IPv4 subnetting is one of the most important building blocks in computer networking. It is the process of dividing a single IP network into multiple smaller networks, known as subnets. This technique was developed to improve the efficiency of IP address usage and to make large networks easier to manage. Without subnetting, networks would become congested, difficult to organize, and inefficient in terms of IP allocation.
At its core, subnetting allows network administrators to take a large pool of IP addresses and break it into smaller logical segments. Each segment can operate independently while still being part of the same overall network structure. This separation provides better control over traffic flow, reduces unnecessary broadcasting, and improves overall performance. Subnetting is widely used in enterprises, educational institutions, and service provider networks where multiple departments or systems need isolated yet connected network spaces.
Understanding IPv4 Address Structure
To understand subnetting, it is essential to first understand how IPv4 addresses are structured. An IPv4 address is a 32-bit numerical label assigned to each device connected to a network that uses the Internet Protocol. It is typically written in decimal format, divided into four octets separated by dots. Each octet represents 8 bits, meaning each part of the address can range from 0 to 255.
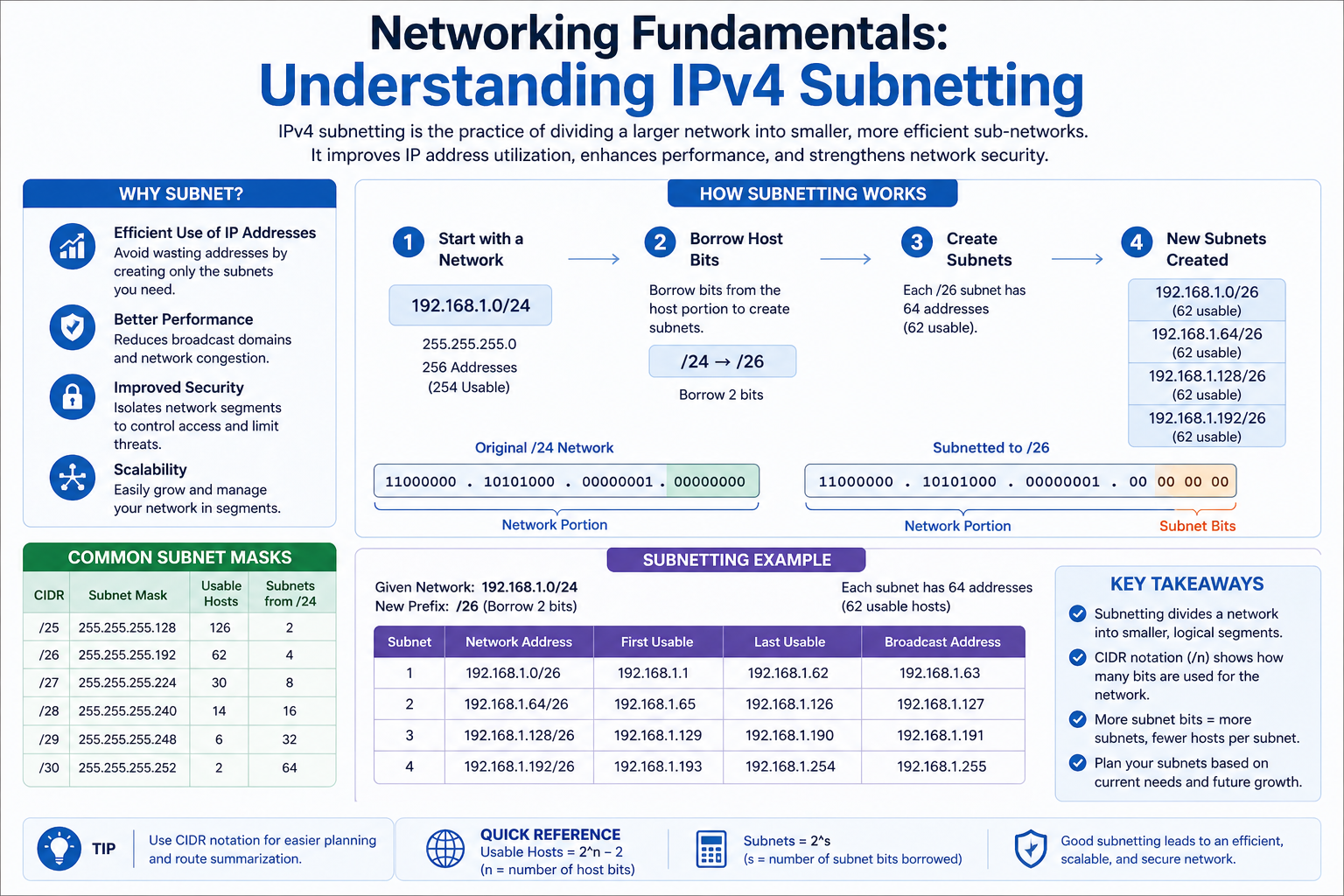
An IPv4 address is divided into two main components: the network portion and the host portion. The network portion identifies the specific network to which a device belongs, while the host portion identifies the individual device within that network. Subnetting works by adjusting the boundary between these two portions, allowing network administrators to create multiple smaller networks from a larger one.
