The generator polynomial is the mathematical foundation of Cyclic Redundancy Check. It is a predefined binary pattern used by both the sender and receiver to calculate and verify the CRC value. This polynomial is not chosen randomly. It is carefully designed to detect specific types of errors with high accuracy and reliability.
In CRC calculations, data is represented as a binary sequence made of 0s and 1s. This sequence is treated like a polynomial where each bit represents a coefficient. The generator polynomial is then used to divide this data using modulo-2 division, which is different from normal division because it does not involve borrowing or carrying. Instead, it uses XOR operations, making the process fast and efficient for digital systems.
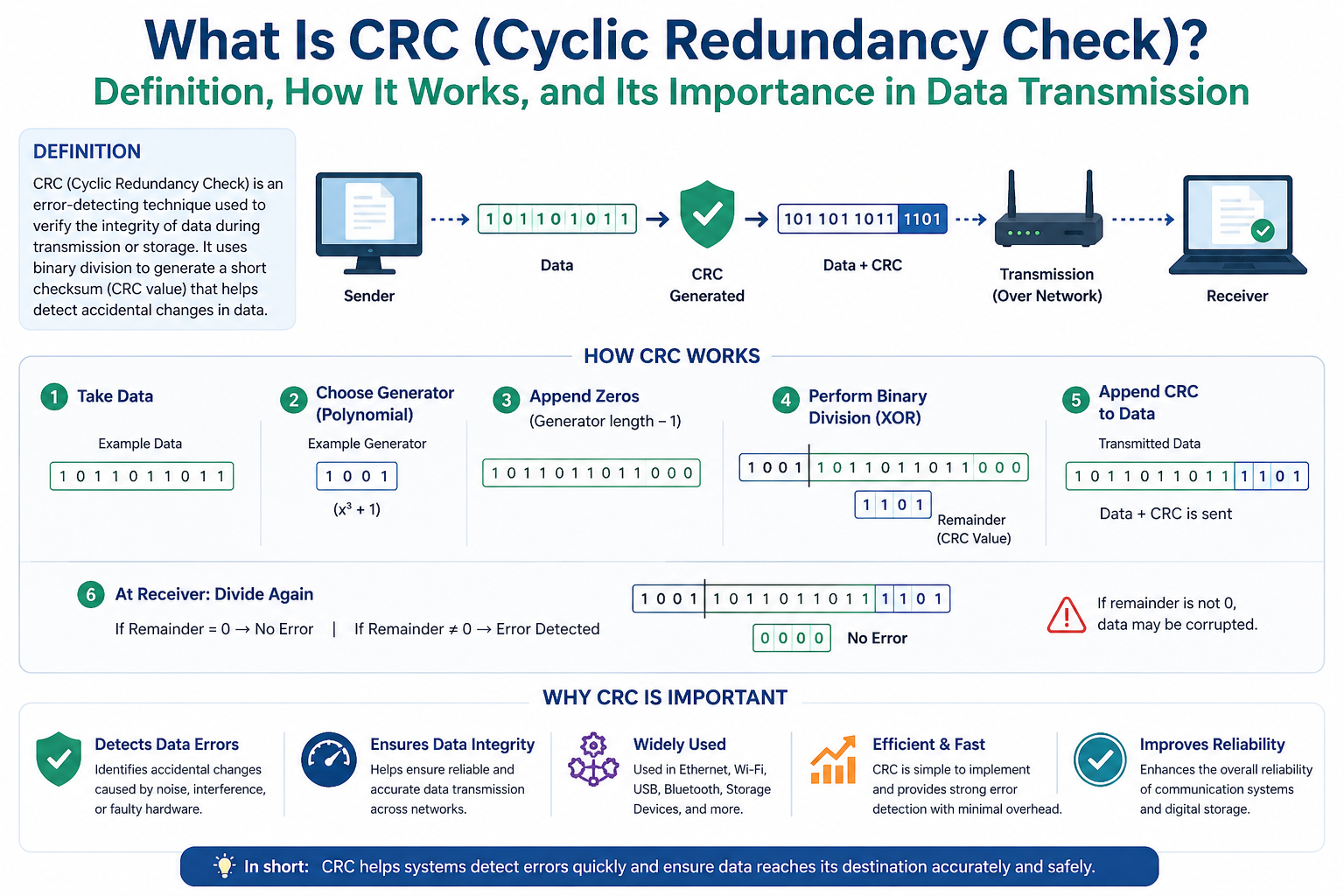
For example, if a system uses CRC-32, it follows a specific 32-bit generator polynomial. The sender appends extra zero bits to the original message and performs the division. The remainder produced after division becomes the CRC checksum. This checksum is added to the transmitted data. At the receiving end, the same division process is repeated. If the remainder is zero or matches the expected value, the data is considered valid.
