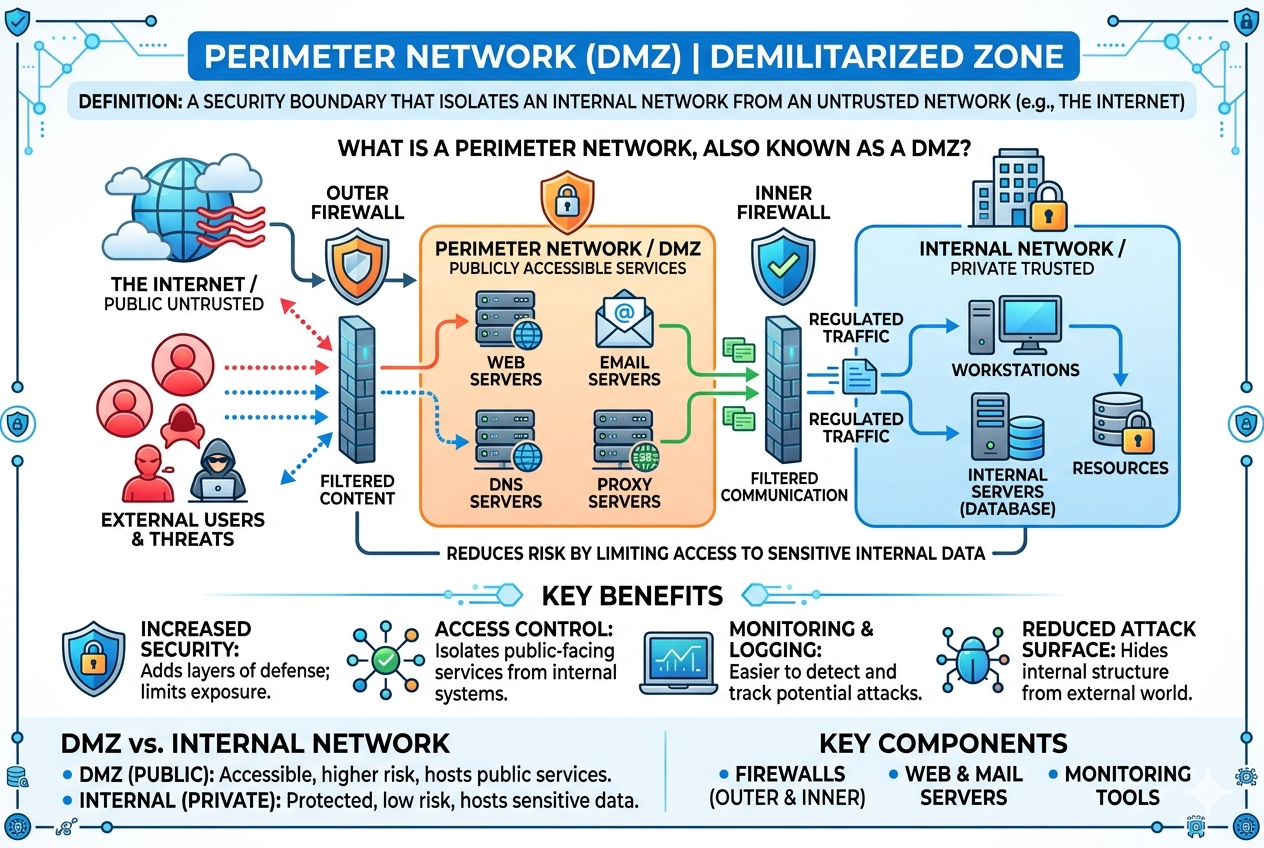
A perimeter network, commonly known as a DMZ (Demilitarized Zone), is a carefully designed segment of a computer network that serves as a secure buffer between an organization’s internal private systems and external untrusted networks. Its main role is to add an additional layer of protection by isolating systems that need to be accessible from outside users while keeping core internal resources shielded from direct exposure.