For example, in a simple network, all devices may share the same network portion, meaning they belong to the same broadcast domain. However, as the network grows, this structure becomes inefficient. Subnetting solves this by redefining how many bits belong to the network and how many belong to hosts.
The Role of Subnet Masks
A subnet mask is a crucial element in IPv4 subnetting. It is used to determine which portion of an IP address represents the network and which portion represents the host. Like an IP address, a subnet mask is also a 32-bit number written in decimal format. It works by applying a logical operation to the IP address, effectively separating the network bits from the host bits.
In a subnet mask, binary ones represent the network portion, while zeros represent the host portion. When a device compares its IP address with a subnet mask, it can determine whether another device is on the same network or a different one. If both devices share the same network portion after applying the subnet mask, they can communicate directly. If not, the data must be sent through a router.
Subnet masks are essential because they define the structure of the network. Without them, devices would not be able to distinguish between local and remote destinations, leading to communication failures and inefficiencies.
Binary Representation in Subnetting
Subnetting relies heavily on binary mathematics because computers operate using binary systems. Every IPv4 address and subnet mask can be converted into binary form, which makes it easier to understand how networks are divided.
In binary, each bit has a value of either 0 or 1. When subnetting, changing even a single bit can significantly alter the size and structure of a network. Network administrators must carefully calculate how many bits to borrow from the host portion to create subnets.
For example, if more bits are borrowed from the host portion, more subnets can be created, but each subnet will have fewer available host addresses. On the other hand, borrowing fewer bits results in fewer subnets but allows more hosts per subnet. This balance is a critical aspect of subnet design and depends entirely on the requirements of the organization.
Network Classes and Their Importance
Originally, IPv4 addresses were divided into classes: Class A, Class B, and Class C. Each class had a fixed network and host structure. Class A networks were designed for very large organizations, Class B for medium-sized networks, and Class C for smaller networks.
Class A addresses used a large portion of bits for hosts, allowing millions of devices in a single network. Class B provided a balanced structure for moderate-sized networks, while Class C was designed for smaller networks with fewer hosts.
However, this class-based system proved to be inefficient over time because it wasted large numbers of IP addresses. Many organizations received more addresses than they needed, while others struggled with shortages. This led to the development of subnetting and later Classless Inter-Domain Routing (CIDR), which provided a more flexible approach to IP allocation.
Why Subnetting is Necessary
Subnetting is essential for several reasons, all of which contribute to better network performance and management. One of the primary reasons is efficient IP address utilization. Instead of assigning large blocks of IP addresses to a single network, subnetting allows administrators to allocate only what is needed.
Another major reason is improved network performance. In large networks without subnetting, broadcast traffic can become overwhelming. Every device receives broadcast messages, even if they are not relevant. Subnetting limits broadcast domains, reducing unnecessary traffic and improving overall speed.
