Networking is built on structured communication between devices, and one of the essential components that make this communication efficient is addressing. Within this structure, wildcard masks play a crucial role in identifying ranges of IP addresses for configuration, filtering, and routing decisions. A wildcard mask is a sequence of numbers used alongside IP addresses to determine which parts of the address should be considered for matching and which parts should be ignored. Unlike subnet masks, which define network boundaries, wildcard masks provide flexibility in specifying multiple addresses with a single rule. This makes them highly useful in access control lists, routing protocols, and network configuration tasks where precision and scalability are required.
Wildcard masks are especially important in environments where administrators need to apply rules to multiple devices without manually listing every single IP address. By using a wildcard mask, a network engineer can define patterns that match entire ranges of addresses efficiently. This reduces configuration complexity and improves the manageability of large networks. Understanding how wildcard masks function is essential for anyone working in networking because they are widely used in enterprise systems, especially in devices such as routers and switches.
Difference Between Subnet Masks and Wildcard Masks
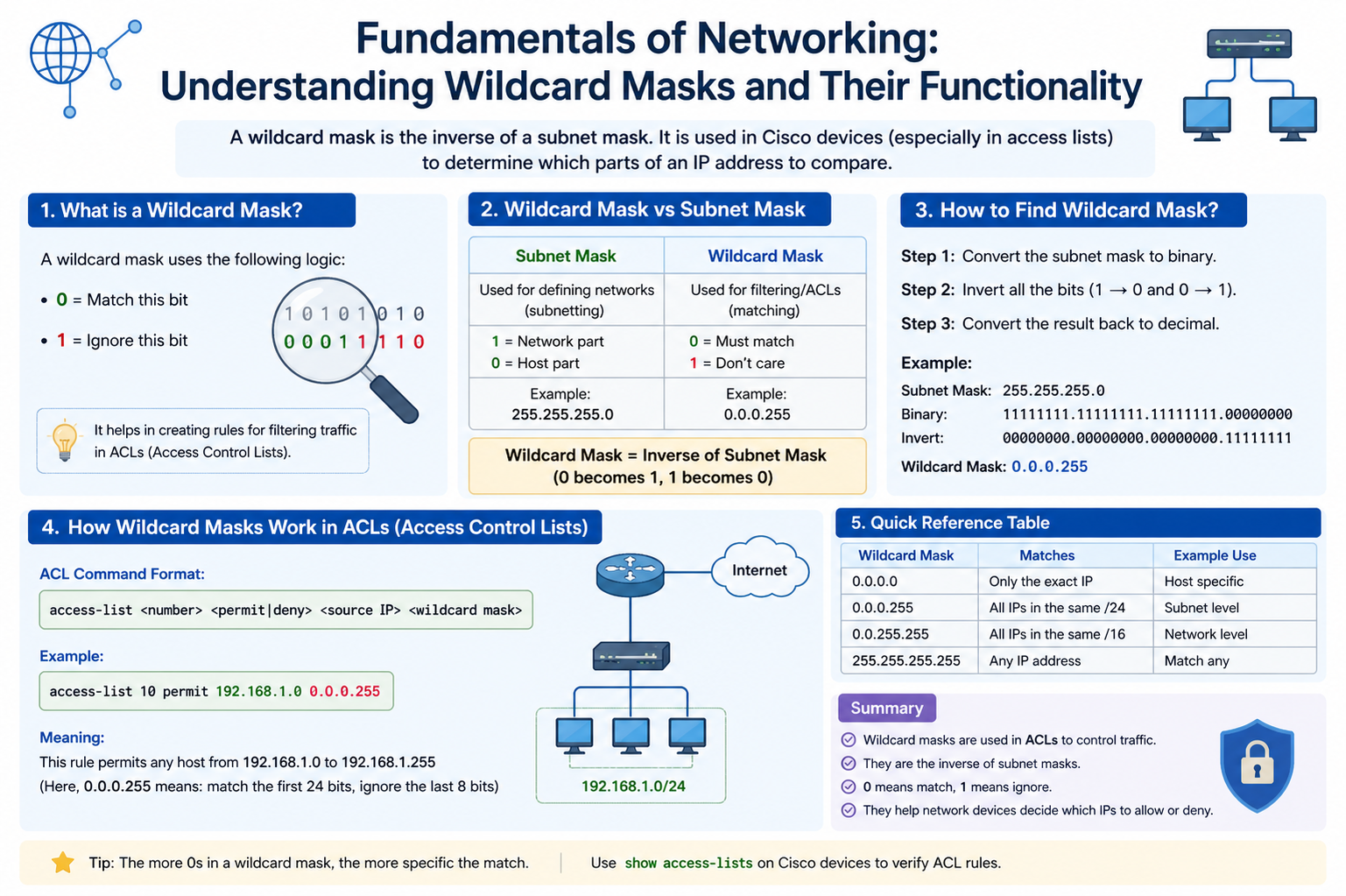
Although wildcard masks and subnet masks appear similar, they serve very different purposes. A subnet mask is used to divide an IP network into smaller networks, helping define network and host portions of an address. It follows a strict binary structure where 1 represents the network portion and 0 represents the host portion. Wildcard masks, on the other hand, work in the opposite manner. They are used to identify which bits of an IP address should be ignored during comparison.
In wildcard masks, the value 0 means the bit must match exactly, while the value 1 means the bit can be ignored. This inverted logic makes wildcard masks highly flexible. For example, a subnet mask of 255.255.255.0 corresponds to a wildcard mask of 0.0.0.255. This means the first three octets must match exactly, while the last octet can vary from 0 to 255. This relationship is critical for understanding how network rules are applied in real-world configurations.
Subnet masks are restrictive by design, while wildcard masks are permissive. This difference allows wildcard masks to be used in scenarios where broader or more flexible matching is required.
