In modern network environments, efficient data delivery is essential for supporting applications that rely on real-time or large-scale data distribution. Multicast communication plays a crucial role in achieving this efficiency by allowing a single data stream to be delivered to multiple recipients simultaneously. Unlike unicast communication, where separate streams are sent to each receiver, multicast reduces unnecessary bandwidth consumption and improves overall network performance. This becomes especially important in scenarios such as live video streaming, online conferencing, financial data distribution, and enterprise-level application delivery where the same information must reach multiple endpoints at the same time.
However, while multicast is highly efficient at the network layer, it can become inefficient at the switching layer if not properly managed. This is where IGMP snooping becomes an essential mechanism. It helps switches intelligently control multicast traffic so that it is only forwarded to devices that actually need it, rather than flooding it across all ports within a network segment.
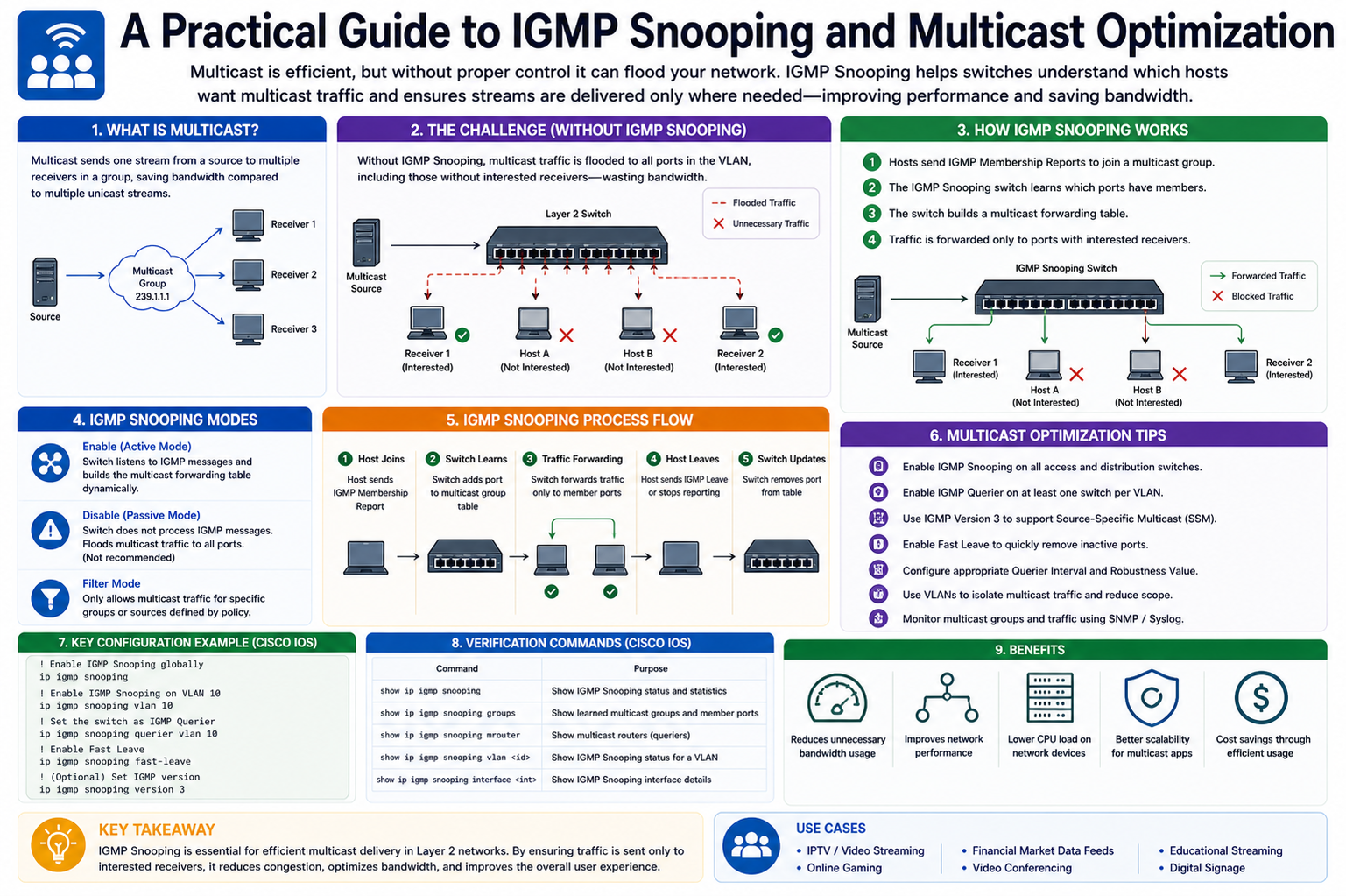
Understanding IGMP and Its Role in Multicast Networks
The Internet Group Management Protocol (IGMP) is a fundamental protocol used by IPv4 networks to manage multicast group memberships. It allows devices within a network to communicate their interest in receiving specific multicast traffic. When a device wants to join a multicast group, it sends IGMP membership reports to inform routers and switches. Similarly, when it no longer needs the multicast stream, it sends a leave message.
