Capture the Flag (CTF) cybersecurity competitions are one of the most effective and engaging ways to build practical hacking and security skills. Unlike traditional learning methods that focus heavily on theory, CTFs challenge participants to solve real-world inspired problems under time pressure. These challenges simulate scenarios in web security, cryptography, reverse engineering, binary exploitation, forensics, and general problem-solving. Preparing for a CTF is not just about learning tools or memorizing techniques; it is about developing a mindset that combines curiosity, analytical thinking, persistence, and structured learning.
A strong preparation strategy requires both technical knowledge and mental readiness. Many beginners assume that success in CTFs depends only on advanced hacking skills, but in reality, consistent practice, familiarity with common patterns, and the ability to research efficiently are equally important. This guide explores a complete approach to preparing for CTF competitions in a practical and structured way.
Understanding the Nature of CTF Competitions
Before diving into preparation, it is important to understand how CTFs work. Most CTFs are designed as a series of challenges, each assigned a point value based on difficulty. Participants or teams solve these challenges to find hidden flags, which are usually strings of text that confirm completion. The team or individual with the highest score wins.
CTFs typically fall into two categories. Jeopardy-style CTFs present a list of independent challenges across multiple domains. Attack-defense CTFs, on the other hand, involve defending your own systems while exploiting others. Beginners usually start with jeopardy-style competitions because they allow flexible learning and do not require real-time system defense.
Understanding the structure of CTFs helps you prioritize skills and manage time effectively during competitions. It also helps reduce confusion when facing unfamiliar problem types.
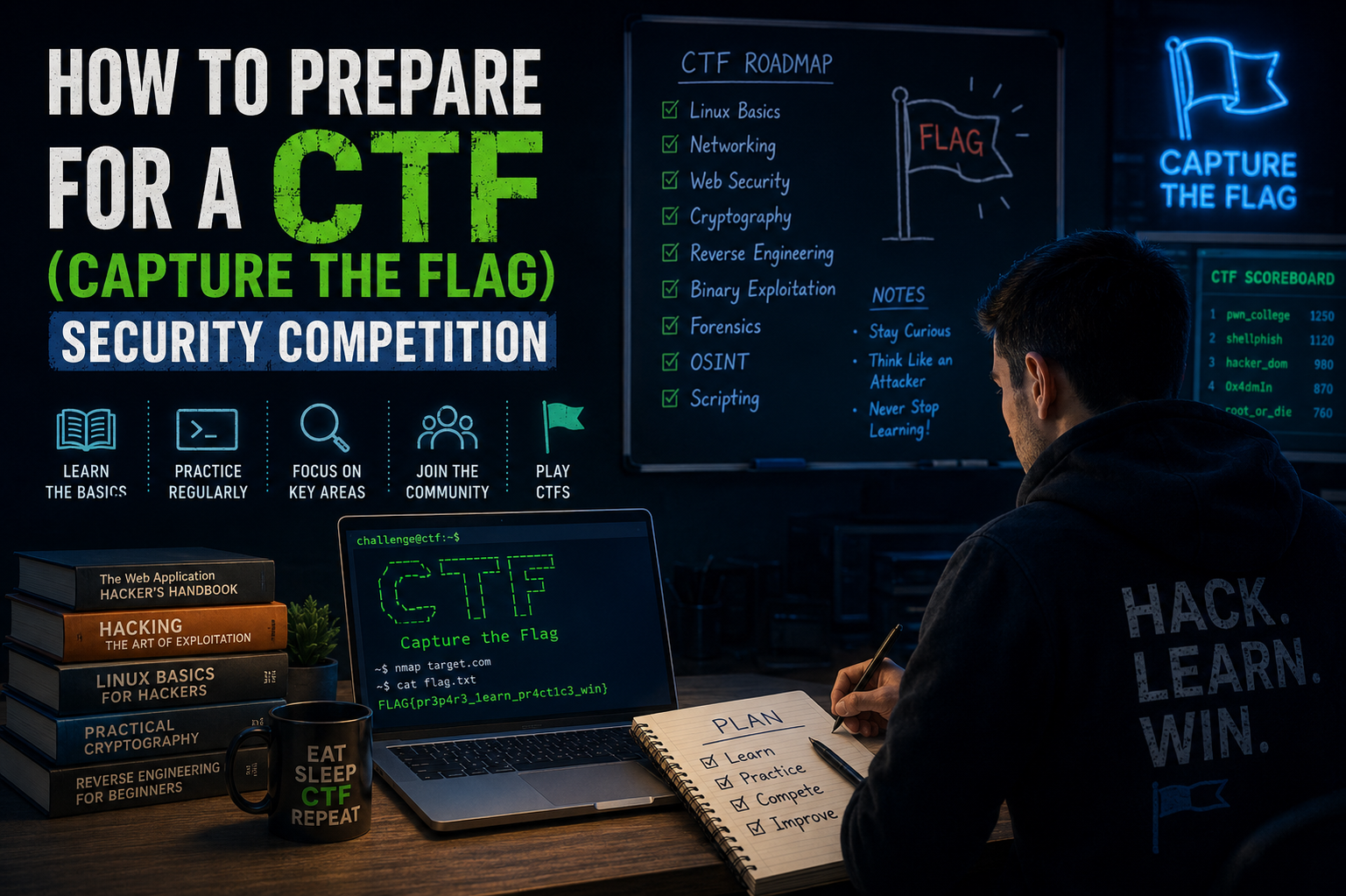
Building a Strong Cybersecurity Foundation
A solid foundation in cybersecurity concepts is essential. Without it, even simple challenges can feel overwhelming. Start by understanding how computer systems work at a basic level. Learn how operating systems manage memory, processes, and file systems. Familiarize yourself with how the internet works, including protocols like HTTP, HTTPS, DNS, and TCP/IP.
Networking knowledge is particularly important. Many CTF challenges involve analyzing traffic, identifying vulnerabilities in communication, or manipulating requests. Understanding how data flows between client and server gives you an advantage when tackling web-based challenges.
Basic programming knowledge is also crucial. Python is widely used in CTFs due to its simplicity and powerful libraries. Bash scripting is useful for automation and quick tasks. Understanding at least one low-level language like C can also help with binary exploitation challenges.