Binary Logic Behind Wildcard Masks
To fully understand wildcard masks, it is important to explore their binary behavior. Every IP address is composed of 32 bits, divided into four octets. Wildcard masks operate at the binary level by comparing each bit of the IP address with the corresponding bit in the mask.
When a wildcard mask bit is set to 0, the corresponding IP address bit must match exactly. When it is set to 1, that bit is ignored in the comparison process. This allows for pattern-based matching rather than strict address matching. For instance, a wildcard mask of 0.0.0.255 in binary allows all variations in the last octet while keeping the first three octets fixed.
This binary flexibility is what makes wildcard masks powerful in large-scale networking environments. Instead of writing multiple rules for each individual IP address, a single rule can cover a wide range of addresses by using binary patterns effectively.
Role of Wildcard Masks in Access Control Lists
One of the most common uses of wildcard masks is in Access Control Lists. Access Control Lists are used to permit or deny traffic based on IP addresses. In such configurations, wildcard masks define which addresses the rule applies to.
For example, if a network administrator wants to allow access from a range of IP addresses within a subnet, a wildcard mask can be used to define that entire range. This eliminates the need to create individual rules for each device. Similarly, if certain IP addresses need to be blocked, wildcard masks can help define exclusion patterns efficiently.
Access Control Lists rely heavily on precision, and wildcard masks provide the flexibility needed to achieve that precision without increasing configuration complexity. They allow administrators to control traffic flow with minimal rules while still maintaining detailed control over network security.
Wildcard Masks in Routing Protocols
Routing protocols also make extensive use of wildcard masks, particularly in protocols like OSPF. In such cases, wildcard masks help define which interfaces or networks should participate in routing updates.
Instead of specifying each network individually, wildcard masks allow grouping of multiple networks under a single configuration statement. This simplifies routing configuration and reduces the chances of errors. For example, a router can be configured to include all networks within a certain range using a single wildcard mask expression.
