Access Control Lists are a foundational security mechanism used across operating systems, networking devices, and application environments to manage and enforce permissions. At their core, ACLs are designed to answer a simple but critical question: who is allowed to access a specific resource, and what exactly are they allowed to do with it. Although the concept appears straightforward, ACLs operate through a structured and layered decision process that makes them highly effective in complex digital environments.
In modern computing systems, resources are constantly being requested by multiple users, services, and automated processes. Without a structured permission model, it would be nearly impossible to maintain security or prevent unauthorized actions. ACLs solve this challenge by acting as a controlled gatekeeper that evaluates every access request against a defined set of rules. These rules are not random; they are carefully designed by system administrators or security policies to ensure that only legitimate access is granted.
ACLs are widely used because they provide both flexibility and precision. Instead of giving broad permissions to all users, ACLs allow fine-grained control at the level of individual users or groups. This means that access can be tailored to specific needs, ensuring that each entity has only the permissions required to perform its tasks. This principle is often referred to as the principle of least privilege, which is a key concept in cybersecurity.
Core Structure of ACL Systems
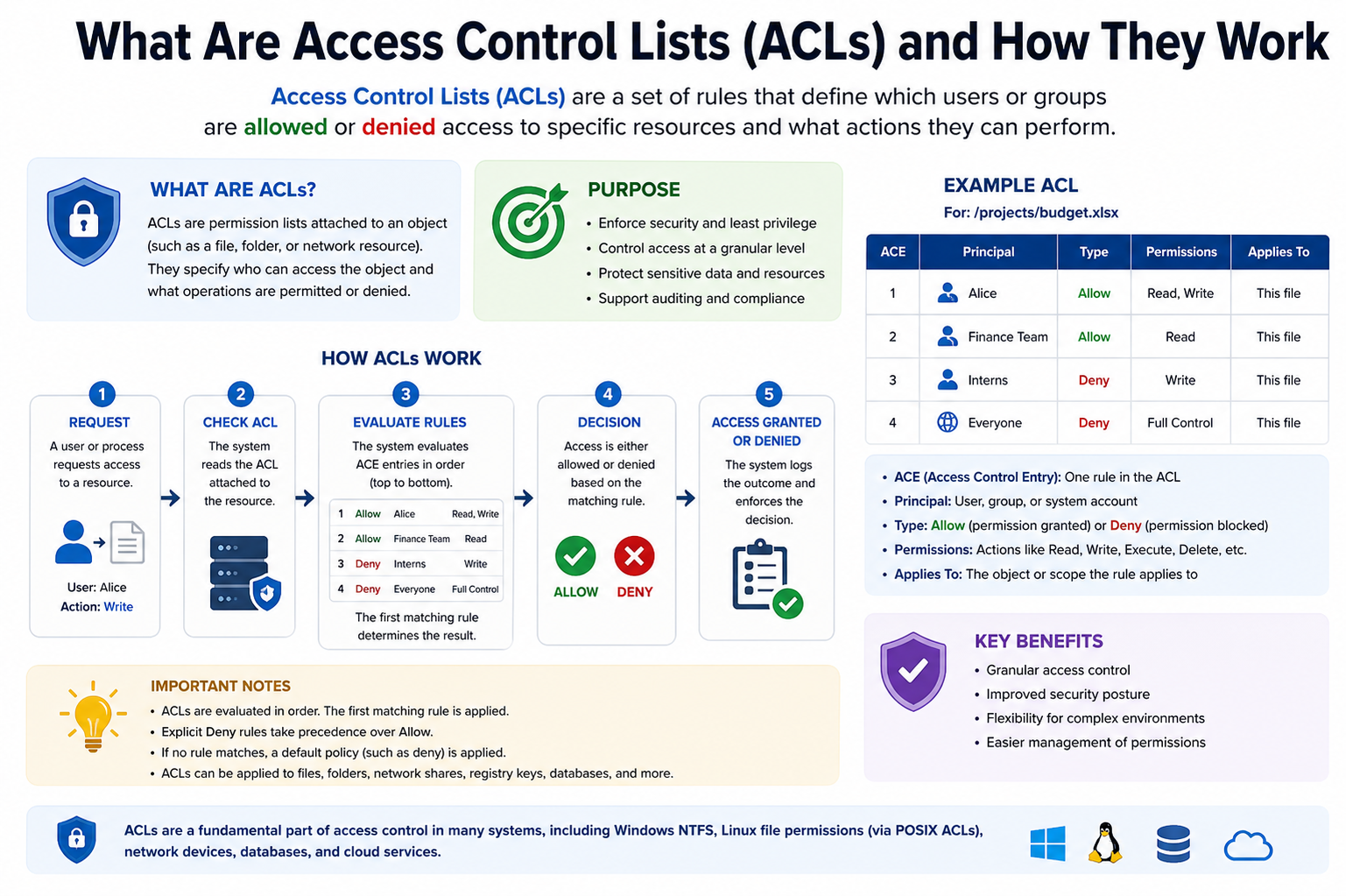
To understand how ACLs operate, it is important to break down their internal structure. An ACL is essentially a collection of entries, where each entry defines a specific rule. These entries are evaluated whenever access to a resource is requested. Each rule typically includes an identity component and a permission component.
The identity component specifies who the rule applies to. This could be a single user, a group of users, or even a system process. The permission component defines what actions are allowed or denied. These actions can include reading data, writing or modifying data, executing programs, or deleting resources.
What makes ACLs powerful is the ability to combine multiple entries into a single list. This allows administrators to define complex permission structures without needing to create separate systems for each resource. Instead, all rules are centralized in one logical structure attached directly to the resource.
ACLs can be associated with many types of objects. In file systems, they control access to files and directories. In networking, they regulate traffic flow between devices. In applications, they manage user roles and feature access. Despite these different contexts, the underlying principle remains the same: evaluate identity against rules and determine access.
How Access Evaluation Works in ACLs
