Modern computer networks are the backbone of digital communication, enabling devices across homes, offices, and global infrastructures to exchange data seamlessly. Every message sent, video streamed, or file downloaded depends on a structured system of network components working together in the background. Among these components, switches, routers, and firewalls form the core foundation that determines how data moves, where it goes, and how securely it is handled.
Understanding these devices is essential for anyone exploring networking because they define both performance and protection. Without them, communication between devices would be slow, disorganized, and highly vulnerable to threats. Each component serves a unique purpose, but their combined function creates a stable and efficient digital environment.
Understanding the Role of Switches in Detail
Switches are often considered the internal traffic managers of a local network. Their primary responsibility is to connect multiple devices within the same network and ensure that data is delivered accurately and efficiently. Unlike basic connectivity devices that simply broadcast information, switches use intelligent forwarding methods to send data only where it is needed.
When a device sends information through a switch, the switch reads the destination address embedded in the data packet. It then identifies the correct recipient device and forwards the packet directly to it. This selective communication reduces unnecessary data traffic and prevents network congestion, allowing multiple devices to communicate simultaneously without interference.
Switches operate primarily at the data link layer of networking, which allows them to recognize hardware addresses known as MAC addresses. Each device connected to a switch has a unique MAC address, enabling precise delivery of information. Over time, switches build a table that maps these addresses to specific ports, making future data transfers even faster.
In addition to basic switching functions, modern switches often include advanced features such as VLAN support, which allows networks to be divided into smaller logical segments. This improves both performance and security by isolating traffic within specific groups of devices. Managed switches can also provide monitoring tools, allowing administrators to analyze network behavior and optimize performance.
How Switches Improve Network Efficiency
One of the most important advantages of switches is their ability to reduce unnecessary data collisions. In older networking systems, devices often shared the same communication channel, leading to frequent data clashes. Switches eliminate this problem by creating dedicated communication paths between devices.
This dedicated communication ensures that each device has full bandwidth available when transmitting data. As a result, network speed increases significantly, especially in environments with heavy traffic such as offices or data centers. Switches also support full-duplex communication, meaning data can be sent and received simultaneously, further enhancing performance.
Another efficiency benefit comes from the way switches manage traffic distribution. Instead of sending data to all connected devices, they intelligently forward it only to the intended recipient. This reduces overall network load and improves response times for applications that require real-time communication.
Introduction to Routers and Their Function
Routers serve a very different purpose compared to switches. While switches operate within a local network, routers are responsible for connecting multiple networks together. Their most common role is to link a private network, such as a home or office, to the internet.
Routers analyze data packets and determine the best path for them to reach their destination across different networks. This process involves reading IP addresses, which function as unique identifiers for devices across the internet. Unlike MAC addresses used by switches, IP addresses operate at a broader level, allowing communication between distant systems.
A router maintains a routing table that stores information about available paths and network destinations. When data is received, the router consults this table to decide where the packet should be forwarded. This decision-making process ensures that data travels efficiently through complex global networks.
How Routers Manage Internet Connectivity
Routers play a crucial role in enabling internet access for multiple devices within a single location. When several devices connect to the same router, it assigns local IP addresses to each one. This process, known as network address management, allows devices to share a single internet connection while maintaining individual identities within the local network.
One of the key technologies used by routers is NAT, which allows multiple devices to access the internet using a single public IP address. This not only conserves IP address space but also adds a layer of security by masking internal device addresses from external networks.
Routers also manage traffic flow between devices and the internet, ensuring that data is directed efficiently. For example, when a user requests a website, the router determines the fastest route to retrieve that information and sends it back to the requesting device.
Advanced Functions of Routers
Modern routers are far more advanced than simple traffic directors. They often include built-in security features, wireless connectivity, and traffic management tools. Quality of service settings allow routers to prioritize certain types of data, such as video calls or streaming, ensuring smooth performance even under heavy network load.
Routers can also provide parental controls, guest networks, and firewall capabilities. These features make them central hubs for both connectivity and security in modern digital environments. In enterprise networks, high-performance routers are capable of handling massive amounts of data while maintaining stability and low latency.