This capability is especially useful in large enterprise networks where hundreds or thousands of subnets may exist. Wildcard masks help streamline routing configuration and ensure that updates are efficiently propagated across the correct network segments.
Calculating Wildcard Masks from Subnet Masks
Understanding how to convert subnet masks into wildcard masks is a fundamental skill in networking. The process is straightforward: subtract each octet of the subnet mask from 255.
For example, if the subnet mask is 255.255.255.0, the wildcard mask becomes 0.0.0.255. If the subnet mask is 255.255.0.0, the wildcard mask becomes 0.0.255.255. This simple subtraction method allows quick conversion between the two formats.
This calculation is essential when configuring network devices because most routing and access control configurations require wildcard masks rather than subnet masks. Being able to quickly derive the correct wildcard mask ensures accurate network configuration and reduces the likelihood of errors.
Practical Use Cases of Wildcard Masks
Wildcard masks are widely used in real-world networking scenarios. One of the most common applications is in defining IP ranges for security policies. Network administrators use wildcard masks to specify which devices are allowed to communicate with certain servers or services.
Another important use case is in grouping networks for routing updates. Instead of configuring each network individually, wildcard masks allow multiple networks to be included in a single statement. This is particularly useful in dynamic environments where networks frequently change or expand.
Wildcard masks are also used in filtering traffic in large-scale enterprise systems. By defining flexible patterns, administrators can efficiently manage network traffic and ensure that only authorized devices are able to access specific resources.
Wildcard Mask Matching Behavior
The matching behavior of wildcard masks is based on comparison logic. When a packet is evaluated against a wildcard mask, each bit of the IP address is compared with the corresponding mask bit. If the mask bit is 0, an exact match is required. If the mask bit is 1, the bit is ignored.
This behavior allows wildcard masks to define both specific and broad matching conditions. For example, a wildcard mask can be used to match a single IP address by setting all bits to 0, or it can be used to match an entire network by setting multiple bits to 1.
This flexibility is what makes wildcard masks so powerful in networking configurations. They provide a balance between precision and scalability, allowing administrators to design efficient network policies.
Importance of Wildcard Masks in Network Design
Wildcard masks play a significant role in designing scalable and efficient networks. They reduce configuration complexity by allowing multiple IP addresses to be grouped under a single rule. This not only saves time but also reduces the chances of configuration errors.
In large enterprise environments, where thousands of devices may exist, wildcard masks help simplify network management. They enable administrators to implement consistent policies across multiple network segments without manually configuring each device.
This efficiency is especially important in dynamic environments where networks are frequently expanded or modified. Wildcard masks provide the flexibility needed to adapt to these changes quickly and effectively.
Common Mistakes When Using Wildcard Masks
Despite their usefulness, wildcard masks are often misunderstood. One common mistake is confusing them with subnet masks, which can lead to incorrect configurations. Another mistake is miscalculating the wildcard mask, resulting in unintended network behavior.
Incorrect wildcard masks can either allow too much traffic or block legitimate traffic, depending on the configuration. This is why careful calculation and understanding of binary logic are essential when working with wildcard masks.
Another issue arises when administrators use overly broad wildcard masks, which can expose networks to unnecessary risks. Proper planning and validation are essential to ensure that wildcard masks are used effectively and securely.
Wildcard Mask Functionality
Wildcard masks are a fundamental component of modern networking, providing flexibility and efficiency in IP address matching. Their ability to define both precise and broad address ranges makes them invaluable in access control, routing, and network design. By understanding their binary logic, relationship with subnet masks, and practical applications, network professionals can effectively manage complex network environments.
Mastering wildcard masks is essential for anyone involved in network administration or engineering, as they form the backbone of many configuration tasks in enterprise systems.