When a request is made to access a resource, the system begins the process of evaluating the ACL associated with that resource. This evaluation is typically performed in a sequential manner, meaning the system checks each rule one by one until a match is found.
The first step in this process is identity verification. The system determines who or what is making the request. This could involve checking user credentials, process identifiers, or network source information. Once the identity is confirmed, the system compares it against the entries in the ACL.
If a matching entry is found, the system applies the corresponding permission rule. This may either allow the requested action or deny it. In many implementations, denial rules take priority to ensure maximum security. If no matching rule is found, the system often defaults to denying access, as a precautionary measure.
This evaluation process ensures that every access attempt is explicitly checked against security policies. It eliminates ambiguity and ensures consistent enforcement of rules across the system.
Types of Access Control Lists
ACLs can be categorized based on how they are implemented and what they control. One of the most common distinctions is between file system ACLs and network ACLs.
File system ACLs are used in operating systems to control access to files and directories. They define which users or groups can read, write, modify, or execute specific files. This type of ACL is essential for protecting sensitive data stored on local or shared systems.
Network ACLs, on the other hand, are used in networking environments to control traffic flow. They determine which packets are allowed to enter or leave a network based on criteria such as IP address, protocol type, or port number. This helps prevent unauthorized access and protects internal networks from external threats.
There are also more advanced ACL models that incorporate dynamic conditions or context-aware rules. These systems can adjust permissions based on factors such as time of access, location, or device type. While more complex, they provide a higher level of security and adaptability.
Role of Permissions in ACL Systems
Permissions are the foundation of any ACL system. They define what actions are allowed or restricted for a given identity. In most systems, permissions are divided into basic categories such as read, write, execute, and delete.
Read permission allows a user to view the contents of a resource without making changes. Write permission allows modification of existing data or creation of new data. Execute permission allows running a program or script. Delete permission allows removal of a resource entirely.
These permissions can be combined in different ways to create customized access levels. For example, one user may only have read access to a file, while another user may have full control over it. This flexibility is what makes ACLs highly adaptable to different security requirements.