Security is another important benefit. By separating a network into subnets, administrators can isolate sensitive systems from general users. This reduces the risk of unauthorized access and limits the spread of potential network attacks.
Subnetting also simplifies network management. Large organizations often have multiple departments such as HR, finance, IT, and operations. Each department can be assigned its own subnet, making it easier to monitor, troubleshoot, and control network activity.
Understanding CIDR Notation
Classless Inter-Domain Routing (CIDR) is a modern method used to represent IP addresses and their associated subnet masks. Instead of using traditional dotted-decimal subnet masks, CIDR uses a slash notation. This notation indicates how many bits are used for the network portion of the address.
For example, an IP address followed by “/24” means that the first 24 bits are used for the network, while the remaining bits are used for hosts. This method provides greater flexibility compared to the older class-based system. It allows network designers to create networks of varying sizes without being restricted to fixed classes.
CIDR also plays a major role in routing efficiency on the internet. It reduces the size of routing tables by allowing multiple IP addresses to be grouped together as a single routing entry. This improves the speed and scalability of global networks.
Subnetting and Network Efficiency
One of the key advantages of subnetting is its ability to improve network efficiency. By dividing a large network into smaller segments, data transmission becomes more organized and controlled. Devices within the same subnet can communicate directly without involving routers, which reduces latency and improves speed.
Subnetting also reduces network congestion. In a large flat network, every broadcast message is sent to all devices. This creates unnecessary traffic and slows down communication. By creating smaller broadcast domains, subnetting ensures that broadcast traffic is limited to relevant devices only.
Furthermore, subnetting allows better fault isolation. If a problem occurs in one subnet, it does not necessarily affect the entire network. This makes troubleshooting easier and reduces downtime.
Practical Concept of Subnet Division
When a network is subnetted, bits from the host portion of the IP address are borrowed to create additional network segments. Each borrowed bit doubles the number of possible subnets but reduces the number of available hosts per subnet.
For example, if one bit is borrowed, the number of subnets doubles. If two bits are borrowed, the number of subnets increases further, but host capacity decreases accordingly. This trade-off is a fundamental concept in subnet design.
Network engineers must carefully analyze requirements before designing a subnet structure. Factors such as number of departments, number of devices per department, and future scalability must all be considered. A poorly designed subnet can lead to inefficiencies or the need for redesign later.
Subnetting in Binary and Bit Manipulation
Subnetting becomes clearer when viewed through the lens of binary mathematics. Every IPv4 address is composed of 32 bits, and subnetting works by manipulating these bits to create new network boundaries. In binary form, a subnet mask is a sequence of consecutive ones followed by zeros. The ones represent the network portion, while the zeros represent the host portion.
When subnetting is performed, bits are borrowed from the host section and added to the network section. This changes the subnet mask and increases the number of available networks. Each borrowed bit doubles the number of subnets because binary systems operate on powers of two. At the same time, each borrowed bit reduces the number of host addresses available in each subnet.
This balance between subnet count and host capacity is one of the most important aspects of subnet design. Network engineers must calculate carefully to ensure that enough subnets exist for organizational needs while still providing sufficient host addresses within each subnet.
For example, if a network originally supports 256 hosts and two bits are borrowed for subnetting, the number of subnets increases significantly, but each subnet now supports only a fraction of the original host capacity. This trade-off must always align with real-world requirements.
Subnet Masks and Their Practical Interpretation
Subnet masks are often represented in dotted decimal format, but their true function is based on binary logic. A subnet mask such as 255.255.255.0 represents a structure where the first 24 bits are network bits and the last 8 bits are host bits.
When a device sends data to another device, it uses the subnet mask to determine whether the destination is local or remote. This is done by performing a logical AND operation between the IP address and the subnet mask. If the resulting network address matches, the devices are on the same subnet. If not, the data must be routed through a gateway.
This process happens instantly and continuously in all network communication. Without subnet masks, devices would not be able to interpret network boundaries, leading to communication breakdowns and inefficient routing.
