Every organization that relies on computers, networks, and digital systems also depends on physical infrastructure that supports those technologies. While cybersecurity often focuses on firewalls, encryption, and threat detection, physical security is just as important because it protects the real-world assets that make digital operations possible. Buildings, hardware, documents, and equipment all form part of an organization’s foundation, and if these are compromised, even the strongest cyber defenses can become irrelevant.
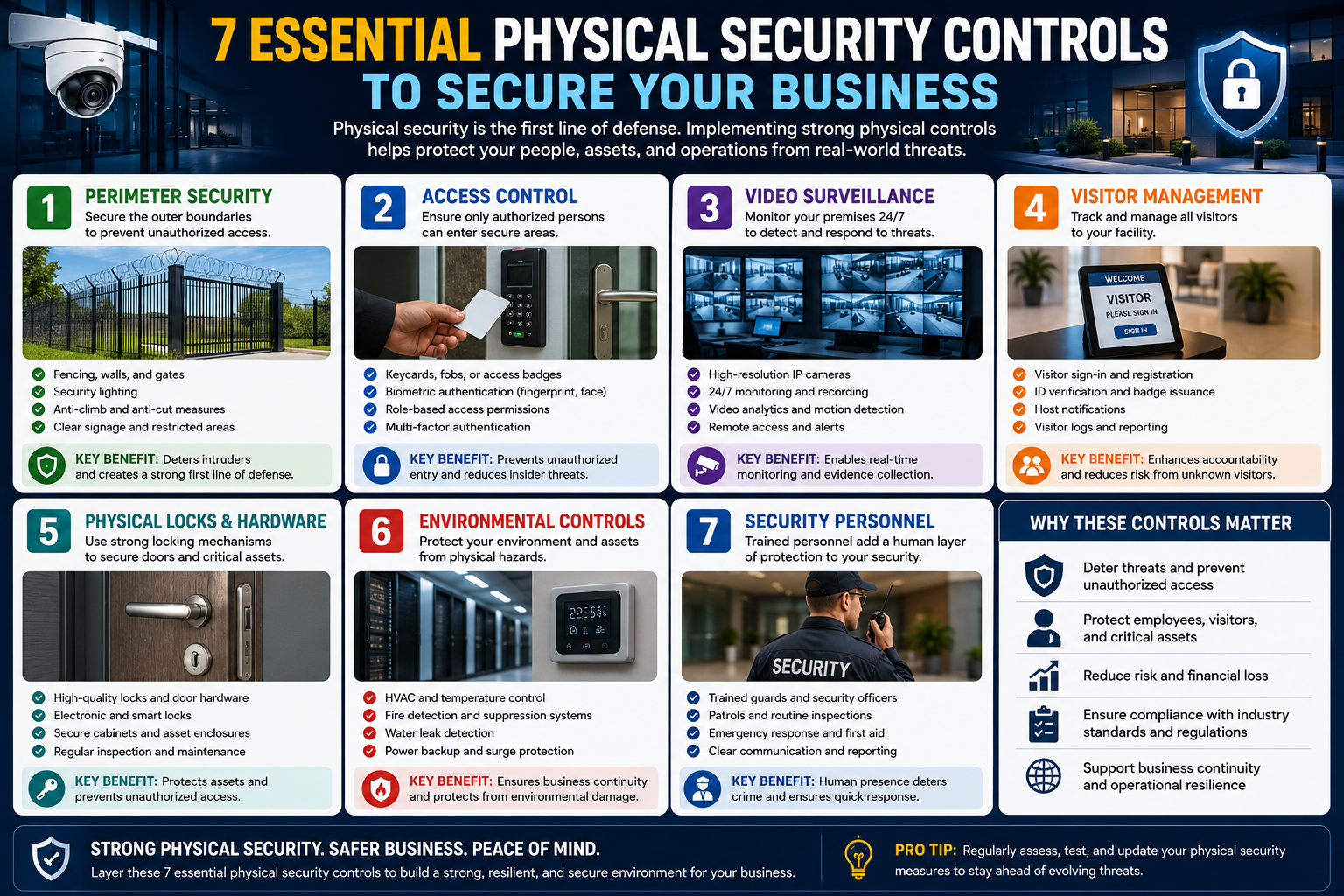
Physical security controls are designed as layered protections that reduce the risk of unauthorized access, theft, and damage. These controls work together in a balanced way, combining prevention, detection, and response. No single control is sufficient on its own, but when combined, they create a strong security posture that protects both data and physical resources. This layered approach ensures that even if one control fails, others are in place to reduce exposure and limit potential impact. It also improves resilience by addressing different types of threats at multiple points of entry. Organizations benefit from this strategy because it not only deters attackers but also provides early warning, improves response time, and supports overall risk management effectiveness.