IGMP operates between hosts and routers, ensuring that multicast traffic is only sent where it is needed. Without IGMP, multicast traffic would be delivered blindly, leading to unnecessary bandwidth usage and potential network congestion. Although IGMP effectively manages group membership at a protocol level, it does not directly control how switches handle multicast frames within a local area network. This limitation is addressed by IGMP snooping.
What IGMP Snooping Means in a Switching Environment
IGMP snooping is a Layer 2 network switch feature that listens to IGMP traffic between hosts and routers. By “snooping” on IGMP messages, the switch learns which devices are interested in specific multicast groups. Based on this information, the switch builds a mapping table that associates multicast groups with specific ports.
Without IGMP snooping, switches typically flood multicast traffic to all ports in a VLAN, similar to broadcast traffic. This can lead to inefficiencies, especially in larger networks where only a small subset of devices actually require the multicast stream. IGMP snooping prevents this unnecessary flooding by ensuring that multicast packets are forwarded only to ports that have active group members.
This intelligent filtering significantly reduces network congestion, improves bandwidth utilization, and enhances overall performance in environments where multicast traffic is heavily used.
How IGMP Snooping Works Behind the Scenes
When IGMP snooping is enabled on a switch, it begins by monitoring all IGMP packets passing through it. These packets include membership reports, queries, and leave messages exchanged between hosts and multicast routers. The switch does not participate in these exchanges but passively listens to them.
As hosts send IGMP join messages to subscribe to a multicast group, the switch records the port number and associates it with the corresponding multicast group. When multiple devices on different ports join the same group, the switch updates its forwarding table accordingly.
When a device leaves a multicast group, the switch removes that port from the forwarding list for that group. If no ports remain subscribed, the switch stops forwarding that multicast stream entirely within that VLAN.
In addition, IGMP queries sent by routers help maintain active group memberships. If a switch does not receive periodic reports from a host, it assumes that the host is no longer interested in the multicast traffic and removes it from the group membership table.
Multicast Traffic Behavior Without IGMP Snooping
In networks where IGMP snooping is not enabled, multicast traffic behaves much like broadcast traffic at the Layer 2 level. This means that every multicast frame is forwarded to all ports within the VLAN, regardless of whether the connected devices need it or not.
This behavior can lead to several issues. First, it increases unnecessary load on network devices, including endpoints that must process unwanted traffic. Second, it wastes bandwidth, especially in environments with high-volume multicast streams such as video distribution systems. Third, it can degrade performance for latency-sensitive applications due to increased congestion.
As networks scale, these inefficiencies become more noticeable, making IGMP snooping a critical optimization feature for modern switching infrastructure.
Benefits of IGMP Snooping in Network Optimization
One of the primary advantages of IGMP snooping is its ability to significantly reduce unnecessary traffic flooding. By ensuring that multicast data is only sent to interested receivers, network efficiency is greatly improved.
Another important benefit is improved bandwidth utilization. Since multicast streams are not replicated across all ports, available bandwidth can be used more effectively for other critical applications. This is particularly valuable in enterprise networks where multiple services compete for limited resources.
IGMP snooping also enhances overall network performance by reducing CPU load on end devices. Devices no longer need to process irrelevant multicast packets, which helps improve responsiveness and reduces processing overhead.
Additionally, it contributes to better scalability. As the number of multicast-enabled applications and devices increases, IGMP snooping ensures that network performance remains stable without requiring major infrastructure changes.
