryption keys.
This periodic renewal limits the exposure of any single key and enhances overall security. Even if an attacker manages to compromise a key, its usefulness is restricted to a short time window, reducing potential damage.
Packet Integrity Verification Process
Every packet transmitted through an IPsec tunnel includes an integrity check value. This value is generated using cryptographic hashing functions before transmission. When the packet arrives at the destination, the receiving gateway recalculates the hash and compares it with the original value.
If the values match, the packet is considered authentic and unaltered. If there is a mismatch, the packet is discarded immediately. This mechanism protects against tampering, corruption, and malicious modification during transit.
Role of Encapsulation in Secure Routing
Encapsulation is a core function of IPsec tunnels. It involves wrapping original data packets inside new packets that contain encrypted payloads and additional routing information. This allows secure data to travel across public networks without exposing internal IP addressing or application data.
Encapsulation also ensures compatibility with existing internet infrastructure, allowing VPN traffic to pass through routers and service providers without requiring changes to the underlying network architecture.
Impact on Latency and Throughput
Because IPsec involves encryption, decryption, and encapsulation processes, it introduces additional processing overhead. This can result in increased latency compared to unencrypted communication. The level of impact depends on factors such as encryption strength, hardware capability, and traffic volume.
Modern VPN devices often include hardware acceleration modules that significantly reduce processing delays. These optimizations allow IPsec tunnels to handle high-speed traffic with minimal performance degradation.
Security Policy Enforcement at Gateways
VPN gateways enforce strict security policies that determine what type of traffic is allowed through the tunnel. These policies define source networks, destination networks, protocols, and ports that are permitted for encrypted communication.
Any traffic that does not match these rules is either blocked or sent through normal routing paths without encryption. This ensures that only authorized communication is protected by the VPN tunnel, maintaining both security and network efficiency.
Scalability in Enterprise Environments
IPsec site-to-site VPNs are widely used in enterprise environments due to their scalability. Multiple branches can be connected to a central network using a hub-and-spoke or mesh topology. In a hub-and-spoke design, all branch networks connect to a central hub, simplifying management. In a mesh design, each site connects directly to multiple other sites, allowing more direct communication paths.
The choice of topology depends on organizational needs, traffic patterns, and administrative complexity.
Operational Transparency for End Users
One of the key advantages of IPsec site-to-site VPNs is that they operate transparently to end users. Users within each network do not need to configure anything or be aware of the underlying secure tunnel. They simply access resources as if they were on a local network.
This transparency simplifies deployment and reduces user-side complexity while still maintaining strong security between locations.
Advanced Security Associations Management
In an IPsec site-to-site VPN environment, Security Associations play a central role in maintaining secure communication, and their management becomes more complex in large-scale deployments. Each tunnel requires properly synchronized inbound and outbound associations that define how traffic is encrypted and decrypted in both directions. These associations are not static; they are dynamically created, updated, and removed based on network activity and security policies.
To maintain consistency, both VPN gateways must agree on identical parameters such as encryption algorithms, integrity checks, and key lifetimes. If even a single parameter differs, the tunnel cannot be established or may become unstable. In enterprise setups with multiple tunnels, careful coordination is required to ensure that all associations remain aligned across different sites.
Cryptographic Key Generation and Distribution
The security of an IPsec tunnel heavily depends on how cryptographic keys are generated and exchanged. During the key exchange process, both gateways participate in a secure negotiation that results in the creation of shared secret keys. These keys are never transmitted directly over the network. Instead, they are derived using secure mathematical algorithms that ensure both sides independently arrive at the same result.
This approach significantly reduces the risk of interception. Even if an attacker captures the negotiation traffic, it remains computationally infeasible to reconstruct the actual encryption keys. The strength of this process depends on the selected Diffie-Hellman group and key length, with stronger groups providing higher security at the cost of additional processing overhead.
Encapsulation Security Payload in Detail
Encapsulation Security Payload is the primary mechanism used in most IPsec site-to-site VPNs for securing data traffic. It provides confidentiality by encrypting the payload of each packet and also ensures integrity by attaching authentication data. When a packet is processed through ESP, the original data is completely hidden from external observation.