How Wildcard Masks Interact with IP Addressing Schemes
Wildcard masks are deeply connected to how IP addressing schemes are structured and interpreted within networks. Every IP address belongs to a logical grouping that defines its network behavior, and wildcard masks provide the flexibility to work across these groupings without strict boundaries. Instead of limiting communication to fixed subnet divisions, wildcard masks allow pattern-based matching, which makes them highly effective in dynamic or large-scale environments.
When a network device evaluates an IP address against a wildcard mask, it does not simply check for membership in a subnet. Instead, it evaluates each bit position individually based on whether the wildcard mask requires a match or allows flexibility. This means that wildcard masks can represent both very narrow and very broad address selections depending on how they are constructed. This adaptability is one of the reasons they are widely used in routing and filtering configurations.
Wildcard Masks and Their Role in Network Efficiency
Network efficiency depends heavily on reducing unnecessary processing and simplifying configuration logic. Wildcard masks contribute directly to this efficiency by reducing the number of individual rules required to manage traffic. Instead of defining multiple entries for different IP addresses, a single wildcard mask rule can cover an entire range of devices.
This reduction in configuration size not only makes systems easier to manage but also improves processing speed in network devices. Routers and switches can evaluate fewer rules, which reduces lookup time and improves overall performance. In large enterprise environments where thousands of rules may exist, wildcard masks significantly reduce administrative overhead.
Efficiency also extends to troubleshooting. When wildcard masks are used correctly, network administrators can quickly identify which range of devices is affected by a rule, making it easier to diagnose connectivity issues or security misconfigurations.
Understanding Inverse Matching Logic in Wildcard Masks
One of the most important concepts in wildcard mask functionality is inverse matching logic. Unlike subnet masks, where binary 1 represents a fixed network portion and 0 represents a host portion, wildcard masks reverse this logic. A 0 indicates that the corresponding bit must match exactly, while a 1 indicates that the bit can be ignored.
This inverse behavior allows wildcard masks to function as flexible pattern-matching tools. For example, if a wildcard mask is designed to ignore the last octet of an IP address, it can match all 256 possible values in that range. This makes it possible to define broad network segments without explicitly listing every address.
Inverse logic is especially useful in scenarios where network patterns are more important than strict boundaries. It enables administrators to focus on logical groupings of devices rather than rigid subnet structures.
Wildcard Masks in Hierarchical Network Design
Modern networks are often designed in hierarchical structures, consisting of core, distribution, and access layers. Wildcard masks play an important role in maintaining this hierarchy by allowing selective control over communication between different layers.
At the core layer, wildcard masks are often used to define broad routing policies that apply to multiple subnets. At the distribution layer, they help refine traffic flow between different departments or segments. At the access layer, they are used to enforce security rules for individual devices or small groups of devices.
This layered usage ensures that network policies remain consistent while still allowing flexibility where needed. Wildcard masks help maintain balance between control and scalability in complex network architectures.
Wildcard Masks in Dynamic Routing Environments
Dynamic routing protocols rely heavily on wildcard masks to determine which networks should participate in routing updates. In protocols such as OSPF, wildcard masks are used to identify interface ranges that should be included in a routing process.
Instead of manually specifying each network, administrators can define a single wildcard mask that covers multiple interfaces. This simplifies routing configuration and ensures that new networks added within the defined range are automatically included in routing updates.
This dynamic behavior is especially valuable in environments where networks frequently change. Wildcard masks allow routing configurations to adapt without requiring constant manual updates.
Bit-Level Flexibility and Pattern Recognition
Wildcard masks operate at a very granular level, working directly with binary representations of IP addresses. This allows them to perform pattern recognition rather than simple equality checks. Each bit in the IP address is evaluated independently, creating a highly flexible matching system.
This bit-level control allows wildcard masks to represent complex patterns such as alternating address ranges, partial subnet matches, or segmented network groups. This flexibility is not possible with traditional subnet masks, which are strictly hierarchical.
Because of this capability, wildcard masks are often used in advanced network configurations where precision and adaptability are both required.