The choice of generator polynomial greatly affects the effectiveness of error detection. Some polynomials are better at detecting burst errors, while others are optimized for single-bit or double-bit errors. This is why different communication protocols use different CRC standards depending on their reliability requirements.
Step-by-Step Process of CRC Calculation
Understanding CRC becomes easier when the process is broken into simple steps. Although the actual mathematics happens at the binary level, the concept is straightforward and practical.
First, the sender takes the original data that needs to be transmitted. This could be a file, a network packet, a command signal, or any digital information. Then, a fixed number of zero bits is added to the end of the data. The number of added zeros depends on the size of the CRC being used. For example, CRC-16 requires 16 extra zero bits.
Next, the sender divides this extended data by the agreed generator polynomial using modulo-2 division. The remainder left after this division is the CRC value. This remainder is then attached to the original data and sent across the network or communication channel.
When the receiver gets the data, it performs the same division using the same generator polynomial. If the remainder is zero, it means the data has most likely arrived without corruption. If the remainder is not zero, an error is detected, and the receiver may discard the packet or request retransmission.
This process happens extremely fast inside hardware and software systems, often without users even noticing it. It protects emails, downloads, cloud storage, operating systems, and even simple USB file transfers.
Modulo-2 Division in CRC
Modulo-2 division is the core mathematical operation behind CRC. Unlike normal arithmetic division, modulo-2 division works only with binary values and uses XOR instead of subtraction. This makes it ideal for digital systems because XOR operations are simple, fast, and efficient for processors and hardware circuits.
In normal subtraction, numbers are borrowed and carried between digits. In modulo-2 division, this does not happen. The rules are simple: 1 XOR 1 equals 0, 0 XOR 0 equals 0, 1 XOR 0 equals 1, and 0 XOR 1 equals 1. This allows binary data to be processed quickly without complex arithmetic.
The sender uses modulo-2 division to calculate the CRC remainder. The receiver repeats the same division to verify the data. Because both sides use the same logic and generator polynomial, even small changes in transmitted bits can produce a completely different remainder, making error detection highly reliable.
This method is one reason CRC remains popular in both software and hardware systems. It provides strong protection without slowing down communication significantly.
Types of Errors CRC Can Detect
CRC is highly effective because it can detect many common transmission errors that occur in real-world communication systems. Data can be damaged by electrical noise, signal interference, weak wireless connections, faulty cables, damaged storage media, or hardware failures.
One of the simplest errors is a single-bit error, where only one bit changes from 0 to 1 or from 1 to 0. CRC can easily detect this type of error. It can also detect double-bit errors, where two separate bits are changed during transmission.
Another important type is burst error detection. A burst error happens when multiple consecutive bits become corrupted, often caused by signal interference or hardware faults. CRC is especially strong at detecting burst errors, which is one of the main reasons it is preferred over simpler methods like parity checks.
CRC can also detect many random error patterns that occur unpredictably. While no error detection system is perfect, CRC offers extremely high detection rates for accidental data corruption. This makes it suitable for high-speed networks, storage systems, and embedded devices where reliability is critical.
Difference Between CRC and Checksum
CRC and checksum are both used for error detection, but they work differently and offer different levels of reliability. Many people confuse the two because both help verify data integrity, but CRC is generally stronger and more advanced.
A checksum is usually created by adding data values together and sending the result along with the original data. The receiver performs the same addition and compares the results. This method is simple and fast, but it may fail to detect certain error patterns, especially when multiple bits change in a way that keeps the total unchanged.
CRC uses polynomial division instead of simple addition. Because of this, it is much better at detecting complex transmission errors such as burst errors and multiple bit corruption. CRC provides stronger protection and is therefore used in systems where data accuracy is more important.
Checksums are often used in simpler applications where speed matters more than maximum reliability. CRC is used in more demanding environments like network protocols, hard drives, industrial automation, and wireless communication systems.
In short, checksum is simpler but weaker, while CRC is stronger and more dependable for serious data transmission tasks.
