Network Address Translation (NAT) is one of the most important mechanisms used in modern computer networking. It allows private networks to communicate with external networks such as the internet by translating private IP addresses into a public IP address. This process is essential for conserving limited IP address space and ensuring secure and efficient communication between devices.
NAT is commonly implemented in routers, firewalls, and gateway devices. It operates silently in the background, meaning users typically do not notice its functioning while browsing the internet, streaming content, or using online applications. Despite being invisible to end users, NAT plays a critical role in maintaining global internet connectivity.
Understanding the Concept of IP Addressing
To understand NAT clearly, it is important to first understand IP addressing. Every device connected to a network is assigned an IP address, which acts as its unique identifier. These addresses can either be private or public. Private IP addresses are used within local networks such as homes, offices, or organizations, while public IP addresses are used to communicate over the internet.
The problem arises because the number of available IPv4 addresses is limited, while the number of internet-connected devices is continuously increasing. NAT solves this issue by allowing multiple devices within a private network to share a single public IP address.
What NAT Actually Does
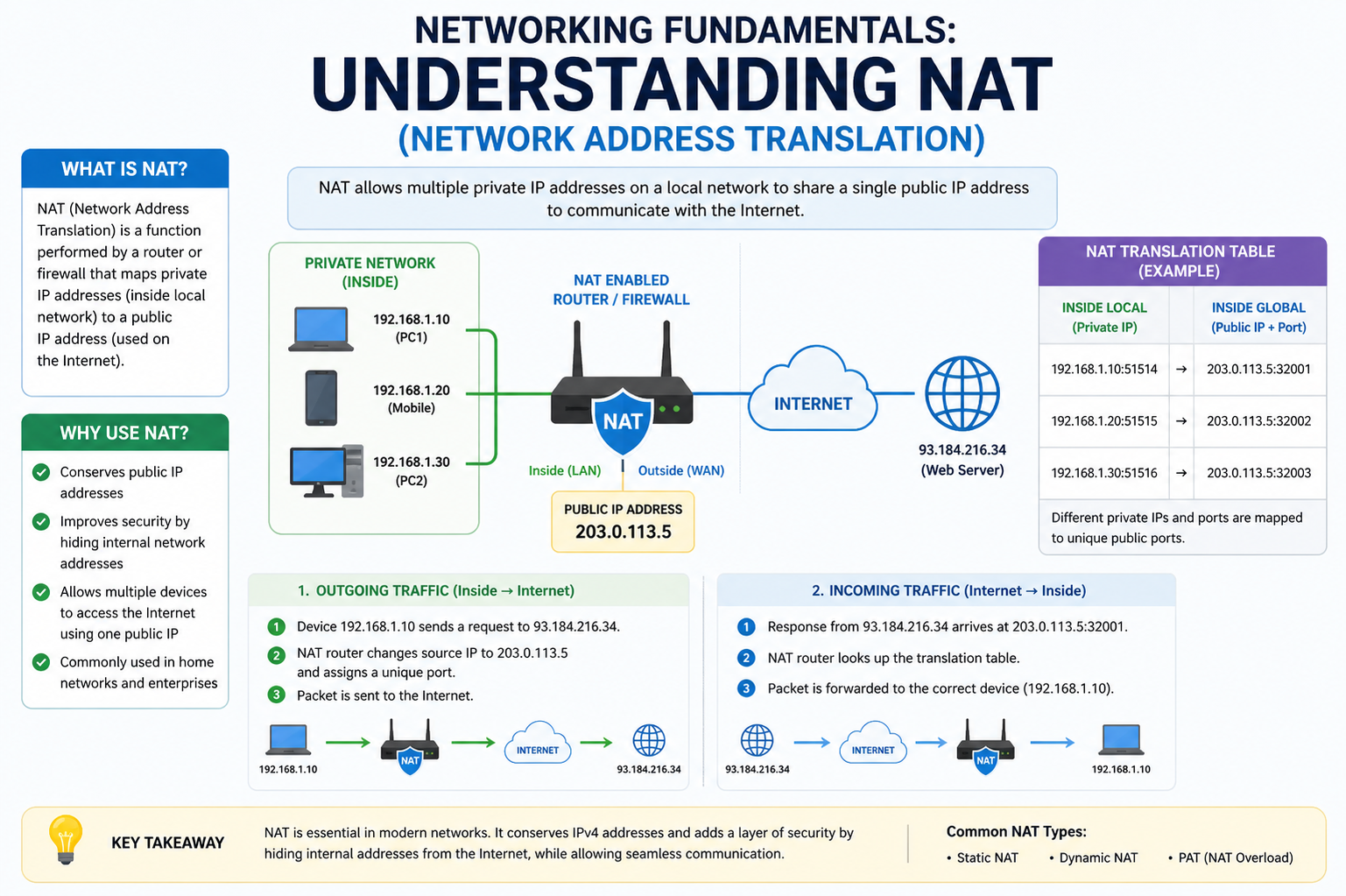
NAT works by modifying network packet information as it passes through a routing device. When a device inside a private network sends a request to the internet, NAT changes the source IP address from a private one to a public one. When the response returns from the internet, NAT reverses the process and forwards the data to the correct internal device.
This translation process happens in real time and is managed through a NAT table maintained by the router. The table keeps track of active connections and ensures that incoming responses are delivered to the correct destination inside the private network.
How NAT Works in a Network Environment
When a device such as a laptop or smartphone sends a request to access a website, the request first goes to the router. The router replaces the private IP address of the device with its own public IP address before sending the request to the internet. The destination server sees the request as coming from the router’s public IP.
Once the server responds, the data is sent back to the router’s public IP address. The router then checks its NAT table to determine which internal device initiated the request and forwards the response accordingly. This entire process happens instantly, ensuring seamless communication.
NAT Table and Its Role
The NAT table is a key component in the functioning of NAT. It stores information about active sessions, including internal IP addresses, external IP addresses, and port numbers. Each time a device initiates a connection, a new entry is created in the table.
