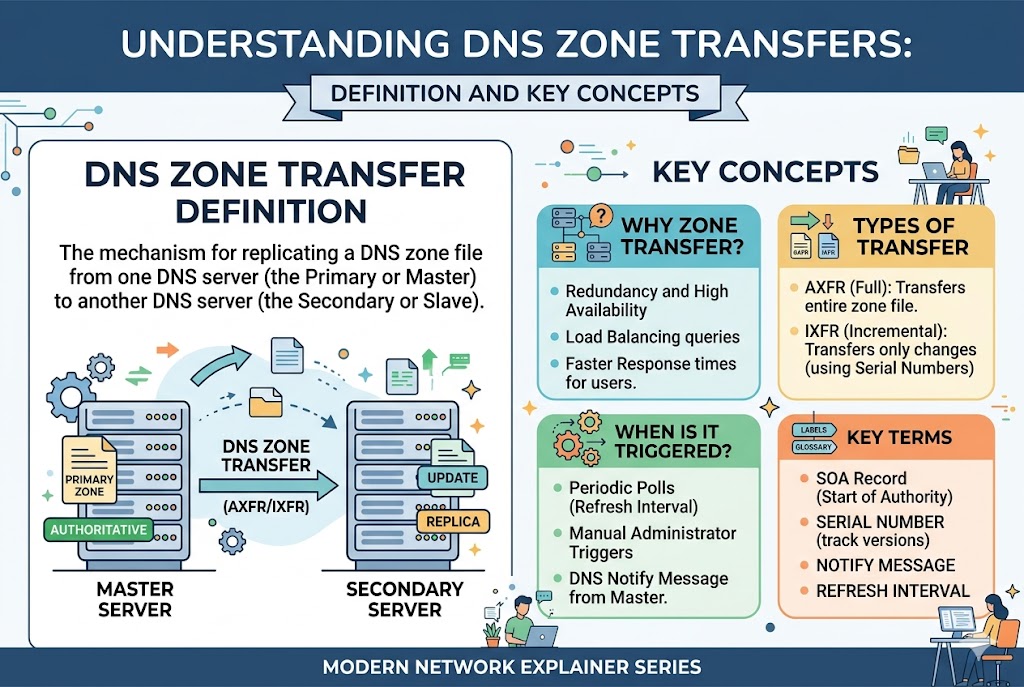
DNS zone transfers are a core mechanism used in the Domain Name System to keep multiple DNS servers synchronized. They ensure that when changes are made to DNS records on a primary server, those updates are accurately replicated to secondary servers. This replication is essential for maintaining consistency, reliability, and fault tolerance in internet name resolution.
Role of DNS in Internet Communication
The Domain Name System acts as the internet’s address book, translating human-readable domain names into IP addresses that machines can understand. Every time a user visits a website, sends an email, or connects to an online service, DNS plays a critical role in locating the correct destination. Because DNS is distributed across many servers worldwide, consistency between these servers is essential, and this is where zone transfers become important.
What DNS Zone Transfers Actually Do
A DNS zone transfer is the process of copying DNS database information from one server to another. This database, known as a DNS zone, contains records such as domain mappings, mail server information, and other configuration details. When a secondary DNS server needs to update or build its copy of the zone, it requests this information from the primary DNS server through a zone transfer.
Primary and Secondary DNS Server Relationship
In most DNS architectures, there is a primary DNS server that holds the original, authoritative version of the zone data. Secondary DNS servers act as replicas that store identical copies of this data. These secondary servers exist to improve redundancy and load distribution. If the primary server becomes unavailable, secondary servers can continue responding to DNS queries without interruption.
The synchronization between primary and secondary servers is maintained through zone transfers. Without this process, secondary servers would quickly become outdated, leading to incorrect or failed domain resolution.
How DNS Zone Transfers Work in Practice
The process begins when a secondary DNS server checks whether its data is up to date. It does this by examining the SOA (Start of Authority) record of the zone. The SOA record contains a serial number that increases every time a change is made to the zone.