Challenges and Limitations of IGMP Snooping
Despite its advantages, IGMP snooping is not without challenges. One common issue arises when there is no multicast router present in the network. In such cases, switches may not receive IGMP queries, leading to incomplete or inaccurate group membership tables. This can result in multicast traffic not being forwarded correctly.
Another challenge involves configuration complexity in large or hierarchical networks. If IGMP snooping is not consistently enabled across all switches, multicast traffic behavior can become unpredictable.
There can also be compatibility issues with certain network topologies or legacy devices that do not fully support IGMP standards. In such environments, administrators must carefully plan deployment to avoid service disruptions.
Key Concepts in Implementing IGMP Snooping
Proper implementation of IGMP snooping requires understanding several key concepts. One important concept is the role of the multicast router port, which is used by the switch to identify where IGMP queries originate. This port is typically treated differently from regular host ports.
Another important concept is the IGMP snooping table, which stores mappings between multicast groups and associated ports. This table is dynamically updated based on IGMP traffic observed by the switch.
It is also essential to understand the aging mechanism. If no IGMP membership reports are received within a certain time period, the switch removes the entry from its table to prevent stale mappings.
Best Practices for Efficient Multicast Optimization
To achieve optimal results with IGMP snooping, it is important to follow best practices in network design and configuration. Ensuring that IGMP snooping is enabled on all relevant switches is a fundamental step.
It is also recommended to maintain consistent IGMP versions across the network to avoid compatibility issues. Proper configuration of multicast routers and ensuring periodic IGMP queries are essential for maintaining accurate group membership information.
Network administrators should also monitor multicast traffic patterns regularly to identify any irregularities or inefficiencies. This helps in fine-tuning the network for better performance.
In addition, segmentation of multicast domains using VLANs can help control traffic flow and prevent unnecessary propagation of multicast streams across unrelated network segments.
Real-World Importance of IGMP Snooping in Modern Networks
In today’s digital environments, multicast traffic is increasingly common due to the rise of streaming services, online collaboration tools, and real-time data applications. Without proper control mechanisms, such traffic can quickly overwhelm network infrastructure.
IGMP snooping provides a practical and scalable solution to this challenge by ensuring that multicast data is delivered efficiently and only to intended recipients. This makes it an essential feature in enterprise networks, educational institutions, broadcasting systems, and large-scale data centers.
As network demands continue to grow, the importance of intelligent traffic management mechanisms like IGMP snooping will only increase. It represents a critical step toward maintaining high-performance, scalable, and efficient network environments.
Advanced IGMP Snooping Concepts and Network Behavior
Building on the foundational understanding of IGMP snooping, it is important to explore more advanced concepts that influence how multicast traffic is handled in complex network environments. In larger infrastructures, simple learning of group memberships is not always sufficient. Additional mechanisms such as querier functionality, proxy behavior, and interaction with multicast routing protocols become necessary to ensure stable and efficient multicast delivery.
IGMP snooping does not operate in isolation; it depends heavily on periodic IGMP query messages to maintain accurate group membership information. Without these queries, switches may not reliably determine whether a host is still interested in receiving multicast traffic. This dependency makes the presence of a querier critical in many network designs.
Role of the IGMP Querier in Multicast Stability
The IGMP querier is responsible for sending periodic IGMP query messages into the network to verify active multicast group memberships. In typical network architectures, this role is performed by a multicast router. However, in environments where no multicast router exists, a switch may be configured to act as a querier.
When the querier sends a general query, all hosts that are members of multicast groups respond with membership reports. These responses allow switches to refresh their IGMP snooping tables and maintain accurate forwarding entries. If these reports are not received within a specific interval, the switch assumes that the group membership has expired and removes the associated entries.
Without a functioning querier, multicast traffic may either stop flowing correctly or continue flooding unnecessarily, depending on how the switch handles stale entries. This makes the querier a fundamental component of a well-functioning multicast environment.
IGMP Snooping with Layer 3 Multicast Routing
In more advanced network setups, IGMP snooping works alongside Layer 3 multicast routing protocols such as Protocol Independent Multicast (PIM). While IGMP manages host-to-router communication, PIM is responsible for routing multicast traffic between different network segments.
