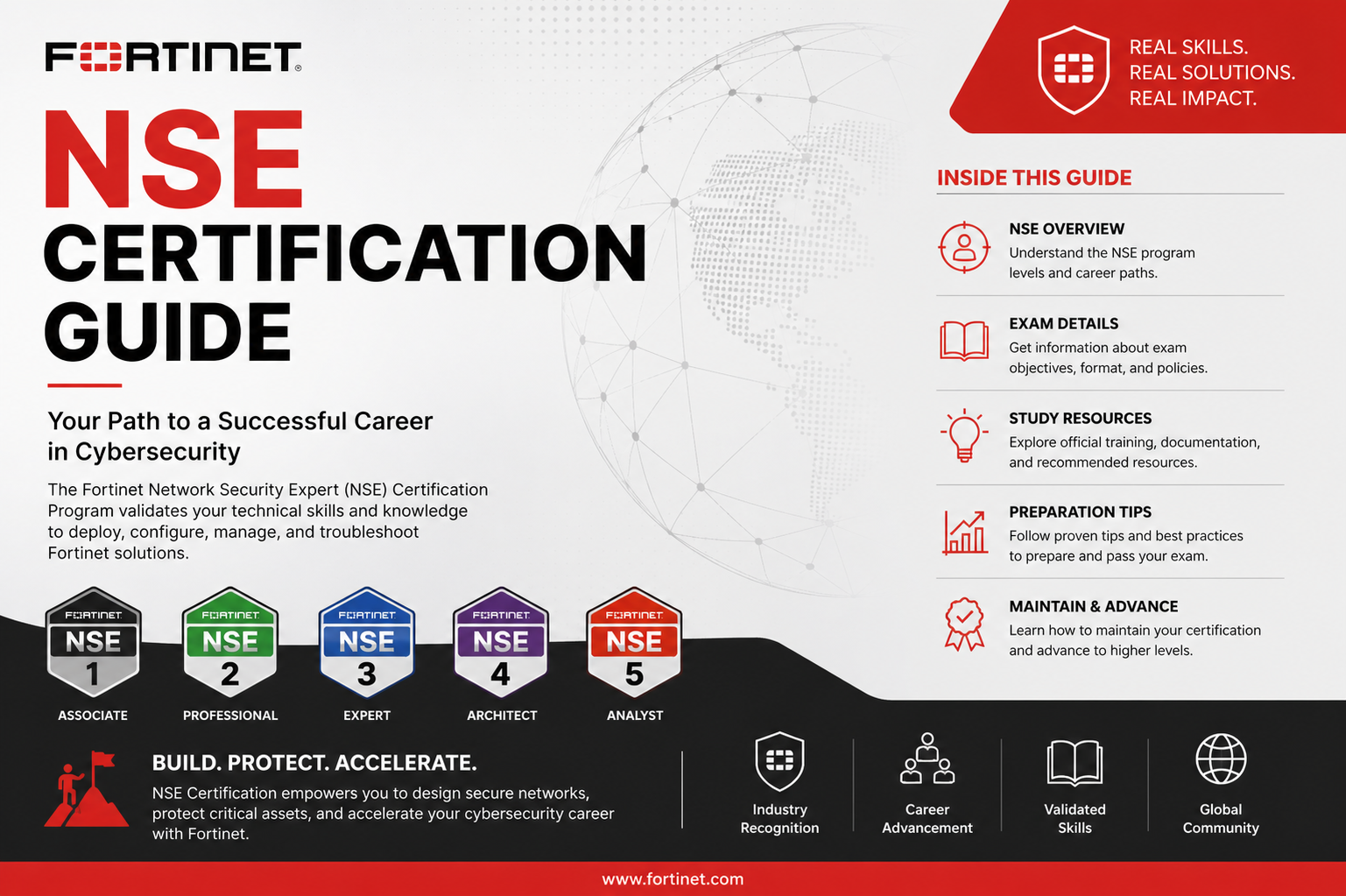
The Fortinet NSE certification program is a structured learning and validation framework designed to build cybersecurity expertise progressively. It focuses on developing both theoretical understanding and practical skills required to secure modern digital environments. The program is widely recognized in the cybersecurity industry because it aligns closely with real-world security operations, enterprise network defense, and threat management practices. The certification path is designed to guide learners from basic cybersecurity awareness to advanced network security engineering and architecture, ensuring continuous skill development at every stage.