If the secondary server detects that its serial number is lower than the primary server’s version, it initiates a zone transfer request. The primary server then responds by sending the required DNS records so the secondary server can update its local copy.
Once the transfer is complete, both servers have identical zone data, ensuring consistent responses to DNS queries.
SOA Record and Its Importance in Zone Transfers
The SOA record is one of the most critical components in DNS zone management. It contains essential metadata about the zone, including the serial number, refresh interval, retry interval, and expiration time.
The serial number is particularly important because it determines whether a zone transfer is necessary. The refresh value tells secondary servers how often to check for updates, while retry defines how frequently they should retry if a transfer fails. The expiration value indicates when the zone data should no longer be considered valid if updates cannot be obtained.
Without the SOA record, DNS servers would have no reliable method to determine when synchronization is required.
Types of DNS Zone Transfers
There are two main types of DNS zone transfers used to manage synchronization efficiently.
A full zone transfer involves copying the entire DNS zone database from the primary server to the secondary server. This method ensures complete synchronization but can consume more bandwidth and processing power, especially for large zones.
An incremental zone transfer is more efficient because it only transfers the changes made since the last update. Instead of copying all records again, only modified, added, or deleted records are transmitted. This reduces network load and speeds up synchronization significantly.
Transport Protocols Used in Zone Transfers
DNS zone transfers typically use TCP rather than UDP. TCP is preferred because it provides reliable, ordered delivery of data, which is essential when transferring potentially large DNS zone files.
The standard port used for these transfers is port 53, which is also used for regular DNS queries. Using TCP ensures that even if packets are lost or delayed, the transfer can still complete accurately without data corruption.
Step-by-Step Flow of a Zone Transfer
The process of a DNS zone transfer follows a structured flow. First, the secondary server checks its stored serial number against the primary server’s SOA record. If the primary server has a newer version, the secondary server initiates a request for zone data.
The primary server verifies whether the requesting server is authorized to receive the zone information. If permitted, it begins transmitting DNS records over a TCP connection.
The secondary server receives the data and updates its local zone file. Once the transfer is complete, it updates its SOA serial number to match the primary server. From that point onward, it can respond to DNS queries using the updated data.
Why DNS Zone Transfers Are Important
Zone transfers play a key role in maintaining the reliability and scalability of DNS infrastructure. By allowing multiple servers to hold identical copies of DNS data, they ensure that users can always resolve domain names even if one server fails.
They also help distribute query traffic across multiple servers, improving response times and reducing the load on any single system. This makes DNS more efficient and resilient under high traffic conditions.
Performance Benefits of Zone Transfers
One of the major advantages of DNS zone transfers is improved performance. When DNS data is replicated across multiple servers, queries can be answered faster because users are directed to the nearest or least busy server.
Incremental transfers also reduce bandwidth usage by only sending updated data instead of full zone files. This optimization is especially important for large organizations with frequently changing DNS records.
Common Misconfigurations and Risks
Although DNS zone transfers are essential, improper configuration can lead to serious issues. One of the most common risks is unauthorized zone transfers. If a DNS server is not properly restricted, external systems may be able to request and download the entire DNS zone file.
This can expose sensitive infrastructure details, such as internal hostnames and network configurations. In some cases, it may even assist attackers in mapping out an organization’s network structure.
Another issue arises when synchronization settings are incorrect. If refresh or retry intervals are poorly configured, secondary servers may become outdated or fail to update on time, leading to inconsistent DNS responses.
Security Considerations in DNS Zone Transfers
To prevent unauthorized access, DNS zone transfers should always be restricted to trusted secondary servers. Access control mechanisms are commonly used to ensure that only approved systems can request zone data.
Additionally, authentication methods can be implemented to verify the identity of requesting servers before allowing data transfer. This helps ensure that DNS information is only shared within the intended infrastructure.