This mapping allows the router to correctly track multiple simultaneous connections. Without the NAT table, it would be impossible to differentiate between different devices using the same public IP address.
Types of NAT in Networking
There are several types of NAT used in different networking scenarios, each serving a specific purpose.
Static NAT involves a one-to-one mapping between a private IP address and a public IP address. This means a specific device always uses the same public IP address when communicating externally. It is commonly used for servers that need consistent external access.
Dynamic NAT assigns a public IP address from a pool of available addresses whenever a device requests internet access. The mapping is temporary and changes once the session ends.
Port Address Translation (PAT), also known as NAT overload, is the most widely used form of NAT. It allows multiple devices to share a single public IP address by using different port numbers to distinguish between connections. This is highly efficient and is commonly used in home and office networks.
Port Address Translation in Detail
Port Address Translation works by modifying not only the IP address but also the port number of outgoing packets. Each device is assigned a unique port combination, allowing the router to manage multiple connections simultaneously using a single public IP.
For example, if two devices request data from the internet at the same time, PAT ensures that each request is tracked separately using different port numbers. When responses arrive, PAT uses these port numbers to send data back to the correct device.
Private and Public Network Interaction
NAT acts as a bridge between private and public networks. Private networks are typically isolated and use reserved IP address ranges. These addresses are not routable on the internet. NAT enables devices using these private addresses to access online resources without directly exposing them to external networks.
This separation improves security and reduces the risk of direct external attacks on internal devices.
Security Benefits of NAT
One of the major advantages of NAT is improved network security. Since internal IP addresses are hidden from external networks, attackers cannot directly target individual devices within a private network. Only the public IP address of the router is visible, adding a layer of protection.
However, it is important to note that NAT is not a complete security solution. It should be used in combination with firewalls and other security mechanisms for stronger protection.
IPv4 Address Exhaustion Problem
The development of NAT was largely driven by the shortage of IPv4 addresses. IPv4 provides approximately 4.3 billion unique addresses, which is insufficient for the growing number of devices connected to the internet.
