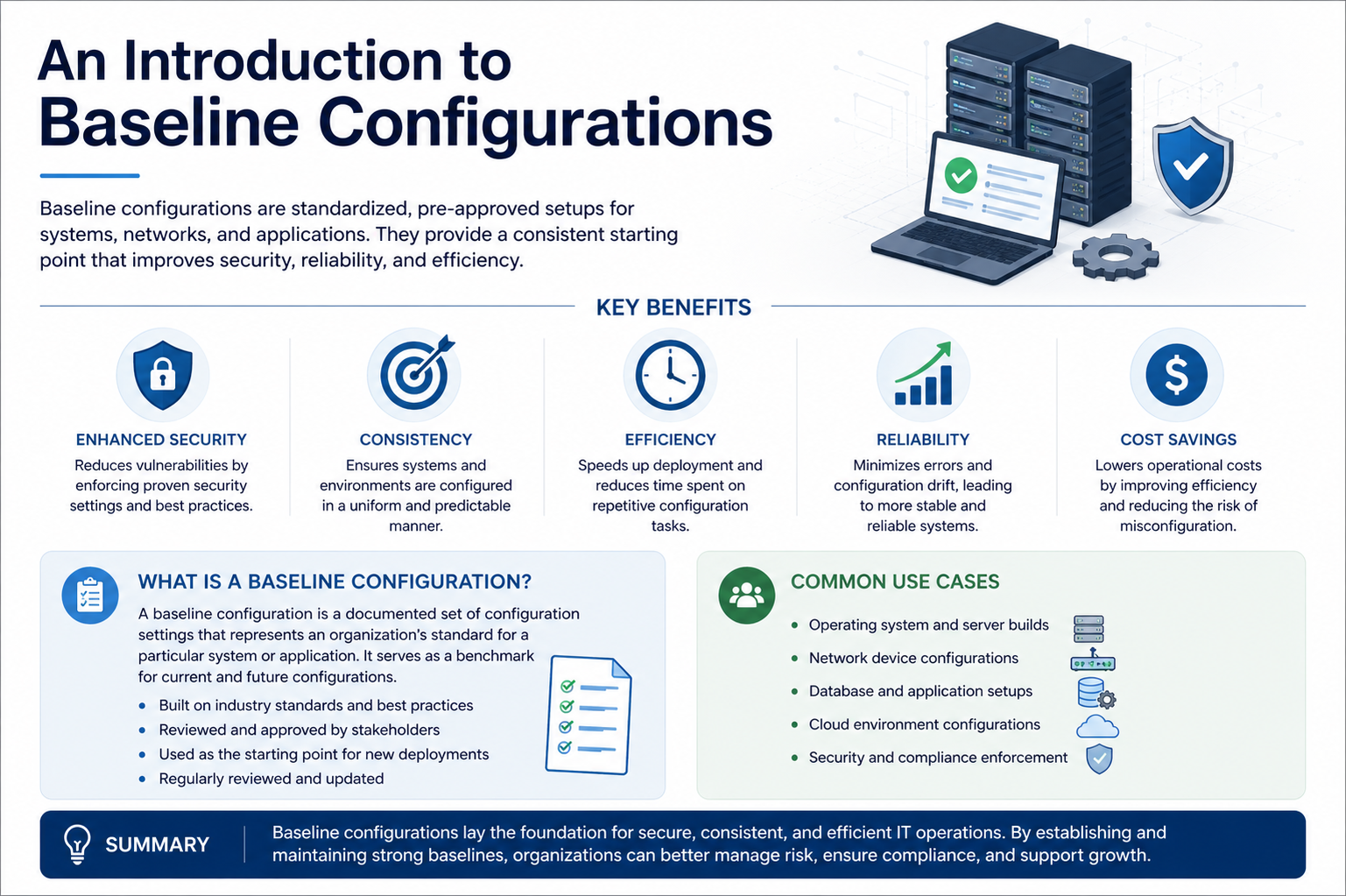
Baseline configurations refer to a predefined and standardized set of system or software settings that serve as a reference point for maintaining consistency across environments. These configurations define how systems should be set up initially, ensuring that all deployments follow the same foundational structure. By establishing a baseline, organizations can reduce variability, improve reliability, and maintain better control over system behavior.
