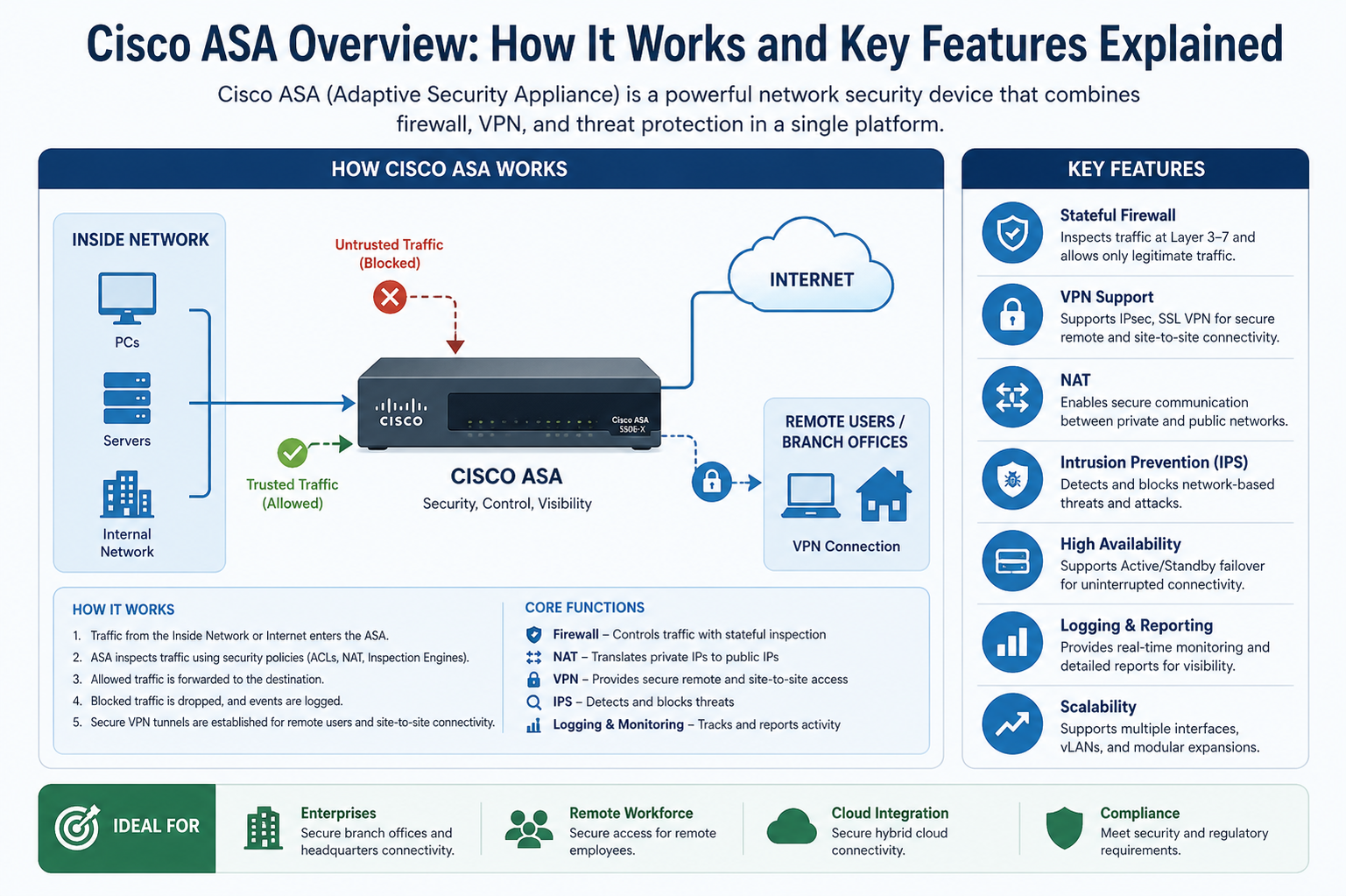
Cisco ASA is built on a purpose-driven security architecture that integrates multiple protective functions into a unified system. At its core, it is designed to enforce security policies at the network perimeter while maintaining high performance for enterprise traffic. Unlike traditional firewalls that only filter packets based on static rules, Cisco ASA uses a stateful inspection model that understands the context of traffic flows. This means it tracks the state of active sessions and makes decisions based on the legitimacy of the entire connection rather than individual packets alone.