Monitoring and logging zone transfer activity is also important, as it helps detect unusual or suspicious behavior that could indicate an attempted breach.
Best Practices for Managing Zone Transfers
Proper management of DNS zone transfers involves a combination of security, performance, and reliability practices. Limiting zone transfers to known servers is one of the most effective measures to reduce risk.
Using incremental transfers whenever possible helps optimize bandwidth usage and improves efficiency. Regular monitoring of SOA serial numbers ensures that updates are being applied correctly across all servers.
It is also important to test DNS configuration changes in controlled environments before deploying them to production systems. This reduces the risk of propagation errors and downtime.
Reliability and Redundancy Through Zone Transfers
One of the main reasons DNS zone transfers are widely used is to achieve high availability. By maintaining multiple synchronized DNS servers, systems can continue functioning even during outages or maintenance.
This redundancy is critical for large-scale internet services where downtime can result in significant disruption. Zone transfers ensure that no single point of failure exists within the DNS infrastructure.
DNS Zone Transfer Process in Greater Detail
The DNS zone transfer process is not just a simple copy operation; it is a structured synchronization method that ensures data integrity between DNS servers. When a secondary server identifies that its data is outdated, it does not immediately overwrite its records. Instead, it carefully initiates a validation process by comparing serial numbers in the SOA record to confirm whether an update is required. This step prevents unnecessary data transfers and reduces network overhead.
Once the need for synchronization is confirmed, the secondary server establishes a connection with the primary server using TCP. This connection is essential because DNS zone data can be large and must be transferred reliably. During this phase, both servers communicate to verify compatibility and permissions before any data is exchanged.
The primary server then begins transmitting DNS records in a structured format. These records include all essential zone information such as A records, MX records, CNAME records, and other DNS entries. The secondary server receives this data sequentially and temporarily stores it before applying it to its active DNS database.
After the transfer is complete, the secondary server performs a validation check to ensure that all records have been received correctly. Only after successful validation does it replace its old zone data with the updated version.
Incremental Zone Transfers and Efficiency Improvements
Incremental zone transfers play a significant role in optimizing DNS performance. Instead of transferring the entire zone file each time a change occurs, only the modified portions of the zone are sent. This includes newly added records, updated entries, or deleted records.
This method significantly reduces bandwidth consumption, especially in environments where DNS records change frequently. It also speeds up synchronization, allowing secondary servers to stay updated almost in real time without placing excessive load on the primary server.
To support incremental transfers, DNS systems maintain a change history or track modifications using the SOA serial number system. Each update increments the serial number, which signals secondary servers that a partial update is available.
Full Zone Transfers and Their Use Cases
Despite the efficiency of incremental transfers, full zone transfers are still necessary in certain situations. A full zone transfer copies the entire DNS zone database from the primary server to the secondary server.
This process is typically used when a new secondary server is added to the system or when a server has fallen significantly out of sync. It is also used when data corruption is detected or when configuration changes require a complete refresh of the zone data.
Although full transfers consume more resources, they ensure complete consistency and are essential for maintaining DNS integrity during major updates or recovery operations.
Role of TCP in DNS Zone Transfers
TCP is the preferred transport protocol for DNS zone transfers due to its reliability. Unlike UDP, which is used for standard DNS queries, TCP ensures that all packets are delivered in order and without loss.
This is critical because DNS zone data must remain accurate and complete. Even a single missing record could result in incorrect domain resolution or service disruption. TCP also provides built-in error checking and retransmission mechanisms, which further enhance reliability.
The use of TCP also allows larger data transfers without fragmentation issues, making it suitable for extensive DNS zones with many records.
Zone Transfer Security Risks and Exposure
One of the most significant risks associated with DNS zone transfers is unauthorized access. If improperly configured, a DNS server may allow any external system to request a full copy of its zone data.