Difference Between CRC and Parity Check
Parity check is one of the oldest and simplest methods of error detection. It works by adding a single parity bit to a group of data bits. This parity bit ensures that the total number of 1s is either even or odd, depending on the system design.
When the receiver gets the data, it checks whether the parity rule still holds. If not, an error is detected. While this method is easy to implement, it is very limited. It can usually detect only single-bit errors and may fail when multiple bits change in a way that preserves parity.
CRC is far more powerful than parity checking. Instead of using one extra bit, CRC uses multiple bits and mathematical division to identify errors. It can detect single-bit errors, multiple-bit errors, and burst errors with much higher accuracy.
Parity checks may still be used in simple devices or memory systems where basic protection is enough. However, for modern networking, storage, and communication systems, CRC is the preferred solution because it provides stronger and more reliable error detection.
Common CRC Standards
Different systems use different CRC standards depending on how much protection they need. These standards mainly differ in the length of the checksum and the generator polynomial used.
CRC-8 is a small and lightweight version often used in embedded systems, sensors, and simple communication devices. It provides basic error detection with minimal overhead.
CRC-16 is widely used in industrial communication, Bluetooth, USB protocols, and some file systems. It offers stronger protection than CRC-8 while still being efficient for devices with limited resources.
CRC-32 is one of the most common standards and is used in Ethernet, ZIP files, storage systems, and software downloads. It provides excellent detection for large amounts of data and is considered highly reliable for general-purpose computing.
CRC-64 is used in systems that require even stronger protection, such as large databases, enterprise storage, and advanced data verification systems. It offers very high reliability but uses more processing and storage resources.
The selection of a CRC standard depends on system requirements, data size, processing power, and the acceptable risk of transmission errors.
CRC in Network Communication
Network communication depends heavily on accurate data transfer. Whether users are browsing websites, sending emails, streaming videos, or making online payments, data packets travel across many devices and networks before reaching their destination. CRC helps ensure those packets arrive correctly.
In Ethernet communication, every frame includes a Frame Check Sequence, which is based on CRC. When a device receives a frame, it checks the CRC value to verify whether the frame was damaged during transmission. If an error is found, the corrupted frame is discarded.
Wireless communication systems such as Wi-Fi and mobile networks also use CRC to detect errors caused by weak signals, interference, or signal fading. This helps maintain stable and reliable connections even in noisy environments.
Without CRC, corrupted packets could enter systems unnoticed, causing broken downloads, unstable connections, software failures, or security issues. CRC acts as a protective layer that keeps communication trustworthy and efficient.
CRC in Storage Devices
Storage devices such as hard drives, SSDs, memory cards, and optical discs also rely on CRC for data protection. Stored data can become corrupted because of physical damage, aging hardware, electrical faults, or interrupted write operations.
When data is written to storage, a CRC value is often calculated and saved along with it. Later, when the data is read, the system recalculates the CRC and compares it with the stored value. If the values do not match, the system knows the data may be corrupted.
This is especially important for operating systems, databases, backups, and system files where data integrity is essential. A damaged system file could cause crashes, boot failures, or security vulnerabilities.
File compression formats such as ZIP also use CRC-32 to verify file integrity after extraction. This helps users know whether downloaded or transferred files are complete and uncorrupted.
CRC in storage systems improves long-term reliability and protects users from silent data corruption that might otherwise go unnoticed.
CRC in Embedded Systems
Embedded systems are specialized computing devices found inside machines, vehicles, medical equipment, industrial controllers, smart appliances, and IoT devices. These systems often operate in environments where reliability is extremely important.
In such systems, CRC helps verify commands, sensor data, firmware updates, and communication between components. For example, in automotive electronics, CRC can ensure that control signals sent between engine systems are accurate and safe.
In medical devices, incorrect data transmission could lead to dangerous outcomes. CRC helps reduce this risk by detecting communication errors before they affect operation.
Firmware updates in embedded devices also use CRC verification to ensure the update file is not damaged. Installing corrupted firmware could permanently damage the device or make it unstable.
Because embedded systems often have limited memory and processing power, CRC is ideal since it provides strong error detection without requiring heavy computational resources.
Advantages of Using CRC
CRC offers several major advantages that make it one of the most trusted error detection methods in digital systems. One of its biggest strengths is speed. CRC calculations can be performed very quickly in both software and hardware, making it suitable for real-time communication.