The architecture of Cisco ASA is modular in nature, allowing it to support different security services such as firewalling, VPN termination, intrusion prevention, and advanced traffic control. This integration reduces the need for multiple standalone devices and simplifies network security management. The system is optimized to operate in high-throughput environments, making it suitable for both small business networks and large enterprise infrastructures.
At a structural level, Cisco ASA separates network zones into security levels. Each interface is assigned a security value that determines how traffic is treated when moving between interfaces. Higher-security zones are generally considered trusted, while lower-security zones are treated as untrusted. This model allows administrators to define granular policies that control how data flows across different segments of the network.
Stateful Inspection and Traffic Control Mechanism
One of the most important aspects of Cisco ASA is its stateful inspection engine. This mechanism ensures that every packet is evaluated not only based on its header information but also based on its relationship to previously seen traffic. When a connection is initiated, ASA records its state in a connection table. Any returning traffic is then matched against this table to verify whether it is part of an existing legitimate session.
This process significantly improves security because it prevents unauthorized traffic from impersonating valid sessions. It also enhances performance by reducing the need for repeated deep inspection of every packet once a session is validated. The stateful engine also plays a critical role in detecting abnormal behavior, such as session hijacking attempts or unexpected protocol usage.
Cisco ASA also implements inspection engines for various protocols such as HTTP, FTP, SIP, and DNS. These engines understand protocol-specific behavior and can detect anomalies that may indicate malicious activity. For example, in FTP sessions, ASA can monitor both control and data channels to ensure they remain synchronized and compliant with expected behavior.
Firewall Functionality and Security Policies
At its core, Cisco ASA functions as a robust firewall that enforces security policies defined by administrators. These policies determine which traffic is allowed, denied, or subjected to additional inspection. The firewall rules are typically organized based on source and destination addresses, protocols, and ports, allowing precise control over network communication.
The policy framework in Cisco ASA is highly flexible. It supports both static and dynamic rules, enabling organizations to adapt quickly to changing security requirements. Access control lists are used to define these rules, and they are processed in a top-down manner, meaning that the order of rules is critical to how traffic is handled.
Cisco ASA also supports object grouping, which allows administrators to simplify complex rule sets by grouping similar network objects together. This reduces configuration complexity and improves manageability in large-scale environments. Additionally, time-based rules can be implemented to restrict access during specific periods, further enhancing security control.
Virtual Private Network Capabilities
One of the most widely used features of Cisco ASA is its VPN functionality. It supports both site-to-site and remote-access VPN configurations, enabling secure communication over untrusted networks such as the internet. VPN tunnels created by ASA are encrypted, ensuring that sensitive data remains protected during transmission.
Site-to-site VPNs are commonly used to connect different office locations, allowing them to function as a single unified network. Remote-access VPNs, on the other hand, allow individual users to securely connect to corporate resources from remote locations. This is particularly important in modern work environments where remote work is increasingly common.
Cisco ASA supports multiple VPN protocols, including IPsec and SSL. IPsec is typically used for secure site-to-site communication, while SSL VPNs are often used for client-based remote access due to their ease of deployment and compatibility with standard web browsers. The encryption mechanisms used in these VPNs ensure confidentiality, integrity, and authentication of data.
Intrusion Prevention and Threat Detection
Cisco ASA includes intrusion prevention capabilities that help detect and block malicious activity in real time. This is achieved through deep packet inspection and signature-based detection methods. The system compares network traffic against a database of known attack signatures and behavioral patterns.
When suspicious activity is detected, ASA can take immediate action such as blocking the traffic, alerting administrators, or logging the event for further analysis. This proactive approach helps reduce the risk of network breaches and minimizes the impact of potential attacks.
In addition to signature-based detection, Cisco ASA also supports anomaly-based monitoring. This method identifies deviations from normal traffic behavior, which may indicate unknown or emerging threats. By combining both approaches, ASA provides a layered defense strategy that improves overall security effectiveness.
Network Address Translation and Traffic Management
Cisco ASA plays a significant role in managing IP addressing through Network Address Translation (NAT). NAT allows private IP addresses within an internal network to be mapped to public IP addresses for external communication. This not only conserves public IP space but also adds a layer of security by hiding internal network structures from external observers.