NAT helps extend the usability of IPv4 by allowing multiple devices to share a single public IP address. This has significantly delayed the exhaustion of IPv4 address space and allowed continued expansion of the internet.
Relation Between NAT and IPv6
IPv6 was introduced to solve the IP address shortage problem permanently by providing a vastly larger address space. With IPv6, each device can have a unique global IP address, reducing the need for NAT.
However, NAT is still widely used in IPv4 networks, and many systems continue to rely on it. Even in environments transitioning to IPv6, NAT-like mechanisms may still be used for compatibility and network management purposes.
Carrier-Grade NAT (CGNAT)
Carrier-Grade NAT is a large-scale version of NAT used by internet service providers. It allows multiple customers to share a limited number of public IP addresses. Instead of just one home network using NAT, CGNAT operates at the service provider level.
While CGNAT helps conserve IP addresses, it can sometimes introduce limitations such as difficulty in hosting servers or reduced performance for certain applications.
Advantages of NAT
NAT provides several important benefits. It conserves public IP addresses by enabling multiple devices to share a single address. It improves security by hiding internal network structures. It also allows flexible network management and simplifies IP addressing within private networks.
Additionally, NAT makes it easier for organizations to manage internal networks without requiring large blocks of public IP addresses.
Limitations of NAT
Despite its advantages, NAT also has some limitations. It can introduce complexity in network troubleshooting because tracking individual connections becomes more difficult. Certain applications such as peer-to-peer services and online gaming may experience connectivity issues due to NAT restrictions.
NAT can also add slight processing overhead because every packet must be translated, although modern hardware minimizes this impact.
NAT Traversal Challenges
Some applications require direct device-to-device communication, which can be challenging when NAT is involved. NAT traversal techniques are used to overcome these challenges and allow devices behind NAT to communicate directly.
These techniques are commonly used in video calls, online gaming, and real-time communication applications.
Real-World Applications of NAT
NAT is used in almost every modern network environment. Home routers use NAT to allow multiple devices to access the internet through a single connection. Businesses use NAT to manage large internal networks securely. Internet service providers use CGNAT to handle large numbers of customers efficiently.
Without NAT, it would be extremely difficult to manage current internet infrastructure with limited IPv4 addresses.
Advanced Working of NAT in Modern Networks
NAT is not just a simple translation mechanism; in modern networking environments, it performs complex state tracking and intelligent mapping of connections. When multiple devices inside a private network access the internet simultaneously, NAT maintains a dynamic record of every session. This includes source IP, destination IP, port numbers, and protocol type.
Each entry in the NAT table is temporary and exists only for the duration of the active communication. Once the session ends or times out, the entry is removed automatically. This ensures efficient memory usage in networking devices and prevents unnecessary overload.
Modern routers also optimize NAT behavior by grouping similar traffic patterns and prioritizing active sessions. This helps maintain performance even when hundreds or thousands of devices are connected at the same time.
Deep Understanding of Port Address Translation (PAT)
Port Address Translation is the most widely deployed form of NAT in real-world networks. Its efficiency comes from the ability to distinguish connections not just by IP address but also by port numbers.
When a device sends a request to the internet, PAT assigns a unique combination of public IP and port number. Even if multiple devices are accessing the same website or service, PAT ensures that each session is uniquely identifiable.
This mechanism allows thousands of devices to share a single public IP address without conflicts. The router internally modifies packet headers, tracks port mappings, and ensures that responses are delivered accurately to the correct internal device.
PAT is especially important in residential networks where internet service providers assign only one public IP to an entire household.
NAT and Connection Tracking Mechanism
Connection tracking is the backbone of NAT functionality. Every time a device initiates communication, the router creates a session entry. This entry contains detailed metadata about the connection, including timing information and protocol state.
This tracking allows NAT to understand whether incoming traffic is part of an existing session or a new request. If it matches an existing entry, the router forwards the packet accordingly. If not, it may drop the packet for security reasons.