Creating Subnets Step by Step
Subnet creation follows a structured process that ensures accurate division of IP networks. The first step is identifying the original network and determining the number of required subnets. This depends on organizational structure, such as departments, locations, or functional groups.
The next step is deciding how many bits must be borrowed from the host portion. This decision determines both the number of subnets and the number of hosts per subnet. Once the borrowing process is complete, a new subnet mask is created based on the updated bit structure.
After defining the subnet mask, the next step is calculating the range of IP addresses available within each subnet. Each subnet has a network address, a range of usable host addresses, and a broadcast address. The network address identifies the subnet itself, the host addresses are assigned to devices, and the broadcast address is used to communicate with all devices in that subnet.
This structured approach ensures that IP allocation remains organized and prevents address conflicts within the network.
Network Address, Broadcast Address, and Usable Hosts
Each subnet contains three important components: the network address, the broadcast address, and usable host addresses. The network address is the first address in a subnet and is used to identify the subnet as a whole. It cannot be assigned to any device.
The broadcast address is the last address in the subnet and is used to send messages to all devices within that subnet simultaneously. Like the network address, it cannot be assigned to a host device.
Between these two lies the range of usable host addresses. These are the IP addresses that can be assigned to devices such as computers, printers, servers, and routers. The number of usable hosts depends on how many bits are allocated to the host portion of the address.
As more bits are borrowed for subnetting, the number of usable hosts decreases. This relationship is essential in subnet planning, as it directly impacts network scalability and device allocation.
Fixed-Length vs Variable-Length Subnetting
There are two main approaches to subnetting: fixed-length subnetting and variable-length subnetting. Fixed-length subnetting, also known as FLSM, divides a network into subnets of equal size. This approach is simple to design and manage but may lead to wasted IP addresses if subnet requirements vary.
Variable-length subnetting, known as VLSM, allows subnets of different sizes within the same network. This method is more flexible and efficient because it allocates IP addresses based on actual need rather than uniform distribution.
For example, a large department may require hundreds of IP addresses, while a small team may only need a few. VLSM allows network designers to assign larger subnets where needed and smaller subnets where appropriate, optimizing overall IP utilization.
Modern networks almost always use VLSM because of its efficiency and adaptability. It is especially useful in large enterprise environments where different departments have varying network requirements.
Subnetting and Routing Efficiency
Subnetting plays a major role in improving routing efficiency. Routers are responsible for directing data between different networks, and subnetting helps reduce the size and complexity of routing tables.
When networks are properly subnetted, routers can group multiple IP addresses into a single routing entry. This process is known as route aggregation or summarization. It reduces the workload on routers and speeds up data forwarding decisions.
Without subnetting, routing tables would become extremely large and difficult to manage, especially in global networks. Subnetting ensures that routing remains scalable and efficient, even as networks continue to grow.
Private IP Addressing and Subnetting
Private IP address ranges are commonly used within local networks and are not directly accessible from the internet. These ranges include specific blocks reserved for internal use. Subnetting is frequently applied within these private ranges to organize internal networks.
Organizations often assign different subnets to different departments using private IP ranges. For example, one subnet may be used for employees, another for servers, and another for guest access. This separation improves security and control while maintaining internal connectivity.
Even though these subnets are private, they still follow the same subnetting principles as public networks. Routers within the organization manage communication between these subnets and ensure proper data flow.
Subnetting in Real-World Network Design
In real-world networking, subnetting is used to design scalable and efficient systems. Large organizations often have thousands of devices spread across multiple locations. Without subnetting, managing such a network would be extremely complex.
By dividing networks into subnets, administrators can group devices logically. For example, each office location may have its own subnet, or each department within a building may be assigned a separate subnet. This structure simplifies network management and improves troubleshooting.
Subnetting also helps in implementing security policies. Access control rules can be applied at the subnet level, restricting or allowing communication between different parts of the network. This adds an additional layer of protection against unauthorized access and internal threats.