Fences as the First Layer of Defense
One of the most basic but important physical security measures is perimeter fencing. Although it may seem simple, fencing plays a critical role in defining boundaries and preventing unauthorized access to a property. It acts as the first visible barrier that discourages intruders from approaching sensitive areas.
Fences are not meant to stop highly determined attackers on their own, but they significantly reduce casual trespassing and force anyone attempting entry to take more time and effort. This delay is valuable because it increases the chance of detection by other security systems or personnel. Depending on the organization’s risk level, fences can vary from simple chain-link barriers to reinforced walls with anti-climb features.
The main purpose of fencing is deterrence and delay. It ensures that physical security starts before anyone even reaches the building itself.
Security Cameras for Monitoring and Evidence
Surveillance cameras are one of the most widely used physical security controls in modern organizations. They serve two main purposes: deterrence and recording. When people know they are being watched, they are less likely to engage in suspicious or unauthorized activities. At the same time, cameras provide valuable evidence in the event of an incident.
Modern camera systems are highly advanced compared to older versions. They can record high-definition video, store footage digitally, and allow users to quickly search recordings based on time and date. This makes investigations much faster and more efficient.
Many systems are connected through existing network infrastructure, which simplifies installation and management. Some cameras also include motion detection, night vision, and smart alerts that notify security teams when unusual activity is detected. Strategic placement of cameras at entrances, exits, hallways, and restricted areas ensures complete coverage of critical zones.
Alarm Systems for Immediate Response
Alarm systems add a reactive layer to physical security. While fences and cameras focus on prevention and monitoring, alarms are designed to alert people when a breach or emergency occurs. These systems can detect unauthorized entry, motion in restricted areas, fire, smoke, or other environmental threats. Once triggered, they immediately notify security personnel and can also activate sirens, flashing lights, or automated alerts to discourage intruders and prompt a fast response.
Modern alarm systems are often integrated with centralized monitoring centers, allowing real-time communication with emergency services when necessary. This rapid detection and response capability significantly reduces potential damage, improves incident handling speed, and strengthens overall security by ensuring that threats are addressed as quickly as possible.
When triggered, alarms can produce loud sounds, flashing lights, or automated notifications to security personnel. This immediate response helps reduce damage by ensuring that action is taken quickly. In some cases, alarms are directly connected to emergency services, allowing for rapid external response.
Alarm systems are especially important because they provide real-time awareness. Even if an intruder bypasses other controls, alarms ensure that the situation does not go unnoticed.
Access Control Systems for Restricted Entry
Access control systems regulate who can enter specific areas within a facility. Instead of allowing unrestricted movement, these systems ensure that only authorized individuals can access certain rooms, buildings, or zones.
Traditional methods include physical keys, but modern systems often use electronic solutions such as keycards, PIN codes, or biometric verification like fingerprints or facial recognition. These technologies offer greater flexibility and control over access permissions.
One major advantage of electronic access systems is the ability to quickly deactivate credentials. If an employee loses a keycard, it can simply be disabled without changing physical locks. Additionally, access logs provide detailed records of who entered which area and at what time, improving accountability.