This exposure can reveal sensitive internal infrastructure details, including server names, IP address ranges, and organizational structure. Such information can be valuable to attackers attempting reconnaissance before launching targeted attacks.
Another risk arises from misconfigured access control lists. If these lists are too permissive or incorrectly applied, unauthorized systems may gain access to DNS data without proper validation.
Techniques Used to Prevent Unauthorized Transfers
To protect against unauthorized access, DNS administrators implement strict access control policies. These policies define which servers are allowed to initiate zone transfers.
Only trusted secondary servers should be included in this list, and all other requests should be denied by default. This approach follows the principle of least privilege, ensuring that only necessary systems can access sensitive DNS data.
In some cases, additional authentication mechanisms are used to verify the identity of requesting servers. This adds an extra layer of protection and reduces the risk of spoofed requests.
DNS Synchronization Timing and Refresh Intervals
Timing plays an important role in DNS zone transfers. Secondary servers do not constantly request updates; instead, they follow a structured schedule defined in the SOA record.
The refresh interval determines how often a secondary server checks for updates. If the primary server is unreachable, the retry interval defines how often the secondary server should attempt reconnection.
If synchronization fails repeatedly and the expiration time is reached, the secondary server may stop serving the zone data altogether, as it is considered outdated.
These timing mechanisms ensure that DNS data remains both current and reliable while avoiding excessive network traffic.
Load Distribution Benefits of DNS Zone Transfers
DNS zone transfers also contribute to load balancing across DNS infrastructure. By distributing identical copies of zone data across multiple servers, query traffic can be shared more evenly.
This reduces the burden on any single DNS server and improves response times for users. It also ensures that high traffic volumes do not overwhelm the system during peak usage periods.
In global networks, secondary servers are often strategically placed in different geographic regions. This allows users to connect to the nearest DNS server, further improving performance.
Data Consistency Across Distributed Systems
Maintaining data consistency is one of the most important goals of DNS zone transfers. Without synchronization, different servers could provide conflicting responses to the same query.
Zone transfers ensure that all servers within a DNS zone reflect the same information. This consistency is crucial for preventing errors such as incorrect IP resolution or failed domain lookups.
Even small inconsistencies in DNS data can lead to significant disruptions, making synchronization a critical function in distributed systems.
Failure Handling and Recovery Mechanisms
DNS zone transfer systems are designed to handle failures gracefully. If a transfer is interrupted due to network issues or server downtime, the process can resume without restarting from the beginning in many cases.
Secondary servers continuously monitor the status of primary servers and retry transfers based on predefined intervals. This ensures that temporary failures do not lead to long-term inconsistencies.
In more advanced configurations, multiple backup servers may be used to provide alternative sources for zone data in case the primary server is unavailable.
Scalability of DNS Infrastructure Using Zone Transfers
As organizations grow, their DNS requirements also expand. Zone transfers enable scalability by allowing new secondary servers to be added without duplicating manual configuration efforts.
Once a new server is configured as a secondary DNS server, it automatically receives zone data from the primary server. This simplifies deployment and ensures rapid scaling of DNS infrastructure.
Large networks often rely heavily on this mechanism to support global services with millions of users.
Monitoring and Maintenance of Zone Transfers
Ongoing monitoring is essential to ensure that DNS zone transfers are functioning correctly. Administrators track transfer success rates, synchronization delays, and error logs to identify potential issues.
Regular maintenance includes verifying that all secondary servers are up to date and that transfer permissions remain correctly configured. Any discrepancies must be addressed quickly to prevent service disruptions.
Monitoring also helps detect unusual activity that may indicate misconfiguration or unauthorized access attempts.
Advanced DNS Zone Transfer Mechanisms and Internal Operations
DNS zone transfers operate through a structured internal mechanism that ensures data integrity while minimizing disruption to active DNS services. At a deeper level, the process involves multiple validation layers, secure communication checks, and data formatting rules that allow DNS servers to exchange information efficiently without compromising stability.