In addition to encryption and integrity, ESP also supports optional anti-replay protection. This mechanism assigns sequence numbers to packets, allowing the receiving gateway to detect and discard duplicate or delayed packets that may be part of a malicious replay attempt. This ensures that captured traffic cannot be resent by attackers to disrupt communication or gain unauthorized access.
Authentication Header and Its Role
Although less commonly used in modern deployments, the Authentication Header protocol still plays a role in certain IPsec configurations. Unlike ESP, it does not encrypt data but focuses on verifying the authenticity and integrity of the entire packet, including certain parts of the IP header.
This makes it useful in scenarios where encryption is not required but data integrity and source verification are essential. However, due to its limitations in handling NAT environments and lack of encryption, it is often replaced by ESP in most site-to-site VPN implementations.
Interaction with Routing Protocols
IPsec site-to-site VPNs often need to integrate with dynamic routing protocols to efficiently manage traffic between multiple networks. Protocols such as OSPF or BGP can be used to automatically exchange routing information between sites. This allows the network to adapt to changes without manual configuration updates.
When combined with route-based VPN configurations, routing protocols enable more flexible and scalable network designs. They help ensure that traffic is always directed through the most appropriate tunnel based on network conditions, availability, and policy rules.
Tunnel Fragmentation and Packet Handling
Due to the additional headers introduced by encapsulation and encryption, IPsec packets are often larger than their original size. This can lead to fragmentation when packets exceed the maximum transmission unit of intermediate networks.
To address this, VPN gateways may adjust packet sizes using techniques such as Path MTU discovery. This process helps determine the optimal packet size that can travel through the network without fragmentation. Proper handling of fragmentation is important to avoid performance issues and ensure reliable communication.
Encryption Overhead Optimization Techniques
While encryption provides strong security, it also introduces processing overhead. To minimize performance impact, modern VPN gateways use several optimization techniques. Hardware-based encryption accelerators are commonly used to offload cryptographic operations from the main CPU, significantly improving throughput.
Software optimizations such as efficient algorithm selection and traffic batching also contribute to better performance. In high-traffic environments, these optimizations are essential to maintain low latency and stable connectivity.
Role of Digital Certificates in Authentication
Instead of relying solely on pre-shared keys, many IPsec deployments use digital certificates for authentication. Certificates provide a more scalable and secure method of verifying identity, especially in environments with multiple VPN endpoints.
Each gateway is issued a certificate by a trusted authority, and during tunnel establishment, these certificates are exchanged and validated. This ensures that both parties are legitimate and reduces the risk of unauthorized devices attempting to establish a connection.
Policy Enforcement and Traffic Filtering
VPN gateways enforce strict traffic filtering rules to ensure that only authorized data is transmitted through the tunnel. These policies define which networks, protocols, and services are allowed. Any traffic that does not match these rules is either dropped or routed outside the VPN tunnel.
This policy-based control is essential for maintaining security boundaries between different network segments. It also helps prevent unauthorized access and limits exposure in case of misconfigurations or compromised systems.
Handling Asymmetric Routing Scenarios
In complex network environments, traffic may take different paths in each direction, a situation known as asymmetric routing. IPsec tunnels are sensitive to this condition because security associations are direction-specific.
To handle this, VPN configurations must ensure that return traffic follows a compatible path that aligns with the established security associations. Failure to properly manage asymmetric routing can lead to packet drops or tunnel instability.
Tunneling Across Multiple Hops
Although IPsec site-to-site VPNs are typically established between two endpoints, traffic often passes through multiple intermediate networks and routers. The encapsulated nature of IPsec ensures that these intermediate devices do not interfere with the encrypted payload.
Only the VPN gateways at each end are responsible for encryption and decryption. This allows secure communication to traverse complex network infrastructures without exposing sensitive information at any intermediate point.
Session Resilience and State Preservation
IPsec tunnels are designed to maintain session continuity even in the event of temporary disruptions. When a brief network interruption occurs, the system attempts to preserve session state and quickly restore connectivity without requiring full renegotiation.
This resilience is particularly important for real-time applications and critical business systems where uninterrupted communication is essential. The ability to recover quickly minimizes the impact of transient network issues.
Scalability Challenges in Large Deployments
As the number of VPN tunnels increases, managing configurations and security policies becomes more complex. Each additional tunnel requires careful coordination of parameters, routing rules, and authentication methods.