Core Idea Behind a DMZ
The fundamental idea of a DMZ is separation and controlled access. In a typical network environment, internal systems such as databases, internal applications, and sensitive business resources must remain protected from direct external access. At the same time, organizations often need to expose certain services to the public, such as websites, email gateways, or authentication portals. A DMZ solves this conflict by creating a middle zone where these exposed services can operate without granting direct access to the internal network.
This separation ensures that even if an attacker compromises a public-facing service, they still cannot directly reach critical internal systems without passing through additional security layers.
Position of the DMZ in Network Architecture
In a standard network architecture, the DMZ is placed between two security boundaries. One boundary connects to the external network, typically the internet, while the other connects to the internal private network. The DMZ sits in the middle as a controlled environment.
Traffic flowing from the internet is first directed to the DMZ, where public services are hosted. From there, only carefully filtered and monitored traffic is allowed to pass into the internal network. Similarly, internal systems may communicate with DMZ services, but such communication is also restricted and tightly controlled.
Purpose of Using a Perimeter Network
The primary purpose of implementing a DMZ is to reduce security risks while maintaining necessary external accessibility. Organizations that provide online services must expose certain systems to users, but exposing internal networks directly would create significant vulnerabilities. The DMZ minimizes this risk by acting as a protective buffer.
Another important purpose is containment. If a system in the DMZ is attacked or compromised, the damage can be contained within that zone. This prevents attackers from easily moving laterally into more sensitive areas of the network.
Common Systems Placed in a DMZ
A variety of services are typically hosted within a DMZ, depending on organizational needs. These include web servers that handle public websites, email servers that manage incoming and outgoing mail, proxy servers that mediate user requests, and authentication gateways that control secure access.
These systems are chosen specifically because they need to interact with external users or systems. However, they are configured in a way that limits their access to internal data and resources, ensuring that even if they are targeted, the exposure remains limited.
Security Mechanisms in a DMZ
Security in a perimeter network is enforced using multiple layers of protection. Firewalls play a central role by controlling traffic between the internet, DMZ, and internal network. Typically, at least two firewalls are used—one between the internet and the DMZ, and another between the DMZ and the internal network.
These firewalls are configured with strict rules that define what kind of traffic is allowed in each direction. Only necessary communication is permitted, while all other traffic is blocked by default.
In addition to firewalls, intrusion detection and prevention systems are often deployed to monitor suspicious activity. These systems analyze traffic patterns and can alert administrators or automatically block malicious behavior.
Isolation and Risk Reduction
One of the most important benefits of a DMZ is isolation. By separating public-facing services from internal systems, organizations significantly reduce their attack surface. Even if a hacker exploits a vulnerability in a web server, they are still confined within the DMZ and cannot easily reach internal databases or critical infrastructure.
This layered isolation model is a key principle of modern cybersecurity design. It assumes that breaches can happen, and therefore focuses on limiting the impact of those breaches.
Traffic Flow in a DMZ Setup
Traffic flow in a DMZ environment follows strict rules. When a request comes from an external user, it first reaches the outer firewall, which evaluates whether the request should be allowed into the DMZ. If permitted, the request is forwarded to the appropriate service within the DMZ.
If that service needs to access internal data, it must pass through the internal firewall, which applies additional filtering rules. This ensures that no direct or unrestricted communication exists between external networks and internal systems.
Similarly, when internal systems need to interact with DMZ services, the communication is also controlled and monitored.
Types of DMZ Architectures
There are different ways to design a DMZ depending on security requirements and infrastructure complexity. One common approach is the single firewall DMZ, where one firewall is used with multiple interfaces to separate networks logically. Another approach is the dual firewall DMZ, which uses two separate firewalls for stronger isolation.
The dual firewall approach is generally considered more secure because it creates multiple layers of defense. However, it is also more complex and requires careful configuration and management.