Introduction to Firewalls and Network Protection
Firewalls are essential components responsible for protecting networks from unauthorized access and potential cyber threats. They act as security checkpoints that monitor all incoming and outgoing data and decide whether it should be allowed or blocked based on predefined rules.
A firewall can be implemented as hardware, software, or a combination of both. Hardware firewalls are typically integrated into network devices such as routers, while software firewalls are installed directly on individual computers or servers. Both serve the same purpose of controlling access and preventing malicious activity.
Firewalls analyze data packets by examining their source, destination, and content. If a packet matches a known threat pattern or violates security rules, it is blocked immediately. This helps prevent attacks such as hacking attempts, malware infections, and unauthorized data access.
How Firewalls Strengthen Network Security
The primary strength of a firewall lies in its ability to enforce security policies consistently. Organizations define specific rules that determine which types of traffic are allowed or denied. These rules can be based on IP addresses, ports, protocols, or application types.
Firewalls also provide logging and monitoring capabilities, allowing administrators to track suspicious activity and respond quickly to potential threats. This visibility is crucial in identifying attack patterns and improving overall network defense strategies.
Another important function of firewalls is segmentation. By dividing networks into secure zones, firewalls limit the spread of potential attacks. Even if one part of a network is compromised, other sections remain protected due to strict access controls.
Types of Firewalls in Modern Networks
Different types of firewalls are used depending on the level of security required. Packet-filtering firewalls are the most basic type, inspecting individual data packets and allowing or blocking them based on simple rules. Stateful inspection firewalls go further by analyzing the state of active connections, providing more intelligent filtering.
More advanced systems include proxy firewalls, which act as intermediaries between users and external networks. These firewalls hide internal network details and add an extra layer of security. Next-generation firewalls combine multiple security features, including deep packet inspection and intrusion prevention systems, to provide comprehensive protection.
Interaction Between Switches, Routers, and Firewalls
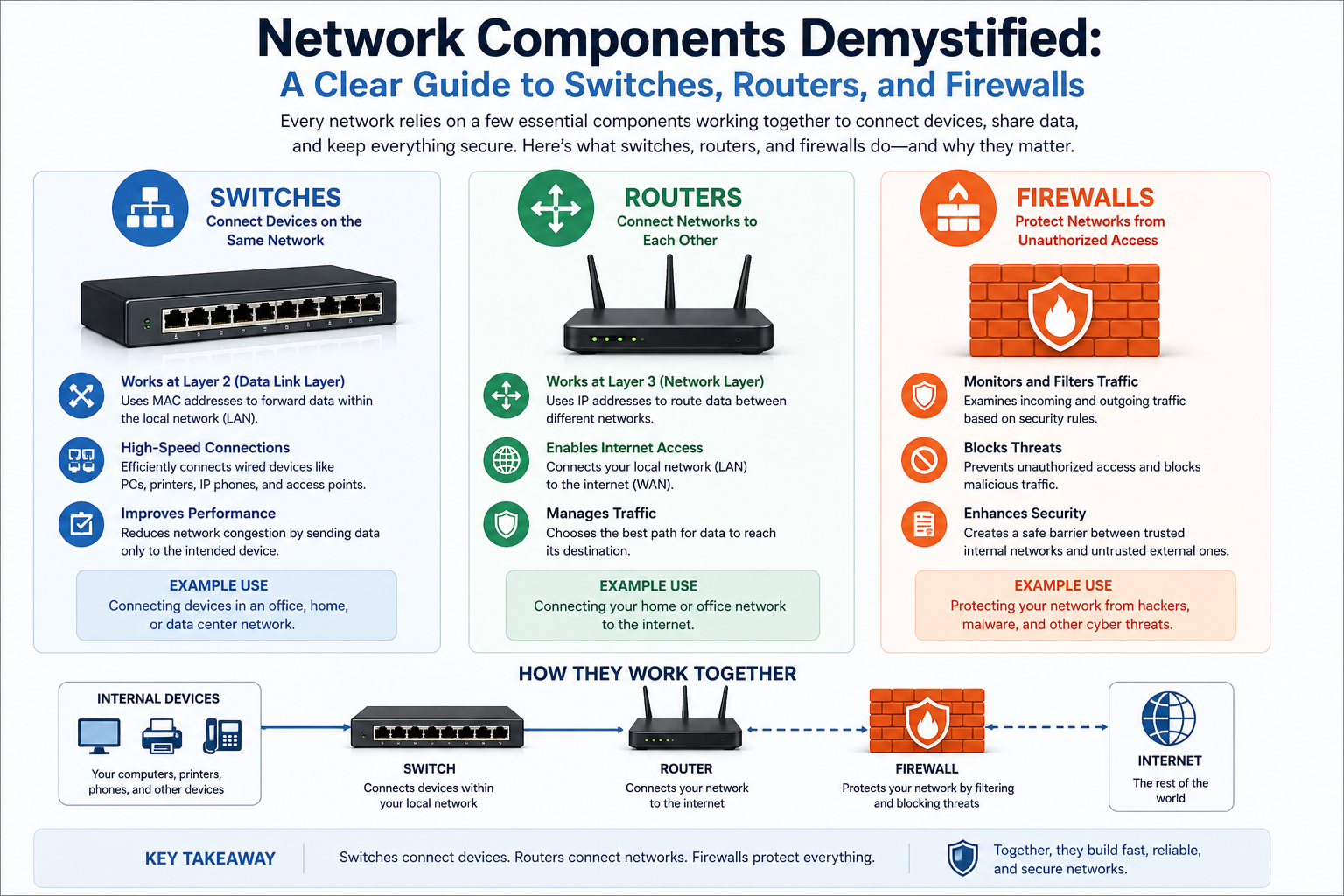
Although switches, routers, and firewalls perform different functions, they work together to create a complete networking system. Switches handle internal communication within a local network, routers manage communication between different networks, and firewalls protect the entire system from external threats.
For example, when a device sends data to the internet, the switch first directs the data to the router. The router then determines the best path to send the data externally. Before the data leaves the network, the firewall checks it to ensure it complies with security rules. This layered approach ensures both efficiency and protection.
