The CompTIA CySA+ certification is designed for cybersecurity professionals who focus on detecting, analyzing, and responding to security threats within an organization. The transition from the CS0-002 version to CS0-003 represents a meaningful update that reflects the evolving nature of cyber threats and the tools used to combat them. Rather than being a simple revision, the newer version reshapes how candidates are expected to think and respond in real-world security environments.
The cybersecurity landscape has changed significantly in recent years, with attackers using more sophisticated methods, automation, and cloud-based attack vectors. As a result, the CySA+ certification has been updated to ensure professionals are better prepared for modern challenges. The CS0-003 exam builds on the foundation of CS0-002 but introduces deeper analytical expectations and more realistic operational scenarios.
Evolution of the CySA+ Certification
The CS0-002 version of CySA+ focused heavily on core cybersecurity analysis concepts such as threat detection, vulnerability management, and incident response fundamentals. It provided a strong baseline for security analysts entering the field. However, it was more structured around traditional security environments and less focused on emerging technologies.
With CS0-003, the certification evolves to reflect current industry demands. Modern security operations are heavily influenced by cloud computing, automation, and advanced threat intelligence systems. The updated exam places greater emphasis on interpreting complex data sources, responding to dynamic threats, and using security tools in an integrated manner. This evolution ensures that certified professionals remain relevant in fast-changing environments.
Shift Toward Real-World Security Operations
One of the most significant differences in CS0-003 is its stronger focus on practical, real-world scenarios. Instead of relying primarily on theoretical questions, candidates are now expected to analyze security events as they would occur in a Security Operations Center environment.
This includes evaluating logs, identifying anomalies, correlating events from multiple sources, and determining the appropriate response. The exam encourages critical thinking rather than memorization, requiring candidates to understand how different security tools and processes work together in practice.
CS0-002 introduced scenario-based thinking, but CS0-003 expands it significantly, making it a central part of the exam experience. This shift aligns more closely with job roles such as security analyst, threat intelligence analyst, and SOC engineer.
Expansion of Threat Intelligence and Analysis
Threat intelligence plays a more prominent role in CS0-003 compared to CS0-002. While the earlier version covered basic threat identification and classification, the updated exam explores how analysts interpret threat data from multiple sources.
Candidates are expected to understand indicators of compromise, attack patterns, and adversary behaviors. More importantly, they must be able to connect these elements to real-world attack campaigns. This requires a deeper understanding of how attackers operate over time rather than focusing on isolated incidents.
The updated exam also emphasizes behavioral analysis, which involves studying patterns within systems and networks to detect unusual activity. This approach reflects modern cybersecurity practices where detecting subtle deviations is often more important than identifying known signatures.
Greater Emphasis on Cloud and Hybrid Environments
Another key change in CS0-003 is the increased focus on cloud and hybrid environments. As organizations continue to migrate infrastructure to cloud platforms, security analysts must understand how threats operate in these environments.
CS0-003 introduces more concepts related to cloud security monitoring, identity management, and access control in distributed systems. Candidates are expected to understand how security tools function across on-premises and cloud environments and how to respond to incidents that span both.
CS0-002 included some cloud-related concepts, but they were limited in scope. The updated version recognizes that cloud security is now a core part of cybersecurity operations rather than an optional skill set.
Automation and Security Orchestration
Modern security operations rely heavily on automation, and CS0-003 reflects this shift. Security orchestration, automation, and response tools are now more prominently featured in the exam objectives.
Candidates are expected to understand how automated systems help reduce response times, improve accuracy, and manage large volumes of security data. This includes understanding how automated workflows support incident response and how analysts interact with these systems.
CS0-002 introduced automation concepts at a basic level, but CS0-003 integrates them more deeply into practical scenarios. This ensures that certified professionals are prepared to work in environments where automation plays a critical role in daily operations.
Incident Response Enhancements
Incident response remains a core domain in both versions of CySA+, but CS0-003 enhances its depth and complexity. The updated exam expects candidates to not only follow response procedures but also to evaluate and adapt them based on evolving situations.
This includes identifying the scope of incidents, prioritizing responses, and coordinating actions across different teams. Candidates must also understand how to document incidents effectively and use lessons learned to improve future responses.
CS0-002 focused more on structured incident response steps, while CS0-003 emphasizes adaptability and decision-making under pressure. This reflects real-world environments where incidents rarely follow predictable patterns.