When a zone transfer is initiated, the secondary server does not immediately accept data. Instead, it first prepares a local cache environment where incoming records will be temporarily stored. This prevents partial or corrupted data from affecting live DNS responses. Only after the full transfer is completed and verified does the system commit the changes to active memory.
This staging process is critical in environments where DNS uptime is essential. It ensures that even during updates, the server can continue responding to queries using its existing stable dataset.
DNS Record Structure During Transfers
During a zone transfer, DNS data is transmitted in a standardized format consisting of multiple record types. Each record serves a specific purpose in domain resolution.
Address records define direct mappings between domain names and IP addresses, while mail exchange records specify how email traffic should be routed. Canonical name records allow one domain to point to another, enabling aliasing and redirection. There are also text records that store additional metadata used for verification and configuration purposes.
These records are transmitted in sequence, ensuring that hierarchical relationships within the DNS zone are preserved. The structure of the data is maintained so that secondary servers can reconstruct the zone exactly as it exists on the primary server.
Zone Transfer Authentication and Validation Layers
Modern DNS systems often implement multiple layers of validation before allowing zone transfers. The first layer involves verifying the identity of the requesting server through its IP address. Only pre-approved addresses are permitted to initiate transfer requests.
The second layer involves checking compatibility between DNS configurations. This ensures that both servers are configured for the same zone and are operating under compatible DNS software versions.
In more secure environments, cryptographic authentication may also be used. This ensures that even if an attacker gains access to the network, they cannot successfully impersonate a legitimate DNS server.
These validation steps significantly reduce the risk of unauthorized data exposure and maintain the integrity of DNS infrastructure.
Data Integrity Checks During Transfer
Ensuring that DNS data is transferred accurately is one of the most important aspects of the process. To achieve this, integrity checks are performed at multiple stages.
Before transmission begins, the primary server prepares a structured dataset that includes checksums or validation markers. As data is transmitted, the secondary server compares received records against expected values to detect inconsistencies.
If any mismatch or corruption is detected, the transfer may be aborted and restarted. This ensures that incomplete or damaged data does not enter the active DNS database.
These integrity mechanisms are essential for maintaining trust in DNS responses, as even minor errors could lead to incorrect routing of internet traffic.
Propagation Delays and Synchronization Timing
Although DNS zone transfers are designed for efficiency, slight delays in propagation can still occur. These delays depend on factors such as network latency, server load, and configured refresh intervals.
Secondary servers do not constantly request updates; instead, they follow timed intervals defined by the SOA record. This means that there is always a short window during which DNS data may be temporarily inconsistent across servers.
However, this inconsistency is usually minimal and quickly resolved through subsequent synchronization cycles. In most systems, these delays are measured in seconds or minutes rather than hours.
Impact of DNS Zone Transfers on Global Internet Stability
DNS zone transfers contribute significantly to the overall stability of the internet. By ensuring that multiple servers maintain synchronized records, they prevent single points of failure and reduce dependency on any one system.
This distributed approach allows DNS queries to be resolved even during large-scale outages or network disruptions. If one server becomes unavailable, others can continue providing accurate responses without interruption.
This redundancy is a fundamental reason why the internet remains operational even when individual systems fail.
Scalability Challenges in Large DNS Environments
As DNS zones grow in size, managing zone transfers becomes more complex. Large organizations may have thousands or even millions of DNS records that need to be synchronized across multiple servers.
In such environments, transfer efficiency becomes critical. Incremental transfers help reduce load, but careful tuning of refresh intervals and server capacity is still required to maintain performance.
Network congestion can also impact transfer speed, especially when multiple secondary servers request updates simultaneously. To address this, administrators often stagger update intervals or distribute load across multiple primary servers.
Role of DNS Caching in Reducing Transfer Load
DNS caching plays an important role in reducing the frequency of zone transfers. When DNS data is cached at various levels, fewer direct queries reach authoritative servers.