Advantages of a Perimeter Network
A DMZ provides several important advantages in network security. It enhances protection by limiting exposure of internal systems. It also improves monitoring and control of external traffic. Organizations can safely host public services without compromising sensitive internal data.
Another advantage is flexibility. Businesses can offer online services, remote access, and public applications while maintaining strong security boundaries. This balance between accessibility and protection is essential in modern digital environments.
Limitations and Challenges
Despite its benefits, a DMZ is not without limitations. One challenge is complexity. Properly configuring firewalls, access rules, and monitoring systems requires expertise. Misconfigurations can create vulnerabilities instead of eliminating them.
Another limitation is maintenance. A DMZ must be continuously monitored and updated to respond to new threats. If neglected, even a well-designed perimeter network can become vulnerable over time.
Additionally, while a DMZ reduces risk, it does not eliminate it entirely. Advanced attackers may still find ways to exploit weaknesses, especially if multiple layers of security are not properly maintained.
Role in Modern Cybersecurity Strategy
In modern cybersecurity, a DMZ is considered a foundational element of defense-in-depth strategy. Instead of relying on a single layer of protection, organizations use multiple overlapping security measures. The DMZ plays a key role in this approach by serving as the first line of controlled exposure.
It works alongside other security practices such as encryption, identity management, endpoint protection, and continuous monitoring. Together, these elements create a more resilient security posture.
DMZ in Cloud and Hybrid Environments
With the rise of cloud computing and hybrid infrastructures, the concept of a DMZ has evolved. Instead of physical network segments, virtual DMZs are now commonly implemented using cloud-based firewalls and segmentation tools.
Even though the implementation has changed, the core principle remains the same: separating public-facing services from private internal resources. This ensures that security remains consistent even in distributed environments.
Importance of Proper Configuration
The effectiveness of a DMZ depends heavily on proper configuration. Firewall rules must be carefully designed to allow only necessary traffic. Unnecessary open ports or overly permissive rules can weaken the entire security model.
Regular audits and updates are essential to maintain the integrity of the DMZ. Security policies should evolve alongside new threats and organizational changes.
DMZ Security Architecture in Depth
A perimeter network or DMZ is not just a simple separation zone; it is a carefully structured security architecture that relies on layered protection, strict segmentation, and controlled communication paths. The deeper purpose of a DMZ is to enforce the principle that no external system should ever directly interact with internal resources without passing through multiple security checks.
Firewall Placement and Role in DMZ
Firewalls are the backbone of any DMZ design. In most secure implementations, at least two firewalls are used to create layered defense. The first firewall sits between the external network and the DMZ, controlling all incoming and outgoing traffic from public sources. The second firewall sits between the DMZ and the internal network, acting as a stricter barrier that filters internal access.
This dual-layer firewall structure ensures that even if one layer is compromised or misconfigured, another layer still protects the internal systems. Each firewall is configured with specific rules that define which services are allowed to communicate and under what conditions.
Traffic Filtering and Access Control
Traffic filtering in a DMZ is highly restrictive. Only explicitly permitted protocols and services are allowed to pass through. For example, HTTP or HTTPS traffic may be allowed to a web server, while all other ports remain blocked. This minimizes exposure to unnecessary attack surfaces.
Access control is also enforced based on source, destination, port, and protocol. In more advanced setups, additional checks such as user authentication, device identity, and behavioral analysis may also be applied before allowing communication.
Segmentation Strategy in DMZ Design
Segmentation is one of the most important principles in DMZ architecture. Instead of placing all public services in a single unprotected space, they are often divided into smaller segments. For example, web servers may be separated from email servers, and each segment may have its own firewall rules.
This internal segmentation ensures that if one service is compromised, the attacker cannot easily move laterally to other services within the DMZ. It creates multiple internal boundaries that further reduce risk.
Data Flow Restrictions Between Zones
In a properly designed DMZ, data flow is tightly controlled in both directions. External users can only access specific services in the DMZ, and DMZ systems can only communicate with internal systems when absolutely necessary.