Vulnerability Management Improvements
Vulnerability management is another area that has been refined in CS0-003. While CS0-002 covered vulnerability scanning and basic risk assessment, the updated version places greater emphasis on prioritization and context-based analysis.
Candidates are expected to evaluate vulnerabilities based on exploitability, business impact, and threat intelligence data. This approach ensures that security teams focus on the most critical risks rather than treating all vulnerabilities equally.
CS0-003 also highlights the importance of continuous monitoring and remediation tracking, reflecting modern security practices where vulnerability management is an ongoing process rather than a periodic task.
Security Architecture Awareness
Security architecture concepts have also been expanded in CS0-003. The exam now places greater emphasis on understanding how different security controls interact within an enterprise environment.
This includes network segmentation, endpoint protection, identity management, and data protection strategies. Candidates must understand how these components work together to create a layered defense strategy.
Compared to CS0-002, the updated version requires a more integrated understanding of security architecture rather than isolated knowledge of individual components.
Increased Analytical Thinking Requirements
A major shift in CS0-003 is the increased demand for analytical thinking. Candidates are expected to interpret complex datasets, identify relationships between events, and draw conclusions based on incomplete information.
This reflects the reality of cybersecurity work, where analysts often must make decisions quickly using partial or evolving data. The exam tests the ability to think critically rather than simply recall information.
CS0-002 included analytical elements, but CS0-003 significantly raises the level of complexity and expectation in this area.
Modern Attack Techniques and Evolving Threats
CS0-003 incorporates more coverage of modern attack techniques such as ransomware campaigns, phishing evolution, supply chain attacks, and advanced persistent threats. These topics reflect the current threat landscape more accurately than CS0-002.
Candidates must understand how these attacks are executed, how they evolve over time, and how defenders can detect and mitigate them. This includes recognizing early indicators and understanding attacker motivations and methodologies.
The updated exam ensures that professionals are prepared for threats that are actively used in real-world cyberattacks today.
Improved Alignment with Industry Roles
One of the key goals of CS0-003 is better alignment with actual job roles in cybersecurity. The exam is designed to reflect the responsibilities of security analysts working in SOC environments, threat intelligence teams, and incident response units.
This alignment ensures that certified professionals are job-ready and capable of contributing effectively from day one. CS0-002 provided a strong foundation, but CS0-003 refines this foundation to match current industry expectations more closely.
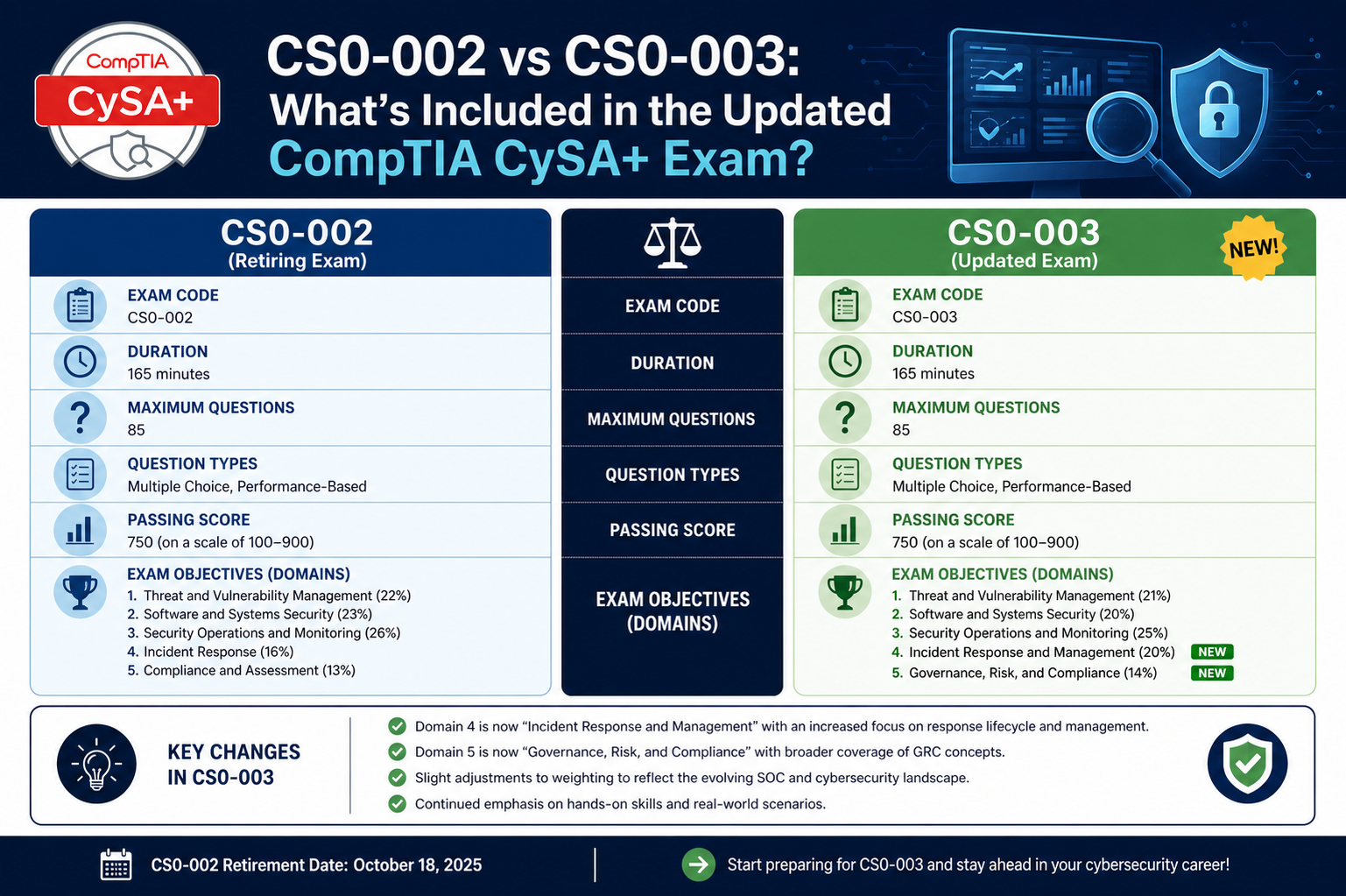
Refinement of Domain Weighting and Structure