Security Applications of Wildcard Masks
Wildcard masks are widely used in network security to control access to resources. In access control systems, they define which IP addresses are allowed or denied communication with specific services.
By carefully designing wildcard masks, administrators can enforce strict security boundaries without creating overly complex rule sets. For example, a wildcard mask can be used to allow access to an entire department while blocking external networks.
This makes wildcard masks an essential tool in firewall configuration and network security policy design. They allow security rules to be both broad and precise at the same time, depending on the requirement.
Optimization of Large Network Configurations
In large-scale networks, configuration optimization is critical to maintaining stability and performance. Wildcard masks contribute to this optimization by reducing redundancy in configuration files. Instead of repeating similar rules for different IP addresses, a single wildcard mask can cover all required addresses.
This reduces configuration size and makes it easier to update network policies. When changes are required, administrators only need to modify a single wildcard mask rather than multiple individual entries. This significantly reduces the risk of configuration errors.
Optimization also improves readability, making it easier for network engineers to understand and manage complex systems.
Common Misinterpretations in Advanced Usage
Even experienced network engineers can misinterpret wildcard masks, especially in complex configurations. One common issue is assuming that wildcard masks behave the same as subnet masks in all scenarios. This misunderstanding can lead to incorrect rule definitions.
Another frequent mistake is miscalculating wildcard ranges when dealing with non-standard subnet sizes. This can result in unintended access permissions or routing behavior.
In advanced environments, even small errors in wildcard mask configuration can have significant impacts, making careful design and testing essential.
Wildcard Masks in Scalable Network Architectures
Scalability is a key requirement in modern networking, and wildcard masks support this by allowing flexible expansion of network rules. As new devices or subnets are added, wildcard masks can automatically include them if they fall within the defined pattern.
This eliminates the need for constant reconfiguration and ensures that network policies remain consistent as the infrastructure grows. In cloud-based and virtualized environments, this scalability becomes even more important due to the dynamic nature of resource allocation.
Wildcard masks therefore act as a foundation for scalable network design, supporting both growth and adaptability.
Real-World Importance of Wildcard Mask Mastery
Understanding wildcard masks is essential for anyone working in professional networking environments. They are not just theoretical concepts but practical tools used daily in enterprise systems. From routing protocols to security policies, wildcard masks influence how networks operate at a fundamental level.
Mastery of wildcard masks allows network professionals to design more efficient, secure, and scalable systems. It also improves troubleshooting capabilities, as understanding mask logic helps identify configuration issues more quickly.
In modern IT infrastructure, where networks are becoming increasingly complex, wildcard masks remain a core skill for effective network management.
Configuring Wildcard Masks in Network Devices
In real-world networking environments, wildcard masks are primarily configured on routers and switches to define rules for traffic handling and routing behavior. The configuration process usually involves associating an IP address with a wildcard mask inside a command structure that determines how broadly or narrowly a rule should apply.
When configuring wildcard masks, the administrator must carefully define both the base IP address and the range of addresses that should be included. The base address acts as a reference point, while the wildcard mask determines which portions of that address can vary. This combination allows precise control over network traffic patterns without needing to specify every individual host.
Correct configuration is critical because even a small error in the wildcard mask can lead to unintended network exposure or blocked communication. For this reason, network engineers often validate configurations in test environments before applying them to production systems.
Wildcard Masks in Enterprise Routing Strategies
In enterprise-level networks, routing strategies depend heavily on efficient network summarization and grouping. Wildcard masks play a key role in defining which networks should participate in routing updates and how routing information is distributed across different segments of the network.
By using wildcard masks, network engineers can group multiple subnets under a single routing statement. This reduces the complexity of routing tables and ensures that routing protocols operate more efficiently. Instead of processing numerous individual routes, routers can handle aggregated entries defined through wildcard patterns.