Purpose of Baseline Configurations
The main purpose of baseline configurations is to create a stable and secure starting point for systems. They help ensure that every system begins with approved settings, which reduces the risk of misconfigurations and security vulnerabilities. This consistency also makes it easier to manage updates, monitor performance, and enforce compliance across multiple environments.
Key Elements of Baseline Configurations
Baseline configurations typically include operating system settings, security controls, installed software versions, network parameters, and user access rules. These elements are carefully selected to meet organizational requirements and industry best practices. Once defined, they act as a benchmark that all systems should align with throughout their lifecycle.
Importance in System Management
Using baseline configurations improves operational efficiency by simplifying system deployment and maintenance. It allows administrators to quickly identify deviations from the standard setup and correct them before they cause issues. This approach also supports scalability, as new systems can be deployed rapidly using the same trusted configuration model.
Application in Real Environments
Baseline configurations are widely used in IT infrastructure, cloud environments, and enterprise networks. They help organizations maintain uniformity across servers, applications, and devices. This uniformity is essential for troubleshooting, auditing, and ensuring that systems remain secure and predictable over time.
Evolution of Baseline Configurations
The concept of baseline configurations has evolved alongside the growth of computing systems. In earlier computing environments, system setups were often manual and inconsistent, leading to frequent errors and operational inefficiencies. As organizations began to scale their infrastructure, the need for standardized configurations became more apparent. This led to the development of structured approaches for defining system states that could be replicated across multiple machines. Over time, baseline configurations became a fundamental part of system administration and IT governance, especially with the rise of large-scale enterprise networks and distributed systems.
Core Principles Behind Baseline Configurations
Baseline configurations are built on several important principles that ensure their effectiveness. Consistency is one of the most important, as it ensures that all systems behave in a predictable manner. Security is another key principle, since baseline settings often include hardened configurations that reduce vulnerabilities. Repeatability is also essential, allowing systems to be deployed in the same state every time without manual intervention. Lastly, maintainability ensures that configurations can be updated and managed efficiently as organizational needs evolve.
Types of Baseline Configurations
Baseline configurations can be categorized into different types depending on their focus and application. System baseline configurations define the core operating system settings and installed components. Security baseline configurations focus on protective measures such as access controls, password policies, and encryption standards. Network baseline configurations establish rules for communication, routing, and connectivity. Application baseline configurations define how specific software applications should be installed and operated within an environment. Each type plays a role in maintaining a stable and controlled infrastructure.
Creation of Baseline Configurations
Creating a baseline configuration involves careful planning and analysis. The process begins by identifying organizational requirements, including performance expectations, security standards, and compliance obligations. Once these requirements are defined, system administrators select appropriate settings that align with best practices. These settings are then documented in detail to ensure clarity and repeatability. After implementation, the baseline is tested in controlled environments to verify stability and compatibility before being deployed across production systems.
Role in Standardization
Baseline configurations play a critical role in standardization across IT environments. Without a baseline, systems may be configured differently by various administrators, leading to inconsistencies and operational challenges. Standardization ensures that every system follows the same structure, making it easier to manage large-scale infrastructures. It also simplifies training, as administrators only need to learn one standardized configuration model instead of multiple variations.
Security Benefits of Baseline Configurations
One of the most important advantages of baseline configurations is improved security. By defining secure default settings, organizations can reduce the risk of unauthorized access and system vulnerabilities. Baseline configurations often disable unnecessary services, enforce strong authentication mechanisms, and restrict administrative privileges. These measures help create a hardened environment that is more resistant to cyber threats. Additionally, consistent configurations make it easier to detect unauthorized changes, as deviations from the baseline can be quickly identified and corrected.
Baseline Drift and Its Impact
Over time, systems may gradually deviate from their original baseline configurations due to updates, manual changes, or software installations. This phenomenon is known as baseline drift. When drift occurs, systems become less consistent and may introduce security or performance issues. Managing baseline drift is essential to maintaining system integrity. Regular audits and automated monitoring tools are often used to compare current system states against the established baseline and detect any differences that need correction.