Challenges in Subnet Design
While subnetting provides many advantages, it also presents certain challenges. One of the main challenges is accurate planning. Incorrect subnet design can lead to IP address shortages or inefficient usage of address space.
Another challenge is scalability. Networks must be designed with future growth in mind. If too few IP addresses are allocated to a subnet, expansion may require redesigning the entire network structure.
Complexity is also a factor, especially when using variable-length subnetting. Although VLSM is efficient, it requires careful calculation and documentation to avoid errors. Misconfiguration can lead to communication issues or routing conflicts.
Advanced Subnetting Concepts and CIDR Aggregation
As networking systems grow larger and more complex, basic subnetting is no longer sufficient on its own. Advanced subnetting concepts such as CIDR aggregation become essential for managing large-scale networks efficiently. Classless Inter-Domain Routing (CIDR) allows multiple subnets to be grouped into a single routing entry, reducing the size of routing tables and improving overall network performance.
CIDR aggregation works by combining contiguous IP address blocks that share a common prefix. Instead of listing each subnet individually, routers can treat them as a single summarized route. This significantly reduces the workload on routing devices and allows faster decision-making when forwarding data packets.
For example, instead of managing multiple small subnets separately, a network administrator can summarize them into a larger block that represents all of them. This concept is especially important in internet service provider networks where thousands of routes must be managed efficiently.
Supernetting and Route Summarization
Supernetting is the opposite of subnetting. While subnetting divides a network into smaller segments, supernetting combines multiple networks into a larger one. This technique is primarily used in routing optimization.
Route summarization is a key application of supernetting. It allows routers to advertise a single route that represents multiple networks. This reduces routing table size and improves performance by minimizing the number of entries a router must process.
In large-scale networks, especially those spanning multiple regions or data centers, route summarization plays a crucial role in maintaining scalability. Without it, routing tables would grow excessively large, leading to slower network performance and increased hardware requirements.
Variable-Length Subnet Mask (VLSM) in Depth
Variable-Length Subnet Masking (VLSM) is an advanced subnetting technique that allows different subnet sizes within the same network. Unlike traditional fixed-length subnetting, VLSM provides flexibility by allocating IP addresses based on actual need rather than uniform distribution.
In VLSM, the same network can contain both large and small subnets. This makes it highly efficient for organizations with varying departmental sizes. For instance, a server department may require a large number of IP addresses, while a security or management team may require only a few. VLSM ensures that IP address space is not wasted.
The implementation of VLSM requires careful planning and hierarchical design. Subnets must be assigned in a structured order, typically from largest to smallest, to avoid overlap and ensure proper address utilization.
VLSM is widely used in modern enterprise networks because it maximizes IP efficiency and supports scalable network design.
Subnetting and Network Hierarchy Design
Subnetting plays a vital role in creating hierarchical network structures. A well-designed network is typically divided into multiple layers, such as core, distribution, and access layers. Each layer may contain multiple subnets depending on its function and size.
The access layer connects end devices such as computers and printers. The distribution layer handles routing between subnets, while the core layer ensures high-speed data transfer across the network backbone. Subnetting allows each of these layers to be logically separated and efficiently managed.
This hierarchical approach improves performance, simplifies troubleshooting, and enhances security. By isolating network segments, administrators can apply specific policies to different parts of the network without affecting the entire system.
Broadcast Control and Traffic Optimization
One of the most important benefits of subnetting is broadcast control. In a non-subnetted network, broadcast messages are sent to all devices, which can lead to network congestion and reduced performance. Subnetting limits the scope of broadcast traffic to individual subnets.
Each subnet acts as its own broadcast domain. This means that broadcast messages are only received by devices within the same subnet. As a result, unnecessary traffic is significantly reduced, improving overall network efficiency.
Traffic optimization is another key advantage. By dividing networks into smaller segments, data flows more efficiently because fewer devices are competing for bandwidth within each subnet. This leads to faster communication and reduced latency.