In CS0-003, the structure of the CySA+ exam has been refined to better reflect the actual distribution of tasks performed by cybersecurity analysts in real organizations. While CS0-002 already established four main domains, the updated version adjusts the emphasis placed on each area to match modern operational priorities.
Threat management and detection now carry more analytical depth, requiring candidates to go beyond identifying threats and instead focus on understanding their behavior, origin, and potential impact. Vulnerability management is more context-driven, meaning candidates must evaluate risks in relation to business environments rather than treating vulnerabilities as isolated findings.
Incident response continues to remain central, but CS0-003 increases the expectation for adaptive decision-making rather than fixed procedural knowledge. Security architecture is also more integrated, requiring a holistic understanding of how systems, networks, and controls interact under real-world conditions.
More Complex Data Interpretation Requirements
One of the defining characteristics of CS0-003 is the increased complexity in data interpretation. Candidates are expected to analyze logs, alerts, and security event data that may come from multiple tools and platforms.
Instead of straightforward identification questions, the exam now presents layered scenarios where multiple indicators must be correlated to identify a single incident. This requires not only technical knowledge but also logical reasoning and pattern recognition skills.
CS0-002 introduced log analysis at a basic level, but CS0-003 significantly expands this by simulating real SOC environments where data is often noisy, incomplete, or contradictory. Candidates must filter relevant information and prioritize what matters most in a security investigation.
Greater Integration of Threat Hunting Concepts
Threat hunting has become a more visible component in CS0-003. While CS0-002 focused primarily on reactive security analysis, the updated exam introduces more proactive approaches to identifying threats before they fully materialize.
Candidates are expected to understand how security analysts actively search for hidden threats within systems using hypotheses, behavioral patterns, and anomaly detection techniques. This represents a shift from reactive defense to proactive security operations.
Threat hunting in CS0-003 is not just about tools but also about mindset. Candidates must demonstrate the ability to think like an attacker in order to identify weaknesses and suspicious activity that might otherwise go unnoticed.
Enhanced Focus on Detection Engineering Concepts
CS0-003 places more importance on how detection rules and mechanisms are built and refined. Candidates are expected to understand how security tools generate alerts and how those alerts can be tuned to reduce false positives and improve accuracy.
This includes knowledge of detection logic, rule creation, and correlation techniques used in SIEM systems. While CS0-002 introduced SIEM concepts, CS0-003 expands them into practical analytical workflows.
The exam now reflects the reality that security analysts are not just consumers of alerts but also contributors to improving detection systems over time.
