MAC spoofing is a technique used in computer networking where a device changes its hardware identity to appear as another device on the network. Every device that connects to a network has a unique identifier, and MAC spoofing involves altering this identifier for various purposes. These purposes may include bypassing security controls, increasing privacy, or in some cases performing unauthorized or malicious actions.
To understand MAC spoofing clearly, it is important to first understand what a MAC address is, how it functions in networking, and why it is so critical in controlling communication between devices.
What Is a MAC Address?
A MAC address, short for Media Access Control address, is a unique identifier assigned to a network interface card in a device. This address is embedded into the hardware by the manufacturer and is used to identify a device at the data link layer of a network.
A MAC address is typically represented in hexadecimal format and consists of six groups of two characters. These characters can include numbers from 0 to 9 and letters from A to F. An example format looks like this: F0:0F:F0:0F:00:FF.
Each network-capable device may have multiple MAC addresses. For example, a computer may have one MAC address for its Wi-Fi adapter and a different one for its Ethernet adapter. Even though they belong to the same device, each interface is treated separately on a network.
The MAC address is divided into two main parts. The first portion is known as the Organizationally Unique Identifier, which identifies the manufacturer of the device. The second portion is the device-specific identifier, which is intended to be unique for each network interface produced by that manufacturer.
This structure allows network systems to identify not only the device itself but also the company that produced it. Network administrators often use MAC addresses to monitor devices, apply security rules, and manage network traffic effectively.
Role of MAC Addresses in Networking
MAC addresses play a fundamental role in how devices communicate within local networks. When data is transmitted across a network, it is broken into frames that include both source and destination MAC addresses. These addresses ensure that data reaches the correct device.
At the data link layer, switches use MAC addresses to build tables that map devices to specific ports. This allows efficient forwarding of data only to the intended recipient instead of broadcasting it to all connected devices.
Without MAC addresses, devices would not be able to identify each other on a local network, making communication impossible. They are essential for Wi-Fi networks, Ethernet connections, and many industrial and embedded systems.
