In modern cybersecurity, protecting networks from unauthorized access and malicious activity is a top priority for organizations of all sizes. As cyber threats continue to evolve, businesses rely on advanced security tools to monitor, detect, and prevent attacks before they cause serious damage. Two of the most commonly used security technologies in this area are Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS).
These tools play a crucial role in strengthening network defense by continuously analyzing traffic and identifying suspicious behavior. They help security teams gain better visibility into potential threats and respond more effectively to incidents. IDS and IPS systems are often integrated into broader security frameworks, working alongside firewalls, antivirus solutions, and other monitoring tools. Together, they create a layered security approach that improves an organization’s ability to defend against both external attackers and internal misuse, reducing overall risk and improving incident response capabilities across the entire network environment.
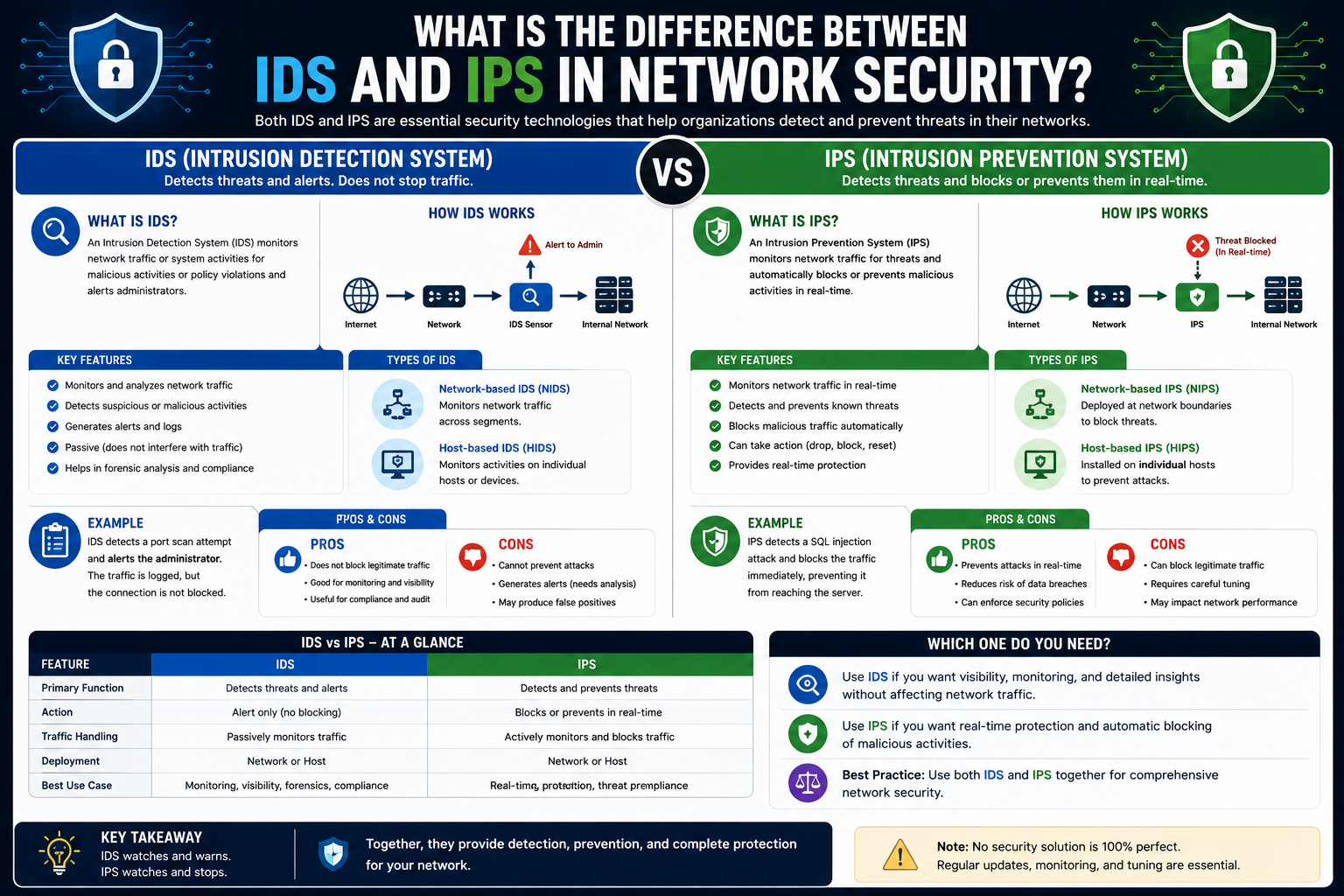
While both are designed to identify suspicious activity within a network, they operate in different ways and serve slightly different purposes. Understanding how they work, where they are used, and what sets them apart is essential for building a strong network security strategy.
What is an Intrusion Detection System (IDS)?
An Intrusion Detection System, commonly known as IDS, is a security tool that monitors network traffic for signs of malicious activity or policy violations. Its primary role is to detect and alert administrators when something suspicious occurs.
An IDS works by analyzing copies of network traffic rather than interacting directly with the live data flow. This means it operates outside the main traffic path, often referred to as being “out-of-line.” Because of this setup, it does not interfere with the actual transmission of data.
When an IDS identifies suspicious behavior—such as unusual traffic patterns, known attack signatures, or policy breaches—it generates alerts for network administrators. These alerts allow security teams to investigate and respond manually.
However, one important limitation of an IDS is that it cannot actively block or stop malicious traffic. Its function is strictly detection and reporting, not prevention. This makes it valuable for monitoring and visibility but not sufficient as a standalone defense mechanism.
What is an Intrusion Prevention System (IPS)?