The program emphasizes applied knowledge rather than only theoretical concepts. This means learners are expected to understand how security technologies function in live environments, how threats evolve, and how enterprise networks are protected using integrated security systems. The certification also reflects current cybersecurity demands, including cloud security, zero trust principles, and advanced threat protection strategies.
Foundational Cybersecurity Understanding
At the beginning of the certification journey, learners are introduced to fundamental cybersecurity concepts. This stage focuses on building awareness of how digital threats operate and how organizations defend against them. It covers basic principles such as confidentiality, integrity, and availability, which form the core foundation of information security.
Learners develop an understanding of common cyber threats including malware, phishing attacks, ransomware, denial-of-service attacks, and insider threats. This stage also introduces the basics of network communication, including how data flows across systems and how vulnerabilities can be exploited if proper protections are not in place.
The foundational stage is important because it shapes how candidates think about security problems. Instead of focusing only on tools or configurations, learners begin to understand the logic behind security decisions. This mindset is essential for progressing into more advanced technical roles within the cybersecurity field.
Introduction to Fortinet Security Ecosystem
A key component of the certification path is understanding the Fortinet security ecosystem. This includes learning how different Fortinet products work together to provide integrated security across networks, endpoints, applications, and cloud environments.
At this stage, learners are introduced to core security appliances such as next-generation firewalls, secure web gateways, and intrusion prevention systems. The focus is on understanding how these technologies interact to provide layered protection. The concept of security fabric is also introduced, which represents the idea of integrating multiple security tools into a unified system that can detect, prevent, and respond to threats in real time.
This integrated approach is important because modern cyber threats often bypass isolated security tools. By understanding how security components work together, candidates develop a more holistic view of enterprise security architecture.
Basic Network Security Concepts
As learners progress, they begin to study fundamental network security principles in greater detail. This includes understanding IP addressing, subnetting, routing basics, and network segmentation. These concepts are essential because most cybersecurity controls operate at the network level.
Firewall concepts are introduced in depth, including packet filtering, stateful inspection, and application control. Learners also study how policies are created to control traffic flow between different network zones. This helps build practical skills in managing access control and securing internal and external communication channels.
Another important concept at this stage is secure remote access. Learners explore how virtual private networks function and how encrypted tunnels are created to protect data transmission over public networks. This understanding is critical in modern environments where remote work and cloud access are common.
Security Threat Analysis and Prevention
A major focus of the certification path is understanding how to identify and prevent security threats. This includes studying attack vectors and the techniques used by cybercriminals to exploit systems.
Learners explore how malware spreads through networks, how phishing campaigns target users, and how attackers exploit vulnerabilities in software and configurations. This knowledge helps build the ability to recognize suspicious activity and respond effectively.
Threat prevention techniques are also introduced, including intrusion prevention systems, antivirus scanning, and web filtering. These tools are studied not only in terms of functionality but also in terms of deployment strategy and configuration.
The goal at this stage is to develop a proactive security mindset. Instead of reacting to attacks after they occur, learners are trained to anticipate threats and implement preventive measures.
Security Policies and Access Control Fundamentals
Another important area of study is access control and policy management. Security policies define how traffic is allowed or blocked within a network environment. Learners study how to create rules that control user access, application usage, and data movement.
This includes understanding user authentication, role-based access control, and identity management principles. Learners also explore how policies can be fine-tuned to balance security with usability, ensuring that systems remain both secure and functional.
Access control is a critical part of enterprise security because improper configuration can lead to unauthorized access or data exposure. This stage helps candidates understand how to design secure environments that restrict access based on user roles and organizational requirements.
Introduction to FortiGate Configuration Concepts
A significant portion of the certification path involves working with FortiGate devices, which are core firewall and security appliances in the Fortinet ecosystem. At this stage, learners are introduced to basic configuration concepts.
This includes setting up interfaces, defining security zones, configuring routing, and applying basic firewall policies. Learners also explore how logging and monitoring work, allowing administrators to track network activity and identify potential issues.
Understanding FortiGate configuration is essential because it forms the foundation for more advanced security tasks. It also provides practical experience in managing real-world security infrastructure.
Security Monitoring and Logging Fundamentals
Monitoring and logging are critical components of cybersecurity operations. Learners study how security events are recorded, analyzed, and used to detect threats.
This includes understanding log types, event severity levels, and how alerts are generated when suspicious activity is detected. Learners also explore how logs are used for forensic analysis, helping security teams investigate incidents after they occur.