There are different types of NAT supported by Cisco ASA, including static NAT, dynamic NAT, and PAT (Port Address Translation). Static NAT creates a one-to-one mapping between internal and external addresses, while dynamic NAT assigns addresses from a pool as needed. PAT allows multiple internal devices to share a single public IP address using different port numbers.
Traffic management is another critical function of ASA. It allows administrators to control bandwidth usage, prioritize certain types of traffic, and ensure optimal network performance. This is particularly important in environments where multiple applications compete for limited network resources.
High Availability and Redundancy Design
Cisco ASA supports high availability configurations to ensure continuous network protection even in the event of hardware or software failure. This is typically achieved through active/standby or active/active failover setups. In an active/standby configuration, one device handles all traffic while the other remains in standby mode, ready to take over if the primary device fails.
In active/active configurations, both devices share the traffic load, improving performance while maintaining redundancy. State synchronization between devices ensures that active sessions are preserved during failover events, minimizing disruption to users.
This redundancy model is essential for mission-critical environments where downtime is not acceptable. It ensures that security services remain operational even under adverse conditions.
Logging, Monitoring, and Event Analysis
Cisco ASA provides comprehensive logging and monitoring capabilities that allow administrators to track network activity in detail. Logs include information about allowed and denied traffic, system events, VPN connections, and security alerts.
These logs can be stored locally or sent to external syslog servers for centralized analysis. Monitoring tools help administrators identify patterns, detect anomalies, and respond to security incidents quickly. Real-time alerts can also be configured to notify administrators of critical events as they occur.
This visibility into network activity is crucial for maintaining security compliance and conducting forensic analysis after incidents.
Performance Optimization and Scalability
Cisco ASA is designed to handle high volumes of network traffic without compromising security. It uses hardware acceleration and optimized processing engines to ensure efficient performance. This allows it to operate effectively in environments with heavy data loads and complex security requirements.
Scalability is another key advantage. Cisco ASA can be deployed in different sizes and configurations depending on organizational needs. It supports modular upgrades and integration with other Cisco security solutions, allowing organizations to expand their security infrastructure as needed.
Role in Modern Cybersecurity Environments
In modern cybersecurity frameworks, Cisco ASA continues to play an important role despite the emergence of newer next-generation firewalls. Its reliability, stability, and comprehensive feature set make it a trusted choice for many enterprises. It is often used in conjunction with other security tools to create a layered defense strategy.
Organizations rely on Cisco ASA to enforce perimeter security, secure remote access, and maintain control over network traffic. Its long-standing presence in the industry has made it a well-understood and widely deployed security solution.
Advanced Cisco ASA Configuration and Management
Cisco ASA provides a highly structured configuration system that allows administrators to define security behavior in a precise and scalable way. The configuration is primarily handled through a command-line interface, although graphical tools may also be used in some environments. The CLI is considered the most powerful method because it provides direct access to all features and allows for fine-grained control over system behavior.
The configuration process in Cisco ASA is based on hierarchical command modes. Each mode is responsible for a specific level of configuration, such as global settings, interface configuration, or policy definitions. This structure ensures that changes are organized and applied consistently across the system. Administrators typically begin by defining basic system parameters such as hostname, interface settings, and routing information before moving on to security policies and advanced features.
One of the key strengths of ASA configuration is its object-based approach. Network objects, service objects, and groups allow administrators to define reusable components that simplify complex rule sets. Instead of writing repetitive rules for each individual host or service, objects can be created once and reused across multiple policies. This reduces configuration errors and improves long-term maintainability.
Interface Configuration and Security Levels
Cisco ASA relies heavily on interface-based security segmentation. Each physical or logical interface is assigned a security level ranging from 0 to 100. Higher values represent more trusted networks, while lower values represent less trusted or external networks. By default, traffic is allowed to flow from higher-security interfaces to lower-security interfaces, but the reverse direction requires explicit permission through access control rules.
This model provides a clear and intuitive way to segment networks. For example, an internal corporate network may be assigned a high security level, while a DMZ hosting public-facing services is assigned a lower level. The internet-facing interface typically has the lowest security level. This hierarchy helps enforce strict control over how data moves between different parts of the network.