MAC addresses are also used in network security systems. Some networks rely on MAC-based filtering, where only approved devices are allowed to connect. Others use authentication systems that verify a device’s identity based on its MAC address before granting access.
What Is MAC Spoofing?
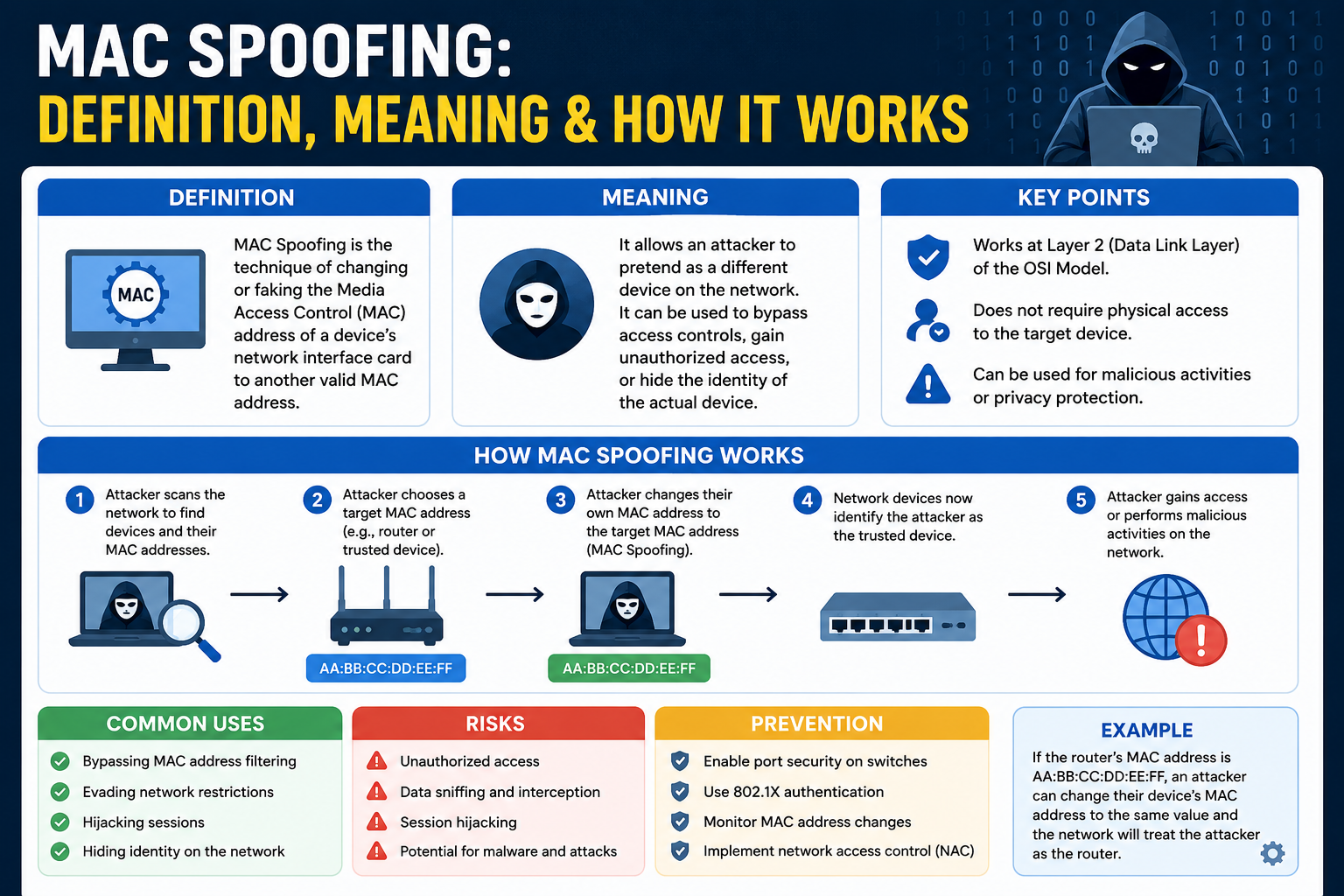
MAC spoofing is the process of changing or falsifying the MAC address of a network interface. Instead of using the original hardware-assigned address, a device is configured to present a different MAC address to the network.
This altered identity can be used to impersonate another device, bypass restrictions, or avoid tracking. In technical terms, the device is using a locally assigned address instead of its original burned-in address provided by the manufacturer.
When MAC spoofing is performed, the network perceives the device as a completely different system. This is because most network systems rely on MAC addresses as a form of identity verification at the local level.
The process of spoofing can be done through software settings or specialized tools that allow users to manually assign a new MAC address to a network interface. Once changed, the network treats the device according to the new identity.
How MAC Spoofing Works
MAC spoofing works by replacing the original hardware address stored in a network interface with a custom value. When a device sends data across a network, it includes this new MAC address in its communication frames.
Switches and routers then update their tables based on this modified identity. From the perspective of the network, the spoofed MAC address appears legitimate as long as it follows valid formatting rules.
There are several ways MAC spoofing can be implemented. Some operating systems allow users to temporarily change their MAC address through configuration settings. In other cases, third-party tools are used to permanently or temporarily alter the address.
The spoofed address can be randomly generated or deliberately chosen to match another known device on the network. This makes it possible for a device to impersonate another system and potentially gain access to restricted resources.
Why MAC Spoofing Is Used
MAC spoofing is not always used for harmful purposes. In some cases, it serves legitimate needs such as privacy protection. Since MAC addresses can be used to track devices across networks, changing the address can help reduce tracking and increase anonymity.
In corporate environments, network administrators may use MAC spoofing during testing or troubleshooting. It allows them to simulate different devices without needing physical hardware changes.