This mechanism is also why NAT contributes to security. Unauthorized or unexpected incoming traffic is often blocked because it does not match any existing session entry.
NAT Traversal and Communication Challenges
Despite its advantages, NAT introduces challenges for applications that require direct peer-to-peer communication. Devices behind different NATs cannot easily establish direct connections because their private IP addresses are not visible externally.
To solve this, NAT traversal techniques are used. These methods help devices discover each other and establish communication paths even when both are behind NAT systems.
Common NAT traversal techniques include hole punching, relay servers, and session negotiation protocols. These methods are widely used in real-time communication applications such as video conferencing and online gaming.
Double NAT Problem in Networks
Double NAT occurs when a network connection passes through two layers of NAT devices. This usually happens when a router is connected to another router that is already performing NAT.
In such cases, packets must be translated twice before reaching the internet, which can create complications. These complications may include slower performance, difficulty in port forwarding, and connectivity issues in certain applications.
Double NAT is often unintentional and can be resolved by adjusting router configurations or using bridge mode on one of the devices.
NAT and Port Forwarding Relationship
Port forwarding is a configuration technique used alongside NAT to allow external devices to access specific services inside a private network. While NAT normally blocks unsolicited incoming traffic, port forwarding creates exceptions.
When port forwarding is configured, the router is instructed to send incoming traffic on a specific port directly to a designated internal device. This is commonly used for hosting game servers, web servers, or remote access services.
Port forwarding must be carefully managed because incorrect configurations can expose internal devices to external threats.
NAT Types in Online Connectivity Systems
In many systems, especially gaming and real-time applications, NAT behavior is categorized into different types based on restrictions.
A strict NAT type allows limited connectivity and often blocks peer-to-peer communication. A moderate NAT type allows some connections but may still restrict certain interactions. An open NAT type provides the most flexible connectivity and allows seamless communication between devices.
These classifications are not separate technologies but rather behavioral outcomes of how NAT and firewall rules are configured in a network.
NAT and Firewall Interaction
NAT and firewalls often work together in modern networking devices. While NAT handles address translation, firewalls control access rules and security policies.
A firewall inspects incoming and outgoing traffic based on predefined rules. When combined with NAT, it ensures that only legitimate traffic is allowed into the internal network.
This dual-layer protection significantly improves network security by preventing unauthorized access while still enabling controlled external communication.
Performance Impact of NAT
Although NAT is highly efficient, it still introduces a small amount of processing overhead. Every packet passing through a NAT-enabled device must be inspected, modified, and recorded in the NAT table.
In high-traffic environments, such as enterprise networks or service providers, this can lead to performance bottlenecks if hardware is not optimized.
To address this, modern routers and firewalls use hardware acceleration and specialized processors to handle NAT operations efficiently.
NAT in Enterprise Networks
In large organizations, NAT is used to manage complex internal network structures. Multiple departments may use overlapping private IP address ranges, and NAT helps unify external communication through controlled public IPs.
Enterprises often use multiple layers of NAT along with advanced routing policies to segment traffic, improve security, and manage bandwidth usage effectively.
In such environments, NAT is often combined with load balancing systems and redundancy mechanisms to ensure continuous availability.
NAT Logging and Monitoring
Network administrators often rely on NAT logs to analyze traffic behavior and troubleshoot connectivity issues. These logs contain detailed records of translations, including timestamps, IP mappings, and port usage.
By analyzing NAT logs, administrators can identify unusual traffic patterns, detect security threats, and optimize network performance.
However, NAT logging can generate large amounts of data, especially in high-traffic networks, so efficient storage and filtering mechanisms are necessary.
NAT and VPN Interaction
Virtual Private Networks (VPNs) often interact closely with NAT systems. When a VPN is active, it creates an encrypted tunnel between the user and the VPN server. NAT then operates on this encrypted traffic just like any other network traffic.
In some cases, NAT can interfere with VPN performance if not properly configured. This is why many VPN protocols are designed to be NAT-friendly and can pass through NAT devices without disruption.