Interfaces can be configured in routed mode or transparent mode. In routed mode, ASA acts as a traditional Layer 3 device, managing IP addresses and routing traffic between networks. In transparent mode, it operates more like a Layer 2 bridge, filtering traffic without changing IP addressing schemes. This flexibility allows ASA to be deployed in a variety of network architectures.
Network Address Translation in Depth
Network Address Translation in Cisco ASA is a critical function that enables secure and efficient IP address management. NAT modifies packet headers as they pass through the device, translating private internal addresses into public external addresses and vice versa. This process allows internal networks to communicate with external systems without exposing internal IP structures.
Static NAT is used when a fixed mapping between internal and external addresses is required. This is commonly used for servers that need to be accessible from the internet. Dynamic NAT, on the other hand, assigns external addresses from a pool on demand, making it suitable for general outbound traffic. Port Address Translation extends this concept further by allowing multiple internal devices to share a single public IP address using different port numbers.
Modern Cisco ASA versions also support policy-based NAT, which allows translation rules to be applied based on specific traffic conditions such as source, destination, or service type. This adds a high level of flexibility and allows complex network scenarios to be implemented efficiently.
Access Control and Traffic Filtering Mechanisms
Access control in Cisco ASA is implemented through Access Control Lists, which define rules for permitting or denying traffic. These rules are evaluated sequentially, and the first matching rule determines the outcome for each packet. This makes rule ordering extremely important for correct system behavior.
ACLs can be applied to interfaces to control inbound or outbound traffic. They can also be combined with object groups to simplify large rule sets. In addition to basic filtering, ASA supports time-based access control, which allows rules to be active only during specific time periods. This is useful for restricting access outside business hours or enforcing temporary security policies.
Beyond traditional ACLs, Cisco ASA includes advanced inspection engines that analyze traffic at a deeper level. These engines understand application behavior and can enforce protocol compliance. This helps prevent attacks that attempt to exploit application-layer vulnerabilities.
VPN Architecture and Secure Connectivity
Cisco ASA implements a robust VPN architecture that supports secure communication over untrusted networks. The VPN system is built around encryption, authentication, and tunnel management, ensuring that data remains confidential and protected during transmission.
In site-to-site VPN deployments, ASA establishes encrypted tunnels between different network locations. These tunnels allow remote offices to function as part of a unified network. In remote-access scenarios, individual users connect to the corporate network using secure VPN clients or browser-based connections.
Encryption in ASA VPNs is typically handled using IPsec protocols, which provide strong security through encryption algorithms and key exchange mechanisms. SSL-based VPNs are also supported, offering flexibility for users who require simpler access methods. Authentication can be integrated with local user databases or external identity systems, enhancing security and user management.
VPN tunnels in Cisco ASA are monitored continuously to ensure stability and security. If a tunnel fails, automatic re-establishment mechanisms attempt to restore connectivity without manual intervention.
High Availability and Failover Systems
Cisco ASA supports high availability configurations designed to eliminate single points of failure. In an active/standby setup, one device actively handles traffic while the other remains in standby mode. If the active device fails, the standby device automatically takes over, ensuring uninterrupted service.
Stateful failover is a key feature in this system. It ensures that active connections are synchronized between devices so that users do not experience session drops during failover events. This is especially important for critical applications such as financial systems or real-time communications.
Active/active failover configurations allow both devices to process traffic simultaneously. This not only provides redundancy but also improves overall performance by distributing the load. Synchronization between devices ensures consistency in configuration and session states.
Logging, Monitoring, and Security Auditing
Cisco ASA provides extensive logging capabilities that give administrators visibility into network activity. Logs capture events such as connection attempts, security violations, system errors, and configuration changes. This information is essential for troubleshooting, compliance, and forensic analysis.
Logs can be stored locally or forwarded to centralized logging systems for long-term storage and analysis. Real-time monitoring tools allow administrators to observe active connections and detect unusual behavior as it occurs. Alerts can be configured to notify administrators of critical events immediately.
Security auditing features help organizations maintain compliance with regulatory standards. By reviewing logs and reports, administrators can verify that security policies are being enforced correctly and identify potential weaknesses in the network.