Improved Realism in Scenario-Based Questions
The scenarios in CS0-003 are more realistic and layered compared to CS0-002. Instead of simple question-and-answer formats, candidates are presented with detailed security situations that mirror actual incidents in enterprise environments.
These scenarios often involve multiple systems, overlapping alerts, and conflicting data points. Candidates must determine the most likely cause, prioritize response actions, and sometimes even identify what additional information is needed before making a decision.
This approach closely reflects real-world cybersecurity work, where analysts must often make decisions under uncertainty and time pressure.
Increased Importance of Identity and Access Security
Identity and access management concepts are more deeply integrated into CS0-003. With the rise of cloud environments and remote work, identity has become a critical security boundary.
Candidates are expected to understand authentication mechanisms, access control models, privilege escalation risks, and identity-based attack techniques. CS0-002 included these topics, but CS0-003 expands their practical application in modern environments.
This includes scenarios involving compromised credentials, misconfigured permissions, and identity-based lateral movement within networks.
Stronger Emphasis on Endpoint and Behavioral Security
Endpoint security is another area that has gained importance in CS0-003. Modern attacks often begin at the endpoint level, making it essential for analysts to understand endpoint detection and response tools.
Candidates must be familiar with how endpoint telemetry is collected and analyzed to detect suspicious behavior. This includes file execution patterns, process monitoring, and memory-based indicators of compromise.
CS0-002 introduced endpoint security concepts, but CS0-003 integrates them more deeply into incident analysis and threat detection workflows.
Evolution of Risk-Based Thinking
CS0-003 places greater emphasis on risk-based decision making. Instead of treating all security events equally, candidates are expected to evaluate the severity and impact of each situation.
This involves understanding how business context influences security priorities. For example, a low-level vulnerability on a critical system may be more important than a high-level vulnerability on a non-essential system.
CS0-002 introduced risk concepts in a more theoretical way, while CS0-003 requires candidates to apply risk evaluation in practical scenarios.
Improved Coverage of Security Tool Integration
Another important change in CS0-003 is the focus on how different security tools work together. Modern cybersecurity environments rely on interconnected systems such as SIEM, SOAR, EDR, and threat intelligence platforms.
Candidates are expected to understand how these tools exchange data and support each other in detecting and responding to threats. This reflects real-world environments where no single tool operates in isolation.
CS0-002 covered tools individually, but CS0-003 emphasizes integration and workflow between systems.
More Advanced Incident Prioritization Skills
Incident prioritization is more advanced in CS0-003. Candidates must determine not only whether an incident is valid but also how urgent it is and what resources should be allocated to it.
This requires evaluating multiple factors such as asset criticality, threat intelligence, attack severity, and potential business impact. The ability to prioritize effectively is a key skill for cybersecurity analysts in real-world environments.
CS0-002 focused more on identifying and responding to incidents, while CS0-003 emphasizes decision-making under multiple competing priorities.
Greater Emphasis on Continuous Monitoring
Continuous monitoring is another area that has been strengthened in CS0-003. Modern cybersecurity operations require constant visibility into systems, networks, and applications.
Candidates are expected to understand how continuous monitoring tools collect and analyze data in real time to detect anomalies. This includes understanding alert thresholds, baseline behavior, and dynamic risk scoring.
CS0-002 introduced monitoring concepts, but CS0-003 expands them into ongoing operational processes.
Alignment with Modern Security Operations Centers
CS0-003 is closely aligned with how modern Security Operations Centers actually function. SOC environments today rely heavily on automation, real-time data analysis, and collaborative workflows between analysts.
The exam reflects this by focusing on teamwork, communication, and structured response processes. Candidates are expected to understand not only technical analysis but also how security teams coordinate during incidents.
CS0-002 provided a foundation for SOC operations, but CS0-003 brings it closer to real operational maturity.
Preparation Mindset Shift for Candidates
Preparing for CS0-003 requires a different mindset compared to CS0-002. Instead of focusing primarily on memorization of concepts, candidates must develop analytical thinking, pattern recognition, and decision-making skills.
Study approaches that worked for CS0-002 may not be sufficient for CS0-003. Candidates need to engage with practice scenarios, interpret logs, and understand how security tools interact in real environments.
This shift ensures that certified professionals are not only knowledgeable but also capable of performing effectively in real cybersecurity roles.
Strengthened Focus on Adversary Behavior Analysis
CS0-003 places a much stronger emphasis on understanding attacker behavior compared to CS0-002. Instead of only identifying indicators of compromise, candidates are now expected to interpret the intent and strategy behind attacks.