Importance of Network Design and Architecture
The way switches, routers, and firewalls are arranged in a network significantly impacts performance and security. A well-designed network ensures smooth data flow, minimal delays, and strong protection against threats.
In small networks, a single router with built-in switching and firewall features may be sufficient. However, larger organizations require more complex architectures involving multiple switches, specialized routers, and dedicated firewall systems. This scalability allows networks to handle increased traffic and more advanced security requirements.
Proper network design also ensures redundancy, meaning that if one component fails, others can take over to maintain connectivity. This is especially important in critical systems where downtime can lead to significant disruptions.
Expanding the Role of Switches in Larger Networks
In larger and more complex network environments, switches become far more than simple device connectors. They evolve into highly structured traffic managers that support thousands of devices simultaneously. Enterprise-grade switches are designed to handle massive data loads while maintaining stability and speed, making them essential in corporate networks, data centers, and educational institutions.
One of the key developments in advanced switching technology is the ability to create multiple virtual networks within a single physical switch. This allows organizations to separate departments or user groups without needing separate hardware. For example, finance, HR, and IT departments can operate on isolated network segments even though they share the same switching infrastructure.
Switches also support link aggregation, which combines multiple physical connections into a single logical connection. This increases bandwidth and provides redundancy, ensuring that network performance remains stable even if one connection fails. In environments where uptime is critical, such as banking systems or cloud infrastructure, this feature is extremely valuable.
Another important aspect of modern switches is their ability to support Power over Ethernet, allowing devices such as IP cameras, wireless access points, and VoIP phones to receive both power and data through a single cable. This reduces wiring complexity and simplifies network installation while maintaining efficiency.
Switching Techniques and Data Handling Methods
Switches use different techniques to manage how data is forwarded across a network. One of the most common methods is store-and-forward switching, where the switch receives the entire data packet, checks it for errors, and then forwards it to the destination. This method ensures accuracy but may introduce slight delays.
Another method is cut-through switching, where the switch begins forwarding data as soon as it reads the destination address. This reduces latency and improves speed, making it suitable for environments where fast communication is more important than error checking.
There is also fragment-free switching, which combines elements of both methods by checking the initial portion of the packet before forwarding it. Each switching technique is used depending on the performance and reliability requirements of the network.