This reduces the need for constant synchronization, as cached data can serve user requests without immediate reliance on the primary DNS database.
However, caching must be carefully balanced with update frequency to ensure that outdated information is not served for extended periods.
Zone Transfers in Multi-Server Architectures
In complex infrastructures, DNS zones may be replicated across multiple layers of servers. In such setups, a primary server may transfer data to multiple secondary servers, which may further replicate the data to additional nodes.
This hierarchical structure improves scalability and fault tolerance but also increases the complexity of synchronization. Each layer must carefully manage update timing to prevent inconsistencies from propagating through the system.
Proper coordination between these layers ensures that DNS data remains consistent across the entire network.
Error Handling During Zone Transfers
Errors can occur during zone transfers due to network instability, server overload, or configuration mismatches. When this happens, DNS systems are designed to retry the transfer rather than failing permanently.
Retry mechanisms follow predefined intervals to avoid overwhelming the network with repeated requests. If repeated failures occur, administrators are alerted so they can investigate and resolve the issue.
This automated error-handling approach ensures that temporary disruptions do not lead to long-term DNS inconsistencies.
Monitoring Tools and Diagnostics for Zone Transfers
Administrators rely on monitoring tools to track the performance and health of DNS zone transfers. These tools provide insights into transfer frequency, success rates, and synchronization delays.
Logs are analyzed to detect patterns that may indicate underlying issues such as misconfigurations or network bottlenecks. In some cases, alerts are generated automatically when transfer failures exceed acceptable thresholds.
This proactive monitoring helps maintain high availability and ensures that DNS infrastructure remains stable and responsive.
Security Hardening Strategies for DNS Systems
To further secure DNS zone transfers, administrators often implement additional hardening techniques. These include isolating DNS servers within secure network segments and limiting exposure to external traffic.
Firewalls are commonly used to restrict access to DNS transfer ports, ensuring that only trusted systems can communicate with DNS servers.
Regular audits are also conducted to verify that access control rules remain accurate and effective over time.
Future Trends in DNS Zone Transfer Technology
As internet infrastructure continues to evolve, DNS zone transfer mechanisms are also being refined. There is a growing focus on automation, encryption, and real-time synchronization.
Future systems are expected to reduce propagation delays even further and improve security through stronger authentication methods. Enhanced monitoring and AI-driven diagnostics may also play a role in optimizing transfer efficiency.
These advancements aim to make DNS infrastructure more resilient, scalable, and secure in increasingly complex digital environments.
Final Expansion of Core Understanding
DNS zone transfers are far more than a simple data replication process. They represent a carefully engineered system of synchronization, validation, and distribution that supports the global DNS infrastructure.
Through structured communication between servers, strict security controls, and efficient transfer methods, they ensure that domain name resolution remains accurate and reliable across the internet at all times.
DNS Zone Transfer Security Architecture and Threat Landscape
DNS zone transfers exist within a broader security context where data availability and data protection must be carefully balanced. While their primary function is synchronization, they can also become a potential exposure point if not properly controlled. This makes understanding their security architecture essential for maintaining safe DNS operations.
At the core of DNS security design is the principle that zone data should only be shared with explicitly trusted systems. Any deviation from this principle can expose the entire DNS structure of an organization. Because DNS records often reveal internal system naming patterns and infrastructure layouts, unauthorized access can provide attackers with valuable reconnaissance information.
To mitigate this, modern DNS systems implement strict trust boundaries that define exactly which servers are allowed to participate in zone transfers. These boundaries are enforced at multiple layers, including network filtering, server-level configuration, and identity validation mechanisms.
Threat Models Associated with DNS Zone Transfers
Several potential threats are associated with improperly configured zone transfers. One of the most common is information disclosure, where an external entity gains access to the full DNS zone and extracts internal hostnames and network mappings.