Effective monitoring allows organizations to detect threats early and respond quickly. This stage emphasizes the importance of visibility in cybersecurity operations and how proper logging supports incident response and compliance requirements.
Understanding Intrusion Prevention and Detection Systems
Intrusion prevention and detection systems play a key role in identifying malicious activity within network traffic. Learners study how these systems analyze data packets to detect known attack patterns and abnormal behavior.
At this stage, the focus is on understanding signature-based detection and anomaly-based detection methods. Learners also explore how these systems can block or alert administrators when threats are detected.
This knowledge is important because modern cyberattacks often attempt to bypass traditional security controls. Intrusion prevention systems provide an additional layer of defense by actively analyzing traffic in real time.
Web Filtering and Application Control Concepts
Web filtering and application control are essential for managing user activity on enterprise networks. Learners study how organizations control access to websites and applications based on security policies.
This includes blocking malicious websites, restricting access to non-work-related applications, and ensuring compliance with organizational policies. Application control also helps prevent the use of unauthorized software that may introduce security risks.
These controls are important because many cyber threats originate from web-based sources. By understanding how to implement filtering and control mechanisms, learners gain the ability to reduce exposure to online risks.
Foundations of Secure Network Design
The certification path also introduces basic concepts of secure network design. This involves understanding how to structure networks in a way that minimizes risk and improves security.
Learners study concepts such as network segmentation, demilitarized zones, and layered security architecture. These principles help ensure that even if one part of the network is compromised, the entire system is not affected.
Secure design is a fundamental skill for cybersecurity professionals because it influences how resilient an organization is against attacks. This stage helps learners begin thinking like security architects rather than just administrators.
Importance of Hands-On Practice and Simulation
Practical experience plays a crucial role in mastering cybersecurity skills. Learners are encouraged to work with simulated environments or real devices to reinforce theoretical knowledge.
Hands-on practice allows learners to configure security policies, troubleshoot issues, and observe how security systems respond to different scenarios. This experience is essential for building confidence and technical competence.
Simulation environments also provide a safe space for experimentation, allowing learners to make mistakes and learn from them without impacting real systems.
Building a Strong Cybersecurity Mindset
Beyond technical knowledge, the certification journey emphasizes the development of a strong cybersecurity mindset. This includes analytical thinking, problem-solving skills, and attention to detail.
Learners are encouraged to think like attackers in order to better defend systems. This involves understanding how vulnerabilities are exploited and how security controls can be bypassed.
A strong mindset also includes continuous learning, as cybersecurity is a constantly evolving field. Professionals must stay updated with new threats, technologies, and defense strategies.
Intermediate Fortinet NSE Skill Development
As learners progress beyond the foundational stage, the certification path shifts toward intermediate-level cybersecurity skills. This phase is focused on strengthening technical expertise and introducing more complex security configurations. The emphasis moves from basic understanding to practical implementation, where learners begin working with real-world security scenarios that reflect enterprise environments.
At this stage, candidates are expected to understand how different security components interact within a network. The focus is not only on individual tools but also on how they function together as part of a broader security infrastructure. This includes firewalls, intrusion prevention systems, secure gateways, and centralized management platforms.
The intermediate level is critical because it bridges the gap between basic cybersecurity awareness and advanced security engineering. It prepares learners for hands-on roles in network security administration and operations.
Advanced Firewall Configuration and Management
One of the most important areas of this stage is advanced firewall configuration. Learners build upon their basic understanding of FortiGate systems and begin working with more complex policy structures and security rules.
This includes creating detailed firewall policies that control traffic between multiple network zones. Learners study how to prioritize rules, manage exceptions, and ensure efficient traffic flow without compromising security. They also explore advanced features such as NAT configuration, virtual IP mapping, and policy-based routing.
Firewall management also involves understanding how to optimize performance while maintaining strong security controls. This requires balancing system resources, minimizing latency, and ensuring that security inspections do not degrade network performance.
At this level, learners are expected to think strategically about firewall deployment rather than simply applying basic rules.
VPN and Secure Connectivity Implementation
Secure communication is a key requirement in modern enterprise environments, and this stage introduces advanced VPN concepts. Learners study how virtual private networks are used to create encrypted communication channels between remote users and corporate networks.
This includes understanding site-to-site VPNs, remote access VPNs, and SSL VPN configurations. Learners also explore authentication mechanisms such as certificates, pre-shared keys, and multi-factor authentication.