To address scalability challenges, centralized management systems are often used to automate configuration and monitoring. This reduces administrative overhead and ensures consistency across all VPN connections in large organizations.
Integration with Network Security Architecture
IPsec site-to-site VPNs are often integrated into a broader network security framework that includes firewalls, intrusion detection systems, and access control mechanisms. This layered approach enhances overall security by combining multiple protective technologies.
The VPN tunnel acts as a secure transport layer, while other security systems monitor and control traffic before and after it passes through the tunnel. This creates a comprehensive defense strategy that protects both data in transit and network infrastructure.
Advanced Tunnel Establishment Behavior
In a real-world environment, the establishment of an IPsec site-to-site VPN tunnel is not a single fixed process but a dynamic sequence influenced by network conditions, policy configurations, and authentication methods. When two gateways initiate communication, they first determine whether a tunnel already exists or needs to be created. If no active Security Association is found, the Internet Key Exchange process begins to negotiate secure parameters.
This negotiation is highly structured, ensuring both endpoints agree on encryption standards, hashing algorithms, and authentication methods before any protected traffic is exchanged. The system is designed to fail safely, meaning that if any mismatch occurs during negotiation, the tunnel is not established, preventing insecure communication.
Dynamic Re-establishment of Tunnels
IPsec site-to-site VPN tunnels are designed to recover automatically when disruptions occur. If a tunnel is interrupted due to network instability, routing changes, or gateway failure, the system does not rely on manual intervention. Instead, it detects the loss of connectivity and attempts to re-initiate the negotiation process.
This re-establishment may involve partial or full renegotiation depending on the severity of the disruption. In minor cases, existing session parameters may be reused, while in more significant failures, both phases of the negotiation process are repeated. This ensures continuity while maintaining strict security standards.
Role of Dead Peer Detection Mechanism
A key mechanism used in maintaining tunnel reliability is Dead Peer Detection. This function allows a VPN gateway to determine whether the remote endpoint is still responsive. It works by sending periodic messages that require a valid response from the peer gateway.
If multiple consecutive attempts fail, the system concludes that the remote peer is unreachable. This triggers cleanup of existing Security Associations and initiates reconnection procedures. Dead Peer Detection is essential in preventing stale or inactive tunnels from consuming system resources.
Encryption Algorithm Negotiation Flexibility
During tunnel creation, both gateways must agree on encryption and hashing algorithms. This negotiation process is flexible, allowing multiple acceptable options to be defined in advance. If the preferred algorithm is not supported by both sides, the system automatically selects the next compatible option from the configured list.
This flexibility ensures interoperability between different devices and vendors while still maintaining strong security. However, administrators must carefully choose algorithm sets to avoid fallback to weaker encryption standards.
Transport and Tunnel Mode Differences in Operation
Although site-to-site VPNs primarily operate in tunnel mode, understanding the difference between tunnel mode and transport mode is important for deeper comprehension. In tunnel mode, the entire original packet is encapsulated and encrypted, hiding both payload and original headers. In contrast, transport mode only encrypts the payload while leaving the original IP header visible.
For site-to-site communication, tunnel mode is preferred because it provides full network-to-network protection and hides internal addressing structures from external observation.
Interaction with Firewall Systems
IPsec VPN gateways often work closely with firewall systems to enforce security policies. Firewalls determine whether VPN traffic is allowed to enter or exit the network based on predefined rules. In many configurations, firewall rules must explicitly permit IPsec-related protocols and ports to ensure proper tunnel operation.
Additionally, once traffic is decrypted at the gateway, it is subject to internal firewall inspection before being forwarded to destination devices. This ensures that encrypted traffic does not bypass security controls once it enters the trusted network.
Impact of Packet Reordering and Latency Variation
Because IPsec traffic may travel across multiple network paths, packets can sometimes arrive out of order or with varying delays. The receiving gateway must be able to correctly reorder packets before processing them. Sequence numbering and buffering mechanisms are used to handle this scenario.
If packet reordering exceeds acceptable thresholds, it can lead to performance degradation or retransmissions. Proper network design helps minimize such issues by ensuring consistent routing paths and stable latency conditions.