This includes recognizing how attackers move through different stages of an intrusion, from initial access to lateral movement and data exfiltration. The exam expects candidates to connect seemingly unrelated events into a complete attack narrative.
CS0-002 introduced basic attack lifecycle concepts, but CS0-003 expands them into deeper behavioral analysis. This shift helps candidates think more like threat hunters rather than passive observers of security alerts.
More Detailed Coverage of Attack Chains
The concept of attack chains is more developed in CS0-003. Candidates must understand how multiple small actions within a system can form part of a larger coordinated attack.
Instead of analyzing events in isolation, candidates are expected to link them together. For example, a suspicious login, followed by privilege escalation and unusual data access patterns may represent a single coordinated intrusion attempt.
CS0-002 covered attack stages in a linear format, while CS0-003 requires multi-layered interpretation across time and systems.
Expanded Role of Security Analytics
Security analytics plays a larger role in CS0-003, reflecting the industry’s reliance on data-driven decision making. Candidates are expected to interpret large volumes of security data and extract meaningful insights.
This includes identifying trends, recognizing anomalies, and understanding baseline behavior within networks and systems. Analytical thinking is no longer optional but central to the exam structure.
CS0-002 introduced analytics in a limited form, while CS0-003 integrates it deeply into almost every domain of the exam.
Improved Emphasis on False Positive Reduction
One important operational challenge addressed in CS0-003 is the issue of false positives in security monitoring systems. Candidates must understand how excessive alerts can overwhelm analysts and reduce efficiency.
The exam expects candidates to know how tuning detection systems and refining rules can improve signal-to-noise ratio. This includes understanding correlation rules, thresholds, and context-aware alerting.
CS0-002 briefly covered alert management, but CS0-003 treats false positive reduction as a critical operational skill.
Stronger Focus on Collaboration in Security Teams
CS0-003 reflects the collaborative nature of modern cybersecurity environments. Security analysts rarely work alone, and the exam now includes scenarios that require coordination between different roles.
Candidates must understand how incident response teams, threat intelligence analysts, and system administrators work together during security events. Communication and information sharing are important parts of effective response.
CS0-002 focused more on individual analytical tasks, while CS0-003 emphasizes teamwork and structured collaboration.
Increased Relevance of Regulatory Awareness
While not a legal exam, CS0-003 places slightly more emphasis on understanding how security operations align with regulatory and compliance requirements.
Candidates are expected to recognize the importance of data protection, incident reporting standards, and organizational security policies. These elements influence how incidents are handled and documented.
CS0-002 included compliance concepts in a general way, but CS0-003 integrates them more naturally into operational scenarios.
More Realistic Log Analysis Complexity
Log analysis in CS0-003 is significantly more complex than in CS0-002. Instead of simple log interpretation, candidates are presented with multi-source logs that must be correlated to identify meaningful patterns.
These logs may include authentication records, network traffic data, application logs, and security alerts. The challenge lies in connecting them to form a coherent understanding of an event.
CS0-002 introduced log reading basics, but CS0-003 simulates real-world SOC environments where logs are large, noisy, and distributed.
Deeper Understanding of Attack Mitigation Strategies
CS0-003 requires candidates to go beyond detection and understand mitigation strategies in greater depth. This includes short-term containment actions and long-term remediation approaches.
Candidates must know how to isolate affected systems, prevent further spread, and restore normal operations. They must also understand how to strengthen defenses after an incident.
CS0-002 focused more on identifying incidents, while CS0-003 emphasizes complete lifecycle management from detection to recovery.
Greater Integration of Automation Logic in Decision Making
Automation is not just a tool in CS0-003 but part of the decision-making process. Candidates are expected to understand when automated responses are appropriate and when human intervention is necessary.
This includes evaluating the reliability of automated alerts and adjusting workflows based on risk levels. Automation is positioned as a support system rather than a replacement for analysts.
CS0-002 introduced automation concepts, but CS0-003 integrates them into practical judgment-based scenarios.
Enhanced Focus on Data Correlation Techniques
CS0-003 places strong emphasis on correlating data from different sources. This skill is essential for identifying complex attacks that may not be visible from a single dataset.
Candidates must understand how to combine endpoint data, network traffic, and threat intelligence to form a complete picture. Correlation is often the key to identifying advanced persistent threats.