Permissions are not only assigned to individuals but also to groups. Group-based permissions simplify management by allowing administrators to assign rules to multiple users at once. This reduces complexity and ensures consistency across large systems.
Inheritance and Propagation in ACLs
In many systems, ACLs support the concept of inheritance. This means that permissions defined at a higher level can automatically apply to lower-level resources. For example, if a folder has specific permissions, those permissions may be inherited by all files within that folder.
Inheritance simplifies administration by reducing the need to manually assign permissions to every individual resource. However, it also requires careful management to avoid unintended access. If not properly configured, inherited permissions can lead to security gaps.
Propagation refers to how ACL rules are applied across related resources. When changes are made to a parent resource, those changes can propagate to child resources. This ensures consistency but must be controlled to prevent unwanted overrides.
Decision Priority and Rule Conflicts
One of the most important aspects of ACL behavior is how conflicts between rules are resolved. In complex systems, it is possible for multiple rules to apply to the same request. In such cases, the system must determine which rule takes priority.
Most ACL systems follow a deny-over-allow approach, meaning that if any rule explicitly denies access, that denial overrides any permission that allows access. This ensures a more secure default behavior.
Rule order can also play a role in decision-making. In some systems, rules are evaluated from top to bottom, and the first matching rule is applied. In others, all rules are evaluated, and the most restrictive result is enforced.
Understanding how conflicts are resolved is essential for designing effective ACL policies. Poorly structured rules can lead to unintended access or unnecessary restrictions.
Security Importance of ACLs in Modern Systems
ACLs are a critical component of modern cybersecurity strategies. They help enforce access boundaries, protect sensitive information, and reduce the risk of unauthorized actions. Without ACLs, systems would be vulnerable to uncontrolled access and potential exploitation.
By implementing ACLs, organizations can ensure that users only have access to the data and systems necessary for their roles. This reduces the attack surface and limits the potential impact of security breaches.
ACLs also support compliance with regulatory standards that require strict access control measures. Many industries rely on ACLs to meet legal and operational security requirements.
In addition to external threats, ACLs also help prevent internal misuse. Even authorized users are restricted to specific actions, reducing the likelihood of accidental or intentional damage.
Challenges in Managing ACL Systems
Despite their effectiveness, ACLs can become complex to manage in large environments. As the number of users and resources increases, maintaining clear and efficient rule sets becomes more difficult.
One common challenge is rule redundancy, where multiple entries define similar permissions. This can lead to confusion and inefficiency. Another challenge is misconfiguration, which can either grant excessive permissions or block legitimate access.
Scalability is also a concern. In very large systems, ACL evaluation can introduce performance overhead if not optimized properly. Administrators must balance security with efficiency to ensure smooth system operation.
Proper planning, regular audits, and clear policy design are essential for maintaining effective ACL systems over time.
Advanced Behavior of ACL Evaluation in Real Systems
In more complex environments, Access Control Lists do not simply act as static rule checkers. They often operate within layered security frameworks where multiple ACLs may apply to a single access request. This can happen when resources are nested, such as files inside directories or services inside network segments. In such cases, the system must evaluate permissions at different levels and combine the results to reach a final decision.
This layered evaluation ensures that security is not dependent on a single point of control. Instead, multiple checkpoints reinforce each other. For example, even if a user has permission at the file level, they may still be restricted by a higher-level directory rule. This hierarchical structure strengthens overall security by preventing isolated misconfigurations from creating vulnerabilities.
In distributed systems, ACLs may also be evaluated across multiple machines or services. Each component can maintain its own ACL rules while still participating in a unified access control strategy. This requires consistent synchronization of policies to ensure that permissions remain aligned across the entire system.
Explicit and Implicit Deny Logic in ACLs
One of the most important design principles in ACL systems is the distinction between explicit and implicit deny rules. An explicit deny occurs when a rule clearly states that access is not allowed for a specific identity. An implicit deny occurs when no rule exists to grant access, resulting in a default rejection.
Most secure systems rely heavily on implicit deny behavior as a safety mechanism. This means that unless access is explicitly granted, it is automatically denied. This approach reduces the risk of accidental exposure of sensitive resources.