IGMP snooping ensures that within a single VLAN or broadcast domain, multicast traffic is only forwarded to interested devices. Meanwhile, PIM determines how multicast streams are distributed across different routers and subnets.
This layered approach ensures efficiency at both the local switching level and the broader routing level. Without proper coordination between IGMP snooping and multicast routing, networks can suffer from inefficiencies such as duplicate traffic, routing loops, or incomplete delivery of multicast streams.
IGMP Snooping Proxy Behavior in Modern Switches
Some advanced switches implement IGMP snooping proxy functionality. In this mode, the switch not only listens to IGMP messages but also actively participates in IGMP communication on behalf of connected hosts.
Instead of simply forwarding IGMP reports to the router, the switch aggregates membership information and sends summarized reports upstream. This reduces the number of IGMP messages on the network and improves scalability in environments with a large number of multicast receivers.
IGMP proxy behavior is particularly useful in access layer switches where hundreds of endpoints may be connected. By reducing signaling overhead, the network becomes more efficient and easier to manage.
Multicast Flooding and Unknown Group Handling
Even with IGMP snooping enabled, there are scenarios where multicast traffic may still be flooded across all ports. This typically occurs when the switch receives multicast traffic for a group that is not yet known or has no registered members in its IGMP table.
This behavior is known as unknown multicast flooding. While it ensures that no legitimate traffic is dropped, it can reduce the efficiency gains provided by IGMP snooping. Proper configuration of multicast routers and consistent IGMP participation across devices helps minimize this issue.
Some advanced switches allow administrators to restrict unknown multicast flooding or configure default behaviors to better control traffic distribution.
Common Problems in IGMP Snooping Deployments
Despite its usefulness, IGMP snooping can introduce operational challenges if not configured correctly. One common issue is multicast traffic not reaching intended receivers. This often occurs when IGMP queries are not being generated or when hosts fail to send proper membership reports.
Another frequent problem is excessive multicast flooding. This usually indicates that the switch is not correctly learning group memberships or that the querier function is missing in the network.
Timing issues can also occur. IGMP operates based on timers, and mismatched configurations between routers and switches can lead to premature removal of group entries or delayed updates.
In some cases, network administrators may also encounter asymmetric multicast behavior, where traffic flows correctly in one direction but not the other due to incomplete snooping information.
Security Considerations in IGMP Snooping Networks
While IGMP snooping primarily focuses on efficiency, it also has security implications. Multicast traffic can be exploited if not properly controlled, potentially allowing unauthorized access to sensitive data streams.
IGMP snooping helps mitigate this risk by restricting multicast traffic only to ports that have explicitly joined a group. This prevents unauthorized devices from passively receiving multicast streams.
However, IGMP itself does not provide authentication mechanisms. This means that any device connected to the network can potentially send spoofed IGMP join or leave messages. In sensitive environments, additional security measures such as port security, access control lists, or multicast filtering may be required.
Scalability Challenges in Large-Scale Networks
As networks grow in size and complexity, maintaining efficient multicast distribution becomes increasingly challenging. Large-scale environments may include thousands of multicast groups and devices, making it difficult for switches to maintain accurate and up-to-date IGMP tables.
Memory limitations, processing overhead, and frequent membership changes can all impact performance. To address these challenges, network designers often implement hierarchical multicast architectures, combining IGMP snooping at the access layer with optimized multicast routing at higher layers.
Careful planning of VLAN segmentation and multicast domain boundaries also helps reduce the scope of multicast traffic and improves scalability.
Optimizing Network Performance with IGMP Snooping
To maximize the benefits of IGMP snooping, network administrators must ensure that it is properly integrated into the overall network design. One key aspect is ensuring consistent configuration across all switches in the multicast domain.
It is also important to tune IGMP timers appropriately based on application requirements. Real-time applications such as video streaming may require faster convergence, while less time-sensitive applications can tolerate longer intervals.
Monitoring tools can also play a crucial role in identifying multicast inefficiencies. By analyzing traffic patterns, administrators can detect unnecessary flooding, missing group memberships, or misconfigured devices.
Proper hardware selection is another important factor. Not all switches handle multicast traffic equally well, and enterprise-grade devices typically offer more advanced IGMP snooping features.