Switches continuously learn and update their internal tables as devices connect and communicate. This dynamic learning process allows them to adapt to changes in network structure without manual configuration, making them highly efficient in evolving environments.
Deep Dive into Router Functionality
Routers operate as intelligent decision-makers in networking systems, directing traffic between different networks with precision. Unlike switches, which focus on local communication, routers must understand complex global routing structures and make decisions based on multiple factors such as distance, congestion, and network policies.
Each router maintains a routing table that contains information about available routes, including direct connections and learned paths from neighboring routers. These tables are constantly updated through routing protocols, which allow routers to exchange information and adapt to network changes.
Routers use these protocols to calculate the most efficient path for data transmission. If one route becomes congested or unavailable, the router automatically selects an alternative path, ensuring uninterrupted communication. This adaptability is one of the key reasons why the internet remains stable despite its vast and constantly changing structure.
Routing Protocols and Path Selection
Routing protocols play a major role in how routers communicate with each other. These protocols determine how routing information is shared and how decisions are made about data paths. Some protocols focus on distance, while others consider factors like speed, reliability, or network load.
Interior routing protocols are used within a single organization or autonomous system, helping manage internal traffic efficiently. Exterior routing protocols, on the other hand, manage data exchange between different organizations or internet service providers, making them essential for global connectivity.
Routers continuously evaluate multiple paths and choose the best one based on predefined metrics. This ensures that data is delivered in the most efficient way possible, reducing delays and improving overall network performance.
Security and Management Features in Routers
Modern routers are not only responsible for directing traffic but also for enforcing security policies. Many routers include built-in firewall capabilities that filter incoming and outgoing traffic based on specific rules. This helps prevent unauthorized access and protects internal networks from external threats.
Routers can also implement access control lists, which define which devices or users are allowed to access certain resources. This adds an additional layer of security and ensures that sensitive data remains protected.
Network administrators can also configure routers to monitor traffic patterns and detect unusual behavior. This is particularly useful in identifying potential security breaches or performance issues before they escalate.
Understanding Firewalls in Greater Depth
Firewalls have evolved significantly over time, becoming one of the most critical components of network security. Their primary function is to establish a controlled boundary between trusted internal networks and untrusted external environments.
At a basic level, firewalls examine data packets and compare them against predefined security rules. However, advanced firewalls go much further by analyzing the behavior of traffic, identifying patterns, and detecting anomalies that may indicate malicious activity.
Firewalls can operate at multiple layers of the network model, allowing them to inspect data at different levels of depth. This multi-layered approach provides stronger protection against sophisticated cyber threats that attempt to bypass simple filtering methods.
Next-Generation Firewall Capabilities
Next-generation firewalls integrate traditional firewall functions with advanced security features such as intrusion detection, application awareness, and deep packet inspection. These capabilities allow them to identify not only where data is coming from but also what type of data is being transmitted.
For example, a next-generation firewall can distinguish between video streaming, file sharing, and web browsing traffic, and apply different security rules to each type. This level of control allows organizations to enforce detailed security policies and optimize network performance simultaneously.
These firewalls also use threat intelligence systems that continuously update security definitions based on global threat data. This ensures that networks remain protected against emerging cyber threats without requiring manual updates.
Firewall Deployment in Network Architecture
Firewalls can be placed at different points within a network depending on the level of security required. Perimeter firewalls are installed at the edge of a network to protect against external threats. Internal firewalls are used to segment different parts of a network and control communication between them.
In more advanced architectures, multiple firewalls are deployed in layers, creating a defense-in-depth strategy. This means that even if one layer is compromised, additional layers continue to provide protection.
Firewalls are also commonly used in cloud environments, where they help secure virtual networks and protect data stored across distributed systems. Their flexibility makes them suitable for both traditional and modern computing environments.
Integration of Network Components in Real Systems
In real-world networks, switches, routers, and firewalls are tightly integrated to ensure seamless communication and security. Data typically flows through multiple stages before reaching its destination, with each component performing a specific function.
Within a local environment, switches handle communication between devices. When data needs to leave the network, it is passed to a router, which determines the best external path. Before leaving or entering the network, firewalls inspect the data to ensure it meets security standards.