Explicit deny rules are even more powerful because they override any allow permissions that might otherwise exist. This ensures that critical resources can be protected even in complex permission structures where multiple rules might conflict.
Understanding this logic is essential when designing ACL policies, because incorrect assumptions about rule priority can lead to unintended access or over-restriction.
Group-Based Access Control in ACL Systems
While individual user permissions are important, ACL systems become significantly more efficient when group-based access control is introduced. Instead of assigning permissions to each user separately, users are organized into groups based on roles, responsibilities, or departments.
Each group is then assigned a set of permissions within the ACL. When a user makes an access request, the system checks both individual and group memberships to determine the final access decision. This layered identity evaluation simplifies administration and reduces redundancy in rule definitions.
Group-based ACLs are especially useful in large organizations where users frequently join, leave, or change roles. Instead of modifying multiple ACL entries, administrators only need to update group memberships, and permissions automatically adjust accordingly.
However, group-based control also introduces complexity when users belong to multiple groups. In such cases, conflicting permissions must be resolved using predefined priority rules.
ACLs in File System Security
In file systems, ACLs play a crucial role in controlling access to data stored on disks or cloud storage platforms. Each file or directory can have its own ACL defining who can read, modify, execute, or delete its contents.
Unlike simpler permission models, file system ACLs allow multiple users and groups to have different levels of access to the same file. This enables fine-grained control over sensitive data, ensuring that only authorized users can interact with specific files.
Directory-level ACLs often influence all files contained within them through inheritance. This means that if a folder is restricted, all files inside it may automatically inherit those restrictions unless explicitly overridden.
File system ACLs are particularly important in multi-user environments, where data isolation is necessary to prevent unauthorized access between users sharing the same system.
ACLs in Network Security Systems
In networking environments, ACLs are used to control traffic flow between devices, networks, and services. These ACLs operate by inspecting incoming and outgoing data packets and determining whether they match defined rules.
Network ACLs typically evaluate parameters such as source IP address, destination IP address, protocol type, and port number. Based on these attributes, the system decides whether to allow or block the traffic.
This mechanism is essential for protecting internal networks from external threats. By carefully defining ACL rules, administrators can restrict access to sensitive servers, limit exposure of services, and control communication between network segments.
Network ACLs are often deployed at routers, firewalls, and gateway devices, making them a first line of defense in cybersecurity architecture.
Order of Evaluation and Rule Matching Strategy
The order in which ACL rules are evaluated plays a significant role in determining the final access decision. In many systems, rules are processed sequentially from top to bottom, and the first matching rule is applied immediately.
This approach makes rule ordering extremely important. A misconfigured rule placed too early in the list can unintentionally override more specific permissions defined later.
Other systems use a cumulative evaluation strategy, where all applicable rules are checked before making a decision. In such cases, the most restrictive rule often takes precedence.
Regardless of the method used, consistent rule design is critical to ensuring predictable behavior. Poorly structured ACLs can lead to confusion and security gaps.
Performance Considerations in ACL Processing
As systems scale, ACL evaluation can become a performance concern. Each access request may require multiple rule checks, especially in environments with large and complex ACL lists.
To address this, many systems implement optimization techniques such as caching frequently used permissions or grouping similar rules together. These optimizations reduce the number of comparisons required during evaluation.
Efficient ACL design also plays a role in performance. Minimizing redundant rules and organizing entries logically can significantly improve access decision speed.
In high-traffic systems, even small inefficiencies in ACL processing can accumulate and impact overall system performance.
Role-Based Access Control vs ACL-Based Systems
While ACLs provide direct permission assignment to users and groups, they are often compared with role-based access control systems. In role-based models, permissions are assigned to roles rather than directly to users or resources.
ACLs offer more granular control because they define permissions at the resource level. However, this can make them more complex to manage in large environments.
Role-based systems simplify administration by grouping permissions into roles, but they may lack the fine-grained flexibility of ACLs. In many modern systems, both models are combined to balance control and manageability.
This hybrid approach allows organizations to benefit from the strengths of both systems while reducing their individual weaknesses.