Mastering Problem-Solving Skills
CTFs are less about memorization and more about problem-solving. Each challenge is designed to test your ability to think critically and creatively. Developing a structured approach to solving problems is essential.
When faced with a challenge, start by carefully reading the description. Many clues are hidden in the wording. Next, identify the category of the problem. Is it web-based, cryptographic, forensic, or reverse engineering? Categorization helps narrow down the tools and techniques needed.
Break the problem into smaller parts. Instead of trying to solve everything at once, isolate components and test them individually. Document your findings as you go. This prevents confusion and helps you track progress.
It is also important to develop persistence. Many CTF problems are designed to mislead or frustrate participants. The ability to stay calm and continue experimenting is often what separates successful participants from others.
Learning Web Security Fundamentals
Web security is one of the most common categories in CTF competitions. It involves identifying vulnerabilities in web applications. Common topics include SQL injection, cross-site scripting, command injection, file inclusion, and authentication bypass.
Understanding how web applications process input is key. Learn how browsers interact with servers, how cookies work, and how sessions are managed. Practice inspecting HTTP requests and responses using browser developer tools or interception tools.
A good preparation strategy is to study common vulnerability patterns. For example, many SQL injection challenges involve manipulating input fields to alter database queries. Similarly, cross-site scripting challenges often require injecting scripts into vulnerable inputs.
Practicing web challenges regularly helps you recognize patterns quickly during competitions, saving valuable time.
Exploring Cryptography Basics
Cryptography challenges involve encoding, decoding, and breaking encrypted messages. These problems often test your understanding of classical and modern encryption techniques.
Start by learning simple encoding methods like Base64, hexadecimal, and URL encoding. Then move on to classical ciphers such as Caesar cipher, Vigenère cipher, and substitution ciphers. Many beginner CTF challenges are based on these concepts.
As you advance, learn about modern cryptographic concepts like RSA, AES, hashing algorithms, and public-key encryption. Understanding how encryption works helps you identify weaknesses in implementations rather than breaking the algorithms themselves.
In many cases, cryptography challenges are more about pattern recognition and logical deduction than brute force computation.
Introduction to Reverse Engineering
Reverse engineering involves analyzing compiled programs to understand how they work. This category is often considered advanced but is extremely rewarding once mastered.