However, MAC spoofing is also commonly associated with unauthorized access attempts. If a network restricts access based on MAC addresses, spoofing can be used to bypass these restrictions and gain entry.
Some users also use MAC spoofing to avoid network bans or restrictions imposed on their original device identity.
Security Risks of MAC Spoofing
Although MAC spoofing can have legitimate uses, it also introduces significant security risks, especially when used maliciously.
One major risk is unauthorized network access. If a network relies only on MAC-based filtering, an attacker can easily bypass this protection by spoofing an allowed MAC address.
Another risk is identity impersonation. A malicious user can impersonate a trusted device on the network, gaining access to sensitive data or internal systems.
MAC spoofing also plays a role in more advanced attacks such as man-in-the-middle scenarios. In such cases, an attacker intercepts communication between two devices by pretending to be one of them.
This allows the attacker to monitor, modify, or redirect data without the knowledge of the legitimate users.
Wireless networks are particularly vulnerable because attackers can create fake access points that mimic legitimate ones. Devices may unknowingly connect to these rogue networks, allowing attackers to capture sensitive information.
Denial of service attacks can also be performed using spoofed MAC addresses. By overwhelming a network with fake identities, attackers can disrupt normal communication and prevent legitimate users from accessing services.
Limitations of MAC-Based Security
One of the key weaknesses exposed by MAC spoofing is the reliance on MAC addresses as a security mechanism. While MAC filtering may provide basic access control, it is not sufficient as a standalone security measure. MAC addresses were originally designed for identification and communication at the local network level, not for authentication or security enforcement. Because of this, they can be easily observed, copied, and altered using widely available tools and system settings.
When attackers exploit MAC spoofing, they take advantage of this design limitation. Once a legitimate device’s MAC address is discovered, it can be cloned and reused on another system, allowing unauthorized access without triggering strong security alerts in poorly configured networks. This makes MAC-based security particularly weak in environments where sensitive data or critical infrastructure is involved.
Another issue is that MAC filtering does not scale well in modern networks. In large organizations with hundreds or thousands of devices, maintaining and updating MAC address lists becomes difficult and error-prone. It also does not account for dynamic environments where devices frequently join and leave the network.
For these reasons, MAC filtering should only be considered a supplementary control rather than a primary security layer. Stronger authentication methods such as multi-factor authentication, certificate-based access, and network segmentation provide far more reliable protection against unauthorized access and spoofing attempts.
Because MAC addresses can be easily changed, they do not provide strong authentication. This makes them unsuitable for environments that require high levels of security.
Modern networks typically use more advanced authentication methods that combine multiple layers of verification, including credentials, certificates, and encrypted communication.
MAC addresses are still useful for identification and traffic management, but they should not be relied upon for securing sensitive systems.
Preventing and Mitigating MAC Spoofing Risks
Organizations can reduce the risks associated with MAC spoofing by implementing stronger security practices.
One approach is to use multi-layer authentication systems that verify both the device and the user. This makes it harder for attackers to gain access even if they spoof a MAC address.
Network monitoring tools can also help detect unusual behavior, such as duplicate MAC addresses or unexpected changes in device identity.
Encrypted communication protocols provide another layer of protection by ensuring that even if traffic is intercepted, it cannot be easily read or modified.
Regular network audits and strict access controls also help reduce the chances of unauthorized devices gaining entry.
Conclusion
MAC spoofing is a technique that alters a device’s network identity by changing its MAC address. While it can be used for legitimate purposes such as privacy protection and testing, it also introduces serious security risks when used maliciously.
Understanding how MAC addresses function and how they can be manipulated is essential for anyone working with computer networks. Although MAC-based controls are useful for basic device identification, they should never be relied upon as the sole security mechanism.
As network threats continue to evolve, stronger authentication methods and layered security approaches are necessary to protect systems from spoofing attacks and unauthorized access.