Another threat involves reconnaissance-based attacks, where exposed DNS data is used to map internal systems before launching targeted intrusion attempts. Even if no direct vulnerability exists in the DNS system itself, the information gained can significantly increase the effectiveness of other attacks.
There is also the risk of unauthorized replication, where a malicious server attempts to mimic a legitimate secondary server and request zone data. Without proper authentication, such attempts may succeed in poorly secured environments.
Defense-in-Depth Strategy for Zone Transfers
A layered defense approach is commonly used to secure DNS zone transfers. The first layer is network restriction, where only specific IP addresses are permitted to initiate transfer requests.
The second layer involves server-side validation, where DNS software verifies that incoming requests match known and trusted secondary servers. This prevents unknown systems from interacting with the zone data even if they reach the server.
The third layer may include cryptographic validation, where secure keys or signatures are used to authenticate transfer requests. This ensures that even if an attacker is on the same network, they cannot successfully impersonate a trusted system.
Together, these layers create a robust defense system that significantly reduces the risk of unauthorized access.
Role of Firewall and Network Segmentation
Firewalls play an important role in controlling DNS zone transfer traffic. By restricting access to DNS ports, particularly TCP-based transfer channels, firewalls ensure that only approved systems can communicate with DNS servers.
Network segmentation further enhances security by isolating DNS infrastructure from general network traffic. In many enterprise environments, DNS servers are placed within dedicated network zones that are not directly accessible from external networks.
This isolation reduces exposure and ensures that even if another part of the network is compromised, DNS zone transfer mechanisms remain protected.
Logging, Auditing, and Traceability
Logging is a critical component of DNS zone transfer security. Every transfer request, whether successful or failed, should be recorded for auditing purposes.
These logs provide valuable insight into system behavior and help identify unusual patterns such as repeated failed transfer attempts or unexpected source IP addresses.
Auditing mechanisms allow administrators to review historical transfer activity and ensure that all operations comply with security policies. This traceability is essential for forensic analysis in case of a security incident.
Performance vs Security Trade-offs in Zone Transfers
There is often a balance that must be maintained between performance and security in DNS zone transfers. While strict security controls improve protection, they can sometimes introduce additional processing overhead or delay synchronization.
For example, cryptographic authentication adds computational cost, and strict firewall rules may require more complex routing configurations. However, these trade-offs are generally acceptable because DNS integrity and confidentiality are high-priority concerns.
Organizations typically tune their DNS systems based on their operational requirements, balancing speed of propagation with acceptable security levels.
Impact of Misconfiguration on DNS Ecosystems
Misconfiguration of DNS zone transfers is one of the most common causes of DNS-related security issues. A single incorrectly set permission can expose an entire zone to the public internet.
Such exposure may include internal server names, administrative hostnames, and service endpoints that were never intended to be publicly visible. Once exposed, this information can be cached or archived by external systems, making it difficult to fully remove.
Misconfiguration can also lead to synchronization failures, where secondary servers stop receiving updates, resulting in outdated or inconsistent DNS responses.
Automation in Modern DNS Management
Modern DNS environments increasingly rely on automation to manage zone transfers. Automated systems can detect configuration changes, adjust synchronization schedules, and validate transfer success without manual intervention.
Automation reduces the likelihood of human error, which is one of the primary causes of DNS misconfiguration. It also improves response time when changes are made to DNS records, ensuring that updates propagate quickly and consistently.
However, automation must be carefully controlled to prevent unintended changes from propagating across the DNS infrastructure.
High Availability Architectures Using Zone Transfers
DNS zone transfers are a fundamental part of high availability architectures. By distributing identical zone data across multiple servers, systems ensure continuous operation even during hardware or network failures.
In such architectures, multiple secondary servers may exist in different geographic regions. These servers continuously synchronize with primary or master nodes to maintain up-to-date data.
This distributed model ensures that even if an entire data center goes offline, DNS resolution can continue through alternative servers.