An Intrusion Prevention System, or IPS, goes a step beyond detection by actively blocking or preventing malicious activity in real time. Unlike IDS, an IPS is placed directly in the flow of network traffic, meaning all data must pass through it before reaching its destination.
This inline position allows it to inspect every packet as it moves across the network and immediately take action when threats are identified. If suspicious or harmful behavior is detected, the IPS can drop the traffic, block the source IP address, or reset the connection to stop the attack from continuing. This makes it highly effective against fast-moving threats such as malware, exploits, and denial-of-service attacks. Because it works automatically, an IPS reduces the need for manual intervention and helps organizations respond to security incidents much faster while maintaining stronger overall protection of critical network resources.
Because it operates “in-line,” an IPS can inspect traffic as it happens and take immediate action if it detects a threat. This action may include dropping malicious packets, blocking connections, or resetting sessions to stop an attack from continuing.
The key advantage of an IPS is its ability to respond instantly. Instead of waiting for an administrator to react, it can automatically prevent threats from reaching internal systems. This makes it highly effective for reducing the impact of fast-moving cyberattacks such as malware propagation, denial-of-service attempts, and exploit-based intrusions.
Key Differences Between IDS and IPS
Although IDS and IPS share similar detection capabilities, the main difference lies in how they handle network traffic and respond to threats.
An IDS is passive. It monitors traffic by analyzing copies of data and alerts administrators when suspicious activity is detected. It does not interfere with network communication.
An IPS is active. It sits directly in the traffic path and can block or prevent malicious activity in real time before it reaches its target.
Another important distinction is their impact on network performance and risk. Since IDS does not sit in-line, it has minimal effect on network speed and carries no risk of blocking legitimate traffic. IPS, however, must carefully inspect every packet in real time, which can introduce performance overhead and carries a small risk of false positives disrupting normal traffic.
In simple terms, IDS is focused on visibility, while IPS is focused on control and protection.
How IDS and IPS Are Positioned in a Network
The placement of IDS and IPS within a network is one of the most important differences between them.
An IDS is usually placed off to the side of the main network path. It receives mirrored or copied traffic from network devices such as switches or routers. This setup allows it to analyze all activity without affecting the flow of communication.
An IPS, on the other hand, is placed directly between network devices. All incoming and outgoing traffic must pass through it. This positioning allows it to inspect and filter traffic in real time but also means it becomes a critical point in the network’s operation.
Because of this difference in placement, IDS is often used for monitoring and analysis, while IPS is used for active enforcement of security policies.
Host-Based vs Network-Based IDS and IPS
IDS and IPS solutions can also be categorized based on where they are deployed: on individual devices or across the network.
A network-based IDS or IPS monitors traffic traveling across the entire network. It is typically installed at strategic points such as gateways or core switches. This allows it to observe traffic between multiple devices and identify large-scale attacks or suspicious behavior affecting the network as a whole.
A host-based IDS or IPS is installed directly on individual devices such as servers, workstations, or endpoints. Instead of analyzing network traffic alone, it monitors system-level activity, including application behavior, file access, system logs, and operating system changes.
Host-based solutions provide deeper visibility into what is happening on a specific device, making them effective for detecting insider threats or attacks that originate locally. However, they require installation and maintenance on each device, which increases cost and management overhead.
Network-based solutions, on the other hand, provide broader coverage but may not detect issues occurring within a single device.
How IDS and IPS Detect Threats
Both IDS and IPS use similar techniques to identify malicious activity. The two most common methods are signature-based detection and anomaly-based detection.
Signature-based detection relies on a database of known attack patterns. These signatures act like fingerprints of previously identified threats. When network traffic matches a known signature, the system recognizes it as malicious and triggers an alert or blocks it, depending on whether it is IDS or IPS.
Anomaly-based detection works differently. Instead of looking for known patterns, it establishes a baseline of normal network behavior. This baseline may include typical traffic volumes, connection rates, or protocol usage.
If the system detects activity that significantly deviates from this normal behavior, it flags it as suspicious. For example, a sudden spike in connection requests or unusual protocol usage could indicate an attack in progress.
While anomaly detection is powerful for identifying unknown threats, it can sometimes produce false positives, requiring careful tuning by security teams.
Which One is Better: IDS or IPS?
Neither IDS nor IPS is universally better than the other. Each serves a different purpose and is often used together as part of a layered security strategy.
IDS is ideal for environments where monitoring and visibility are the primary goals. It allows security teams to analyze traffic patterns, investigate incidents, and improve long-term security planning without interfering with network performance.
IPS is better suited for environments that require real-time protection and automated response. It helps stop attacks immediately, reducing the window of opportunity for attackers.
In most modern networks, both systems are used together. IDS provides detailed insight and analysis, while IPS delivers active defense.
Advantages and Limitations
IDS offers strong visibility with minimal impact on network performance. However, its inability to block threats means it relies on human response, which can delay mitigation.
IPS provides immediate protection but requires careful configuration to avoid blocking legitimate traffic. It also introduces additional processing overhead since it must inspect all traffic in real time.
Choosing between them depends on the organization’s security needs, infrastructure size, and risk tolerance.
Conclusion
Intrusion Detection Systems and Intrusion Prevention Systems are both essential components of modern cybersecurity strategies. While they share similar detection capabilities, their roles are fundamentally different. IDS focuses on identifying and reporting threats, offering visibility without intervention. IPS goes further by actively blocking malicious activity in real time.
In most secure network environments, these technologies are not used in isolation. Instead, they complement each other, creating a layered defense system that improves both detection and response. By understanding how IDS and IPS work—and where each fits into a security architecture—organizations can build stronger defenses against the growing range of cyber threats targeting their networks.