Maintenance and Updating of Baselines
Baseline configurations are not static and must be updated periodically to remain effective. As technology evolves and new threats emerge, baseline settings need to be adjusted accordingly. Maintenance involves reviewing existing configurations, incorporating new security practices, and ensuring compatibility with updated software versions. Proper version control is essential during this process, as it allows organizations to track changes and revert to previous configurations if needed.
Challenges in Managing Baseline Configurations
Despite their benefits, managing baseline configurations can present certain challenges. One common issue is complexity, especially in large environments with diverse systems. Ensuring that all systems adhere to a single baseline can be difficult when different applications or departments have unique requirements. Another challenge is keeping the baseline up to date without disrupting system stability. Additionally, enforcing compliance across distributed systems requires robust monitoring and management tools.
Role in Automation and Modern Infrastructure
In modern IT environments, baseline configurations are closely tied to automation. Automated deployment tools rely on predefined baselines to quickly provision systems without manual intervention. This approach reduces human error and speeds up deployment processes. In cloud-based environments, baseline configurations are often used to define virtual machine templates, ensuring that every instance is created with consistent settings. Automation also makes it easier to enforce baseline compliance at scale.
Governance and Compliance Considerations
Baseline configurations are an important part of IT governance and regulatory compliance. Many industries require organizations to maintain secure and standardized system configurations as part of compliance frameworks. Baselines help demonstrate that systems are configured according to approved standards and policies. They also support audit processes by providing a clear reference point for evaluating system integrity.
Baseline Configuration Lifecycle
The lifecycle of baseline configurations describes how they are created, maintained, updated, and eventually replaced. It begins with the planning stage, where requirements are gathered based on organizational goals, security policies, and operational needs. During this phase, stakeholders define what a “standard system state” should look like, ensuring that both functional and security expectations are considered. This initial planning is critical because it sets the foundation for every system that will be deployed under that baseline.
Once requirements are defined, the design and development phase begins. In this stage, specific configuration settings are selected and documented. These settings may include system parameters, security policies, network rules, and application preferences. The goal is to create a configuration model that is both secure and practical for real-world deployment. Careful attention is given to compatibility, ensuring that the baseline does not interfere with essential business applications or services.
After the design phase, the baseline moves into testing. Testing is an important step because it verifies that the configuration works as intended in a controlled environment. Systems are deployed using the baseline settings, and their performance, stability, and security are evaluated. Any issues discovered during testing are corrected before the baseline is approved for production use. This step ensures that the configuration is reliable and does not introduce unexpected problems.
Once validated, the baseline is deployed across production systems. This deployment can happen manually or through automated tools, depending on the size and complexity of the environment. In modern infrastructures, automation is often preferred because it ensures consistency and reduces human error. At this stage, all systems begin operating under the standardized configuration, which improves uniformity and simplifies management.
After deployment, the maintenance phase begins. This is a continuous process where the baseline is monitored and reviewed regularly. Systems may evolve over time due to updates, patches, or new software installations, so the baseline must also evolve. Maintenance ensures that the configuration remains relevant, secure, and aligned with organizational needs. Without proper maintenance, baselines can become outdated and lose their effectiveness.
Eventually, a baseline may be retired or replaced. This happens when technology changes significantly or when organizational requirements shift. A new baseline is then created, following the same lifecycle process. This cyclical approach ensures that system configurations remain modern and effective over time.
Baseline Configuration in Security Management
Baseline configurations play a major role in strengthening system security. By defining secure default settings, organizations can reduce exposure to threats and limit potential attack surfaces. These configurations often include disabling unnecessary services, enforcing strong authentication mechanisms, and restricting administrative privileges. Such measures reduce the number of vulnerabilities that attackers can exploit.
Security baselines also ensure consistency in protection mechanisms across all systems. When every system follows the same security rules, it becomes easier to enforce policies and detect deviations. For example, if one system suddenly allows unauthorized access or enables a disabled service, it can be quickly identified as a violation of the baseline.
Another important aspect of security baselines is hardening. System hardening involves configuring systems in the most secure way possible by removing unnecessary components and tightening access controls. Baseline configurations often serve as the foundation for this process. By starting with a hardened baseline, organizations can significantly improve their overall security posture.
Monitoring and auditing are also closely tied to baseline security. Continuous monitoring tools compare current system states against the established baseline. Any deviation is flagged for investigation. This helps detect unauthorized changes, configuration drift, or potential security breaches. Regular audits further ensure that systems remain compliant with security standards and organizational policies.
