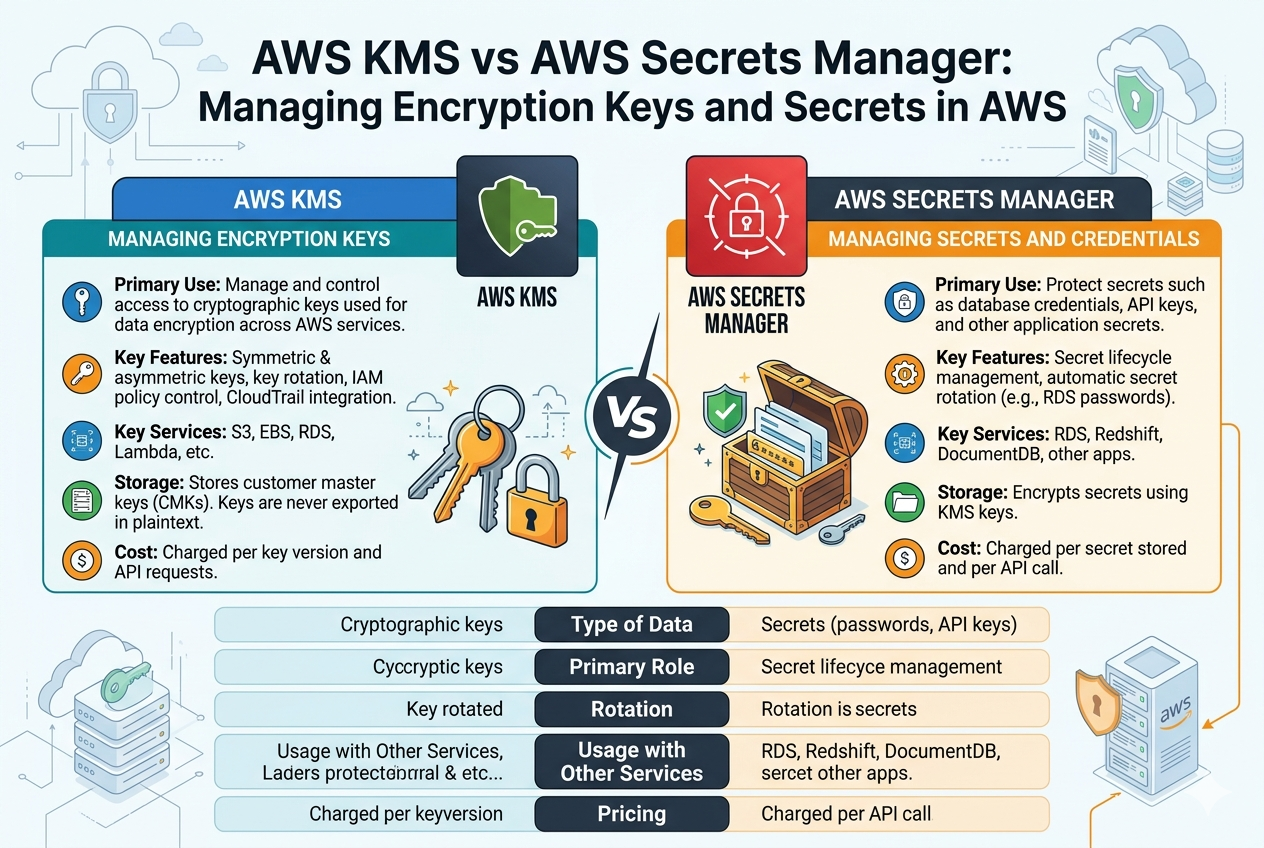
In large-scale cloud-native systems, security is not just about storing data safely but about designing an architecture that enforces protection at every layer. AWS KMS and AWS Secrets Manager often function together within complex systems, but their proper placement in architecture requires careful planning. When organizations move beyond basic usage, they start to treat encryption and secret management as foundational building blocks rather than optional features. This shift is critical for systems that handle financial data, healthcare records, authentication systems, or any workload where sensitive information flows continuously.