A major focus is on troubleshooting VPN connectivity issues and ensuring stable and secure connections. Learners analyze common problems such as phase mismatches, encryption failures, and routing conflicts.
By mastering VPN technologies, candidates gain the ability to secure remote work environments and interconnect distributed networks safely.
Intrusion Prevention System Configuration and Optimization
At the intermediate level, intrusion prevention systems are studied in greater depth. Learners move beyond basic concepts and focus on tuning IPS policies for optimal performance and accuracy.
This includes understanding how signature databases are updated, how detection rules are applied, and how false positives are managed. Learners also study advanced filtering techniques that allow administrators to target specific types of threats while minimizing unnecessary alerts.
Performance optimization is a key focus area. Learners explore how to balance security depth with system efficiency, ensuring that IPS does not become a bottleneck in high-traffic environments.
This stage also introduces threat intelligence integration, where external data sources are used to enhance detection capabilities.
User Authentication and Identity Management Systems
Modern cybersecurity relies heavily on identity-based security models. At this stage, learners study how user authentication systems are implemented and managed within Fortinet environments.
This includes understanding local user databases, LDAP integration, RADIUS authentication, and single sign-on systems. Learners also explore how identity-based policies are created to control access based on user roles rather than just IP addresses.
Identity management is a critical component of zero trust security models, which assume that no user or device should be trusted by default. This approach significantly improves security in distributed and cloud-based environments.
Learners also study session management and user tracking, which are essential for monitoring user activity and enforcing security compliance.
Security Fabric Integration Concepts
A key feature of the Fortinet ecosystem is the security fabric, which integrates multiple security tools into a unified platform. At this stage, learners gain a deeper understanding of how this integration works.
The security fabric connects different Fortinet products to share threat intelligence, automate responses, and improve visibility across the entire network. Learners study how events detected by one device can trigger automated actions on another.
This integration improves response times and reduces the workload on security teams by enabling coordinated defense mechanisms.
Learners also explore fabric connectors, which allow integration with third-party security tools and cloud services. This ensures that the security architecture remains flexible and scalable.
Advanced Logging, Monitoring, and Reporting
Security monitoring becomes more advanced at this stage. Learners study how to interpret complex logs and generate detailed security reports.
This includes analyzing traffic patterns, identifying anomalies, and correlating events across multiple systems. Learners also explore how dashboards are used to visualize security data in real time.
Reporting plays an important role in compliance and auditing. Learners understand how to generate reports that demonstrate adherence to security policies and regulatory requirements.
Advanced monitoring also involves setting up automated alerts and integrating with security information and event management systems.
Threat Intelligence and Security Analytics
Threat intelligence is a critical component of modern cybersecurity strategies. At this stage, learners study how external threat data is collected, analyzed, and applied to improve security defenses.
This includes understanding indicators of compromise, threat feeds, and reputation-based filtering. Learners also explore how security analytics are used to detect patterns of malicious behavior.
By integrating threat intelligence into security systems, organizations can proactively defend against emerging threats rather than reacting after an attack occurs.
This stage emphasizes data-driven security decision-making, where analytics play a central role in identifying risks.
Secure Application Control and Deep Packet Inspection
Application control becomes more advanced at this level, focusing on deep packet inspection and granular traffic analysis. Learners study how applications are identified not just by ports but by their actual behavior and signatures.
This allows security systems to detect hidden or encrypted applications that may bypass traditional controls. Learners also explore how policies are applied to allow, block, or restrict specific application functions.
Deep packet inspection enables more precise security enforcement, ensuring that only legitimate application traffic is allowed within the network.
This capability is essential for preventing data leakage and unauthorized application usage.
Network Segmentation and Advanced Design Principles
Network segmentation becomes more complex at the intermediate stage. Learners study how large networks are divided into smaller, isolated segments to reduce risk and improve control.
This includes designing secure zones for different departments, separating critical systems from general user networks, and implementing strict communication rules between segments.
Advanced design principles also involve redundancy, high availability, and failover mechanisms. Learners explore how to ensure continuous security operations even in the event of hardware or network failures.
These design strategies are essential for building resilient enterprise environments.
Security Policy Optimization and Troubleshooting
As security environments grow more complex, policy management becomes more challenging. Learners study how to optimize security policies for efficiency and clarity.
This includes reducing rule redundancy, improving policy order, and ensuring that configurations are scalable. Troubleshooting becomes an important skill, as learners must identify and resolve conflicts between policies.
Common issues such as traffic blocking, authentication failures, and routing errors are analyzed in detail. Learners develop systematic approaches to diagnosing and resolving these problems.