Another major advantage is strong error detection capability. CRC can detect many common transmission problems including single-bit errors, burst errors, and random corruption patterns with very high accuracy.
It is also efficient because it adds only a small amount of extra data compared to the protection it provides. This means systems can maintain reliability without using too much bandwidth or storage space.
CRC is highly standardized, which allows different devices and systems to communicate using the same rules. This makes it ideal for networking, storage, and industrial applications.
Its low implementation cost also makes it practical for both simple and complex systems, from small sensors to large enterprise servers.
These advantages explain why CRC remains widely used across nearly every area of modern computing and telecommunications.
Limitations of CRC
Although CRC is very powerful, it does have limitations. The most important limitation is that CRC only detects errors; it does not correct them. If corrupted data is found, the system must either discard it or request retransmission.
Another limitation is that CRC is mainly designed for accidental errors, not intentional tampering. It is not a security mechanism and should not be used as protection against malicious attacks. Attackers can sometimes modify both data and CRC values together, bypassing detection.
For strong security verification, cryptographic hash functions and digital signatures are used instead of CRC. CRC focuses on transmission reliability, not cybersecurity.
Also, no CRC system can guarantee detection of every possible error pattern. While the probability of missing an error is very low, it is not zero. This is why critical systems may combine CRC with other validation methods for additional protection.
Despite these limitations, CRC remains extremely effective for its intended purpose and continues to be a core part of reliable digital communication.
How CRC Is Used in Ethernet Networks
Ethernet is one of the most common networking technologies used in homes, offices, data centers, and industrial environments. Every time devices communicate over a wired local area network, Ethernet frames are exchanged between systems. CRC plays an essential role in ensuring these frames are delivered accurately.
Each Ethernet frame includes a field called the Frame Check Sequence, commonly known as FCS. This field contains a CRC value generated from the frame’s contents before transmission. The sending device calculates the CRC and attaches it to the frame before sending it across the network.
When the receiving device gets the frame, it performs the same CRC calculation using the received data. If the calculated value matches the FCS, the frame is accepted as valid. If the values do not match, the frame is considered corrupted and is usually discarded immediately.
This process prevents damaged frames from entering higher network layers where they could cause application errors, system failures, or unreliable communication. CRC in Ethernet helps maintain stable and dependable network performance even when electrical interference or cable faults occur.
Because Ethernet networks are used in critical systems such as banking, cloud services, hospitals, and industrial automation, reliable frame validation through CRC is extremely important.
CRC in Wireless Communication
Wireless communication is more vulnerable to data corruption than wired communication because signals travel through the air and can be affected by interference, obstacles, weather conditions, and signal fading. CRC helps protect wireless data by detecting errors before corrupted information causes problems.
Technologies such as Wi-Fi, Bluetooth, mobile networks, satellite communication, and radio systems all use CRC as part of their transmission protocols. When a wireless device sends data, a CRC value is generated and attached to the message.
The receiving device checks the CRC after receiving the signal. If the values match, the data is processed normally. If the CRC check fails, the system knows the data was damaged during transmission and may request the message again.
This is especially important in mobile networks where users expect stable internet connections, voice calls, and video streaming. Without CRC, frequent wireless interference could cause serious communication failures.
CRC also supports wireless sensors and Internet of Things devices, where accurate communication is necessary for automation, monitoring, and remote control systems.
Its ability to detect burst errors makes CRC especially useful in wireless environments where signal disruption often affects multiple bits at once.
CRC in USB and Peripheral Devices
Universal Serial Bus, commonly known as USB, is used to connect keyboards, printers, storage drives, cameras, smartphones, and many other devices to computers. CRC helps ensure that data transferred through USB connections remains accurate and complete.
When files are copied to a flash drive or commands are sent to a printer, USB communication uses CRC to verify the integrity of the transmitted information. Both the host device and the connected peripheral perform CRC validation during the transfer process.
If an error is detected, the corrupted packet may be retransmitted automatically without the user noticing. This helps maintain smooth operation and prevents problems such as damaged files, failed print jobs, or unstable device connections.
USB systems often operate in environments with electrical noise caused by power supply fluctuations, nearby devices, or cable quality issues. CRC provides a strong defense against these common problems.
Because users depend on USB devices for everyday work and data transfer, CRC plays an important background role in making these connections reliable and safe.