Application-Level Issues Caused by NAT
Certain applications rely on direct IP communication and can face issues when NAT is present. These include VoIP services, multiplayer games, and file-sharing applications.
To overcome this, many modern applications are designed with NAT-aware protocols that automatically adjust connection methods based on network conditions.
Some applications also use relay servers to bypass NAT restrictions, ensuring stable communication even in restrictive network environments.
Security Misconceptions About NAT
A common misconception is that NAT alone provides complete network security. While NAT does hide internal IP addresses, it does not inspect packet content or prevent all types of attacks.
True network security requires a combination of NAT, firewalls, intrusion detection systems, and secure authentication mechanisms.
Relying solely on NAT for security can lead to a false sense of protection and expose networks to vulnerabilities.
Future of NAT in Evolving Internet Architecture
With the gradual adoption of IPv6, the dependency on NAT is expected to decrease over time. IPv6 provides a vast address space that eliminates the need for address translation in most cases.
However, NAT will continue to exist for many years due to legacy systems, compatibility requirements, and established infrastructure. Many hybrid networks already use both IPv4 with NAT and IPv6 simultaneously.
This transitional phase ensures that NAT remains relevant even as internet technologies evolve.
NAT continues to be a fundamental component of modern networking, enabling efficient use of IP addresses and providing an additional layer of network protection. Its advanced behaviors, including connection tracking, port translation, and integration with firewalls, make it a powerful tool in both small and large-scale networks.
Although newer technologies like IPv6 are gradually reducing its necessity, NAT remains deeply embedded in global internet infrastructure. Understanding its working, limitations, and real-world applications is essential for anyone studying or working in networking environments.
NAT in Internet Service Provider Networks
Internet Service Providers (ISPs) rely heavily on NAT to manage large-scale user connectivity. Since ISPs serve thousands or even millions of customers, assigning a unique public IP address to each user is not practical due to IPv4 limitations. NAT allows ISPs to group many users under a smaller pool of public IP addresses, making internet distribution more efficient.
In ISP environments, NAT is often implemented at carrier level, where multiple layers of translation may exist. This ensures that even with limited IPv4 resources, users can still access the internet without interruption. However, this also means that users often share public IPs with many others, which can affect certain online services that rely on unique IP identification.
Understanding Carrier-Grade NAT in Detail
Carrier-Grade NAT is an advanced form of NAT used by service providers on a massive scale. Instead of managing NAT at the home router level, CGNAT operates within the ISP infrastructure. It translates private IP addresses from thousands of customers into a smaller set of public IP addresses.
This system helps extend the life of IPv4 significantly, but it introduces additional complexity. Since many users share the same public IP, tracking individual connections becomes more difficult. This can sometimes cause issues with online authentication systems, security verification, and hosting services.
Despite its limitations, CGNAT remains widely used because it is a practical solution to global IP address shortages.
Impact of NAT on Online Gaming and Real-Time Applications
Online gaming is one of the most NAT-sensitive applications. Many multiplayer games require direct communication between players, which can be restricted by NAT configurations. If NAT is strict, players may experience difficulty joining matches, hosting games, or connecting with others.
Game developers often design their systems to handle NAT limitations by using matchmaking servers and relay systems. These servers act as intermediaries, allowing players behind different NATs to communicate indirectly.
Voice chat and streaming applications also rely on NAT traversal techniques to maintain smooth real-time communication without interruptions.
NAT and Cloud Computing Environments
In cloud computing, NAT plays a significant role in managing virtual networks. Cloud providers use NAT to allow virtual machines with private IP addresses to access the internet securely.
This approach ensures that internal cloud resources remain isolated from direct external access while still being able to communicate with external services. NAT also helps in managing large-scale cloud infrastructure efficiently by reducing the need for public IP allocation.
Cloud environments often use advanced NAT configurations combined with load balancers and virtual firewalls to maintain performance and security.
Role of NAT in Virtual Private Networks (VPNs)
VPNs and NAT often work together in modern networks. When a VPN is activated, it creates a secure tunnel between the user and the VPN server. NAT then processes this encrypted traffic as it passes through routers and gateways.