CS0-002 included basic correlation concepts, while CS0-003 makes it a core analytical requirement.
More Sophisticated Understanding of Security Metrics
Security metrics and key performance indicators are more relevant in CS0-003. Candidates are expected to understand how organizations measure the effectiveness of their security operations.
This includes metrics such as mean time to detect, mean time to respond, and alert accuracy rates. These measurements help organizations improve their overall security posture.
CS0-002 briefly introduced performance concepts, but CS0-003 connects them more closely to operational decision making.
Expanded Coverage of Emerging Threat Technologies
CS0-003 reflects the growing influence of emerging technologies in cybersecurity threats. This includes attacks involving cloud-native environments, containerized applications, and API-based systems.
Candidates must understand how modern infrastructure changes the way attacks are executed and detected. Traditional perimeter-based security models are no longer sufficient in many environments.
CS0-002 focused more on traditional infrastructure, while CS0-003 aligns with modern distributed architectures.
More Realistic Time-Based Incident Scenarios
Time-based analysis is more important in CS0-003. Candidates are often required to interpret events that occur across different time periods and determine how they are related.
Understanding the sequence of events is critical for identifying attack progression. Delayed detection or missing early indicators can change the interpretation of an incident.
CS0-002 included time-based analysis at a basic level, but CS0-003 makes it more central to scenario evaluation.
Stronger Emphasis on Analytical Prioritization Under Pressure
CS0-003 simulates situations where analysts must prioritize actions under time pressure. This reflects real SOC environments where multiple incidents may occur simultaneously.
Candidates must decide which alerts require immediate attention and which can be monitored or deferred. This requires balancing risk, impact, and available resources.
CS0-002 included prioritization concepts, but CS0-003 increases complexity and realism.
Improved Alignment with Threat Intelligence Lifecycle
The threat intelligence lifecycle is more deeply integrated into CS0-003. Candidates must understand how raw data is collected, processed, analyzed, and transformed into actionable intelligence.
This includes understanding how intelligence feeds influence detection systems and incident response strategies. Intelligence is no longer static but continuously evolving.
CS0-002 introduced intelligence concepts, while CS0-003 integrates them into operational workflows.
Greater Emphasis on Real-Time Security Decision Making
CS0-003 introduces a stronger focus on real-time decision making compared to CS0-002. In modern cybersecurity environments, threats often evolve within minutes, requiring analysts to act quickly and accurately based on incomplete information.
The updated exam reflects this reality by presenting situations where candidates must evaluate ongoing incidents and decide the most appropriate next step. These decisions may involve containment, escalation, investigation, or monitoring depending on the severity and context of the situation.
CS0-002 focused more on structured understanding of processes, while CS0-003 places greater pressure on situational judgment and speed of analysis. This change better reflects actual SOC operations where time is a critical factor.
Improved Expectation of Technical Fluency
CS0-003 expects candidates to demonstrate a higher level of technical fluency when interpreting security data and system behavior. This does not mean advanced engineering knowledge, but rather the ability to understand how systems behave under normal and abnormal conditions.
Candidates must be comfortable with interpreting network activity, system logs, authentication patterns, and application behavior without needing step-by-step guidance. This independence is a key difference from CS0-002.
The earlier version allowed more structured guidance within questions, while CS0-003 expects candidates to think independently and draw conclusions from raw data.
Stronger Focus on Security Operations Workflow Understanding
CS0-003 places greater importance on understanding how security operations function as a complete workflow rather than isolated tasks. Candidates must understand how alerts move through a SOC pipeline from detection to resolution.
This includes alert triage, investigation, escalation, response coordination, and post-incident review. Each stage is interconnected, and candidates must understand how decisions at one stage impact the next.
CS0-002 introduced these concepts individually, but CS0-003 integrates them into continuous operational flow scenarios.
Increased Complexity in Multi-Stage Problem Solving
Multi-stage problem solving is more prominent in CS0-003. Candidates are often required to analyze a situation step by step, where each answer influences the next part of the question.
This reflects real-world cybersecurity investigations where analysts must build understanding gradually as new information becomes available. It also tests logical consistency and structured thinking.
CS0-002 used simpler, single-step scenarios, while CS0-003 requires layered reasoning across multiple stages of analysis.
Enhanced Focus on Detection Accuracy and Validation
CS0-003 emphasizes validating security alerts before taking action. Not every alert represents a real threat, and candidates must understand how to distinguish between false positives, benign activity, and actual malicious behavior.