CRC in Hard Drives and SSDs
Hard drives and solid-state drives store valuable system files, documents, applications, and databases. Even small errors in stored data can lead to serious consequences such as file corruption, system crashes, or data loss. CRC helps prevent these issues by monitoring data integrity during both writing and reading operations.
When data is written to a storage device, the system may generate a CRC value and store it alongside the actual information. Later, when the data is accessed, the CRC is recalculated and compared with the stored value.
If the values match, the data is considered reliable. If they do not match, it suggests that corruption may have occurred due to bad sectors, aging hardware, controller failures, or interrupted operations.
Some operating systems also display CRC-related error messages when they detect problems during file transfers or disk access. These warnings help users identify damaged drives or unstable connections before complete failure occurs.
In enterprise storage systems and cloud infrastructure, CRC helps protect massive amounts of information where even minor corruption could affect thousands of users or important business operations.
CRC in ZIP Files and Software Downloads
Many compressed files such as ZIP archives use CRC-32 to verify the integrity of stored files. This helps users know whether downloaded or extracted files are complete and unchanged.
When a file is compressed into a ZIP archive, CRC values are calculated for the included files and stored inside the archive. During extraction, the system checks these values again. If the CRC does not match, the software warns the user that the file may be damaged or incomplete.
This is especially important when downloading software, updates, games, or important documents from the internet. Network interruptions, incomplete downloads, or storage problems can easily corrupt files without obvious signs.
CRC helps detect these problems before users try to install damaged software or open broken documents. This prevents application failures, installation errors, and potential security risks caused by corrupted system files.
Software installers, firmware packages, and backup archives also commonly use CRC as a quick integrity check before proceeding with installation or restoration.
CRC in Database Systems
Databases store highly valuable information such as financial records, customer details, medical history, and business operations. Data corruption inside a database can cause serious operational failures and legal risks. CRC helps reduce this risk by supporting integrity verification in storage and transmission.
When data blocks are written to database storage, CRC may be calculated and saved with them. Later, when the database engine reads those blocks, it checks the CRC to confirm that the data remains unchanged.
If corruption is detected, the system can prevent damaged records from being processed and may trigger recovery mechanisms such as backups, replication, or repair operations.
Large enterprise databases and distributed systems rely heavily on this kind of protection because corruption may occur from hardware faults, storage failures, memory errors, or unexpected shutdowns.
CRC helps maintain trust in data-driven systems where accuracy is essential for decision-making and compliance requirements.
CRC in Operating Systems
Operating systems depend on thousands of system files, configuration data, drivers, and boot records. If these files become corrupted, the system may become unstable or fail to start entirely. CRC is often used to help protect these important components.
During software installation, updates, and file transfers, CRC checks help verify that files are complete and unchanged. If corruption is found, the process may stop automatically to prevent system damage.
Disk utilities and system diagnostics may also use CRC to identify bad sectors or failing drives. For example, when users see a cyclic redundancy check error during file copying, it usually indicates a problem with the storage device or the data being transferred.
Backup and recovery systems also depend on CRC to ensure restored files are accurate. Without this validation, users might unknowingly restore corrupted backups.
CRC supports the long-term reliability of operating systems by detecting silent errors before they become major failures.
CRC in Industrial Automation
Factories, power plants, manufacturing systems, and industrial control environments depend on accurate communication between machines. Sensors, controllers, robotic systems, and monitoring devices constantly exchange information that must remain correct and dependable.
CRC is widely used in industrial communication protocols such as Modbus, CAN bus, and many programmable logic controller systems. It helps ensure that commands, measurements, and control signals are transmitted without corruption.
For example, if a machine receives an incorrect control instruction because of a transmission error, it could cause production failures, equipment damage, or safety risks. CRC helps prevent this by detecting corrupted messages before they are executed.
Industrial environments often contain strong electrical noise from motors, high-voltage systems, and heavy machinery. This makes error detection even more important than in normal office networks.
Because CRC is fast and lightweight, it is ideal for real-time industrial systems where both speed and reliability are required.
CRC in Automotive Systems
Modern vehicles contain many electronic control units that manage braking, engine performance, airbags, navigation, entertainment, and safety systems. These components communicate constantly using internal networks such as CAN bus and LIN bus.
CRC helps verify the accuracy of data exchanged between these systems. For example, if braking commands or sensor readings are corrupted during transmission, the consequences could be dangerous.
By using CRC, automotive systems can detect errors before incorrect information affects vehicle operation. This improves both performance and passenger safety.