Subnetting in Enterprise Environments
In enterprise environments, subnetting is used to organize large-scale infrastructures that support thousands of users and devices. Each department or business unit is typically assigned its own subnet. This allows for better control, monitoring, and resource allocation.
For example, a corporate network may assign separate subnets for human resources, finance, engineering, and guest users. Each subnet operates independently while still being part of the same organizational network.
This separation also improves security. Sensitive departments such as finance or administration can be isolated from general user networks, reducing the risk of unauthorized access or data breaches. Access control policies can be enforced at the subnet level to further enhance protection.
Subnetting in Data Centers and Cloud Networks
Modern data centers and cloud computing environments rely heavily on subnetting for scalability and performance. In these environments, thousands or even millions of virtual machines may exist across multiple physical servers.
Subnetting allows cloud providers to organize these virtual resources efficiently. Each tenant or customer can be assigned isolated subnets, ensuring data separation and security. This is particularly important in multi-tenant environments where multiple users share the same infrastructure.
In addition, subnetting enables dynamic scaling. As demand increases, new subnets can be created quickly to accommodate additional resources. This flexibility is essential for cloud environments where workloads frequently change.
Security Implications of Subnetting
Subnetting is not only a tool for organization but also a critical component of network security. By dividing a network into smaller segments, administrators can implement security boundaries that restrict unauthorized communication.
Firewalls and access control lists can be configured to allow or deny traffic between specific subnets. This ensures that even if one part of the network is compromised, the attack does not easily spread to other segments.
Subnetting also supports network segmentation strategies used in cybersecurity frameworks. Sensitive systems, such as databases and authentication servers, are often placed in isolated subnets with strict access controls.
Common Subnetting Mistakes and Misconfigurations
Despite its importance, subnetting is often prone to configuration errors. One common mistake is incorrect calculation of subnet masks, which can lead to overlapping networks or address conflicts.
Another issue is poor planning of IP address allocation. If subnets are not designed with future growth in mind, organizations may quickly run out of available addresses, requiring network redesign.
Misconfigured routing tables can also cause communication failures between subnets. If routers are not properly updated with subnet information, data packets may be lost or incorrectly forwarded.
To avoid these issues, careful documentation and planning are essential in any subnetting implementation.
Subnetting and Network Scalability
Scalability is one of the most important benefits of subnetting. As organizations grow, their network requirements increase. Subnetting allows networks to expand without requiring complete redesign.
New subnets can be added as needed, and existing subnets can be modified or resized using advanced techniques such as VLSM. This flexibility ensures that the network can adapt to changing demands over time.
Scalable network design is essential in modern IT environments where growth is constant and unpredictable. Subnetting provides the foundation for this adaptability.
Future of IPv4 Subnetting and Transition to IPv6
Although IPv4 subnetting remains widely used, the growing demand for IP addresses has led to the development of IPv6. IPv6 uses a much larger address space, which reduces the need for traditional subnetting in terms of address scarcity.
However, subnetting principles still apply in IPv6 networks. Network segmentation, hierarchy, and traffic control remain essential concepts regardless of address size.
In fact, subnetting becomes even more important in large IPv6 deployments because of the massive scale of address space available. Proper planning ensures efficient routing and organization even in next-generation networks.
Practical Subnetting Methodologies in Real Networks
In real-world networking, subnetting is not performed randomly or theoretically. It follows structured methodologies that ensure accuracy, scalability, and long-term efficiency. Network engineers begin by analyzing the total number of required networks and the number of hosts needed in each segment. This requirement-based approach ensures that IP address allocation aligns with actual operational needs rather than guesswork.
Once requirements are identified, engineers determine the appropriate subnet mask that can support both the number of subnets and hosts. This involves calculating how many bits must be borrowed from the host portion. Each decision directly affects network capacity, so precision is essential. Even a small miscalculation can result in wasted IP addresses or insufficient host availability.
After defining subnet requirements, engineers map out the entire address space. This includes identifying network addresses, usable host ranges, and broadcast addresses for each subnet. This planning stage ensures that no overlap occurs and that the network remains logically organized.