Security Auditing and Monitoring of ACLs
Regular auditing of ACLs is essential for maintaining a secure environment. Over time, permissions can become outdated, overly permissive, or misaligned with current organizational needs.
Auditing involves reviewing ACL entries to ensure that only appropriate users and groups have access to resources. It also helps identify redundant or conflicting rules that may weaken security.
Monitoring tools can track access attempts and detect unusual patterns, such as repeated denied requests or unauthorized access attempts. This information can be used to refine ACL policies and improve security posture.
Without regular auditing, ACL systems can gradually drift away from their intended security model, creating hidden vulnerabilities.
Common Misconfigurations in ACL Systems
One of the most frequent issues in ACL management is misconfiguration. This can occur when rules are incorrectly defined, leading to either excessive access or unnecessary restrictions.
Overly broad permissions are particularly dangerous because they can expose sensitive data to unintended users. On the other hand, overly strict rules can disrupt system functionality and prevent legitimate access.
Another common issue is inconsistent rule application across different systems or environments. This can create gaps in security coverage and lead to unpredictable behavior.
Careful planning, documentation, and testing are essential to avoid these problems and ensure that ACL systems function as intended.
Importance of ACLs in Modern Cybersecurity Architecture
In today’s digital environments, ACLs remain a fundamental component of security architecture. They provide the first layer of defense by controlling access at the resource level.
When combined with other security mechanisms such as authentication, encryption, and intrusion detection, ACLs contribute to a comprehensive security framework.
Their ability to enforce precise access rules makes them indispensable in environments where data protection and system integrity are critical.
Real-World Applications of ACLs Across Systems
Access Control Lists are not limited to a single type of environment; they are widely implemented across many areas of computing and networking. In enterprise systems, ACLs are used to manage access to shared resources such as databases, file servers, and cloud storage platforms. They ensure that employees only interact with the information relevant to their responsibilities, reducing the risk of accidental or intentional data exposure.
In cloud computing environments, ACLs are often integrated into storage services to control access to objects such as files, backups, and application data. Each object can have its own ACL defining which users, applications, or services are allowed to interact with it. This becomes especially important in multi-tenant systems where multiple organizations share the same infrastructure but must remain isolated from one another.
In operating systems, ACLs are deeply embedded into file security mechanisms. They control how users interact with system files, application data, and configuration settings. This ensures that critical system components are protected from unauthorized modification, which could otherwise compromise system stability.
In networking devices such as routers and firewalls, ACLs are used to regulate traffic flow between different network segments. By defining which types of traffic are allowed or blocked, administrators can control access to internal systems and protect networks from external threats.
Dynamic Nature of Modern ACL Systems
Modern ACL implementations are no longer static. In many systems, permissions can change dynamically based on context, environment, or policy updates. This allows ACLs to adapt to evolving security requirements without requiring manual reconfiguration for every change.
For example, in some systems, access may depend on time-based rules, where users are only allowed to access certain resources during specific hours. In other cases, access may depend on location, device type, or network security level.
This dynamic behavior makes ACLs more powerful but also more complex to manage. It requires continuous monitoring to ensure that changes in conditions do not unintentionally grant or restrict access.
Automation tools are often used to manage dynamic ACL updates, especially in large-scale environments where manual updates would be inefficient or error-prone.
Conflict Resolution in Complex ACL Structures
As ACL systems grow in size, conflicts between rules become more common. These conflicts occur when multiple rules apply to the same access request but define different outcomes. Resolving these conflicts requires a clear and consistent policy framework.
In many systems, priority is given to more specific rules over general ones. For example, a rule targeting a specific user may override a broader group rule. This ensures that precise configurations take precedence over general assumptions.
Another common approach is the use of explicit deny rules, which override any allow permissions. This ensures that critical restrictions are always enforced, even if other rules suggest otherwise.
Some advanced systems use scoring or weighting mechanisms, where each rule contributes to a final decision based on its priority level. This allows for more flexible but also more complex decision-making processes.