Firmware updates for vehicles also use CRC validation to ensure update files are complete and safe before installation. A damaged update could disable important features or create system instability.
As vehicles become more connected and software-driven, CRC continues to play an important role in maintaining dependable electronic communication.
CRC in Medical Devices
Medical devices require extremely high reliability because incorrect data can directly affect patient safety. Equipment such as infusion pumps, heart monitors, imaging systems, ventilators, and diagnostic tools all depend on accurate data transmission.
CRC helps ensure that sensor readings, patient records, software commands, and device communication remain correct. If a message is corrupted, CRC can detect the problem before incorrect data leads to harmful decisions.
For example, in remote patient monitoring systems, CRC helps protect health data sent from sensors to hospital systems. In surgical equipment, it supports safe communication between control modules.
Medical software updates also rely on CRC verification before installation to prevent system failures caused by corrupted files.
Because healthcare systems demand trust and precision, CRC serves as an important layer of protection behind the scenes.
CRC in Space and Satellite Communication
Space communication presents major challenges because signals must travel extremely long distances and are exposed to radiation, atmospheric interference, and signal weakening. CRC is widely used to protect data exchanged between satellites, spacecraft, and ground stations.
Commands sent to satellites must be accurate because retransmission may take significant time or may not be possible immediately. CRC helps detect errors before damaged instructions are executed.
Scientific data returned from satellites and probes also depends on CRC validation. This ensures that research information, weather monitoring, navigation data, and communication services remain reliable.
Satellite television, GPS systems, and remote sensing technologies all benefit from CRC-based protection.
In these environments, where communication is expensive and conditions are harsh, reliable error detection is critical for mission success.
CRC in Cloud Computing and Data Centers
Cloud platforms and data centers manage enormous amounts of information for businesses, governments, and personal users. Data moves constantly between servers, storage systems, backup platforms, and network infrastructure.
CRC helps protect this movement by verifying data integrity during storage, replication, and transmission. It ensures that copied files, virtual machine images, and database records remain accurate across distributed systems.
If corruption occurs during backup or synchronization, CRC can detect it before damaged information spreads across multiple systems. This is especially important in disaster recovery and high-availability environments.
Large-scale storage platforms often combine CRC with additional integrity checks to provide stronger protection for mission-critical operations.
Because users trust cloud systems to store important information securely and reliably, CRC remains a key part of maintaining that trust behind the infrastructure.
CRC in Internet of Things Devices
The Internet of Things, commonly called IoT, includes smart devices such as security cameras, smart thermostats, fitness trackers, industrial sensors, smart home systems, and connected appliances. These devices constantly exchange information with each other and with cloud platforms. CRC helps ensure that this data remains accurate during transmission.
IoT devices often work in environments with unstable wireless signals, low power conditions, and limited hardware resources. Because of this, they need an error detection method that is both reliable and lightweight. CRC is ideal because it provides strong protection without requiring large amounts of memory or processing power.
For example, a smart temperature sensor sending incorrect readings to an automation system could cause equipment failure or wasted energy. CRC helps detect such transmission errors before bad data is accepted.
Firmware updates for IoT devices also use CRC validation to ensure update files are complete and safe before installation. This prevents damaged firmware from making devices unstable or unusable.
As IoT continues to grow in homes, healthcare, agriculture, and smart cities, CRC remains a key technology for maintaining dependable communication.
CRC in Banking and Financial Systems
Banking systems handle highly sensitive information including transactions, account balances, payment processing, and digital records. Even a small transmission error could create serious financial problems. CRC helps support data integrity across these systems.
When transaction records move between ATMs, banking servers, payment gateways, and financial databases, CRC can be used to verify that the information remains unchanged during transfer.
For example, if a payment instruction becomes corrupted during transmission, CRC can help detect the issue before incorrect amounts are processed. This reduces operational risks and improves trust in financial systems.
While stronger cryptographic methods are used for security and fraud prevention, CRC still plays an important role in detecting accidental transmission and storage errors.
Backup systems, transaction logs, and network communication in financial infrastructure often rely on CRC as part of a larger reliability strategy.
Its speed and low overhead make it practical for high-volume systems where millions of transactions may be processed every day.
CRC in Telecommunications
Telecommunication systems such as mobile networks, internet service providers, fiber optic networks, and telephone systems depend on continuous and accurate data exchange. CRC helps protect this communication from corruption caused by noise, signal loss, or hardware faults.