This structured flow ensures that networks remain both efficient and secure. Each component complements the others, creating a balanced system that supports high-speed communication while minimizing risks.
Performance Optimization in Network Systems
Optimizing network performance involves careful configuration of switches, routers, and firewalls. Network administrators must balance speed, reliability, and security to achieve the best results.
Switch configurations may include optimizing port settings, managing VLANs, and monitoring traffic loads. Routers may be adjusted to prioritize certain types of traffic or improve routing efficiency. Firewalls must be carefully configured to avoid blocking legitimate traffic while still preventing threats.
Performance monitoring tools are often used to analyze network behavior and identify bottlenecks. This data helps administrators make informed decisions about upgrades and adjustments, ensuring that the network continues to operate efficiently.
Real World Network Architecture and How Components Fit Together
In practical environments, networks are not built using a single switch, router, or firewall. Instead, they are structured in layers, where each layer performs a specific function to ensure smooth communication and strong protection. This layered approach is what allows modern systems to support everything from small office setups to massive global infrastructures.
At the core of most networks, switches form the internal backbone. They connect end devices such as computers, printers, and servers, ensuring that internal communication remains fast and efficient. Above this layer, routers act as gateways, connecting the internal network to external systems such as the internet or other remote networks. Firewalls are positioned strategically to monitor and control traffic entering or leaving these boundaries.
This structured design ensures that data does not flow randomly but follows a controlled path. Each device in the architecture has a defined role, and together they create a predictable and secure communication environment.
Hierarchical Network Design and Its Importance
Large-scale networks often use a hierarchical design model, which organizes the network into different levels. The access layer is where end devices connect, and switches operate heavily at this level. The distribution layer manages routing decisions and policy enforcement, while the core layer handles high-speed data transfer between different parts of the network.
This structure helps distribute network load efficiently and prevents bottlenecks. It also improves scalability, allowing organizations to expand their networks without redesigning the entire system. Each layer can be upgraded independently based on performance needs, making the system highly flexible.
Hierarchical design also enhances fault isolation. If a problem occurs in one section of the network, it does not necessarily affect the entire system. This separation improves reliability and reduces downtime in critical environments.
Data Flow Journey Across Network Components
Understanding how data travels through a network helps clarify the role of each component. When a user sends a request, such as opening a website, the data first travels through a switch if the destination is within the local network. If the request needs to reach an external server, the switch forwards it to a router.
The router then determines the best path for the data to travel across different networks. Before the data leaves the local environment, the firewall checks it against security rules to ensure it is safe and authorized. Once verified, the data is transmitted across the internet, passing through multiple routers until it reaches its destination.
The response follows a similar path in reverse, passing through firewalls, routers, and switches before reaching the user. This continuous cycle happens in milliseconds, making global communication feel instantaneous.
Advanced Switching in Enterprise Environments
In enterprise networks, switches are not limited to simple forwarding tasks. They often include advanced capabilities such as traffic prioritization, security filtering, and network segmentation. These features allow organizations to control how data flows within different departments or systems.
One important concept in enterprise switching is network segmentation, where a large network is divided into smaller isolated sections. This improves both performance and security by limiting unnecessary traffic between unrelated systems. It also reduces the impact of network issues by containing them within specific segments.
High-end switches also support redundancy features that ensure continuous operation even in the event of hardware failure. If one connection path fails, traffic is automatically rerouted through another path without disrupting communication.
Router Intelligence and Adaptive Decision Making
Routers are often described as the intelligent decision-makers of a network because they continuously evaluate multiple factors before forwarding data. These factors include distance, congestion levels, link reliability, and network policies.
This adaptive decision-making process allows routers to respond dynamically to changes in network conditions. For example, if a particular route becomes slow due to heavy traffic, the router can automatically select an alternative path that offers better performance.
Routers also play a key role in load balancing, distributing traffic evenly across multiple paths to prevent congestion. This ensures that no single route becomes overwhelmed, maintaining consistent network performance even under heavy usage.
Security Layers Provided by Firewalls in Depth
Firewalls act as the first line of defense in network security, but their role extends far beyond simple filtering. They operate as multi-layered security systems that inspect traffic at different levels of depth and complexity.