This stage strengthens problem-solving skills and prepares candidates for real-world operational challenges.
Introduction to Security Automation and Orchestration
Automation is an increasingly important aspect of cybersecurity. At this stage, learners are introduced to basic concepts of security automation and orchestration.
This includes automating repetitive tasks such as log analysis, alert generation, and policy updates. Learners also explore how automated responses can be triggered when specific threats are detected.
Automation improves efficiency and reduces response times, allowing security teams to focus on more complex tasks.
Orchestration involves coordinating multiple security tools to respond to incidents in a unified manner.
Preparing for Advanced Certification Levels
The intermediate stage serves as preparation for advanced certification levels. Learners are expected to have a strong understanding of both technical configurations and security strategies.
At this point, candidates should be comfortable working with complex network environments, managing security policies, and analyzing threats.
The knowledge gained at this stage forms the foundation for advanced topics such as enterprise security architecture, cloud security integration, and large-scale security operations management.
Advanced Security Architecture and Design Principles
At the advanced stage of the Fortinet NSE certification journey, the focus shifts toward enterprise-level security architecture and system-wide design principles. This stage is not centered on basic configuration tasks anymore but on how entire security infrastructures are planned, structured, and optimized for large organizations. Learners are expected to think like security architects who design scalable, resilient, and highly secure environments.
Security architecture at this level involves integrating multiple security domains such as network security, endpoint protection, cloud security, and application security into a unified framework. The goal is to ensure that all layers of an organization’s infrastructure work together to provide consistent protection against threats.
Learners study how to design segmented networks that isolate sensitive systems, how to implement layered defense strategies, and how to ensure redundancy and high availability. The emphasis is on building systems that remain secure even under failure conditions or active attacks.
This stage also introduces the concept of defense in depth, where multiple security mechanisms are deployed at different layers of the infrastructure. This ensures that if one layer is compromised, additional layers continue to provide protection.
Enterprise Network Security Strategy Development
At this level, cybersecurity becomes more strategic rather than purely technical. Learners focus on how to develop enterprise-wide security strategies that align with business objectives.
This includes understanding risk management frameworks, security governance models, and compliance requirements. Security decisions are no longer made in isolation but are aligned with organizational goals, regulatory standards, and industry best practices.
Learners also study how to assess risk across large environments, identify critical assets, and prioritize protection efforts based on business impact. This helps ensure that security resources are allocated efficiently and effectively.
A key part of this stage is understanding how to create long-term security roadmaps that evolve with technological changes and emerging threats.
Zero Trust Security Model Implementation
One of the most important modern cybersecurity concepts covered at this stage is the zero trust security model. This model operates on the principle that no user, device, or system should be trusted by default, even if it is inside the network perimeter.
Learners study how to implement zero trust principles using continuous authentication, strict access controls, and micro-segmentation. Every access request is verified based on identity, device posture, and contextual factors.
This approach significantly reduces the risk of lateral movement within a network in the event of a breach. Even if an attacker gains access to one part of the system, they are unable to move freely without additional verification.
Zero trust also emphasizes continuous monitoring and real-time validation of user activity, ensuring that security is maintained at all times rather than only at the point of entry.
Advanced Threat Detection and Response Systems
At the expert level, threat detection becomes significantly more sophisticated. Learners study how advanced security systems use behavioral analysis, machine learning, and correlation engines to detect complex attacks.
Unlike traditional signature-based detection, advanced systems focus on identifying anomalies in network behavior. This includes unusual traffic patterns, unauthorized access attempts, and deviations from normal user activity.
Learners also explore how security events are correlated across multiple systems to identify coordinated attacks. This allows security teams to detect multi-stage attacks that may otherwise go unnoticed.
Response mechanisms are also more advanced at this stage. Automated containment actions can be triggered when threats are detected, such as isolating affected systems or blocking suspicious traffic in real time.
Security Operations Center (SOC) Concepts
A major focus of this stage is understanding the role of a Security Operations Center. A SOC is responsible for continuous monitoring, detection, analysis, and response to cybersecurity incidents within an organization.
Learners study how SOC teams operate, including incident triage, alert prioritization, and escalation procedures. The goal is to ensure rapid response to security threats while minimizing business disruption.
SOC environments rely heavily on centralized dashboards that provide real-time visibility into security events. Learners explore how these dashboards are used to correlate data from multiple sources and support decision-making.