Even when communication is allowed, it is often one-directional or heavily filtered. For example, a web server in the DMZ might retrieve data from an internal database, but the database will never accept direct external requests.
This strict control of data flow ensures that sensitive information remains protected even if one part of the system is compromised.
Role of Proxies in DMZ Environments
Proxy servers are commonly deployed within a DMZ to act as intermediaries between users and internal services. A proxy server receives requests from external clients and forwards them to the appropriate internal or DMZ services after applying security checks.
This setup hides internal network structures from external users and adds an additional layer of abstraction. It also allows organizations to monitor, filter, and log traffic more effectively.
Intrusion Detection and Prevention Systems
Intrusion detection systems (IDS) and intrusion prevention systems (IPS) play a critical role in DMZ security. These systems continuously monitor network traffic for suspicious patterns or known attack signatures.
An IDS typically alerts administrators when unusual activity is detected, while an IPS can actively block or drop malicious traffic in real time. Together, they provide continuous monitoring and automated threat response within the DMZ.
Logging and Monitoring in DMZ
Logging is an essential component of DMZ management. Every connection, request, and data transfer is recorded for analysis. These logs help security teams detect anomalies, investigate incidents, and improve system defenses.
Monitoring tools analyze this data in real time, identifying unusual spikes in traffic, repeated failed login attempts, or unauthorized access attempts. This continuous visibility is crucial for maintaining security in a high-risk exposure zone like a DMZ.
Attack Scenarios and DMZ Protection
To understand the importance of a DMZ, it is useful to consider potential attack scenarios. Without a DMZ, a compromised public server could provide direct access to internal databases, financial records, or sensitive business systems.
With a DMZ in place, however, the attacker is limited to the isolated environment. Even if they gain control of a public-facing server, they must still overcome additional firewalls, authentication systems, and segmentation barriers before reaching internal resources.
This containment significantly reduces the potential damage of a breach.
Lateral Movement Prevention
Lateral movement refers to an attacker moving from one compromised system to another within a network. A well-designed DMZ restricts this behavior by limiting internal communication paths and enforcing strict segmentation rules.
Even within the DMZ itself, systems are often isolated from each other. This means that compromising one service does not automatically grant access to others.
Authentication and Identity Controls
Authentication mechanisms are often integrated into DMZ architecture to ensure that only verified users and systems can access services. These may include multi-factor authentication, token-based systems, or certificate-based validation.
Identity controls ensure that every request is associated with a verified source, reducing the risk of unauthorized access.
Encryption and Secure Communication
Data transmitted through a DMZ is often encrypted to protect it from interception or tampering. Secure protocols ensure that even if traffic is captured, it cannot be easily read or modified by attackers.
Encryption is especially important for sensitive communications such as login credentials, personal data, or financial transactions passing through DMZ services.
DMZ in Enterprise-Level Security Models
In large organizations, DMZ architecture is often part of a broader enterprise security model that includes multiple security zones. These may include internal trusted zones, restricted zones, and highly secure data zones.
The DMZ acts as the first layer of exposure, while deeper layers protect critical business assets. This hierarchical structure ensures that security increases as systems become more sensitive.
High Availability and Redundancy in DMZ
To ensure continuous service, DMZ environments are often designed with redundancy. Multiple servers may perform the same function, so if one fails, another can take over without interruption.
Load balancing may also be used to distribute traffic evenly across multiple systems, improving performance and reliability while maintaining security controls.
Security Policy Management
Security policies define how the DMZ operates. These policies include rules for traffic filtering, access control, authentication, and monitoring. They must be carefully documented and consistently enforced.
Regular policy reviews are necessary to ensure that the DMZ remains aligned with evolving security threats and organizational requirements.