Load Balancing and Traffic Distribution Effects
Zone transfers indirectly support load balancing by enabling multiple authoritative servers to respond to DNS queries. Instead of relying on a single server, queries are distributed across several synchronized nodes.
This reduces latency for end users and prevents overload on any single system. It also improves resilience during traffic spikes, such as during peak usage hours or large-scale events.
By maintaining identical zone data across servers, DNS ensures that load distribution does not affect consistency of responses.
Real-Time Synchronization Challenges
Achieving near real-time synchronization in DNS environments can be challenging due to inherent propagation delays. Even with incremental transfers, there is always a short delay between when a change is made and when it is fully reflected across all servers.
These delays are influenced by network conditions, server load, and configured refresh intervals. While typically small, they can become noticeable in highly dynamic environments where DNS records change frequently.
Advanced systems attempt to minimize these delays through optimized scheduling and rapid propagation mechanisms.
DNS Zone Transfers in Cloud-Based Environments
In cloud-based infrastructure, DNS zone transfers are often integrated into distributed management systems. Instead of relying on traditional static servers, DNS data may be replicated across virtualized environments.
This introduces additional complexity, as servers may be dynamically created or removed based on demand. Zone transfer mechanisms must adapt to these changes while maintaining consistency across all active nodes.
Cloud environments often rely heavily on automation and orchestration tools to manage DNS synchronization efficiently.
Operational Best Practices for Long-Term Stability
Maintaining stable DNS zone transfer operations requires consistent monitoring, regular configuration reviews, and adherence to best practices.
Administrators should ensure that only authorized servers are included in transfer configurations and that outdated or unused entries are removed promptly. Regular testing of transfer processes helps identify potential issues before they affect production systems.
Documentation also plays an important role, ensuring that all DNS configurations are clearly recorded and understood by operational teams.
Final Advanced Perspective on Zone Transfers
At an advanced level, DNS zone transfers can be seen as a coordination system that enables distributed agreement across multiple network nodes. They ensure that independent servers operate with a shared understanding of domain structure and routing information.
This synchronization capability is what allows DNS to function as a global, fault-tolerant system capable of handling massive scale while maintaining accuracy and speed.
DNS Zone Transfers and Their Role in Modern Networks
DNS zone transfers are a fundamental part of how the Domain Name System maintains accuracy, consistency, and reliability across multiple servers. By enabling the replication of DNS zone data from a primary server to secondary servers, they ensure that domain resolution remains stable even in the presence of failures, high traffic, or network disruptions.
Throughout the DNS ecosystem, zone transfers act as the synchronization backbone that keeps distributed servers aligned. Without this mechanism, DNS infrastructure would quickly become inconsistent, leading to incorrect domain lookups, service failures, and reduced internet reliability. Their ability to maintain identical records across multiple locations is what allows DNS to function seamlessly at a global scale.
Conclusion:
From a technical perspective, zone transfers rely on structured communication, validation checks, and secure data transmission methods to ensure accuracy during replication. The use of SOA records for version control, TCP for reliable transport, and incremental updates for efficiency all contribute to a highly optimized synchronization system.
Security remains a critical aspect of DNS zone transfers. Proper configuration, strict access control, and monitoring are essential to prevent unauthorized access and potential data exposure. When misconfigured, zone transfers can reveal sensitive infrastructure details, making them a potential security risk. However, when properly secured, they operate safely and efficiently as part of a well-designed DNS architecture.
In modern environments, especially large-scale and cloud-based systems, DNS zone transfers continue to evolve with automation, improved monitoring, and stronger authentication methods. These advancements help reduce manual errors, improve synchronization speed, and enhance overall system resilience.
Ultimately, DNS zone transfers are not just a background technical process—they are a critical mechanism that supports the stability and scalability of the internet itself. By ensuring that DNS data remains consistent across distributed systems, they help maintain uninterrupted connectivity, reliable performance, and global accessibility of online services.