In some cases, NAT can interfere with VPN connections if both systems are not properly configured. This is why modern VPN protocols are designed to be NAT-compatible, ensuring smooth connectivity even in restrictive network environments.
NAT also helps VPN services by allowing multiple users to share a limited number of public IP addresses while maintaining encrypted communication.
NAT Behavior in Mobile Networks
Mobile networks use NAT extensively due to the large number of users and limited IPv4 resources. Mobile carriers often implement NAT at multiple levels, including base stations and core network infrastructure.
When a mobile device connects to the internet, it is usually assigned a private IP address internally. NAT then translates this address to a public IP before accessing external services.
This system allows millions of mobile users to stay connected simultaneously without requiring an equal number of public IP addresses.
Security Implications of NAT in Mobile Environments
In mobile networks, NAT adds an additional layer of security by hiding user devices behind shared public IPs. This makes it harder for attackers to directly target individual mobile devices.
However, just like in other environments, NAT alone is not enough for full protection. Mobile networks also rely on encryption, authentication systems, and firewalls to ensure secure communication.
NAT and Internet of Things (IoT) Devices
The Internet of Things introduces a massive number of connected devices, many of which operate within private networks. NAT plays a key role in managing communication between IoT devices and external systems.
Most IoT devices are assigned private IP addresses within a local network. NAT allows these devices to send data to cloud services or remote servers without exposing their internal network structure.
This is especially important in smart homes, industrial automation, and healthcare systems where security and controlled access are critical.
Challenges of NAT in IoT Ecosystems
While NAT helps manage IoT connectivity, it also introduces challenges. Some IoT devices require direct external access for monitoring or control, which can be restricted by NAT configurations.
To overcome this, IoT systems often use cloud-based intermediaries or secure tunneling protocols. These methods allow devices to communicate externally without breaking NAT restrictions.
NAT and Network Scalability
One of the key reasons NAT is widely used is its ability to support network scalability. Without NAT, every device would require a unique public IP address, which is not feasible in large-scale networks.
NAT allows networks to grow freely without worrying about IP exhaustion. Whether in homes, businesses, or global service providers, NAT ensures that adding new devices does not require major changes in IP allocation.
This scalability is one of the main reasons NAT remains a fundamental part of networking architecture.
Troubleshooting NAT-Related Issues
Network troubleshooting involving NAT can be complex because multiple devices may share the same public IP address. Identifying which device caused a specific issue requires analyzing NAT tables and logs.
Common NAT-related problems include connection timeouts, failed port forwarding, and restricted access to services. These issues are often resolved by checking router configurations, restarting sessions, or adjusting NAT rules.
Network administrators rely on diagnostic tools to monitor NAT behavior and ensure smooth operation.
NAT and Load Balancing Systems
Load balancing systems often work alongside NAT to distribute network traffic efficiently. NAT helps hide internal server structures, while load balancers distribute incoming requests across multiple servers.
This combination improves performance, reliability, and availability of online services. It ensures that no single server becomes overloaded with traffic.
In large-scale applications such as websites and cloud services, NAT and load balancing work together to maintain stability under heavy usage.
Evolution of NAT in Modern Networking
Over time, NAT has evolved from a simple address translation method into a complex network management system. Early versions of NAT were basic, focusing only on IP replacement. Modern NAT systems include advanced features such as session tracking, security filtering, and performance optimization.
Today, NAT is deeply integrated into networking hardware and software, making it an essential component of global internet infrastructure.
Transition from IPv4 NAT to IPv6 Networking
As IPv6 adoption increases, the need for NAT is expected to decrease. IPv6 provides an almost unlimited number of IP addresses, eliminating the core reason for NAT usage.
However, the transition is gradual, and NAT will continue to exist for many years due to compatibility requirements. Many networks operate in dual-stack mode, supporting both IPv4 with NAT and IPv6 simultaneously.
This ensures smooth migration without disrupting existing services.