A well-architected security model typically begins with AWS KMS acting as the root of trust. Every encryption decision in the system is tied back to cryptographic keys managed centrally. Instead of allowing individual applications to generate or store encryption keys, KMS enforces a controlled environment where key usage is logged, monitored, and restricted. This creates a strong boundary between data and encryption logic, ensuring that even if an application is compromised, the attacker cannot easily extract encryption keys.
At the same time, Secrets Manager handles a completely different layer of the architecture. Applications frequently require dynamic credentials to connect to databases, external APIs, or internal microservices. Embedding these credentials directly into code introduces significant risks, especially in distributed systems where multiple services interact. Secrets Manager eliminates this problem by acting as a centralized vault that delivers secrets only when needed and only to authorized entities.
The combination of both services enables a layered defense strategy. Even if secrets are exposed, encryption keys remain protected under KMS governance. Similarly, even if encrypted data is accessed, it remains unusable without proper decryption permissions. This separation of responsibilities is one of the most powerful security patterns in cloud architecture.
Deep Dive into Encryption Key Hierarchies in AWS KMS
AWS KMS does not simply store a single type of key. Instead, it uses a hierarchical model where multiple layers of keys work together to provide encryption security. At the top level are customer-managed keys, which give organizations full control over key policies, rotation schedules, and access permissions. These keys are often used when compliance requirements demand strict governance over encryption processes.
Underneath this layer, KMS internally uses envelope encryption. In this model, data is encrypted using a data key, and that data key is then encrypted using a master key stored in KMS. This approach improves performance while maintaining strong security guarantees. Instead of repeatedly calling KMS for large data encryption operations, applications use data keys locally while still benefiting from KMS-level protection.
This hierarchical structure is particularly important in high-performance systems where large volumes of data need to be encrypted and decrypted frequently. By separating data encryption from key encryption, KMS ensures that performance bottlenecks are minimized while maintaining cryptographic security.
Operational Complexity and Secret Lifecycle Management
While AWS KMS focuses on cryptographic stability, AWS Secrets Manager deals with operational fluidity. Secrets in real-world systems are rarely static. Database passwords expire, API keys are rotated, and third-party integrations change authentication mechanisms. Managing these changes manually introduces operational risk and increases the likelihood of downtime.
Secrets Manager addresses this challenge through automated lifecycle management. Secrets can be rotated automatically on a schedule, ensuring that credentials remain fresh without requiring manual intervention. This is particularly important in systems that require high availability, where even a small misconfiguration during credential updates could lead to service outages.
The rotation process is designed to be seamless. Applications retrieve the latest version of a secret at runtime, meaning they do not need to be redeployed or restarted when credentials change. This decoupling of configuration from application logic is a key advantage in modern cloud environments.
Security Governance and Access Control Models
Security in AWS is heavily dependent on well-designed access control policies. Both KMS and Secrets Manager rely on identity-based permissions, but their enforcement models differ slightly due to their functional roles.
In AWS KMS, access control is tightly linked to key usage operations. Policies define who can encrypt data, who can decrypt data, and who can administer the keys themselves. This separation ensures that administrative access does not automatically grant data access, and vice versa. Such granular control is essential in regulated environments where separation of duties is required.
In Secrets Manager, access control focuses on secret retrieval and modification. Applications typically require read access to retrieve secrets at runtime, while administrative roles manage creation, rotation, and deletion. The principle of least privilege is strongly enforced, ensuring that no entity has more access than necessary.
Both services also integrate with audit logging systems. Every key usage or secret retrieval event can be tracked, providing full visibility into how sensitive resources are being accessed across the environment. This auditability is critical for compliance frameworks and security investigations.
Performance Considerations in Encryption and Secret Retrieval
One often overlooked aspect of security services is performance impact. AWS KMS introduces API-based encryption operations, which means every encryption or decryption request involves network communication. While this is acceptable for most use cases, high-frequency operations require careful design to avoid latency bottlenecks.