Start by learning basic programming in C, as many binaries are written in it. Understand how programs are compiled and executed. Learn about assembly language basics, especially x86 or x64 architecture.
Tools like disassemblers and debuggers are commonly used in reverse engineering. These tools help you inspect program behavior without source code.
Begin with simple programs that perform basic operations like string comparison or password validation. Gradually move to more complex binaries with obfuscation and anti-debugging techniques.
Reverse engineering improves your understanding of how software behaves at a low level, which is valuable across all cybersecurity fields.
Understanding Binary Exploitation
Binary exploitation is one of the most challenging CTF categories. It involves finding and exploiting vulnerabilities in compiled programs, often related to memory corruption.
Key concepts include buffer overflows, stack and heap memory, return-oriented programming, and format string vulnerabilities. Understanding how memory is allocated and managed is essential.
Start by learning how stack-based memory works. Then practice identifying simple buffer overflow vulnerabilities. Over time, move on to more complex exploitation techniques that involve bypassing security protections.
This area requires patience and practice, but it significantly strengthens your understanding of system-level security.
Forensics and Digital Investigation Skills
Forensics challenges involve analyzing files, images, network traffic, or memory dumps to extract hidden information. These problems simulate real-world digital investigations.
Learn how to inspect different file formats and extract metadata. Practice analyzing network captures to identify suspicious activity. Understanding how data can be hidden or obfuscated is important.
Many forensics challenges require attention to detail. Small clues hidden in images or files can lead to the flag. Tools and techniques help, but careful observation is equally important.
Developing Tool Familiarity
While understanding concepts is important, familiarity with tools is equally valuable. Common tools include network analyzers, disassemblers, debugging tools, and scripting environments.
However, relying only on tools without understanding underlying principles can be limiting. The best approach is to learn both how tools work and when to use them.
Practice using tools in different scenarios so that during competitions, you can quickly select the right one without hesitation.
Practicing Regularly Through Challenges
Consistent practice is one of the most effective ways to improve. Solve challenges regularly across different categories. Start with beginner-friendly problems and gradually increase difficulty.
After solving a challenge, review the solution even if you solved it correctly. This helps you learn alternative approaches and improves efficiency.
It is also helpful to revisit unsolved challenges after gaining more experience. Problems that seemed difficult earlier may become easier later.
Working in Teams and Communication
Many CTF competitions allow team participation. Working in a team introduces collaboration, communication, and task distribution.
Effective teams divide responsibilities based on strengths. For example, one member may focus on web challenges while another handles cryptography. Clear communication helps avoid duplication of effort.
Sharing knowledge within the team also accelerates learning. Explaining solutions to others reinforces your own understanding.
Time Management During Competitions
Time management plays a crucial role in CTF success. Not all challenges are worth equal effort. Sometimes it is better to skip a difficult problem and return later.
Start by solving easier challenges to build momentum and secure initial points. Then move to medium and difficult problems. Avoid spending too much time stuck on a single challenge.
Tracking progress and allocating time wisely helps maximize your overall score.
Common Mistakes to Avoid
Many beginners make similar mistakes. One common mistake is focusing too much on tools without understanding concepts. Another is ignoring basic challenges in favor of difficult ones.
Overcomplicating problems is also a frequent issue. Often, solutions are simpler than they appear. Reading carefully and testing assumptions helps avoid unnecessary complexity.
Lack of documentation during problem-solving can also lead to confusion. Keeping notes helps maintain clarity.
Ethical Mindset and Responsible Learning
CTFs are designed for educational purposes. The skills learned should be used responsibly and ethically. Understanding legal boundaries is important in cybersecurity.
Always ensure that your practice and experimentation occur in safe and authorized environments. Ethical behavior is a core principle of cybersecurity professionals.
Conclusion
Preparing for a Capture the Flag cybersecurity competition is a journey that combines technical learning, problem-solving skills, and consistent practice. It requires patience, curiosity, and a willingness to explore unfamiliar concepts.
Success in CTFs does not come from shortcuts but from steady improvement over time. Building strong foundations in networking, web security, cryptography, reverse engineering, and forensics creates a well-rounded skill set.
Equally important is developing the right mindset. Staying persistent, thinking creatively, and learning from mistakes are key factors in long-term improvement.
With regular practice and structured preparation, anyone can progress from a beginner to a confident CTF participant capable of tackling complex cybersecurity challenges.