The importance of collaboration within SOC teams is also emphasized, as effective incident response often requires coordination between analysts, engineers, and management.
Incident Response and Digital Forensics
Incident response becomes a critical skill at the advanced level. Learners study how organizations respond to security breaches in a structured and efficient manner.
This includes identifying the scope of an incident, containing the threat, eradicating malicious activity, and recovering affected systems. Each step must be carefully executed to minimize damage and prevent recurrence.
Digital forensics is also introduced, focusing on the investigation of security incidents after they occur. Learners study how logs, system data, and network traffic are analyzed to reconstruct attack timelines.
This process helps organizations understand how breaches occurred and how similar incidents can be prevented in the future.
Cloud Security Integration and Hybrid Environments
Modern enterprises increasingly rely on cloud infrastructure, and this stage covers how Fortinet security solutions integrate with cloud environments.
Learners study how security policies are extended to cloud platforms, ensuring consistent protection across on-premises and cloud systems. This includes securing virtual machines, cloud storage, and containerized applications.
Hybrid environments, where organizations use both on-premises and cloud resources, require careful security coordination. Learners explore how unified security management is achieved across these environments.
This stage also introduces concepts such as cloud access security brokers and secure cloud gateways, which help enforce security policies in distributed environments.
Secure SD-WAN and Network Optimization
Secure SD-WAN is an important topic at the advanced level, focusing on optimizing network performance while maintaining strong security controls.
Learners study how SD-WAN technology dynamically routes traffic based on application requirements, network conditions, and security policies. This ensures efficient use of network resources while maintaining secure communication.
Security is deeply integrated into SD-WAN solutions, allowing organizations to inspect traffic at multiple points and enforce consistent policies across branches and remote locations.
This approach improves both performance and security, especially in distributed enterprise environments with multiple locations.
Advanced Automation, Orchestration, and AI-Driven Security
Automation becomes significantly more advanced at this stage. Learners study how security orchestration platforms integrate multiple tools to automate complex workflows.
This includes automated threat detection, incident response, log analysis, and policy enforcement. Automation reduces manual workload and improves response times.
Artificial intelligence and machine learning also play a growing role in cybersecurity operations. Learners explore how AI-driven systems analyze large volumes of data to identify patterns and predict potential threats.
These technologies enable proactive security measures, allowing organizations to prevent attacks before they occur rather than reacting afterward.
Compliance, Governance, and Risk Management
Enterprise security is closely tied to regulatory compliance and governance frameworks. Learners study how organizations ensure compliance with industry standards and legal requirements.
This includes understanding data protection laws, security auditing processes, and governance structures. Compliance ensures that organizations maintain proper security hygiene and avoid legal or financial penalties.
Risk management is also a key component, focusing on identifying, assessing, and mitigating security risks across the organization.
Learners develop the ability to balance security requirements with business needs, ensuring that security measures do not hinder operational efficiency.
Large-Scale Network Deployment and High Availability Design
At the expert level, learners study how to design and deploy security systems across large-scale networks. This includes ensuring high availability, redundancy, and failover capabilities.
High availability ensures that security systems remain operational even if individual components fail. Learners explore clustering, load balancing, and redundant architecture designs.
Large-scale deployments require careful planning to ensure consistent policy enforcement across all network segments and geographic locations.
This stage emphasizes reliability, scalability, and resilience in enterprise security design.
Advanced Troubleshooting and Performance Optimization
Troubleshooting at this level becomes more complex, involving multi-layered network environments and distributed systems.
Learners study how to diagnose performance issues, identify bottlenecks, and resolve configuration conflicts across large infrastructures.
Performance optimization involves fine-tuning security systems to ensure that they operate efficiently under high traffic loads without compromising protection.
This requires deep technical knowledge and the ability to analyze system behavior under different conditions.
Strategic Role of Cybersecurity Professionals
At the advanced and expert levels, cybersecurity professionals transition into strategic roles within organizations. They are no longer focused solely on technical implementation but also on planning, decision-making, and leadership.
Learners study how security teams align with business objectives, communicate risks to stakeholders, and contribute to organizational strategy.
This includes understanding how cybersecurity supports business continuity, protects brand reputation, and enables digital transformation initiatives.
Cybersecurity becomes a core component of overall business strategy rather than just an IT function.