At the basic level, firewalls examine packet headers to determine whether traffic should be allowed or blocked. At more advanced levels, they analyze the actual content of the data being transmitted. This deeper inspection allows them to detect hidden threats that may not be visible through basic filtering.
Firewalls also enforce policies based on user roles and network zones. For example, employees in one department may have access to certain resources that are restricted for others. This controlled access ensures that sensitive data remains protected while still allowing necessary communication.
Intrusion Detection and Prevention Systems Integration
Modern firewalls are often integrated with intrusion detection and prevention systems. These systems continuously monitor network traffic for suspicious activity and take immediate action when threats are detected.
Intrusion detection systems focus on identifying potential threats and alerting administrators, while intrusion prevention systems go a step further by actively blocking malicious traffic. Together, they provide real-time protection against attacks such as malware, unauthorized access attempts, and data breaches.
These systems rely on threat intelligence databases that are constantly updated with new information about emerging cyber threats. This allows firewalls to recognize and respond to new attack patterns quickly.
Cloud Networking and Virtualization of Components
With the rise of cloud computing, traditional networking components such as switches, routers, and firewalls have also evolved into virtual forms. Virtual switches and routers perform the same functions as physical devices but operate within software-defined environments.
This virtualization allows networks to be created, modified, and scaled without requiring physical hardware changes. It also enables faster deployment of services and more efficient resource utilization.
Virtual firewalls are widely used in cloud environments to protect virtual machines and applications. They provide the same level of security as physical firewalls but offer greater flexibility in managing distributed systems.
Software Defined Networking and Centralized Control
Software defined networking introduces a new approach where network control is centralized and managed through software instead of individual hardware devices. This allows administrators to control switches, routers, and firewalls from a single interface.
In this model, the network becomes more programmable and adaptable. Changes can be made quickly across the entire system without manually configuring each device. This improves efficiency and reduces the complexity of managing large networks.
Centralized control also enhances visibility, allowing administrators to monitor traffic patterns, detect issues, and optimize performance in real time.
Scalability Challenges in Modern Networks
As networks grow, they face several challenges related to scalability. Increased traffic volume, more connected devices, and higher security demands require continuous upgrades to infrastructure.
Switches must handle larger numbers of connections, routers must process more complex routing decisions, and firewalls must analyze higher volumes of security data. Without proper planning, these demands can lead to performance degradation.
To address these challenges, networks are designed with scalability in mind from the beginning. Modular hardware, virtual components, and distributed architectures allow systems to expand without losing efficiency.
Future Trends in Networking Technologies
The future of networking is moving toward greater automation, intelligence, and integration. Artificial intelligence is increasingly being used to optimize routing decisions, detect security threats, and manage network performance automatically.
Self-healing networks are also emerging, where systems can detect failures and automatically reconfigure themselves to maintain operation. This reduces downtime and improves reliability.
Another major trend is the expansion of edge computing, where data processing occurs closer to the source of data rather than centralized servers. This reduces latency and improves performance for real-time applications.
Network Troubleshooting and Common Issues in Real Systems
Even well-designed networks can experience performance issues, and understanding how switches, routers, and firewalls behave is essential for diagnosing problems. One of the most common issues in switching environments is network congestion, where too many devices attempt to communicate at the same time. This can slow down data transfer and create delays in communication. Misconfigured VLANs or faulty switch ports can also lead to devices being unable to communicate properly within the same network.
Routers can also become a source of problems when routing tables are incorrect or outdated. If a router does not have accurate path information, data packets may be sent in inefficient directions or dropped entirely. This can result in slow internet performance or complete loss of connectivity to certain networks. In larger systems, routing loops can occur if multiple routers continuously send data back and forth without reaching a destination, wasting bandwidth and reducing efficiency.
Firewalls, while essential for security, can sometimes block legitimate traffic if rules are too strict or improperly configured. This can prevent users from accessing websites, applications, or internal services. On the other hand, overly permissive firewall settings can expose the network to security risks. Proper configuration and regular monitoring are necessary to maintain a balance between security and accessibility.