Challenges in Managing a DMZ
Managing a DMZ can be complex due to its layered structure and strict security requirements. Misconfigurations are one of the most common risks, as a single incorrect firewall rule can expose internal systems or block legitimate traffic.
Another challenge is balancing security with performance. Overly strict rules may slow down legitimate communication, while overly relaxed rules may weaken security.
Evolution of DMZ Concepts
The concept of a DMZ has evolved significantly over time. In traditional networks, it was implemented using physical hardware and segmented network zones. In modern environments, virtualization and cloud technologies have transformed DMZs into software-defined security layers.
Despite these changes, the core principle remains the same: separating trusted internal systems from untrusted external access points.
Advanced DMZ Understanding
A perimeter network or DMZ is a fundamental security architecture designed to protect internal systems while allowing controlled external access. Through layered firewalls, strict segmentation, monitoring systems, and controlled communication paths, it creates a secure buffer zone that reduces risk and limits the impact of potential attacks.
DMZ Deployment Models and Real-World Structures
A perimeter network or DMZ can be deployed in different architectural models depending on the size of the organization, security requirements, and complexity of services being offered. Each model follows the same core principle of isolating public-facing systems, but the structure and level of protection vary. The most common designs include single-tier, dual-tier, and multi-tier DMZ architectures, each offering different levels of control and segmentation.
Single Firewall DMZ Design
In a single firewall DMZ setup, one firewall device is used to manage traffic between three zones: the external network, the DMZ, and the internal network. The firewall is configured with multiple interfaces, each assigned to a different zone.
This model is simpler to deploy and manage, making it suitable for smaller environments. However, since a single device handles all filtering, it also represents a single point of failure. If the firewall is misconfigured or compromised, both the DMZ and internal network may be at risk.
Despite this limitation, proper rule configuration and regular monitoring can still make this model reasonably secure for less complex environments.
Dual Firewall DMZ Design
The dual firewall design is a more secure and widely recommended approach. It uses two separate firewalls: one placed between the external network and the DMZ, and another placed between the DMZ and the internal network.
This separation ensures that even if one firewall is bypassed or compromised, the second firewall still provides an additional layer of defense. Each firewall can also be configured by different security policies or even different vendors, reducing the risk of uniform failure.
The dual firewall model significantly improves isolation and is commonly used in enterprise-level environments where security is a high priority.
Multi-Tier DMZ Architecture
A multi-tier DMZ takes segmentation further by creating multiple isolated layers within the DMZ itself. Instead of a single buffer zone, there are several sub-zones, each serving a specific purpose.
For example, one tier may host web servers, another may handle application logic, and a third may connect to internal databases. Each tier is separated by firewalls or strict access controls.
This structure minimizes risk by ensuring that even if one layer is compromised, attackers still face additional barriers before reaching critical systems.
Role of Application Layer Security
Beyond network-level security, application-layer controls play an important role in DMZ protection. Many attacks target vulnerabilities in software applications rather than the network itself.
To counter this, systems in the DMZ often include application firewalls that inspect traffic at a deeper level. These tools analyze requests for malicious patterns, injection attempts, or abnormal behavior before allowing them to reach the application.
This adds another layer of defense beyond traditional packet filtering.
Zero Trust Influence on DMZ Design
Modern cybersecurity approaches such as Zero Trust have influenced how DMZs are designed. Instead of assuming that anything inside a network zone is safe, Zero Trust principles assume that no system is inherently trusted.
In this model, every request must be continuously verified, regardless of whether it originates from the DMZ, internal network, or external source. This approach reduces reliance on traditional perimeter boundaries and enhances security even within segmented environments.
As a result, modern DMZs are often integrated into Zero Trust architectures rather than functioning as standalone protective zones.
Cloud-Based DMZ Implementations
With the growth of cloud computing, traditional DMZ structures have evolved into virtualized security zones. Instead of physical firewalls and hardware segmentation, cloud environments use virtual firewalls, security groups, and software-defined networking.