Scalability Challenges in Large ACL Environments
As organizations grow, the number of users, devices, and resources increases significantly. This growth directly impacts the complexity of ACL management. Large ACL lists can become difficult to maintain, understand, and audit.
One major challenge is rule explosion, where the number of ACL entries grows rapidly due to the need for specific permissions across many resources. This can lead to redundancy and inefficiency in rule evaluation.
Another challenge is consistency. Ensuring that ACL rules remain consistent across multiple systems and environments requires careful coordination. Without consistency, users may experience different access levels depending on the system they are using.
Performance can also degrade in large ACL systems if rule evaluation is not optimized. This is especially important in high-traffic environments where access requests occur frequently and must be processed quickly.
To address these challenges, organizations often adopt structured permission models, regular audits, and automated policy management tools.
ACL Management Best Practices
Effective ACL management requires careful planning and disciplined execution. One of the most important practices is minimizing unnecessary complexity. Simpler ACL structures are easier to understand, maintain, and troubleshoot.
Another key practice is regularly reviewing and updating ACL rules. Over time, user roles change, systems evolve, and outdated permissions can accumulate. Regular audits help ensure that access rights remain aligned with current requirements.
It is also important to follow the principle of least privilege, ensuring that users only receive the minimum level of access necessary to perform their tasks. This reduces the potential impact of security breaches and limits the spread of unauthorized actions.
Documentation plays a critical role in ACL management. Clear records of why specific rules exist help administrators understand the system and make informed decisions when changes are required.
Security Risks Associated with Poor ACL Design
Improperly designed ACL systems can introduce significant security risks. One of the most common risks is over-permissioning, where users are granted more access than they actually need. This can lead to accidental data modification or exposure of sensitive information.
Another risk is under-permissioning, where users are unable to perform necessary tasks due to overly restrictive rules. While this may seem safer, it can disrupt operations and lead to inefficiencies.
Misconfigured ACL inheritance can also create hidden vulnerabilities. If permissions are unintentionally propagated to sensitive resources, it may expose data that should remain restricted.
Inconsistent rule enforcement across systems can further increase risk, as attackers may exploit differences in access control between environments.
Evolution of ACL Systems in Modern Architecture
ACL systems have evolved significantly from simple permission lists to highly advanced security frameworks. Early implementations were relatively basic, focusing on simple read and write permissions. Modern systems now support complex rule sets, conditional access, and integration with identity management systems.
This evolution has been driven by the increasing complexity of computing environments. As systems became more distributed and interconnected, traditional access control methods were no longer sufficient.
Today, ACLs are often integrated with centralized identity systems, allowing for unified management of user permissions across multiple platforms. This integration improves consistency and reduces administrative overhead.
In addition, modern ACL systems are increasingly combined with behavioral analytics and machine learning techniques to detect unusual access patterns and improve security decision-making.
Importance of ACLs in Data Protection and Compliance
In many industries, ACLs play a crucial role in meeting regulatory and compliance requirements. Regulations often require strict control over who can access sensitive data, how it is used, and how it is protected.
ACLs help organizations enforce these requirements by providing detailed control over access rights. This ensures that only authorized individuals can view or modify regulated data.
They also support auditing and reporting processes by maintaining clear records of access rules and changes. This documentation is often required during compliance reviews and security audits.
Without proper ACL implementation, organizations may struggle to meet legal obligations and could face penalties or reputational damage.
Future Trends in ACL Development
The future of ACL systems is likely to involve greater automation, intelligence, and integration. As systems become more complex, manual management of access rules will become increasingly difficult.
Automated policy generation and adjustment based on user behavior and system context are expected to play a larger role. This will help reduce administrative burden and improve accuracy in access control decisions.
There is also a growing trend toward combining ACLs with identity-based and attribute-based access control models. This hybrid approach allows for more flexible and context-aware security policies.
As cybersecurity threats continue to evolve, ACL systems will remain a critical component of defense strategies, adapting to new challenges while maintaining their core function of controlling access to resources.