This approach is especially useful in large organizations where multiple departments or locations are interconnected. Wildcard masks allow routing policies to remain simple while still covering complex network topologies.
Wildcard Masks in Access Control Design
Access control design relies heavily on defining which devices or users are permitted to interact with network resources. Wildcard masks simplify this process by enabling flexible IP range definitions within security rules.
Instead of listing every allowed or denied IP address, administrators can use wildcard masks to define entire groups of addresses. This is particularly useful in environments where user devices frequently change or where large numbers of endpoints need to be managed consistently.
Security policies built using wildcard masks are easier to maintain and scale. When organizational changes occur, such as adding a new department or expanding infrastructure, wildcard-based rules can often accommodate these changes without requiring major reconfiguration.
Behavior of Wildcard Masks in Complex Network Scenarios
In more advanced networking scenarios, wildcard masks can behave in highly flexible and sometimes non-intuitive ways. They are capable of matching non-contiguous address ranges depending on how the binary pattern is structured.
This allows network engineers to design highly specific matching rules that cannot be achieved using traditional subnetting alone. For example, wildcard masks can be configured to match alternating patterns or selectively include certain ranges within a larger block of addresses.
This level of control is particularly useful in environments where traffic segmentation must be extremely precise, such as financial systems, government networks, or large-scale cloud infrastructures.
Performance Considerations of Wildcard Mask Usage
Although wildcard masks improve configuration efficiency, they also play a role in network performance. Efficient wildcard design can reduce processing overhead on network devices by minimizing the number of rules that must be evaluated for each packet.
When wildcard masks are properly structured, routers and switches can quickly determine whether a packet matches a rule without scanning extensive lists of individual entries. This improves packet forwarding speed and reduces latency in high-traffic environments.
However, poorly designed wildcard masks can have the opposite effect. Overly broad or poorly optimized rules may force devices to perform unnecessary evaluations, which can slow down processing and reduce overall network performance.
Wildcard Masks in Network Segmentation Strategies
Network segmentation is a key design principle used to improve security and performance. Wildcard masks support segmentation by allowing administrators to define logical groupings of devices across different parts of the network.
Instead of physically separating networks into many isolated segments, wildcard masks allow logical segmentation through rule-based grouping. This enables more flexible designs where devices can be grouped based on function rather than physical location.
For example, all devices in a specific department or application group can be managed using a single wildcard-based rule, even if they are spread across multiple subnets. This approach simplifies management while maintaining strong segmentation principles.
Troubleshooting Issues Related to Wildcard Masks
Troubleshooting network problems involving wildcard masks requires a strong understanding of how they interpret IP addresses at the binary level. One of the most common issues is incorrect matching behavior caused by misconfigured wildcard values.
When a wildcard mask is too broad, it may unintentionally include devices that should not be part of a rule. Conversely, if it is too narrow, legitimate traffic may be excluded. Both scenarios can lead to connectivity issues or security gaps.
To troubleshoot these issues, network engineers often break down both the IP address and wildcard mask into binary form to verify each bit’s behavior. This method helps identify mismatches and correct configuration errors more effectively.
Wildcard Masks in Modern Cloud and Virtual Networks
In modern cloud and virtualized environments, wildcard masks continue to play an important role in network configuration and policy management. Cloud networks are highly dynamic, with resources being created and destroyed frequently. Wildcard masks help manage this complexity by allowing flexible rule definitions that automatically adapt to changing infrastructure.
In virtual networks, wildcard masks are often used to define security groups, routing policies, and communication rules between virtual machines. Their flexibility makes them ideal for environments where IP addresses may not remain static for long periods.
This adaptability ensures that wildcard masks remain relevant even as networking technology evolves toward more virtualized and software-defined models.
Relationship Between Wildcard Masks and Automation
Network automation has become a major trend in modern IT infrastructure, and wildcard masks integrate well into automated systems. Automation tools often use wildcard-based logic to apply configurations across multiple devices simultaneously.