However, access systems must be carefully managed because no technology is completely immune to risk. Regular updates, monitoring, and policy enforcement are essential to maintaining their effectiveness.
Proper Lighting for Visibility and Deterrence
Lighting is often overlooked but plays a powerful role in physical security. Well-lit environments reduce hiding spots and make it easier for security cameras and personnel to identify suspicious activity. Poor lighting, on the other hand, creates opportunities for intruders to move unnoticed.
Proper illumination should cover all critical areas such as entrances, parking lots, hallways, staircases, and perimeter boundaries to eliminate dark zones that could be exploited. Motion-activated lighting can also improve efficiency by activating only when movement is detected, helping conserve energy while still enhancing security. In addition, consistent lighting improves the effectiveness of surveillance systems by ensuring clearer video quality and reducing blind spots. Emergency lighting is equally important, providing visibility during power failures so that safety and security are not compromised in critical situations.
Outdoor lighting should be installed around building entrances, parking areas, pathways, and vulnerable perimeter zones. Indoor lighting is equally important, especially in hallways, staircases, and less frequently used areas.
Emergency lighting systems also provide backup illumination during power failures. These systems ensure that people can safely navigate the building and that security operations are not disrupted during outages.
Good lighting contributes to both safety and psychological deterrence, making it less attractive for unauthorized individuals to attempt entry.
Secure Disposal of Documents and Equipment
Proper disposal of sensitive materials is a critical but often ignored aspect of physical security. Organizations regularly handle confidential documents, outdated equipment, and storage devices that may contain valuable information. If these materials are not destroyed properly, they can become a major security risk.
Paper documents should be shredded using secure disposal methods to ensure that information cannot be reconstructed. In some cases, specialized services handle large-scale destruction to guarantee complete confidentiality.
Electronic devices such as computers and hard drives require even more careful handling. Simply deleting files is not enough, as data can often be recovered. Instead, devices should be properly wiped using secure methods or physically destroyed when they are no longer needed.
Responsible disposal practices protect organizations from data leaks, corporate espionage, and accidental exposure of sensitive information.
Regular Audits and Maintenance of Security Systems
Security systems are only effective if they are properly maintained. Over time, equipment can fail, policies can become outdated, and vulnerabilities can emerge. Regular audits help ensure that all physical security controls continue to function as intended. These audits should be scheduled regularly rather than performed only after an incident, ensuring continuous protection and early detection of weaknesses.
They typically include reviewing access logs, testing alarms, inspecting surveillance cameras, and confirming that all entry points are properly secured and functioning. Organizations also benefit from assigning responsibility to trained security staff or external auditors who can provide an objective evaluation of existing systems. By identifying gaps early, companies can reduce the likelihood of breaches, equipment failure, and unauthorized access that could lead to serious operational or financial loss. This proactive approach strengthens overall security posture across all physical assets.
Audits involve checking cameras, testing alarms, reviewing access logs, and inspecting physical barriers such as fences and locks. They also include verifying that emergency systems like lighting and alarms are operational.
Another important aspect is ensuring that former employees no longer have access to restricted areas. Access credentials should be updated regularly, and unused permissions should be removed promptly.
Routine inspections also help identify small issues before they become serious problems. For example, a broken camera or a malfunctioning sensor may go unnoticed until a security incident occurs. Regular maintenance prevents such gaps in protection.
Conclusion
Physical security is a fundamental part of any organization’s overall protection strategy. While digital defenses protect data and networks, physical controls safeguard the real-world assets that support those systems. Fences, cameras, alarms, access control systems, lighting, secure disposal methods, and regular audits all work together to create a strong, layered security environment.
Each control serves a specific purpose, but their true strength lies in how they complement one another. When implemented effectively, these measures reduce risks, improve response times, and ensure that both people and assets remain safe. A well-designed physical security strategy is not just about preventing theft or intrusion—it is about creating a secure foundation that supports the entire organization.