Real-World Applications of IGMP Snooping Optimization
IGMP snooping is widely used in environments where efficient multimedia distribution is critical. In corporate networks, it supports internal video conferencing systems and live broadcasts without overwhelming the infrastructure.
In educational institutions, it enables large-scale lecture streaming to multiple classrooms simultaneously. In financial environments, it supports real-time market data feeds that must be delivered with minimal delay.
It is also commonly used in IPTV systems, where television channels are delivered over IP networks to large numbers of subscribers. Without IGMP snooping, such systems would suffer from severe bandwidth inefficiencies and poor scalability.
Future Trends in Multicast and IGMP Technologies
As networking technologies continue to evolve, multicast mechanisms are also adapting to new demands. While IGMP snooping remains a foundational technology, newer approaches are emerging to improve scalability and automation.
IPv6 introduces Multicast Listener Discovery (MLD), which serves a similar role to IGMP but is designed for IPv6 environments. Additionally, software-defined networking (SDN) is enabling more centralized control of multicast traffic, allowing for more intelligent and dynamic distribution strategies.
Despite these advancements, IGMP snooping continues to play a critical role in traditional and hybrid network environments. Its simplicity, efficiency, and compatibility ensure that it remains relevant in modern infrastructure.
Multicast Efficiency and IGMP Snooping
Efficient multicast management is essential for modern network performance, and IGMP snooping provides a powerful mechanism to achieve this efficiency at the switching layer. By intelligently controlling multicast traffic distribution, it reduces unnecessary bandwidth usage, improves device performance, and enhances overall scalability.
When combined with proper IGMP configuration, querier functionality, and multicast routing protocols, IGMP snooping becomes a key component of a well-optimized network architecture. Although it requires careful planning and monitoring, its benefits far outweigh its complexity, making it indispensable in environments where multicast traffic plays a significant role.
Advanced Deployment Strategies for IGMP Snooping in Enterprise Networks
In large enterprise environments, implementing IGMP snooping effectively requires more than simply enabling the feature on network switches. It demands a structured deployment strategy that aligns with the overall network architecture. Multicast traffic patterns vary significantly depending on application types, user density, and infrastructure design, so a one-size-fits-all configuration rarely delivers optimal results.
A well-designed deployment typically begins with identifying multicast sources and receivers. Understanding where multicast traffic originates and where it is consumed allows network engineers to define clear distribution paths. This ensures that IGMP snooping operates within a predictable and controlled environment rather than reacting to uncontrolled traffic flows.
Another key aspect of deployment strategy is ensuring that IGMP snooping is consistently enabled across all Layer 2 devices within the same broadcast domain. Inconsistent configuration can lead to unpredictable flooding behavior, where some switches correctly filter traffic while others broadcast it widely, undermining the entire optimization effort.
Designing Scalable Multicast Architectures
Scalability is one of the most important considerations in multicast network design. As the number of devices and applications grows, multicast traffic can quickly become difficult to manage without a structured architecture. IGMP snooping plays a central role in maintaining scalability at the access layer, but it must be supported by a hierarchical network design.
Typically, modern networks are divided into access, distribution, and core layers. IGMP snooping is primarily implemented at the access layer, where end devices connect to the network. The distribution layer aggregates multicast traffic and applies policy controls, while the core layer ensures high-speed transport between different network segments.
This layered approach ensures that multicast traffic is contained and efficiently forwarded only where needed. Without such segmentation, multicast streams could propagate unnecessarily across the entire network, increasing congestion and reducing performance.
Tuning IGMP Timers for Optimal Performance
IGMP snooping relies heavily on timers to maintain accurate group membership information. These timers determine how long a switch retains multicast group entries without receiving updates from hosts. Proper tuning of these timers is essential for balancing responsiveness and network stability.
If timers are set too short, legitimate multicast traffic may be interrupted due to premature removal of group memberships. On the other hand, if timers are too long, stale entries may persist, leading to inefficient traffic forwarding.
Network administrators must carefully adjust parameters such as query intervals, response times, and group membership aging periods based on application requirements. Real-time applications often require faster convergence, while less time-sensitive services can tolerate longer intervals without impacting user experience.
Troubleshooting IGMP Snooping Issues in Complex Networks
Despite careful planning, IGMP snooping deployments can still encounter operational issues. One of the most common problems is multicast traffic not reaching intended recipients. This often occurs due to missing IGMP queries or improperly configured querier devices.