Subnetting Design for Scalability
Scalability is one of the most important goals in network design. Subnetting plays a critical role in ensuring that networks can grow without requiring complete redesign. A scalable subnet design anticipates future expansion by reserving unused address space or by using flexible addressing schemes like VLSM.
In scalable environments, subnet boundaries are carefully chosen so that additional subnets can be added without disrupting existing configurations. This prevents network downtime and reduces administrative overhead when changes are required.
Scalable subnetting also ensures that routing remains efficient even as the number of devices increases. Without proper design, routing tables can become overloaded, leading to slower performance and increased processing time on routers.
Hierarchical IP Addressing Structures
Hierarchical addressing is a structured approach to subnet design that organizes networks into multiple layers. This structure mirrors organizational hierarchies, making it easier to manage large systems.
At the top level, large blocks of IP addresses are assigned to major network divisions. These are then subdivided into smaller blocks for departments, and further divided into subnets for individual groups or functions. This top-down approach ensures logical organization and simplifies troubleshooting.
Hierarchical subnetting also improves routing efficiency. Routers can summarize multiple subnets under a single route entry, reducing complexity in routing tables. This allows faster decision-making when forwarding packets across large networks.
Role of Subnetting in Network Performance Optimization
Subnetting significantly enhances network performance by reducing unnecessary traffic and improving data flow efficiency. In a flat network architecture, every device receives broadcast messages, which can lead to congestion. Subnetting eliminates this issue by dividing networks into smaller broadcast domains.
Each subnet operates independently, meaning broadcast traffic is limited to devices within that subnet only. This reduces bandwidth consumption and improves response times across the network.
In addition, subnetting reduces collision domains in traditional Ethernet networks. By limiting the number of devices sharing the same network segment, data collisions are minimized, resulting in smoother communication.
Advanced Address Planning Strategies
Effective subnetting requires advanced address planning strategies that take into account both current and future needs. One common strategy is allocating IP address blocks in powers of two, which aligns with binary addressing systems.
Another strategy involves reserving address space for future expansion. Instead of using all available addresses immediately, network designers leave gaps between subnets. This allows new subnets to be inserted later without restructuring the entire network.
Some organizations also use structured numbering systems for subnets, making it easier to identify network locations or functions based on IP ranges. This improves documentation and simplifies troubleshooting processes.
Subnetting in Large-Scale Enterprise Architecture
In large enterprises, subnetting is used to create highly organized and segmented network infrastructures. Each business unit, office location, or operational function is assigned its own subnet or group of subnets.
For example, an organization may separate its network into multiple regions, with each region containing its own internal subnet structure. Within those regions, departments such as finance, operations, and IT may have further subdivisions. This layered approach ensures clarity and control.
Large enterprises also rely heavily on subnetting for policy enforcement. Security rules, bandwidth limitations, and access controls can be applied at the subnet level, allowing granular control over network behavior.
Subnetting and Network Troubleshooting
Subnetting simplifies network troubleshooting by isolating problems to specific segments. When a network issue occurs, administrators can quickly determine which subnet is affected rather than analyzing the entire network.
Because each subnet has its own defined address range, it becomes easier to trace misconfigurations or connectivity issues. Tools such as ping, traceroute, and network analyzers are often used within specific subnets to diagnose problems efficiently.
Without subnetting, troubleshooting would be significantly more complex, as issues could span large, unorganized networks with no clear boundaries.
Subnetting and Access Control Mechanisms
Subnetting plays an important role in implementing access control mechanisms within networks. By dividing networks into subnets, administrators can define rules that control which devices can communicate with each other.
Firewalls and routers can be configured to allow or block traffic between specific subnets. This allows organizations to enforce strict security policies. For example, guest networks can be isolated from internal corporate systems, preventing unauthorized access to sensitive data.
Subnet-based access control also helps reduce the attack surface of a network. If one subnet is compromised, the attacker’s ability to move laterally across the network is limited by segmentation rules.