Integration of ACLs with Identity Management Systems
Modern Access Control Lists are rarely used in isolation. They are increasingly integrated with identity management systems that handle authentication and user lifecycle management. These systems ensure that user identities are verified before any ACL evaluation takes place, creating a two-layer security approach where authentication confirms who the user is, and ACLs determine what that user is allowed to do.
This integration improves both security and efficiency. When a user is added, modified, or removed from the identity system, their access rights automatically reflect those changes across all connected resources. This reduces the risk of orphaned accounts or outdated permissions remaining active in the system.
In enterprise environments, identity providers often synchronize with ACL systems across multiple applications and services. This centralized approach ensures consistency in access control policies and reduces administrative overhead.
Relationship Between ACLs and Authentication Mechanisms
While ACLs control authorization, they depend heavily on authentication mechanisms to function correctly. Authentication verifies the identity of a user or system, while ACLs determine the level of access granted to that identity.
Without proper authentication, ACLs would have no reliable way of distinguishing between legitimate users and unauthorized entities. This is why secure systems always implement strong authentication methods such as passwords, tokens, certificates, or multi-factor authentication before applying ACL rules.
Once authentication is complete, ACLs take over the decision-making process. This separation of responsibilities ensures a structured security model where identity verification and permission enforcement are handled independently but work together seamlessly.
Context-Aware Access Control Enhancements
Traditional ACLs rely primarily on static rules based on identity and resource type. However, modern systems increasingly incorporate contextual information to refine access decisions. This includes factors such as user location, device security status, time of access, and network environment.
Context-aware ACLs allow systems to make more intelligent decisions. For example, a user may be granted full access when working from a secure corporate network but restricted access when connecting from an unknown or unsecured location.
This adaptive approach improves security by reducing the likelihood of unauthorized access in unusual or high-risk situations. It also enhances flexibility by allowing legitimate users to maintain productivity under varying conditions.
Audit Trails and Logging in ACL Systems
Audit trails are an essential component of ACL-based security frameworks. Every access attempt, whether successful or denied, can be recorded in system logs. These logs provide a detailed history of how resources are being accessed and by whom.
This information is critical for security analysis, compliance reporting, and incident investigation. If a security breach occurs, audit logs can help trace the sequence of events leading up to the incident and identify the source of unauthorized activity.
Logging also helps administrators detect unusual behavior patterns, such as repeated access attempts to restricted resources or unexpected changes in permission usage. These insights can be used to strengthen ACL policies and improve overall system security.
Automation in ACL Management
As systems scale, manual management of ACLs becomes increasingly impractical. Automation plays a key role in modern access control systems by reducing administrative workload and improving accuracy.
Automated tools can generate, update, and validate ACL rules based on predefined policies or real-time system changes. For example, when a new employee joins an organization, automation can assign appropriate access rights based on their role without manual intervention.
Similarly, when an employee changes roles or leaves the organization, automated systems can immediately update or revoke access permissions. This reduces the risk of outdated or excessive permissions remaining active.
Automation also helps in detecting and correcting misconfigurations, ensuring that ACL rules remain consistent and aligned with organizational policies.
ACLs in Virtualized and Cloud Environments
Virtualization and cloud computing have significantly expanded the role of ACLs. In these environments, resources are often dynamic, scalable, and distributed across multiple physical and virtual systems.
ACLs are used to control access to virtual machines, storage volumes, containers, and cloud-based applications. Each resource can have its own set of rules, allowing fine-grained control over highly flexible environments.
In cloud systems, ACLs are often integrated with broader security frameworks that include encryption, identity federation, and network segmentation. This layered approach ensures that even in highly distributed systems, access remains tightly controlled.
Because cloud environments are constantly changing, ACLs must be highly adaptable. Automation and policy-based management are especially important in maintaining consistent security across rapidly scaling infrastructures.
Multi-Tenant Security and ACL Isolation
In multi-tenant environments, multiple organizations or users share the same underlying infrastructure while requiring strict isolation from one another. ACLs play a crucial role in maintaining this separation.
Each tenant is assigned its own set of access rules that define what resources they can access and how those resources can be used. These rules ensure that one tenant cannot accidentally or intentionally access another tenant’s data.