Voice calls, text messages, internet traffic, and streaming services all involve data packets moving across complex networks. CRC checks these packets to ensure they arrive correctly before being processed.
In fiber optic systems, signal quality is usually strong, but transmission errors can still occur due to hardware issues or synchronization problems. CRC helps detect these issues early.
In mobile communication, users moving between towers and signal zones may experience interference. CRC supports stable connections by identifying damaged packets and enabling retransmission when necessary.
Without CRC, telecommunication systems would suffer from more dropped calls, corrupted messages, unstable internet sessions, and unreliable service quality.
CRC in Aviation Systems
Aircraft systems require extremely high reliability because errors can directly affect safety. Navigation systems, flight controls, onboard communication, and monitoring equipment all depend on accurate digital information.
CRC helps verify commands and sensor data exchanged between aircraft systems. If a signal becomes corrupted, CRC can detect it before the incorrect data influences flight operations.
For example, navigation instructions, altitude readings, and engine monitoring systems all rely on dependable communication. CRC supports these processes by helping ensure transmitted information remains correct.
Aircraft maintenance systems also use CRC when transferring diagnostic reports and software updates. This helps prevent corrupted updates from affecting system stability.
Because aviation environments demand precision and safety, CRC is a trusted part of the data validation process.
CRC in Military Communication
Military communication systems often operate in difficult and high-risk environments where signal interference, long-distance transmission, and harsh conditions are common. Accurate communication is essential for mission success and personnel safety.
CRC helps protect transmitted data such as commands, location updates, surveillance information, and encrypted communication channels. If a message becomes corrupted, CRC helps identify the problem before the information is acted upon.
In battlefield communication systems, drones, radar systems, and defense networks, fast error detection is critical because delays or incorrect instructions can have serious consequences.
Although military systems also use advanced encryption and security layers, CRC remains valuable for detecting accidental data corruption caused by environmental factors or hardware limitations.
Its efficiency makes it suitable for both portable field equipment and large defense infrastructure.
CRC in Robotics
Robotic systems rely heavily on precise communication between sensors, controllers, motors, and processing units. CRC helps ensure that instructions and feedback signals remain accurate during these exchanges.
In manufacturing robots, incorrect movement commands could damage products or create safety risks. CRC helps prevent this by validating control data before execution.
Autonomous robots such as delivery robots, warehouse systems, and service machines also depend on sensor accuracy. CRC helps verify navigation data, obstacle detection signals, and remote commands.
Medical robots and surgical systems require even higher reliability, where a single transmission error could be dangerous. CRC supports safe operation by reducing the risk of corrupted instructions.
As robotics becomes more advanced in both industry and daily life, CRC remains an important part of maintaining dependable machine communication.
CRC in Smart Grid Systems
Smart grids are modern electricity management systems that use digital communication to monitor and control power generation, transmission, and distribution. These systems connect power plants, substations, smart meters, and energy monitoring devices.
CRC helps protect communication between these components by detecting corrupted data before incorrect control actions are taken. For example, if a smart meter sends inaccurate usage information because of transmission errors, billing and energy management could be affected.
Power grid systems also use automated controls for balancing supply and demand. CRC helps ensure these control signals remain accurate and dependable.
Because electrical environments often contain strong electromagnetic interference, robust error detection is necessary. CRC provides reliable protection without adding major processing overhead.
In critical infrastructure like national power systems, dependable communication is essential, and CRC plays an important supporting role.
CRC in E-commerce Platforms
E-commerce platforms handle product listings, payments, customer accounts, shipping information, and order processing. Behind the scenes, large amounts of data move between databases, payment gateways, warehouses, and delivery systems.
CRC helps ensure this data remains accurate during storage and transmission. For example, if order details become corrupted during processing, it could result in wrong shipments, payment issues, or customer dissatisfaction.
File transfers between inventory systems and logistics platforms also benefit from CRC verification. This helps reduce operational mistakes caused by accidental data corruption.
Product images, invoices, downloadable digital products, and transaction records may all use CRC-based checks during storage and transfer.
Although customers rarely see it directly, CRC contributes to the reliability and consistency of modern online shopping systems.
CRC in Video Streaming and Media Transfer
Streaming platforms for video, music, and live broadcasting depend on fast and accurate data delivery. Corrupted packets can cause buffering, audio distortion, video glitches, or playback failures.