To address this, applications often rely on caching strategies or envelope encryption to reduce the number of direct KMS calls. By encrypting data locally using data keys and only using KMS to protect those keys, systems achieve both performance efficiency and strong security.
Secrets Manager also introduces latency when retrieving secrets, especially during cold starts in serverless environments. However, caching mechanisms at the application level can significantly reduce repeated calls. Many architectures design secret retrieval to occur once during initialization rather than on every request, balancing security and performance.
Cost Implications of Using AWS KMS and Secrets Manager
Cost is another important factor when designing systems with these services. AWS KMS charges are typically based on the number of API requests and the number of keys stored. High-frequency encryption workloads can therefore accumulate costs over time if not optimized properly.
Secrets Manager, on the other hand, charges based on the number of stored secrets and API calls for retrieval. Automated rotation can also influence cost depending on frequency. While these costs are generally justified by the security benefits, inefficient design choices can lead to unnecessary expenses.
For example, repeatedly calling Secrets Manager for every application request instead of caching secrets can significantly increase costs without improving security. Similarly, excessive KMS API calls for small data operations can be optimized using envelope encryption strategies.
Common Mistakes in Implementing KMS and Secrets Manager
One of the most common mistakes in cloud security design is misusing AWS KMS for storing secrets. Some developers mistakenly attempt to store passwords or API keys directly in KMS, not realizing that it is not designed for secret storage. This leads to architectural inefficiencies and operational complexity.
Another frequent mistake is overusing Secrets Manager for data encryption purposes. Since Secrets Manager is not designed for cryptographic operations, using it as a replacement for KMS introduces security gaps and performance limitations.
Improper access control configuration is also a major issue. Overly permissive policies can expose sensitive keys or secrets to unintended users or services. On the other hand, overly restrictive policies can break application functionality. Achieving the right balance requires careful planning and continuous monitoring.
Real-World Architectural Patterns Using Both Services
In modern distributed systems, it is common to see both AWS KMS and Secrets Manager used together in a layered security model. A typical microservices architecture might use KMS to encrypt data stored in databases, object storage, and message queues, while Secrets Manager handles service-to-service authentication credentials.
For example, a web application might retrieve database credentials from Secrets Manager during startup. Those credentials are then used to connect to an encrypted database where the data itself is protected by KMS-managed keys. This dual-layer protection ensures that both access and data integrity are secured independently.
In serverless architectures, this pattern becomes even more important. Functions often require temporary access to secrets and encrypted data, and both services provide the necessary security primitives to support ephemeral workloads without compromising protection.
Best Practices for Secure Implementation
Designing secure systems with AWS KMS and Secrets Manager requires adherence to best practices. One important principle is minimizing direct exposure of secrets to application code. Instead of embedding credentials, applications should always retrieve them dynamically from Secrets Manager.
Another best practice is enabling automatic key rotation in KMS wherever possible. Regular key rotation reduces the risk of long-term key compromise and improves overall security hygiene.
It is also important to monitor usage patterns through logging and alerting. Unexpected spikes in KMS or Secrets Manager usage can indicate misconfiguration or potential security issues.
Finally, organizations should regularly review access policies to ensure that permissions remain aligned with operational needs. As systems evolve, access requirements change, and outdated permissions can become security risks.
Conclusion
AWS KMS and AWS Secrets Manager are foundational components of a secure cloud architecture, each serving a distinct but complementary role. KMS provides the cryptographic backbone for encryption, ensuring that data remains protected at rest and in transit. Secrets Manager, on the other hand, handles the operational complexity of managing sensitive credentials, ensuring that applications can securely access and rotate secrets without manual intervention.
When used together, these services create a layered security model that strengthens both data protection and operational security. Understanding their differences, strengths, and integration points allows organizations to build resilient systems that scale securely in modern cloud environments.