Performance Optimization and Hardware Acceleration
Cisco ASA is engineered for high-performance environments. It uses optimized processing techniques and hardware acceleration to handle large volumes of traffic efficiently. This ensures that security functions do not become a bottleneck in network performance.
Traffic inspection, encryption, and NAT processing are all optimized to reduce latency and maximize throughput. In high-demand environments, ASA can be deployed in clustered configurations to distribute processing loads across multiple devices.
Performance tuning options allow administrators to adjust system behavior based on network requirements. This includes adjusting inspection levels, optimizing rule sets, and managing resource allocation.
Security Contexts and Multi-Tenancy Support
One of the advanced capabilities of Cisco ASA is its support for security contexts. This feature allows a single physical device to operate as multiple virtual firewalls, each with its own configuration, policies, and interfaces. This is particularly useful for service providers or large organizations that need to isolate different departments or clients.
Each security context operates independently, ensuring strong separation between environments. This reduces hardware costs while maintaining strict security boundaries. Context switching is efficient, allowing multiple virtual firewalls to run on the same platform without performance degradation.
Role in Enterprise Network Security Strategy
Cisco ASA plays a central role in enterprise security architectures by providing a unified platform for firewalling, VPN, and threat prevention. It is often deployed at network perimeters, data centers, and branch offices to enforce consistent security policies across the organization.
In modern security strategies, ASA is frequently integrated with other advanced security systems to create a layered defense model. While newer technologies may offer additional capabilities, ASA remains a stable and reliable foundation for network protection due to its proven architecture and long-term industry adoption.
Its ability to combine multiple security functions into a single device reduces complexity and improves operational efficiency. This makes it a valuable component in both traditional and hybrid network environments.
Advanced Threat Protection and Inspection Capabilities
Cisco ASA includes a range of advanced inspection features designed to identify and mitigate sophisticated network threats. These capabilities go beyond basic firewall filtering by analyzing traffic behavior at multiple layers of the network stack. The system is capable of inspecting application-level data, which allows it to detect attacks that might otherwise bypass traditional security controls.
Deep packet inspection is a key component of this capability. It enables ASA to examine the full contents of packets rather than just header information. This allows the device to identify malicious payloads, protocol violations, and suspicious patterns that indicate potential exploitation attempts. Inspection engines are tailored for specific protocols, allowing the system to understand normal behavior and detect anomalies with higher accuracy.
Cisco ASA also supports protocol normalization, which ensures that traffic conforms to expected standards before it reaches internal systems. Attackers often attempt to exploit inconsistencies in protocol handling, but normalization processes eliminate these variations and reduce the attack surface.
In addition, ASA can integrate with external threat intelligence sources in advanced deployments. This allows it to update its understanding of known threats and adjust security policies dynamically. Although traditional ASA deployments are more static compared to next-generation systems, these extended capabilities significantly improve its defensive strength when properly configured.
Intrusion Prevention System Integration
Cisco ASA can operate in conjunction with intrusion prevention systems to enhance its security capabilities. The intrusion prevention function monitors traffic for known attack signatures and suspicious behaviors. When a threat is detected, the system can take immediate action, such as dropping packets, resetting connections, or alerting administrators.
Signature-based detection relies on a database of known attack patterns. These signatures are continuously updated to include newly discovered vulnerabilities and exploits. Behavioral detection complements this by identifying unusual traffic patterns that do not match established baselines.
The combination of firewall filtering and intrusion prevention creates a layered defense model. While the firewall controls access based on rules, the intrusion prevention system actively analyzes the content and behavior of allowed traffic. This dual approach significantly reduces the risk of successful attacks.
Routing and Network Integration
Cisco ASA supports both static and dynamic routing protocols, allowing it to integrate seamlessly into complex network environments. Static routes are used for simple and predictable traffic paths, while dynamic routing protocols enable automatic adaptation to network changes.
In enterprise environments, ASA is often deployed alongside routers and switches, forming part of a larger network topology. It can participate in routing decisions or act purely as a security boundary device depending on configuration. This flexibility allows it to fit into a wide range of architectural designs.
The routing engine works closely with security policies to ensure that traffic is not only directed correctly but also filtered appropriately. This integration between routing and security is one of the key strengths of the platform.