Performance Monitoring and Optimization Techniques
To maintain efficient network performance, continuous monitoring of switches, routers, and firewalls is essential. Network administrators use monitoring tools to track bandwidth usage, device health, error rates, and traffic patterns. This helps identify bottlenecks and predict potential failures before they impact users.
Switch performance can be optimized by ensuring proper load distribution across ports and avoiding overuse of specific links. Upgrading to higher-speed switches or implementing link aggregation can significantly improve throughput in high-demand environments.
Router optimization involves refining routing protocols, adjusting priority settings, and balancing traffic loads across multiple paths. In many cases, improving routing efficiency leads to noticeable improvements in internet speed and stability.
Firewall optimization focuses on refining security rules to ensure that only necessary traffic is inspected in detail. Reducing unnecessary rule complexity can improve processing speed while still maintaining strong protection.
Network Reliability and Redundancy Strategies
Reliability is a key requirement in modern networks, especially in environments where downtime can lead to financial or operational losses. To achieve this, redundancy is built into all major components, including switches, routers, and firewalls.
Redundant switching paths ensure that if one connection fails, traffic can be automatically redirected through an alternative route. This prevents interruptions in internal communication. Similarly, redundant routers are often deployed so that if one gateway fails, another can immediately take over internet traffic handling.
Firewall redundancy ensures continuous security protection even if a device fails. In many systems, firewalls operate in active-passive pairs, where one handles traffic while the other remains on standby, ready to take over instantly if needed.
These redundancy strategies are essential for maintaining high availability and ensuring that networks remain operational under all conditions.
Real World Applications of Network Components
Switches, routers, and firewalls are used in almost every digital environment today. In corporate offices, switches connect employee devices, routers manage internet access, and firewalls protect sensitive business data. In educational institutions, these components support online learning platforms, internal communication systems, and administrative networks.
In healthcare environments, reliable networking is critical for accessing patient records, managing medical devices, and supporting telemedicine services. Here, security and uptime are especially important, making firewalls and redundant routers essential components.
In cloud computing environments, these devices exist in virtualized forms and support global applications used by millions of users. Streaming services, online gaming platforms, and financial systems all depend on high-performance networking infrastructure built on these foundational components.
The Evolution of Networking Technology
Networking technology has evolved significantly from simple wired connections to complex, intelligent systems. Early networks relied on basic hubs that broadcast data to all devices, leading to inefficiency and congestion. The introduction of switches revolutionized internal communication by enabling targeted data delivery.
Routers expanded networking capabilities by connecting multiple networks together, enabling the growth of the internet. Firewalls introduced a critical security layer, protecting networks from increasing cyber threats as global connectivity expanded.
Today, these components are no longer standalone devices but part of integrated systems that combine hardware and software intelligence. Automation, virtualization, and artificial intelligence are transforming how networks operate, making them faster, more secure, and easier to manage.
Future of Switches, Routers, and Firewalls
The future of networking is moving toward greater automation and intelligence. Switches are becoming more programmable, allowing dynamic adjustments based on traffic conditions. Routers are evolving into intelligent systems capable of predicting network congestion and optimizing paths before issues occur.
Firewalls are also becoming more advanced, using machine learning to detect unusual behavior patterns and respond to threats in real time. Instead of relying solely on predefined rules, future firewalls will adapt dynamically to new attack methods.
Another major development is the integration of all networking components into unified systems managed through centralized platforms. This reduces complexity and allows networks to respond more quickly to changes in demand or security conditions.
Edge computing and 5G technology are also reshaping networking by bringing processing power closer to users. This reduces latency and improves performance for applications such as autonomous vehicles, smart cities, and real-time communication systems.
Conclusion
Switches, routers, and firewalls form the essential foundation of all modern communication systems. Each plays a unique and critical role: switches manage internal device communication, routers connect different networks and guide data across global paths, and firewalls protect systems from unauthorized access and cyber threats.
When combined, these components create a structured, efficient, and secure networking environment that supports everything from simple home internet usage to complex global infrastructures. Their continuous evolution reflects the growing demands of digital communication, where speed, security, and reliability are more important than ever.
Understanding how these devices work not only provides technical insight but also reveals how deeply interconnected the modern digital world truly is.