Future Role of NAT in Hybrid Networks
In the future, NAT will still play a role in hybrid networking environments where IPv4 and IPv6 coexist. It may also evolve to support more advanced translation and interoperability functions between different network protocols.
Even as technology advances, NAT’s core concept of managing address translation will remain relevant in certain networking scenarios.
NAT Behavior in High-Traffic Enterprise Environments
In large enterprise networks, NAT must handle extremely high volumes of simultaneous connections. Thousands of employees, servers, and applications may generate constant traffic that passes through NAT-enabled gateways. To manage this efficiently, enterprise-grade routers and firewalls are designed with high-performance hardware and optimized NAT engines.
These systems are capable of processing millions of translation entries while maintaining low latency. They also prioritize critical traffic, ensuring that business applications such as databases, communication tools, and cloud services remain responsive even under heavy load.
In such environments, NAT is often combined with advanced routing policies to control how traffic flows between internal departments and external networks.
NAT Session Lifetimes and Timeout Mechanisms
Every NAT entry has a limited lifespan known as a session timeout. If a connection remains inactive for a certain period, the NAT device automatically removes its entry from the table. This helps free up system resources and prevents the NAT table from becoming overloaded.
Different types of traffic may have different timeout values. For example, web browsing sessions may have shorter timeouts, while long-lived connections such as video streaming or file transfers may be given extended durations.
Proper management of session lifetimes is essential for maintaining network efficiency and avoiding unnecessary connection drops.
NAT and Protocol Compatibility Issues
Not all network protocols work smoothly with NAT by default. Some protocols embed IP address information directly inside packet payloads instead of only in headers. Since NAT modifies only header information, these embedded addresses can cause communication failures.
To solve this, special adaptation techniques or application-level gateways are used. These mechanisms inspect and modify packet contents to ensure compatibility with NAT translation.
Modern applications are increasingly designed to be NAT-friendly, reducing compatibility issues and improving connectivity across diverse networks.
Symmetric NAT and Its Strict Behavior
Symmetric NAT is one of the most restrictive forms of NAT. In this model, each outgoing connection from a private device is mapped to a unique external port and IP combination, and this mapping changes depending on the destination.
This strict behavior enhances security but creates challenges for peer-to-peer communication. Devices behind symmetric NAT often struggle to establish direct connections with each other because their mappings are highly dynamic.
This type of NAT is commonly found in enterprise networks and some mobile carrier environments where security is prioritized over direct connectivity.
Full Cone NAT and Open Connectivity Model
Full Cone NAT is the least restrictive type of NAT. Once an internal device is mapped to a public IP and port, any external host can send packets to that mapping.
This allows easy peer-to-peer communication and is often considered the most “open” NAT behavior. However, it is less secure because it allows external systems to send unsolicited traffic to internal devices once the mapping is known.
Due to security concerns, full cone NAT is rarely used in modern secure environments.
Restricted NAT and Controlled Access
Restricted NAT provides a balance between security and connectivity. In this model, external systems can only send responses if the internal device has previously communicated with them.
This ensures that unsolicited traffic is blocked while still allowing legitimate two-way communication. Many home routers use variations of restricted NAT to provide a safe and functional browsing experience.
NAT and DNS Interaction
Domain Name System (DNS) works closely with NAT in modern networks. When a user enters a domain name, DNS resolves it into an IP address. NAT then handles the translation of that IP communication within the internal network.
Although DNS and NAT operate independently, their interaction is essential for seamless internet browsing. DNS handles name resolution, while NAT manages address translation and routing.
Any misconfiguration between the two can lead to connectivity issues, slow responses, or failed requests.
Impact of NAT on Latency and Performance
While NAT is highly efficient, it does introduce a small amount of processing delay. Each packet must be inspected, modified, and matched against NAT tables before being forwarded.
In most cases, this delay is negligible and unnoticeable to users. However, in high-performance environments such as gaming servers or financial trading systems, even small delays can be significant.
To minimize latency, modern networking devices use hardware acceleration, parallel processing, and optimized algorithms for NAT handling.