Management Interfaces and Administrative Access
Cisco ASA provides multiple methods for system management. The most powerful interface is the command-line interface, which offers complete control over all configuration aspects. Administrators can execute detailed commands to configure interfaces, security policies, VPNs, and system behavior.
In addition to the CLI, graphical management tools are available in some deployments. These tools simplify configuration for less experienced administrators and provide visual representations of network policies. However, advanced configurations are typically still performed through the CLI due to its greater flexibility.
Remote management access can be secured using encrypted protocols such as SSH and HTTPS. Access control mechanisms ensure that only authorized administrators can make configuration changes. Role-based access control allows organizations to assign different privilege levels to different users, improving operational security.
Troubleshooting and Diagnostic Tools
Cisco ASA includes a comprehensive set of diagnostic tools designed to help administrators identify and resolve network issues. These tools provide visibility into traffic flows, system performance, and security events.
Packet capture functionality allows administrators to inspect traffic directly on the device. This is particularly useful for diagnosing connectivity problems or verifying security policy behavior. Captured packets can be analyzed to determine whether traffic is being blocked, modified, or allowed correctly.
Connection monitoring tools provide real-time visibility into active sessions. Administrators can view detailed information about each connection, including source and destination addresses, protocol types, and session duration. This helps in identifying unusual or unauthorized activity.
System logs play a crucial role in troubleshooting. By reviewing log entries, administrators can trace the sequence of events leading up to a problem. This makes it easier to identify misconfigurations or security violations.
Performance Tuning and Optimization Strategies
Optimizing Cisco ASA performance involves careful management of resources and configuration settings. One of the most important aspects is rule optimization. Poorly structured access control lists can slow down traffic processing, so it is important to organize rules efficiently and eliminate unnecessary entries.
Inspection policies should also be tuned based on network requirements. While deep inspection provides stronger security, it can also increase processing overhead. Administrators must balance security needs with performance considerations.
Hardware resources such as CPU and memory usage should be monitored regularly. In high-traffic environments, upgrading hardware or distributing load across multiple devices may be necessary to maintain optimal performance.
Traffic prioritization mechanisms can be used to ensure that critical applications receive sufficient bandwidth. This helps maintain performance consistency even during periods of heavy network usage.
Security Best Practices for Cisco ASA Deployment
Proper deployment of Cisco ASA requires adherence to security best practices to ensure maximum protection. One fundamental principle is the use of least privilege access. Only necessary traffic should be allowed through the firewall, and all other traffic should be explicitly denied.
Regular updates and patch management are also critical. Keeping the system software up to date ensures protection against newly discovered vulnerabilities. Configuration backups should be maintained to allow quick recovery in case of system failure.
Segmentation of network zones is another important practice. Separating internal, external, and DMZ networks reduces the impact of potential breaches and limits lateral movement within the network.
Logging and monitoring should be enabled at all times. Continuous observation of network activity allows early detection of suspicious behavior and faster response to incidents.
Limitations and Challenges
While Cisco ASA is a powerful security solution, it does have certain limitations. Compared to modern next-generation firewalls, its feature set may appear less advanced in areas such as application awareness and cloud-native integration. It relies heavily on manual configuration, which can become complex in large environments.
Scalability, while strong, may require additional hardware or clustering in extremely high-demand scenarios. Additionally, advanced features often require careful configuration and expertise to implement effectively.
Despite these limitations, ASA remains widely used due to its stability, reliability, and proven security model.
Comparison with Modern Security Solutions
In modern cybersecurity landscapes, newer solutions often provide more advanced capabilities such as AI-driven threat detection, integrated cloud security, and deeper application visibility. However, Cisco ASA continues to be valued for its predictable behavior and strong foundational security features.
Unlike some next-generation platforms, ASA focuses on core network security functions rather than broad security ecosystems. This makes it highly reliable for organizations that prioritize stability and control over experimental features.
Many enterprises still deploy ASA as part of a hybrid security architecture, combining it with newer tools to achieve both reliability and advanced protection.
Operational Use in Enterprise Environments
In real-world deployments, Cisco ASA is commonly used at network perimeters, branch offices, and data centers. It serves as the primary barrier between internal systems and external networks, enforcing strict security policies and controlling traffic flow.
It is also frequently used to secure remote access for employees, particularly in organizations with distributed workforces. VPN capabilities allow users to connect securely from any location while maintaining compliance with corporate security standards.