Expert-Level Exam Preparation Approach
At the expert stage of the Fortinet NSE certification journey, preparation becomes less about learning new concepts and more about refining mastery of everything previously covered. Candidates are expected to demonstrate deep understanding of enterprise security design, troubleshooting complexity, and making architectural decisions under realistic constraints. Exam preparation at this level requires a structured and disciplined approach because the questions often test scenario-based thinking rather than simple definitions.
Instead of memorizing configurations, learners must understand how and why specific security decisions are made in real environments. This includes evaluating trade-offs between performance and security, identifying the most efficient solution for complex network problems, and predicting the impact of configuration changes across large infrastructures. The exam is designed to measure practical intelligence rather than theoretical recall.
A strong preparation strategy involves revisiting all foundational, intermediate, and advanced concepts in a connected manner. This helps build a mental map of how different technologies interact within the Fortinet ecosystem. Understanding relationships between firewall policies, intrusion prevention systems, secure access mechanisms, and cloud integrations becomes essential at this stage.
Advanced Hands-On Lab Mastery
Practical lab experience becomes one of the most important factors for success at the expert level. Candidates are expected to be comfortable working in simulated enterprise environments where multiple security components are deployed simultaneously. These environments replicate real-world complexity, including multi-site networks, hybrid cloud configurations, and distributed security policies.
Hands-on practice should focus on building full security architectures from scratch and then troubleshooting them under different failure scenarios. This includes simulating network outages, policy conflicts, authentication failures, and performance degradation issues. The goal is to develop confidence in diagnosing and resolving problems quickly and accurately.
Lab mastery also involves testing security responses under attack conditions. This means simulating intrusion attempts, malware traffic, and unauthorized access scenarios to observe how systems respond. Understanding system behavior under stress is critical for developing expert-level skills.
The ability to rebuild environments repeatedly from memory also strengthens technical fluency. This ensures that candidates are not dependent on documentation during high-pressure situations.
Real-World Scenario Analysis and Decision Making
At the expert level, exams and real-world responsibilities often revolve around scenario analysis. Candidates are presented with complex enterprise situations where multiple possible solutions exist. The challenge is to select the most appropriate approach based on security requirements, business constraints, and system performance considerations.
This requires strong analytical thinking and the ability to interpret incomplete or layered information. In many cases, there is no single perfect answer, only the most efficient or secure compromise based on the situation.
For example, a scenario may involve balancing remote access security with user convenience, or improving threat detection without impacting network performance. Candidates must evaluate risks, benefits, and long-term impact before making decisions.
This type of thinking reflects real cybersecurity leadership roles, where decisions must be made quickly but with full awareness of organizational consequences.
Troubleshooting in Complex Distributed Environments
Advanced troubleshooting is one of the most challenging aspects of expert-level certification. Unlike basic environments where problems are isolated, enterprise systems involve interconnected components that can fail in unpredictable ways.
Candidates must understand how to trace issues across multiple layers, including network routing, firewall policies, authentication systems, and cloud integrations. A single problem may originate in one system but appear in another, making root cause analysis essential.
Effective troubleshooting requires a systematic approach. This includes isolating variables, analyzing logs from multiple sources, and correlating events across different security systems. Candidates must also be able to distinguish between symptoms and actual causes.
Performance-related issues add another layer of complexity. These may involve latency, throughput limitations, or resource exhaustion across distributed systems. Understanding how to identify bottlenecks and optimize system performance is a key expert-level skill.
Security Architecture Optimization for Large Enterprises
At this stage, learners focus heavily on optimizing security architectures for scalability and efficiency. Large enterprises require systems that can handle high traffic volumes while maintaining consistent protection across all locations and users.
Optimization involves refining security policies, improving system segmentation, and ensuring efficient use of resources. It also includes reducing redundancy in configurations and eliminating unnecessary complexity that may slow down operations.
Architectural optimization also considers future growth. Systems must be designed in a way that allows easy expansion without requiring complete redesigns. This requires forward-thinking and strategic planning skills.
High availability and disaster recovery strategies are also refined at this stage. Ensuring that security systems remain operational during failures is critical for enterprise resilience.
Integration of Cloud, Hybrid, and On-Premises Security
Modern enterprises operate in hybrid environments that combine cloud infrastructure with traditional on-premises systems. At the expert level, candidates must understand how to unify security across these diverse environments.
This includes ensuring consistent policy enforcement regardless of where workloads are hosted. Security must extend seamlessly across physical data centers, private cloud environments, and public cloud platforms.
Challenges such as visibility gaps, inconsistent policy enforcement, and fragmented monitoring must be addressed through integrated security frameworks.