By defining wildcard patterns, administrators can automate the deployment of security rules, routing policies, and access controls across large networks. This reduces manual effort and ensures consistency in configuration.
Automation combined with wildcard masks also reduces the likelihood of human error, making networks more reliable and easier to manage at scale.
Importance of Precision in Wildcard Mask Design
Precision is one of the most important factors when working with wildcard masks. Because they define how IP addresses are matched, even small mistakes can have significant consequences.
A well-designed wildcard mask ensures that only intended devices are included in a rule, while all others are excluded. This precision is essential for maintaining both security and performance in a network environment.
Network engineers must carefully analyze addressing schemes and intended traffic flows before implementing wildcard-based rules. Proper planning ensures that wildcard masks function exactly as intended.
Long-Term Value of Understanding Wildcard Masks
Understanding wildcard masks provides long-term value for anyone working in networking or IT infrastructure. They are not limited to basic configurations but extend into advanced routing, security design, and automation systems.
As networks continue to grow in size and complexity, the ability to efficiently manage IP address ranges becomes increasingly important. Wildcard masks provide a powerful and flexible solution to this challenge.
Professionals who master wildcard mask concepts gain a deeper understanding of how networks function at a structural level, enabling them to design more efficient, secure, and scalable systems over time.
Wildcard Masks in Large-Scale Service Provider Networks
In service provider environments, networks are extremely large and often span multiple regions, customers, and technologies. Wildcard masks become essential tools for managing this complexity because they allow engineers to define broad but controlled matching rules across massive infrastructures.
Instead of configuring individual entries for thousands of subnets, service providers use wildcard masks to group networks based on hierarchy, customer allocation, or geographic distribution. This approach ensures that routing policies and access rules remain manageable even as the network scales to enormous sizes.
In such environments, wildcard masks also help maintain consistency across distributed systems. A single well-designed mask can represent entire customer blocks or backbone segments, reducing the risk of configuration drift across multiple devices.
Wildcard Masks and Policy-Based Networking
Modern networks increasingly rely on policy-based management rather than static configurations. Wildcard masks support this shift by enabling dynamic and flexible rule definitions. Policies can be applied to groups of IP addresses rather than individual endpoints, allowing for more adaptive network behavior.
This is especially important in environments where users and devices frequently change locations or IP assignments. Wildcard masks allow policies to remain stable even when the underlying network structure changes.
For example, access policies for a department can remain unchanged even if that department’s devices are moved to a different subnet, as long as the wildcard mask still matches the correct address range.
Wildcard Masks in Multi-Tenant Architectures
Multi-tenant systems, such as cloud platforms and data centers, rely heavily on isolation and controlled communication between tenants. Wildcard masks help define boundaries between different tenant environments while still allowing controlled interactions when necessary.
Each tenant can be assigned a specific IP range, and wildcard masks can be used to enforce policies that apply only within or across those ranges. This ensures that tenants remain logically separated while still allowing shared infrastructure to function efficiently.
This model is critical in cloud computing, where thousands of virtual networks must coexist securely and efficiently on shared physical infrastructure.
Design Patterns for Effective Wildcard Mask Usage
Effective use of wildcard masks requires structured design thinking rather than ad hoc configuration. One common design pattern is hierarchical grouping, where wildcard masks are used at different levels of the network to represent increasing levels of abstraction.
At lower levels, wildcard masks may represent small device groups or subnets. At higher levels, they may represent entire departments, regions, or organizational units. This layered approach ensures that network policies remain both flexible and scalable.
Another important design pattern is range-based grouping, where wildcard masks are carefully structured to align with IP addressing schemes. This reduces complexity and ensures predictable behavior across the network.
Wildcard Masks and Network Evolution
As networks evolve, wildcard masks help ensure continuity between legacy systems and modern architectures. Older systems that rely on static IP configurations can still be integrated into newer, more dynamic environments using carefully designed wildcard rules.