Another frequent issue is excessive multicast flooding. This usually indicates that switches are not receiving valid IGMP reports or that group memberships are not being properly learned. In such cases, verifying IGMP communication between hosts and the network infrastructure is essential.
Network administrators also need to watch for inconsistent behavior across switches. If some devices correctly filter multicast traffic while others flood it, the issue often lies in configuration mismatches or firmware differences between devices.
Advanced troubleshooting typically involves analyzing IGMP packet flows, reviewing multicast forwarding tables, and monitoring interface-level statistics to identify where breakdowns occur in the communication process.
Handling Multicast Storms and Traffic Spikes
In some cases, networks may experience multicast storms, where excessive multicast traffic overwhelms switches and endpoints. These storms can be caused by misconfigured applications, network loops, or malfunctioning devices that generate high volumes of multicast packets.
IGMP snooping helps mitigate the impact of such storms by limiting traffic distribution to only those ports that have joined specific multicast groups. However, it is not a complete protection mechanism against poorly behaving multicast sources.
To further protect the network, administrators may implement rate limiting, storm control mechanisms, and traffic filtering policies. These additional safeguards ensure that even if multicast traffic becomes excessive, its impact on the network remains controlled.
Integration with IPv6 Multicast and MLD
As networks transition toward IPv6, IGMP is replaced by Multicast Listener Discovery (MLD). While IGMP is used for IPv4 multicast management, MLD performs a similar function in IPv6 environments.
IGMP snooping concepts still apply in IPv6 networks, but switches must support MLD snooping instead. This ensures that IPv6 multicast traffic is handled with the same efficiency as IPv4 multicast traffic.
The transition to IPv6 introduces additional complexity, as networks may need to support both IGMP and MLD simultaneously during migration periods. Proper configuration is essential to ensure consistent multicast behavior across dual-stack environments.
Comparing IGMP Snooping with Other Traffic Optimization Techniques
While IGMP snooping is highly effective for multicast optimization, it is not the only technique available for improving network efficiency. Other methods include traffic segmentation, quality of service (QoS), and application-layer optimizations.
Traffic segmentation using VLANs helps isolate multicast domains, reducing unnecessary propagation of streams across unrelated devices. QoS ensures that multicast traffic receives appropriate priority based on application requirements, preventing delays in time-sensitive data delivery.
Unlike these methods, IGMP snooping operates specifically at the Layer 2 switching level, making it highly efficient for controlling local multicast distribution. When combined with other optimization techniques, it contributes to a comprehensive performance enhancement strategy.
Vendor-Specific Implementations and Differences
Although IGMP snooping is a standardized mechanism, its implementation can vary between network equipment vendors. Different vendors may offer additional features, enhanced scalability options, or proprietary extensions to improve multicast handling.
Some switches provide advanced filtering capabilities, allowing administrators to define explicit rules for multicast traffic distribution. Others may include enhanced monitoring tools for analyzing IGMP behavior in real time.
These differences mean that network engineers must carefully review vendor documentation when designing multicast networks. Relying solely on generic IGMP principles without considering vendor-specific behavior can lead to unexpected results in production environments.
Monitoring and Performance Analysis of Multicast Traffic
Continuous monitoring is essential for maintaining optimal multicast performance. Without proper visibility, it becomes difficult to detect inefficiencies or diagnose issues within IGMP snooping environments.
Key performance indicators include multicast packet rates, group membership counts, and interface-level traffic statistics. Monitoring these metrics helps identify unusual patterns such as sudden spikes in multicast traffic or missing group registrations.
Advanced monitoring tools can also provide visualization of multicast distribution paths, making it easier to understand how traffic flows through the network. This level of insight is particularly valuable in large-scale deployments where manual analysis would be impractical.
High Availability and Redundancy Considerations
In mission-critical environments, multicast services must remain available even in the event of network failures. High availability designs ensure that IGMP snooping continues to function correctly even when switches or links fail.
Redundant queriers are often deployed to prevent multicast disruptions if the primary querier becomes unavailable. In such configurations, backup devices automatically take over querier responsibilities to maintain continuity.