Strong ACL isolation is essential for maintaining trust in shared systems. It ensures that despite shared infrastructure, each tenant’s environment remains logically separated and secure.
Performance Optimization Techniques for ACL Systems
Efficient ACL processing is essential in high-performance systems. As the number of rules increases, evaluating every entry for each access request can become resource-intensive.
To improve performance, systems often use indexing techniques that organize ACL rules based on user identity or resource type. This reduces the number of comparisons required during evaluation.
Caching is another common optimization method. Frequently accessed permissions can be stored temporarily, allowing the system to bypass full rule evaluation for repeated requests.
Batch processing and rule consolidation also help reduce complexity by combining similar rules into fewer, more efficient entries.
Human Factors in ACL Misconfiguration
Even though ACLs are technical systems, human error is one of the most common causes of security issues. Misunderstanding rule logic, incorrect prioritization, or accidental permission assignments can all lead to vulnerabilities.
Complex ACL structures increase the likelihood of mistakes, especially in large environments where many administrators are involved. Lack of documentation or inconsistent naming conventions can further complicate management.
Training and standardized procedures are essential to reduce human error. Clear guidelines on how ACLs should be created, modified, and reviewed help maintain system integrity.
Role of ACLs in Zero Trust Architecture
Modern security models increasingly follow the zero trust principle, which assumes that no user or device should be trusted by default, even if they are inside the network perimeter. ACLs play a key role in enforcing this model.
In a zero trust architecture, every access request is evaluated independently, regardless of the user’s location or previous activity. ACLs ensure that permissions are continuously enforced at the resource level.
This approach significantly reduces the risk of lateral movement within a system, where an attacker might attempt to move from one compromised resource to another.
By combining ACLs with continuous verification and strict access policies, organizations can build highly resilient security frameworks.
Long-Term Maintenance of ACL Systems
Maintaining ACL systems over time requires ongoing attention and regular updates. As organizations evolve, so do their access requirements. New applications are introduced, users change roles, and business processes shift.
Without regular maintenance, ACL systems can become outdated and inefficient. Old rules may remain in place long after they are needed, while new requirements may not be properly reflected.
Periodic reviews help ensure that ACLs remain aligned with current operational needs. This includes removing unnecessary rules, updating permissions, and verifying consistency across systems.
A well-maintained ACL system not only improves security but also enhances system performance and usability by reducing unnecessary complexity.
Final Perspective on ACL Importance in Modern Computing
Access Control Lists remain one of the most important building blocks of digital security. Despite the emergence of newer access control models, ACLs continue to play a central role in controlling how users and systems interact with resources.
Their ability to provide precise, flexible, and scalable permission management makes them suitable for a wide range of environments, from small systems to large enterprise infrastructures.
When properly designed and maintained, ACLs contribute significantly to data protection, operational stability, and regulatory compliance.
Conclusion
Access Control Lists remain a fundamental mechanism for enforcing security and managing permissions across modern computing environments. Their core strength lies in their ability to define clear and structured rules that determine who can access specific resources and what actions they are permitted to perform. By evaluating each request against a predefined set of entries, ACLs ensure that access decisions are consistent, predictable, and aligned with organizational security policies.
Throughout their evolution, ACLs have adapted to increasingly complex systems, moving from simple permission models to highly detailed and context-aware frameworks. They are now deeply integrated into operating systems, networks, cloud platforms, and enterprise applications, where they help maintain strict control over sensitive data and critical infrastructure.
Despite their effectiveness, ACLs require careful design, regular maintenance, and continuous monitoring. Poorly configured rules can lead to security vulnerabilities or operational inefficiencies, making proper management essential. When implemented correctly, however, ACLs provide a strong foundation for protecting resources, enforcing least-privilege access, and supporting compliance requirements.
In modern cybersecurity architecture, ACLs continue to play a vital role alongside authentication systems, identity management, and advanced security models. Their simplicity in concept combined with their flexibility in application ensures that they remain a reliable and essential component of secure system design.