NAT in Data Center Architectures
Data centers rely on NAT to manage internal server communication and external service exposure. Many servers operate using private IP addresses for internal communication while NAT handles external requests.
This separation improves security and simplifies internal network design. It also allows data centers to scale easily without exposing internal infrastructure directly to the internet.
Load balancers and reverse proxies are often used alongside NAT to distribute traffic efficiently and maintain system reliability.
NAT and Reverse NAT Concepts
Reverse NAT, also known as inbound NAT, refers to the process of translating external IP addresses into internal ones for incoming traffic. This is commonly used when external users need access to internal services such as websites or application servers.
Reverse NAT ensures that requests from the internet are directed to the correct internal system without exposing private IP structures.
This technique is essential for hosting services securely within private networks.
NAT and Microservices Architecture
In modern software systems, especially microservices architectures, NAT plays an indirect but important role. Services often run in isolated containers or virtual machines using private IPs.
NAT enables these services to communicate with external APIs, databases, and cloud resources without exposing internal network details.
This helps maintain modularity, security, and scalability in complex application environments.
NAT Logging for Security Analysis
NAT logs are valuable for security monitoring and forensic analysis. They record detailed information about network activity, including which internal devices accessed specific external services and at what time.
Security teams use this data to detect suspicious behavior, track unauthorized access attempts, and investigate network incidents.
However, due to the large volume of data generated, efficient log management systems are required to store and analyze NAT logs effectively.
NAT and Artificial Intelligence in Networking
Modern networking systems increasingly use artificial intelligence to optimize NAT performance. AI-driven systems can analyze traffic patterns, predict congestion, and dynamically adjust NAT configurations for better efficiency.
This allows networks to adapt in real time to changing traffic conditions, improving both performance and reliability.
AI can also help detect anomalies in NAT behavior, enhancing security by identifying potential threats early.
Security Limitations of NAT in Modern Threats
Although NAT provides a basic level of security by hiding internal IP addresses, modern cyber threats can still bypass these protections using advanced techniques.
Attackers may exploit application vulnerabilities, compromised endpoints, or misconfigured NAT rules to gain access to internal systems.
This highlights the importance of using NAT alongside comprehensive security frameworks rather than relying on it alone.
NAT in Hybrid Cloud and Multi-Cloud Systems
Hybrid and multi-cloud environments use NAT to manage communication between different cloud platforms and on-premises systems. Since these environments often involve multiple network layers, NAT ensures consistent address translation across all platforms.
This allows seamless integration between private data centers and public cloud services while maintaining security and control.
Future Optimization of NAT Systems
Future NAT systems are expected to become more intelligent and automated. With advancements in machine learning and network virtualization, NAT will likely evolve into adaptive systems that automatically optimize routing, translation, and security policies.
These systems will reduce manual configuration and improve overall network efficiency.
Conclusion
Network Address Translation (NAT) remains a foundational technology in modern networking, enabling efficient communication between private and public networks. It plays a crucial role in solving the limitations of IPv4 by allowing multiple devices to share a single public IP address, which helps conserve the limited pool of available addresses.
Beyond address conservation, NAT also enhances network security by hiding internal IP structures from external networks. This makes it more difficult for unauthorized users to directly target devices within a private network, adding an important protective layer to everyday internet communication.
NAT is widely used across homes, businesses, mobile networks, cloud systems, and large-scale internet service providers. Its flexibility allows it to support everything from simple browsing to complex enterprise-level data exchange. Even with the introduction of IPv6, which reduces the need for NAT, it continues to remain relevant due to existing IPv4 infrastructure and real-world deployment needs.
However, NAT is not without limitations. It can introduce complexity in troubleshooting, affect certain real-time applications, and require additional configurations for services like gaming, remote access, and peer-to-peer communication. Despite these challenges, continuous advancements in networking technologies have made NAT more efficient and reliable than ever.
Overall, NAT is an essential bridge in the networking world, ensuring smooth, secure, and scalable connectivity across billions of devices worldwide.