Link redundancy and failover mechanisms also play a role in maintaining multicast stability. When properly configured, these systems ensure that multicast traffic continues to flow smoothly even during network topology changes.
Performance Optimization in High-Density Environments
High-density environments, such as large campuses or data centers, present unique challenges for IGMP snooping. A large number of connected devices increases the complexity of multicast group management and can strain switch resources.
To address these challenges, network designers often implement aggregation strategies that reduce the number of individual multicast entries a switch must maintain. Efficient hardware utilization and optimized firmware are also critical for handling large-scale multicast deployments.
Careful capacity planning ensures that switches are not overwhelmed by excessive IGMP state information, which could otherwise lead to performance degradation.
Future Evolution of Multicast Optimization Technologies
While IGMP snooping remains a cornerstone of multicast optimization, future network technologies are expected to introduce more intelligent and automated approaches. Software-defined networking is already beginning to reshape how multicast traffic is managed by centralizing control and enabling dynamic policy adjustments.
Machine learning and predictive analytics may also play a role in future multicast optimization, allowing networks to anticipate traffic patterns and adjust configurations proactively.
Despite these advancements, the fundamental principles behind IGMP snooping will continue to remain relevant, especially in traditional and hybrid network environments where simplicity and reliability are essential.
Final Perspective on IGMP Snooping and Network Efficiency
IGMP snooping is a critical technology for ensuring efficient multicast delivery in modern networks. By intelligently controlling how multicast traffic is forwarded at the switching layer, it significantly reduces unnecessary bandwidth consumption and improves overall network performance.
When properly implemented and maintained, it integrates seamlessly with broader network architectures, supporting scalability, reliability, and high performance. Although it requires careful configuration and ongoing monitoring, its benefits make it an indispensable component of multicast-enabled environments.
As network demands continue to grow and evolve, IGMP snooping will remain a foundational mechanism for managing multicast traffic efficiently, ensuring that data is delivered precisely where it is needed without unnecessary overhead.
Operational Best Practices for Long-Term IGMP Snooping Efficiency
Sustaining IGMP snooping efficiency over time requires consistent operational discipline rather than one-time configuration. Networks are dynamic, with devices joining and leaving, applications evolving, and traffic patterns shifting continuously. Because of this, multicast behavior must be regularly reviewed and adjusted to remain efficient.
One of the most important practices is periodic verification of IGMP group membership tables across all switches. This helps ensure that multicast entries accurately reflect real device participation. If stale or incorrect entries accumulate, they can lead to inefficient traffic forwarding or unexpected flooding behavior.
Another key practice is maintaining alignment between network design documentation and actual configuration. Over time, changes in infrastructure can introduce inconsistencies that negatively affect multicast performance. Regular audits help ensure that IGMP snooping continues to function as intended within the broader network architecture.
Ensuring Compatibility Across Network Devices
In heterogeneous network environments, devices from different vendors often coexist. While IGMP snooping is based on standardized protocols, subtle implementation differences can lead to compatibility challenges.
Some devices may handle IGMP queries differently, while others may have variations in how they age out multicast group entries. These differences can create inconsistencies in multicast traffic behavior if not properly managed.
To reduce such issues, it is important to standardize IGMP versions across the network wherever possible. Ensuring consistent protocol behavior helps maintain predictable multicast distribution and reduces troubleshooting complexity.
Firmware updates also play a significant role in compatibility. Keeping network devices updated ensures that known issues are resolved and performance improvements are applied consistently across the infrastructure.
Multicast Optimization in Virtualized and Cloud Environments
Modern network environments increasingly rely on virtualization and cloud-based infrastructure. In these environments, multicast traffic behaves differently due to abstraction layers introduced by virtual switches and software-defined networking components.
IGMP snooping must often be implemented not only on physical switches but also within virtual switching environments. This ensures that multicast traffic remains efficiently controlled even inside virtual machine clusters or containerized workloads.
Cloud environments may also introduce additional complexity, as multicast traffic can span multiple physical and virtual boundaries. Proper integration between physical network infrastructure and virtual networking layers is essential for maintaining consistent multicast performance.
Impact of Network Congestion on IGMP Snooping Behavior
Network congestion can significantly affect the behavior of IGMP snooping mechanisms. When a network becomes heavily congested, IGMP control messages may experience delays or packet loss. This can lead to inaccurate group membership information within switches.