Address Conservation and Efficient Allocation
One of the primary goals of subnetting is efficient IP address utilization. IPv4 has a limited address space, making conservation extremely important. Subnetting ensures that IP addresses are allocated based on actual need rather than fixed blocks.
Without subnetting, large numbers of IP addresses would remain unused or wasted. This was a common issue in early networking systems where class-based addressing allocated more addresses than necessary.
By using subnetting techniques such as VLSM, organizations can allocate small or large address blocks depending on requirements, ensuring minimal waste and maximum efficiency.
Subnetting in Virtualized and Cloud Environments
Modern cloud and virtualization technologies rely heavily on subnetting to manage large-scale distributed systems. In virtualized environments, multiple virtual machines may share physical hardware while remaining logically separated through subnets.
Cloud service providers use subnetting to isolate customer environments, ensuring data privacy and security. Each customer may be assigned one or more subnets depending on their infrastructure requirements.
Subnetting also enables dynamic resource allocation in cloud environments. As workloads increase, new subnets can be created automatically to support additional virtual machines or services. This flexibility is essential for modern scalable computing systems.
Subnetting and Network Documentation
Proper documentation is essential in subnetting design. Without accurate records, managing complex networks becomes extremely difficult. Documentation typically includes subnet ranges, subnet masks, gateway addresses, and assigned device groups.
Well-documented subnet structures help administrators quickly identify network layouts and resolve issues efficiently. It also ensures consistency when multiple engineers work on the same network infrastructure.
In large organizations, subnet documentation is often maintained using centralized systems or network management tools to ensure accuracy and accessibility.
Common Subnetting Challenges in Practice
Despite its advantages, subnetting presents several challenges in real-world implementation. One major challenge is human error during calculation. Incorrect subnet mask configuration can lead to overlapping networks or unreachable devices.
Another challenge is inefficient planning. If subnet sizes are not properly aligned with actual usage, some subnets may become overcrowded while others remain underutilized.
Scalability issues can also arise if subnet structures are not designed with future growth in mind. Expanding a poorly designed network often requires significant restructuring, which can be time-consuming and costly.
Importance of Standardization in Subnetting
Standardization plays a crucial role in maintaining consistency across large networks. By following standardized subnetting practices, organizations ensure that all network segments follow a uniform structure.
Standardization simplifies management, improves documentation, and reduces the likelihood of configuration errors. It also makes it easier for network engineers to understand and work with existing infrastructure, even if they were not involved in its original design.
Evolution of Subnetting in Modern Networking
Subnetting has evolved significantly since its introduction. Early networking systems relied on fixed class-based addressing, which was inefficient and inflexible. The introduction of CIDR and VLSM transformed subnetting into a dynamic and scalable system.
Today, subnetting is integrated into nearly every aspect of networking, from small office networks to global internet infrastructure. Even with the introduction of IPv6, subnetting principles remain relevant for network organization and traffic management.
Future Relevance of Subnetting
Although IPv6 provides a vastly larger address space, subnetting will continue to play a critical role in network design. Modern networks still require segmentation for performance, security, and management purposes.
In future networking environments, subnetting will likely become even more abstract and automated. Software-defined networking (SDN) and artificial intelligence-based network management systems may handle subnet creation dynamically based on demand.
However, the foundational principles of subnetting will remain unchanged, making it an essential concept for all network professionals.
Conclusion
IPv4 subnetting is a foundational concept in networking that enables efficient, scalable, and secure network design. Across all four parts, it becomes clear that subnetting is not just a mathematical process but a critical architectural strategy used in modern network systems.
It allows networks to be divided into manageable segments, improves performance by reducing broadcast traffic, enhances security through isolation, and supports scalability for future growth. From small local networks to large enterprise and cloud infrastructures, subnetting remains essential for organized communication.
Understanding subnetting deeply provides the foundation for advanced networking concepts such as CIDR, VLSM, routing optimization, and cloud networking. Even as technology evolves toward IPv6 and software-defined networks, the principles of subnetting continue to shape how digital communication systems are designed and managed.