In large enterprises, ASA devices are often deployed in redundant pairs or clusters to ensure continuous availability. This ensures that security services remain operational even during maintenance or unexpected failures.
Future Role and Relevance
Although the cybersecurity landscape continues to evolve, Cisco ASA remains relevant due to its reliability and widespread adoption. Many organizations continue to rely on it as a stable foundation for network security, especially in environments where consistency and predictability are critical.
Its long lifecycle and proven performance make it a dependable choice for legacy systems and hybrid infrastructures. While newer technologies may eventually replace it in some areas, its role in existing networks ensures continued importance for years to come.
Cisco ASA Deployment Scenarios in Real Networks
Cisco ASA is widely deployed across different types of network environments, and its role changes depending on organizational structure and security requirements. In enterprise edge deployments, it typically sits between the internal corporate network and the internet, acting as the primary security barrier. In this position, it filters all incoming and outgoing traffic, ensuring that only authorized communication is allowed while blocking malicious attempts.
In data center environments, Cisco ASA is used to segment internal workloads and protect sensitive servers. It helps isolate application tiers, such as separating web servers from database systems, reducing the risk of lateral movement in case of a breach. This segmentation is critical for maintaining strong internal security boundaries.
In branch office scenarios, ASA devices are often deployed to provide secure connectivity back to headquarters. These deployments usually rely on VPN tunnels that connect distributed locations into a unified network. This allows employees in remote offices to access central resources securely without exposing data to public networks.
In remote workforce environments, Cisco ASA plays a major role in enabling secure remote access. Employees connect through encrypted VPN channels, ensuring that sensitive corporate data remains protected even when accessed from external locations. This capability became especially important with the rise of distributed work models.
Security Policy Design and Implementation Strategy
Designing security policies in Cisco ASA requires careful planning to ensure both protection and usability. The goal is to allow necessary business traffic while blocking everything else by default. This approach is often referred to as a “deny all, permit by exception” model, which is a foundational principle in firewall security design.
Policies are typically structured based on network zones, user roles, and application requirements. For example, internal users may be allowed broader access to resources, while external users are restricted to specific services. DMZ zones are carefully controlled to expose only necessary services to the internet.
Object-based policy design is commonly used to simplify rule management. Instead of creating individual rules for each host or service, administrators define reusable objects that represent groups of resources. This makes policies easier to maintain and reduces the risk of configuration errors.
Proper policy documentation is also essential. As environments grow more complex, maintaining clear records of rules and their purpose helps prevent misconfigurations and ensures compliance with security standards.
Traffic Flow Behavior and Packet Processing Lifecycle
When a packet enters Cisco ASA, it goes through a structured processing lifecycle. First, the device checks whether the packet belongs to an existing connection. If it does, the packet is quickly allowed based on the existing session state, which improves performance and efficiency.
If the packet is part of a new connection, it is evaluated against access control rules. These rules determine whether the traffic is permitted or denied. If allowed, the packet is then inspected further using protocol-specific inspection engines.
After inspection, the packet may be subjected to NAT translation if required. This step modifies source or destination addresses based on configured translation rules. Finally, the packet is forwarded to its destination interface.
Return traffic follows a similar path but is matched against the established connection table. This ensures that only legitimate response traffic is permitted back into the network, preventing unauthorized access attempts.
This structured flow ensures both security and performance by minimizing unnecessary processing for trusted traffic while thoroughly inspecting new or suspicious connections.
Advanced VPN Configuration and Security Enhancements
Cisco ASA VPN configurations can be highly customized to meet different security requirements. Encryption strength, authentication methods, and tunnel behavior can all be adjusted based on organizational policies. Strong encryption algorithms are typically used to ensure that intercepted data cannot be decrypted by attackers.
Multi-factor authentication is often integrated into VPN setups to enhance security. This adds an additional layer of verification beyond passwords, reducing the risk of unauthorized access. Certificate-based authentication is also commonly used in enterprise environments for stronger identity validation.
Split tunneling is another configurable feature. It determines whether all user traffic is routed through the VPN or only corporate-related traffic. While split tunneling improves performance by reducing unnecessary load on the VPN, it must be carefully managed to avoid security risks.