Candidates also study how secure connectivity is maintained between cloud and on-premises environments, ensuring that data flows remain protected at all times.
Advanced Threat Landscape Understanding
At this level, cybersecurity professionals must have a deep understanding of the evolving threat landscape. Cyberattacks are no longer simple or isolated; they are highly coordinated, persistent, and multi-layered.
Candidates study advanced persistent threats, zero-day exploits, ransomware ecosystems, and nation-state attack strategies. Understanding attacker behavior becomes as important as understanding defensive technologies.
Threat actors often use stealth techniques to avoid detection, including encrypted communication, fileless malware, and living-off-the-land tactics. Recognizing these patterns is essential for effective defense.
This stage emphasizes predictive security, where organizations aim to anticipate attacks before they fully develop rather than reacting afterward.
Operational Security Leadership and Responsibility
At the expert stage, cybersecurity professionals often transition into leadership roles. This involves not only technical expertise but also the ability to guide teams, manage security operations, and make strategic decisions.
Candidates must understand how to communicate risks to non-technical stakeholders and translate complex security issues into business terms. This is essential for gaining organizational support for security initiatives.
Leadership also involves prioritizing incidents, managing resources, and ensuring that security operations align with business continuity requirements.
Decision-making becomes a key responsibility, especially during high-impact security incidents where rapid response is required.
Continuous Improvement and Adaptive Security Models
Cybersecurity is a constantly evolving field, and expert-level professionals must adopt a mindset of continuous improvement. Security systems must be regularly updated, tested, and refined to keep up with emerging threats.
Adaptive security models are designed to evolve based on new intelligence, user behavior, and threat patterns. This ensures that defenses remain effective even as attack techniques change.
Candidates study how feedback loops from monitoring systems, incident response teams, and threat intelligence feeds are used to improve security posture over time.
This dynamic approach ensures long-term resilience in rapidly changing digital environments.
Career Pathways After NSE Certification Mastery
Achieving expert-level NSE certification opens doors to advanced career opportunities in cybersecurity. Professionals may move into roles such as security architect, SOC manager, network security engineer, or cybersecurity consultant.
These roles involve designing enterprise security systems, managing large-scale operations, and advising organizations on risk management strategies.
Career progression often leads toward leadership positions where strategic planning and decision-making become primary responsibilities.
The certification also provides a strong foundation for specialization in areas such as cloud security, incident response, and threat intelligence analysis.
Common Challenges and How Experts Overcome Them
Many candidates face challenges when transitioning from intermediate to expert-level understanding. One common difficulty is managing complexity in large-scale environments where multiple systems interact simultaneously.
Another challenge is developing the ability to think in terms of architecture rather than individual configurations. This shift in mindset takes time and consistent practice.
Experts overcome these challenges through continuous exposure to real-world scenarios, structured lab practice, and consistent review of core principles.
Experience plays a critical role in building confidence and improving decision-making speed under pressure.
Final Certification Mindset and Long-Term Growth
At the end of the NSE certification journey, the most important achievement is not just technical knowledge but the development of a cybersecurity mindset. This includes analytical thinking, adaptability, and a deep understanding of how digital systems are protected at scale.
Certified professionals are expected to continuously evolve with the industry, as cybersecurity is never static. New threats, technologies, and architectures constantly reshape the landscape.
Long-term success depends on staying updated, practicing regularly, and applying knowledge in real-world environments. The certification serves as a foundation, but expertise is built through ongoing experience and learning.
Conclusion
The Fortinet NSE certification journey represents a structured progression from foundational cybersecurity awareness to advanced enterprise-level security expertise. Across all stages, the program builds a strong balance between theoretical understanding and hands-on technical capability, ensuring that learners develop both conceptual clarity and practical confidence in real-world environments.
At the foundational level, the focus is on building awareness of cybersecurity principles, basic network concepts, and the role of security technologies in protecting digital systems. This stage establishes the essential mindset required to understand how threats emerge and how organizations defend against them.
As learners move into the intermediate stage, the emphasis shifts toward applied skills such as firewall configuration, VPN setup, intrusion prevention, identity management, and security monitoring. This stage bridges the gap between theory and real-world implementation, allowing candidates to begin working with enterprise-grade security systems.
The advanced stage introduces architectural thinking, enterprise security design, zero trust implementation, cloud integration, and large-scale network security strategies. Here, professionals learn to design resilient infrastructures that can withstand complex and evolving cyber threats while maintaining performance and scalability.