These virtual DMZs provide the same isolation principles but offer greater flexibility and scalability. Services can be deployed across distributed environments while still maintaining strict access control between public and private resources.
Cloud-based DMZs are particularly useful for organizations with dynamic workloads and globally distributed users.
Hybrid Network DMZ Models
Many organizations operate in hybrid environments that combine on-premises infrastructure with cloud services. In such cases, the DMZ must span both environments.
A hybrid DMZ ensures secure communication between internal data centers and cloud-hosted services. Secure tunnels, encrypted connections, and consistent security policies are used to maintain protection across both environments.
This model is increasingly common as businesses transition to cloud-first strategies while still maintaining legacy systems.
Threat Landscape and DMZ Relevance
The modern threat landscape is constantly evolving, with attackers using more advanced techniques such as automated scanning, phishing, ransomware, and zero-day exploits. In this environment, the DMZ remains a critical defensive layer.
It reduces exposure by ensuring that external users never directly interact with sensitive systems. Even when attackers target public services, the DMZ limits how far they can progress within the network.
This containment strategy is essential for minimizing damage during cyber incidents.
Defense in Depth Strategy
The DMZ is a core component of the broader defense in depth strategy, which relies on multiple overlapping security controls. Instead of depending on a single security measure, organizations implement several layers such as firewalls, encryption, authentication, monitoring, and segmentation.
The DMZ serves as the outer defensive layer in this model, filtering and controlling external traffic before it reaches deeper security layers.
This layered approach ensures that even if one defense fails, others remain in place to protect critical assets.
Performance Considerations in DMZ Design
While security is the primary focus of a DMZ, performance must also be considered. Every security check, firewall rule, and inspection adds some level of processing overhead.
To maintain efficiency, organizations often optimize traffic paths, use load balancers, and deploy high-performance security appliances. Proper design ensures that security does not significantly impact system responsiveness.
Balancing performance and protection is a key aspect of effective DMZ implementation.
Common Misconfigurations and Risks
One of the biggest risks in DMZ environments is misconfiguration. Incorrect firewall rules, overly permissive access controls, or exposed services can create serious vulnerabilities.
For example, if internal systems are accidentally made accessible from the DMZ without proper restrictions, attackers could bypass intended security barriers.
Regular audits, automated configuration checks, and strict change management processes are essential to prevent such issues.
Monitoring and Incident Response
Effective DMZ security depends heavily on continuous monitoring. Security teams track network traffic, system logs, and user activity to detect unusual behavior.
When suspicious activity is detected, incident response procedures are activated. These may include isolating affected systems, blocking malicious traffic, or investigating compromised services.
Rapid response is crucial to minimizing the impact of potential breaches.
Future of Perimeter Networks
The traditional idea of a fixed network perimeter is gradually changing due to cloud computing, remote work, and mobile access. However, the concept of controlled exposure zones like DMZs is still highly relevant.
Instead of disappearing, DMZs are evolving into more dynamic, software-defined, and identity-driven security layers. The focus is shifting from location-based security to behavior-based and identity-based protection.
This evolution ensures that the core principle of separating trusted and untrusted systems continues to remain relevant in modern IT environments.
Final Understanding of DMZ Architecture
A perimeter network or DMZ is a foundational cybersecurity structure designed to create a secure boundary between external networks and internal systems. Through carefully controlled segmentation, layered firewalls, monitoring systems, and strict access policies, it ensures that public-facing services can operate safely without exposing critical infrastructure.
Its design continues to evolve with modern technologies, but its core purpose remains unchanged: reducing risk, controlling access, and protecting sensitive data from external threats.
DMZ Security Operations and Maintenance Practices
A perimeter network or DMZ is not a one-time setup but an ongoing security environment that requires continuous management, maintenance, and optimization. Its effectiveness depends on how well it is operated on a daily basis, how quickly it adapts to new threats, and how consistently security policies are enforced across all connected systems.