If IGMP reports are delayed or dropped, switches may incorrectly assume that devices have left multicast groups, resulting in disrupted traffic delivery. Conversely, delayed leave messages may cause unnecessary continuation of multicast forwarding.
To mitigate these risks, network administrators must ensure adequate bandwidth provisioning and prioritize IGMP control traffic using quality of service policies. This helps maintain reliable multicast group management even under high traffic conditions.
Role of Multicast in Real-Time and Critical Applications
Multicast technology is especially important in applications where real-time data delivery is critical. These include live video broadcasting, financial trading systems, online gaming platforms, and distributed monitoring systems.
In such environments, even minor inefficiencies in multicast delivery can lead to noticeable performance degradation. IGMP snooping helps ensure that multicast streams are delivered only to relevant participants, reducing latency and improving responsiveness.
As application demands increase, the importance of precise multicast control continues to grow. Efficient IGMP snooping configurations directly contribute to the stability and performance of these time-sensitive systems.
Security Reinforcement in Multicast Environments
While IGMP snooping improves efficiency, it must be complemented by strong security practices to prevent misuse. Multicast traffic can potentially be exploited if unauthorized devices are allowed to join sensitive groups.
One important security measure is restricting which ports are allowed to send IGMP join messages. This prevents unauthorized devices from subscribing to multicast streams they should not access.
Network segmentation also plays a key role in enhancing security. By isolating multicast domains, organizations can ensure that sensitive data streams are only accessible within controlled network segments.
Monitoring for abnormal IGMP activity is also essential. Sudden spikes in group membership changes or unexpected multicast traffic patterns may indicate misconfiguration or malicious behavior.
Long-Term Scalability Considerations
As networks continue to expand, scalability becomes a central concern in multicast design. IGMP snooping must be able to handle increasing numbers of groups, devices, and traffic flows without degrading performance.
Efficient memory utilization within switches is critical, as multicast group tables can grow significantly in large environments. Proper tuning of aging timers and group limits helps prevent resource exhaustion.
Hierarchical network design also supports scalability by distributing multicast processing across multiple layers. This prevents any single switch from becoming a bottleneck for multicast traffic management.
Troubleshooting Methodology for Persistent Issues
When multicast issues persist over time, a structured troubleshooting approach is necessary. The first step involves verifying basic IGMP communication between hosts and switches. Without proper IGMP exchanges, snooping cannot function correctly.
The next step is to examine multicast forwarding tables to ensure that group memberships are being learned and updated correctly. Any inconsistencies in these tables often point to configuration or communication issues.
Network-wide analysis may also be required to identify topology-related problems. Misconfigured trunks, VLAN mismatches, or missing querier functionality are common root causes of multicast disruptions.
By following a systematic approach, administrators can isolate and resolve issues more efficiently.
Future Outlook of IGMP Snooping in Modern Networking
As networking technologies evolve, IGMP snooping will continue to play an important role, even as new paradigms emerge. Software-defined networking, automation, and intent-based networking are transforming how multicast traffic is managed.
Future systems are expected to provide more intelligent multicast control, with dynamic adjustments based on real-time network conditions. However, the core principles of IGMP snooping—efficient group membership tracking and selective traffic forwarding—will remain relevant.
IPv6 multicast technologies and enhanced control protocols will further extend these capabilities, ensuring that multicast remains a viable solution for large-scale data distribution.
Conclusion
IGMP snooping is a foundational technology for achieving efficient multicast traffic management in modern networks. By intelligently controlling how multicast packets are forwarded at the switching level, it eliminates unnecessary flooding and ensures that data is delivered only to intended recipients.
When combined with proper network design, consistent configuration, and complementary technologies such as multicast routing and quality of service, IGMP snooping significantly enhances network performance, scalability, and stability.
Its importance becomes even more evident in environments that rely heavily on real-time data distribution, where efficiency and reliability are critical. Although it requires careful planning and ongoing management, the benefits it provides far outweigh its complexity.
In conclusion, IGMP snooping is not just a technical feature but a key enabler of modern network efficiency. It ensures that multicast communication remains scalable, controlled, and optimized, supporting the growing demands of today’s data-driven applications and preparing networks for future advancements in communication technology.