This includes evaluating context, comparing historical behavior, and using multiple data sources before confirming an incident. Validation is a critical skill in modern security operations to prevent unnecessary disruption.
CS0-002 introduced alert validation in basic terms, but CS0-003 makes it a central analytical responsibility.
More Realistic Representation of Security Tool Usage
CS0-003 better reflects how security tools are used in real environments. Instead of focusing on tool definitions, the exam emphasizes how tools interact in practical workflows.
Candidates must understand how SIEM systems aggregate logs, how EDR tools provide endpoint visibility, and how threat intelligence platforms enrich security data. These tools are not tested individually but as part of integrated scenarios.
CS0-002 often treated tools in isolation, while CS0-003 emphasizes ecosystem-level understanding.
Greater Importance of Context Awareness in Analysis
Context awareness is a key theme in CS0-003. Candidates must understand that the same security event can have different meanings depending on the environment, user role, system type, and timing.
For example, a failed login attempt may be normal in one context but highly suspicious in another. The ability to interpret context correctly is essential for accurate analysis.
CS0-002 included context considerations but not at the depth required in CS0-003.
Stronger Focus on Continuous Improvement Mindset
CS0-003 encourages a mindset of continuous improvement in security operations. Candidates are expected to understand how organizations learn from incidents and improve their defenses over time.
This includes reviewing past incidents, refining detection rules, updating response procedures, and improving overall security posture. Cybersecurity is presented as an evolving process rather than a static system.
CS0-002 introduced improvement concepts but CS0-003 integrates them more deeply into operational thinking.
Improved Realism in Attack Simulation Scenarios
The attack scenarios in CS0-003 are more realistic and detailed. Instead of simplified examples, candidates are presented with complex attack situations that mimic real-world adversaries.
These scenarios may involve multi-vector attacks, where attackers use different methods such as phishing, credential theft, lateral movement, and data exfiltration in a coordinated manner.
CS0-002 used simpler attack models, while CS0-003 reflects modern, layered attack strategies used by advanced threat actors.
Expanded Focus on Data Interpretation Across Multiple Systems
CS0-003 requires candidates to interpret data coming from multiple systems simultaneously. This reflects real SOC environments where information is distributed across different tools and platforms.
Candidates must combine endpoint data, network logs, authentication records, and threat intelligence to form a complete understanding of events. This multi-source analysis is critical for accurate incident detection.
CS0-002 included multi-source analysis but at a lower level of complexity.
More Demanding Cognitive Load in Exam Questions
The overall cognitive load in CS0-003 is higher than in CS0-002. Candidates must process more information, analyze deeper relationships, and make decisions with less obvious guidance.
This reflects real cybersecurity work, where analysts must often work under pressure with incomplete and rapidly changing data.
CS0-002 was more structured and guided, while CS0-003 is more open-ended and analytically demanding.
Stronger Alignment with Career Progression Expectations
CS0-003 is designed not just as an entry-level validation but as a stepping stone toward more advanced cybersecurity roles. It aligns more closely with expectations for mid-level security analysts working in operational environments.
This makes the certification more relevant for professionals aiming to grow into roles such as senior SOC analyst, threat hunter, or incident response specialist.
CS0-002 served as a strong foundation, but CS0-003 better reflects progression into real-world cybersecurity careers.
Refined Understanding of Security Analyst Responsibilities
CS0-003 brings a clearer and more realistic definition of what a cybersecurity analyst actually does in modern organizations. Unlike CS0-002, which focused more on foundational concepts and structured processes, the updated version reflects the dynamic and unpredictable nature of real security operations.
Analysts are no longer viewed as passive responders who follow fixed steps. Instead, they are expected to actively interpret data, identify patterns, investigate anomalies, and make informed decisions under pressure. This shift makes CS0-003 more aligned with day-to-day responsibilities in Security Operations Centers and threat monitoring environments.
The exam highlights that cybersecurity work is not just technical but also analytical, requiring judgment, prioritization, and contextual awareness.
More Mature Approach to Cyber Defense Strategy
CS0-003 introduces a more mature understanding of cyber defense strategies. Instead of focusing on isolated defensive measures, it emphasizes layered security, continuous monitoring, and adaptive response mechanisms.
Candidates must understand how organizations build defense-in-depth strategies where multiple security controls work together to reduce risk. This includes endpoint protection, network monitoring, identity security, and threat intelligence integration.