VPN session monitoring allows administrators to track active connections in real time. This helps identify unusual login patterns or unauthorized access attempts, enabling faster incident response.
System Hardening and Security Reinforcement Techniques
Hardening Cisco ASA involves reducing its attack surface by disabling unnecessary services and restricting administrative access. Only essential management protocols should be enabled, and access should be limited to trusted networks or administrative hosts.
Strong authentication mechanisms should be enforced for all administrative accounts. Password policies must require complexity and regular updates to prevent unauthorized access. Role-based access control ensures that administrators only have permissions relevant to their responsibilities.
Unused interfaces and services should be disabled to reduce potential entry points for attackers. Regular audits of configuration settings help identify weaknesses and ensure compliance with security standards.
Firmware updates are a critical part of system hardening. Security vulnerabilities are regularly discovered, and applying updates ensures that the system remains protected against known threats.
Scalability in Large Enterprise Networks
Cisco ASA is designed to scale in enterprise environments through clustering and load distribution. Multiple devices can be combined to handle higher traffic volumes while maintaining consistent security policies across the network.
Clustering allows multiple ASA units to operate as a single logical system. This improves performance and ensures redundancy in case one device fails. Traffic is distributed across cluster members, optimizing resource utilization.
In large-scale deployments, centralized management tools are often used to control multiple ASA devices. This simplifies configuration management and ensures consistency across the entire infrastructure.
Scalability also involves careful planning of IP addressing, routing design, and security policy structure. Poor design can lead to bottlenecks, so proper architecture is essential for long-term performance.
Incident Response and Security Event Handling
Cisco ASA plays an important role in incident response by providing detailed logs and alerts during security events. When suspicious activity is detected, the system generates alerts that can be used to trigger response actions.
Administrators can analyze logs to determine the source, type, and impact of a security incident. Packet captures can provide deeper insight into malicious traffic patterns, helping security teams understand attack behavior.
Automated responses can also be configured to block or limit traffic when specific conditions are met. This helps reduce the impact of attacks while investigation is ongoing.
Integration with security information and event management systems allows ASA to contribute to broader organizational threat monitoring strategies.
Operational Challenges in Real Deployments
Despite its strengths, Cisco ASA deployments can present operational challenges. Complex configurations may require experienced administrators to manage effectively. Misconfigured rules can lead to security gaps or connectivity issues.
Performance tuning requires careful balancing between security depth and system efficiency. Overly aggressive inspection settings may impact throughput, while weak settings may reduce protection.
Troubleshooting can also become complex in large environments due to the number of rules, interfaces, and policies involved. Proper documentation and monitoring are essential to manage this complexity.
Long-Term Value in Network Security Architecture
Cisco ASA continues to provide long-term value in network security due to its stability, predictable behavior, and proven architecture. Many organizations rely on it as a core security layer within their infrastructure.
Its ability to integrate firewalling, VPN, and inspection features into a single platform reduces complexity and operational overhead. This makes it particularly valuable in environments where reliability is a top priority.
Even as newer technologies emerge, Cisco ASA remains a foundational component in many enterprise security strategies, especially in hybrid and legacy systems where consistency is essential.
Conclusion
Cisco ASA remains one of the most established and widely deployed network security solutions in enterprise environments due to its strong combination of firewall protection, VPN capabilities, and intrusion inspection features. Its stateful inspection engine, structured policy system, and reliable traffic control mechanisms allow organizations to enforce strict security boundaries while still maintaining smooth network communication.
Across different deployment scenarios such as enterprise perimeters, data centers, branch offices, and remote access environments, Cisco ASA provides consistent protection by controlling how traffic enters, moves through, and exits a network. Its ability to segment networks using security levels, manage complex access control policies, and support secure encrypted tunnels makes it a versatile solution for many security architectures.
While newer security platforms offer more advanced cloud-native and AI-driven capabilities, Cisco ASA continues to be valued for its stability, predictable behavior, and mature feature set. It is especially effective in environments where reliability, control, and proven performance are more important than rapid feature evolution.
Overall, Cisco ASA serves as a foundational security layer that helps organizations reduce risk, protect sensitive data, and maintain secure communication across distributed systems. Its long-standing presence in cybersecurity demonstrates its continued relevance as a trusted and dependable network security appliance.