Continuous Security Monitoring
Continuous monitoring is one of the most critical operational practices in a DMZ environment. Every packet of data entering or leaving the DMZ is potentially meaningful from a security standpoint. Monitoring tools are used to observe traffic patterns, detect anomalies, and identify unauthorized access attempts in real time.
Security teams analyze logs generated by firewalls, intrusion detection systems, servers, and applications. These logs help identify unusual behavior such as repeated failed login attempts, unexpected traffic spikes, or unauthorized connection attempts between zones.
By maintaining constant visibility, organizations can detect threats early and respond before significant damage occurs.
Patch Management and System Updates
Systems located within the DMZ are often exposed to external networks, making them more vulnerable to attacks. Because of this exposure, regular patch management is essential.
Operating systems, applications, and security tools must be updated frequently to fix known vulnerabilities. Attackers often target outdated software, so delaying updates can create serious security risks.
Patch management in a DMZ is carefully planned to avoid service disruption while ensuring that security gaps are closed as quickly as possible.
Configuration Management and Change Control
Configuration management ensures that all DMZ systems are set up consistently and securely. Any changes to firewall rules, server settings, or access controls must follow a controlled approval process.
Unauthorized or poorly planned changes can introduce vulnerabilities. For example, opening unnecessary ports or loosening firewall restrictions can expose internal systems to external threats.
Change control procedures help ensure that every modification is reviewed, tested, and documented before being implemented in the live environment.
User Access Control and Privilege Management
Access control is a key aspect of DMZ security operations. Only authorized personnel should be able to manage or modify systems within the DMZ. Even then, access should be limited based on job roles and responsibilities.
The principle of least privilege is applied, meaning users are granted only the minimum level of access required to perform their tasks. This reduces the risk of accidental or intentional misuse of system resources.
Administrative access is often further protected using multi-factor authentication and secure login mechanisms.
Network Segmentation Reinforcement
Over time, DMZ environments may expand as new services are added. Without proper control, this expansion can weaken segmentation. Regular reviews are necessary to ensure that network boundaries remain strong and clearly defined.
Segmentation reinforcement involves verifying that each service remains in its correct zone and that communication between zones follows approved pathways only.
This helps maintain the integrity of the original security design even as the infrastructure evolves.
Incident Detection and Response Workflow
When a potential security incident occurs within a DMZ, a structured response process is followed. The first step is detection, where monitoring systems identify suspicious activity. Next, the incident is analyzed to determine its severity and impact.
If the threat is confirmed, containment measures are applied. This may include isolating affected systems, blocking malicious IP addresses, or disabling compromised services.
After containment, recovery steps are taken to restore normal operations, followed by a detailed investigation to understand the root cause and prevent future occurrences.
Backup and Recovery Strategies
Because DMZ systems often support critical external services, backup and recovery planning is essential. Regular backups ensure that data and configurations can be restored in case of system failure, corruption, or cyberattacks.
Backup data is typically stored in secure, isolated locations that are not directly accessible from the DMZ. This prevents attackers from targeting backup systems during an intrusion.
Recovery plans are tested periodically to ensure that services can be restored quickly and reliably when needed.
Performance Optimization in Secure Environments
Security controls in a DMZ can sometimes introduce latency or reduce system performance. To balance security and efficiency, performance optimization techniques are applied.
Load balancing distributes traffic across multiple servers to prevent overload. Caching mechanisms reduce repeated processing of identical requests. Efficient firewall rule design also helps minimize unnecessary processing overhead.
These optimizations ensure that security does not negatively impact user experience or service availability.
Threat Intelligence Integration
Modern DMZ environments often integrate threat intelligence feeds to stay updated on emerging cyber threats. These feeds provide real-time information about malicious IP addresses, attack patterns, and vulnerabilities being actively exploited.
By integrating this intelligence into security systems, organizations can proactively block or monitor suspicious activity before it becomes a direct threat.