CRC helps detect damaged packets during transmission so systems can request retransmission or apply correction methods before the problem affects the user experience.
Video conferencing platforms also rely on CRC to maintain stable calls and prevent broken communication during meetings, remote learning, and online collaboration.
Media production systems that transfer large video files between editing workstations and storage servers use CRC to verify file integrity after copying or backup.
Because media files are often very large, even small errors can cause major playback problems. CRC helps reduce these risks and supports smoother content delivery.
CRC in Gaming Systems
Online gaming depends on real-time communication between players, servers, and game engines. Small transmission errors can cause lag, broken gameplay, incorrect player actions, or server instability.
CRC helps verify data packets such as player movements, match updates, game state synchronization, and downloadable content. If corruption is detected, systems can correct the issue before gameplay is affected.
Game installation files and updates also use CRC checks to ensure downloads are complete and uncorrupted. This prevents crashes caused by damaged files or incomplete patches.
Gaming consoles, cloud gaming platforms, and multiplayer servers all benefit from CRC because they require both speed and reliability.
In competitive gaming environments, accurate communication is especially important because even small delays or errors can affect fairness and performance.
CRC in Education Technology Systems
Online learning platforms, examination systems, student databases, and digital classrooms depend on accurate data exchange. CRC helps protect educational content and records from corruption during transfer and storage.
For example, assignment uploads, examination submissions, video lectures, and grading systems all involve file movement across networks. CRC helps ensure these files arrive correctly and remain unchanged.
Student records stored in school databases also benefit from integrity verification, reducing the risk of accidental corruption caused by hardware faults or transfer errors.
Remote learning systems that use live video and messaging platforms rely on CRC to support stable communication and content delivery.
As education becomes increasingly digital, dependable error detection helps protect both learning materials and administrative systems.
CRC in Scientific Research Systems
Scientific research often depends on large volumes of sensitive data collected from experiments, simulations, sensors, and laboratories. Corrupted information can lead to incorrect conclusions, wasted resources, or failed projects.
CRC helps verify research data during storage, transfer, and backup processes. Laboratory instruments, simulation platforms, and scientific databases use CRC to confirm that collected information remains accurate.
Space research, weather monitoring, environmental analysis, and medical research all rely heavily on dependable data handling. CRC helps support this reliability by detecting accidental corruption before analysis begins.
Large datasets shared between institutions also benefit from CRC checks during transfer, ensuring researchers work with correct and complete information.
In research environments where accuracy is essential, CRC quietly supports trust in the scientific process.
Future of CRC in Modern Technology
As digital systems continue to expand, CRC will remain an important part of data reliability. New technologies such as autonomous vehicles, edge computing, advanced robotics, smart healthcare, and large-scale artificial intelligence systems all depend on trustworthy communication.
Even as stronger security tools and more advanced correction methods develop, CRC continues to offer a fast and efficient way to detect accidental errors at the first stage.
Future systems may combine CRC with artificial intelligence-based monitoring, stronger storage validation, and more advanced network protocols to create even higher reliability standards.
Because CRC is simple, efficient, and proven across decades of use, it is likely to remain a core technology in both traditional systems and next-generation infrastructure.
Its role may not always be visible to users, but it continues to protect the digital world by helping ensure that data arrives exactly as intended.
Conclusion
Cyclic Redundancy Check is one of the most reliable and widely used methods for detecting errors in digital communication and storage systems. It helps ensure that data remains accurate when it is transmitted between devices or stored for future use. By using mathematical polynomial division and checksum verification, CRC can quickly identify corruption caused by noise, interference, hardware faults, or transmission failures.
From Ethernet networks and wireless communication to hard drives, medical devices, banking systems, cloud computing, and industrial automation, CRC plays a critical role in maintaining data integrity across nearly every modern technology sector. Its ability to detect single-bit errors, burst errors, and multiple data corruption patterns makes it far more effective than simpler methods like parity checks and basic checksums.
Although CRC does not correct errors or provide security against intentional attacks, it remains highly valuable for detecting accidental data corruption with speed and efficiency. Its low computational cost, strong detection capability, and compatibility with both simple and advanced systems make it an essential part of reliable digital operations.
As technology continues to grow and systems become more connected, the importance of accurate and dependable data transmission will only increase. CRC will continue to serve as a trusted foundation for protecting information and supporting the performance, stability, and reliability of digital communication around the world.