CS0-002 introduced these concepts individually, but CS0-003 connects them into a unified defensive strategy that mirrors real enterprise environments.
Increased Focus on Operational Awareness
Operational awareness is a key theme in CS0-003. Candidates are expected to understand how security operations function on a continuous basis, rather than as isolated incidents.
This includes understanding alert fatigue, resource constraints, escalation procedures, and coordination between teams. Security is presented as a continuous cycle of monitoring, detection, response, and improvement.
CS0-002 provided a more static view of operations, while CS0-003 reflects the ongoing and evolving nature of cybersecurity environments.
Stronger Emphasis on Analytical Independence
One of the most important changes in CS0-003 is the expectation of analytical independence. Candidates are no longer guided through simplified scenarios but are expected to evaluate complex situations on their own.
This includes interpreting incomplete data, making assumptions based on evidence, and validating conclusions through logical reasoning. The ability to think independently is essential for real-world cybersecurity roles.
CS0-002 provided more structured guidance, while CS0-003 challenges candidates to operate with greater autonomy and confidence.
Improved Reflection of Modern Threat Ecosystems
CS0-003 better reflects the complexity of modern threat ecosystems. Cyber threats today are not isolated events but interconnected campaigns involving multiple techniques and targets.
The exam incorporates this by presenting scenarios where attackers use coordinated strategies across different systems and environments. Candidates must understand how these threats evolve and spread across networks.
CS0-002 focused more on traditional attack patterns, while CS0-003 reflects advanced, multi-stage, and adaptive adversary behavior.
Greater Emphasis on Security Intelligence Interpretation
Security intelligence interpretation is significantly more important in CS0-003. Candidates must understand how raw data is transformed into actionable intelligence that supports decision-making.
This includes analyzing threat feeds, identifying relevant indicators, and understanding how intelligence influences detection and response strategies. Intelligence is not treated as background information but as a core component of analysis.
CS0-002 introduced intelligence concepts at a basic level, while CS0-003 integrates them deeply into operational workflows.
Enhanced Understanding of Incident Lifecycle Management
CS0-003 places strong emphasis on managing incidents throughout their entire lifecycle. This includes detection, analysis, containment, eradication, recovery, and post-incident review.
Candidates must understand how each stage connects and how decisions made early in the process affect later outcomes. This holistic view ensures that incidents are handled efficiently and effectively.
CS0-002 covered incident response steps, but CS0-003 treats them as a continuous and interconnected process.
More Realistic Expectation of Professional Competency
The updated exam sets a more realistic expectation of professional competency. Instead of testing isolated knowledge points, CS0-003 evaluates how well candidates can apply their knowledge in practical situations.
This includes working under pressure, handling uncertainty, and making decisions with incomplete information. These are essential skills for cybersecurity professionals in real environments.
CS0-002 was more academic in structure, while CS0-003 is more aligned with professional job performance.
Stronger Connection Between Theory and Practice
CS0-003 bridges the gap between theoretical knowledge and practical application. Candidates are expected to not only understand security concepts but also apply them in realistic scenarios.
This includes using analytical tools, interpreting system behavior, and responding to simulated security incidents. The exam ensures that knowledge is not just memorized but actively applied.
CS0-002 had a stronger theoretical focus, while CS0-003 integrates theory directly into practice-based evaluation.
Improved Representation of Modern Security Challenges
Modern cybersecurity challenges such as ransomware, cloud misconfigurations, insider threats, and supply chain attacks are more accurately represented in CS0-003.
Candidates must understand how these threats operate and how they impact organizations. The exam reflects the reality that cyber threats are constantly evolving and becoming more sophisticated.
CS0-002 included these topics at a foundational level, while CS0-003 expands them into realistic operational scenarios.
Conclusion
The transition from CS0-002 to CS0-003 represents a significant evolution in the CompTIA CySA+ certification. It is not simply an update of content but a complete refinement of how cybersecurity analyst skills are evaluated.
CS0-003 focuses on real-world application, analytical thinking, and operational readiness. It emphasizes the ability to interpret complex data, understand attacker behavior, and make informed decisions in dynamic environments.
Compared to CS0-002, the updated version is more challenging, more realistic, and more closely aligned with modern cybersecurity job roles. It reflects the shift in the industry from basic threat detection to advanced security analytics, automation, and proactive defense strategies.
Overall, CS0-003 prepares candidates not just to pass an exam, but to perform effectively in real cybersecurity operations where accuracy, speed, and critical thinking are essential.