Integration with Multi-Site Network Topologies
In large organizations, IPsec site-to-site VPNs are rarely limited to just two endpoints. Instead, they are part of multi-site topologies where several networks are interconnected. These can be arranged in hub-and-spoke or full mesh designs depending on communication requirements.
In hub-and-spoke models, all branch networks communicate through a central hub, simplifying management but increasing dependency on the central site. In mesh designs, each site connects directly to others, improving redundancy but increasing configuration complexity.
Scalability Through Automation and Templates
As the number of VPN tunnels increases, manual configuration becomes inefficient. To address this, automation tools and configuration templates are used. These allow administrators to define standardized VPN policies that can be applied across multiple sites consistently.
Automation reduces human error and ensures uniform security configurations. It also simplifies scaling when new branches or data centers are added to the network infrastructure.
Handling of Maximum Transmission Unit Limitations
Encapsulation and encryption increase packet size, which can lead to issues when packets exceed the maximum transmission unit of intermediate networks. To prevent fragmentation-related inefficiencies, VPN systems often adjust packet sizes dynamically.
This ensures that packets remain within acceptable limits and reduces the likelihood of fragmentation, which can negatively impact performance and reliability.
Security Monitoring and Logging Mechanisms
IPsec gateways continuously generate logs that record tunnel activity, authentication attempts, and error conditions. These logs are essential for monitoring security events and diagnosing network issues.
Security monitoring systems analyze this data to detect anomalies such as repeated failed authentication attempts or unexpected tunnel drops. This helps in identifying potential security threats or misconfigurations early.
Encryption Key Rotation Strategy
To maintain long-term security, encryption keys are periodically rotated. This process ensures that even if a key is exposed, its usability is limited to a short time window. Key rotation occurs automatically based on predefined time intervals or data transfer thresholds.
When rotation occurs, new Security Associations are created while existing ones are phased out. This transition is designed to be seamless, ensuring uninterrupted communication between sites.
Traffic Classification and Selective Encryption
Not all network traffic needs to pass through the VPN tunnel. Traffic classification mechanisms determine which data should be encrypted based on predefined rules. Sensitive communication between internal networks is typically routed through the tunnel, while less critical traffic may use standard routing paths.
This selective approach optimizes performance while maintaining strong security for important data flows.
Hardware Acceleration in Modern Deployments
To handle high volumes of encrypted traffic, modern VPN gateways often use hardware acceleration technologies. These specialized components are designed to perform cryptographic operations more efficiently than general-purpose CPUs.
Hardware acceleration significantly improves throughput and reduces latency, making it possible to support large-scale VPN deployments without performance bottlenecks.
Error Handling and Fault Isolation
When issues occur within a VPN tunnel, systems are designed to isolate faults without affecting the entire network. For example, if one tunnel fails in a multi-tunnel environment, other tunnels remain operational.
Error handling mechanisms also provide detailed diagnostic information, allowing administrators to quickly identify and resolve underlying issues.
Operational Continuity in Enterprise Networks
One of the most important characteristics of IPsec site-to-site VPNs is their ability to support continuous business operations. Even during network disruptions or maintenance activities, systems are designed to maintain connectivity or quickly restore it.
This operational continuity ensures that critical applications such as databases, communication systems, and cloud services remain accessible across distributed locations.
Conclusion
IPsec site-to-site VPN tunnels form a reliable and secure method for connecting separate networks over untrusted infrastructure. Their operation is built on a combination of strong encryption, structured key exchange, and carefully managed security associations that ensure data remains protected throughout transmission. By encapsulating and encrypting entire network packets, they create a secure virtual bridge between locations while keeping internal network details hidden from external exposure.
Beyond basic encryption, these tunnels rely on continuous negotiation, monitoring, and automatic recovery mechanisms to maintain stable communication even in the presence of network disruptions. Features such as rekeying, dead peer detection, and session re-establishment ensure that connectivity is resilient and self-healing, reducing the need for manual intervention.
Their flexibility allows integration with routing protocols, firewall systems, and multi-site architectures, making them suitable for both small-scale and large enterprise environments. At the same time, performance optimization techniques such as hardware acceleration and efficient packet handling help balance security with speed and scalability.
Overall, IPsec site-to-site VPN tunnels provide a strong foundation for secure inter-network communication, enabling organizations to connect distributed environments confidently while maintaining confidentiality, integrity, and operational continuity.