This proactive approach strengthens the overall defensive capability of the DMZ.
Security Auditing and Compliance
Regular security audits are conducted to evaluate the effectiveness of DMZ controls. These audits examine firewall configurations, access policies, system logs, and segmentation rules to ensure compliance with security standards.
Audits help identify weaknesses, misconfigurations, or outdated practices that may increase risk. Compliance requirements may also dictate specific security measures that must be implemented within the DMZ.
Maintaining compliance ensures that the organization meets industry security expectations and reduces legal or regulatory risks.
Role of Automation in DMZ Management
Automation is increasingly used in DMZ environments to improve efficiency and reduce human error. Automated tools can manage firewall rules, monitor system health, apply patches, and respond to certain types of security events.
Automation helps ensure consistency in security enforcement and allows faster response to threats. However, it must be carefully controlled to avoid unintended changes or over-automation of critical decisions.
Human oversight remains essential even in highly automated environments.
Evolving Attack Techniques and DMZ Adaptation
Cyber attackers continuously develop new techniques to bypass security systems. These include advanced persistent threats, zero-day exploits, and social engineering attacks.
To remain effective, DMZ architectures must evolve alongside these threats. This includes updating detection systems, improving segmentation strategies, and strengthening authentication mechanisms.
Adaptability is a key requirement for maintaining long-term security effectiveness.
Integration with Identity and Access Management
Modern DMZ environments are closely integrated with identity and access management systems. Instead of relying solely on network-based controls, access decisions are increasingly based on user identity, device trust level, and contextual factors.
This integration ensures that only verified users with appropriate permissions can access specific services, even if they are within the same network zone.
Identity-based security adds a more dynamic layer of protection beyond traditional perimeter boundaries.
Importance of Documentation and Policy Enforcement
Clear documentation is essential for managing DMZ environments effectively. All configurations, policies, and procedures must be properly recorded to ensure consistency and accountability.
Policy enforcement ensures that security rules are applied uniformly across all systems. Without proper enforcement, even well-designed security policies may fail in practice.
Documentation also supports troubleshooting, auditing, and training activities.
Long-Term Sustainability of DMZ Architectures
Sustaining a DMZ over time requires continuous investment in security tools, skilled personnel, and infrastructure improvements. As technology evolves, so must the design and operation of perimeter networks.
Organizations must regularly reassess their security architecture to ensure it remains effective against modern threats. This includes adopting new technologies, updating policies, and refining operational practices.
A well-maintained DMZ continues to provide strong protection even in rapidly changing digital environments.
Final Perspective on DMZ Operations
A perimeter network or DMZ is more than just a network design concept; it is an active, evolving security ecosystem. Its strength lies not only in its structure but also in how it is managed, monitored, and continuously improved.
Through consistent maintenance, strict access control, real-time monitoring, and adaptive security practices, a DMZ plays a crucial role in protecting internal systems from external threats while enabling safe and controlled connectivity with the outside world.
Conclusion
A perimeter network, or DMZ, is a vital part of modern network security that creates a controlled boundary between trusted internal systems and untrusted external environments. It works as a protective buffer where public-facing services can operate without directly exposing sensitive internal resources. This separation reduces risk, limits the impact of potential attacks, and strengthens overall security posture.
Through layered firewalls, strict access control, segmentation, and continuous monitoring, a DMZ ensures that all incoming and outgoing traffic is carefully inspected and regulated. Even if an external service is compromised, the internal network remains shielded by additional security barriers.
Over time, the concept of a DMZ has evolved from traditional hardware-based networks to virtualized and cloud-based environments, but its core principle remains the same: isolating critical systems while still enabling secure communication with external users.
In today’s cybersecurity landscape, where threats are constantly evolving, a DMZ continues to play an essential role in defense-in-depth strategies. It provides organizations with a balanced approach to accessibility and protection, ensuring that services remain available while internal systems stay secure.