This makes wildcard masks an important bridge technology in network modernization efforts. They allow organizations to gradually transition toward more automated and cloud-based infrastructures without disrupting existing services.
Their adaptability ensures that they remain relevant even as networking technologies shift toward software-defined networking and virtualization.
Common Pitfalls in Advanced Wildcard Mask Usage
In advanced network environments, wildcard mask misconfigurations can have widespread consequences. One common pitfall is over-generalization, where a wildcard mask is too broad and unintentionally includes devices that should not be part of a rule.
Another issue is inconsistent design across different parts of the network. If wildcard masks are not standardized, it can lead to confusion, overlapping rules, and unpredictable behavior.
Lack of documentation is also a major problem. Without clear documentation of wildcard mask usage, troubleshooting becomes significantly more difficult, especially in large teams or distributed environments.
Best Practices for Wildcard Mask Implementation
To ensure reliable network performance, several best practices should be followed when implementing wildcard masks. First, always define clear IP addressing schemes before designing wildcard rules. This ensures that masks align logically with network structure.
Second, keep wildcard masks as specific as possible while still meeting functional requirements. Overly broad masks should be avoided unless absolutely necessary.
Third, maintain consistent documentation for all wildcard-based configurations. This helps ensure that future changes can be made safely and efficiently.
Finally, test wildcard configurations in controlled environments before deploying them into production networks. This reduces the risk of unexpected behavior.
The Strategic Role of Wildcard Masks in Networking
Wildcard masks are not just technical tools; they are strategic components of network design. They influence how networks scale, how policies are enforced, and how systems adapt to change.
Their ability to simplify complex configurations while maintaining precision makes them essential in modern networking. Whether used in security, routing, or automation, wildcard masks provide a foundation for efficient network control.
Understanding their strategic value allows network engineers to design systems that are not only functional but also adaptable to future growth and technological change.
Mastering Wildcard Masks in Modern Networking
Wildcard masks are a fundamental concept in networking that extend far beyond simple IP matching. They provide a powerful mechanism for defining flexible, scalable, and efficient network rules across a wide range of applications. From access control and routing protocols to cloud computing and automation, wildcard masks play a critical role in shaping how modern networks operate.
Their inverse logic, binary-level operation, and pattern-based matching capabilities make them uniquely suited for complex networking environments. When used correctly, they reduce configuration complexity, improve performance, and enhance scalability. When misunderstood or misconfigured, however, they can lead to significant operational challenges.
Mastering wildcard masks requires both technical understanding and design thinking. Engineers must be able to interpret IP structures, convert subnet masks accurately, and design rules that align with organizational needs. As networks continue to grow in size and complexity, the importance of wildcard masks will only increase.
Ultimately, wildcard masks represent a bridge between rigid network structures and flexible, modern network design. They enable administrators to move beyond fixed addressing constraints and adopt more intelligent, adaptive approaches to network management.
Conclusion:
Wildcard masks are a powerful and flexible mechanism in networking that enable efficient IP address matching, simplified configuration, and scalable network design. They extend beyond simple address filtering by allowing administrators to define patterns instead of individual entries, which greatly reduces complexity in both small and large networks. Their inverse logic compared to subnet masks makes them unique, giving network engineers precise control over which parts of an IP address must match and which can vary.
Across routing protocols, access control lists, security policies, and cloud-based infrastructures, wildcard masks remain an essential tool for managing modern networks. They improve efficiency by reducing redundant configuration, enhance scalability by supporting large address ranges, and strengthen network design by enabling structured grouping of devices and subnets. However, their effectiveness depends heavily on correct calculation and careful planning, as small mistakes can lead to misconfigured access or routing behavior.
In conclusion, mastering wildcard masks is a fundamental skill for anyone working in networking. They bridge the gap between rigid subnet structures and dynamic network requirements, making them indispensable in today’s evolving IT environments.