Role of Automation in Baseline Configurations
Automation has become a key factor in managing baseline configurations, especially in large-scale environments. Manual configuration of systems is time-consuming and prone to errors, which is why automated tools are widely used. These tools allow administrators to define baseline settings once and then apply them consistently across multiple systems.
Automated deployment ensures that every new system is configured exactly the same way. This eliminates inconsistencies caused by human error and speeds up the provisioning process. In cloud environments, automation is even more critical, as systems are often created and destroyed dynamically based on demand.
Configuration management tools also help enforce baseline compliance. They continuously monitor systems and automatically correct any deviations from the baseline. This process, often referred to as self-healing configuration management, ensures that systems remain aligned with the standard configuration without manual intervention.
Automation also supports scalability. As organizations grow, the number of systems increases, making manual management impractical. Automated baseline enforcement allows organizations to scale efficiently while maintaining consistency and security across all systems.
Baseline Drift and Configuration Integrity
Baseline drift occurs when systems gradually deviate from their original configuration. This can happen due to software updates, manual changes, or temporary fixes applied during troubleshooting. While these changes may seem minor individually, over time they can significantly alter system behavior and reduce consistency.
One of the main risks of baseline drift is reduced security. When systems are no longer aligned with the baseline, they may develop vulnerabilities or expose unnecessary services. This creates inconsistencies that attackers can potentially exploit. Drift also makes troubleshooting more difficult because systems no longer share a consistent configuration.
To manage baseline drift, organizations use monitoring and compliance tools. These tools regularly scan systems and compare their current state with the approved baseline. When differences are detected, administrators are alerted, and corrective actions can be taken. In some cases, automated remediation is used to restore systems back to the baseline state.
Preventing drift is often more effective than correcting it. This is achieved through strict change management processes. Any modification to a system must be reviewed and approved before implementation. This ensures that changes are intentional, documented, and aligned with organizational standards.
Baseline Configurations in Enterprise Environments
In enterprise environments, baseline configurations are essential for managing complex infrastructures. Large organizations often operate hundreds or thousands of systems across different locations. Without a standardized configuration approach, managing such environments would be extremely difficult.
Baseline configurations ensure that all systems behave consistently, regardless of where they are deployed. This consistency simplifies administration tasks such as monitoring, troubleshooting, and updating systems. It also reduces training requirements, as administrators only need to understand one standardized configuration model.
Enterprises often maintain multiple baselines for different system types. For example, servers, workstations, and cloud instances may each have their own baseline configuration. This allows organizations to tailor settings based on specific use cases while still maintaining overall consistency within each category.
Baseline configurations also support disaster recovery and business continuity. In the event of system failure, new systems can be quickly deployed using the existing baseline. This ensures minimal downtime and faster recovery.
Challenges in Large-Scale Baseline Management
Managing baseline configurations at scale introduces several challenges. One major challenge is maintaining consistency across diverse environments. Different departments or teams may have unique requirements, making it difficult to enforce a single baseline.
Another challenge is version control. As baselines evolve, organizations must carefully manage different versions to avoid confusion. Without proper tracking, systems may end up using outdated or incompatible configurations.
Performance optimization is also a challenge. A baseline that works well for one environment may not perform efficiently in another. Balancing standardization with flexibility is often a complex task.
Finally, ensuring compliance across all systems requires continuous monitoring and strong governance. Without proper oversight, deviations can accumulate quickly, reducing the effectiveness of the baseline.
Baseline Configurations in Cloud Computing Environments
In cloud computing environments, baseline configurations play a critical role in ensuring that virtual machines, containers, and services are deployed in a consistent and controlled manner. Cloud platforms are highly dynamic, with resources being created, modified, and destroyed frequently. Without standardized baseline configurations, this flexibility can quickly lead to inconsistencies and security gaps. A cloud baseline defines the default structure of virtual infrastructure, including operating system settings, network rules, storage configurations, and security policies.
One of the key advantages of baseline configurations in cloud environments is rapid scalability. When organizations need to deploy multiple instances of a system, a predefined baseline ensures that each instance is identical in configuration. This eliminates the need for manual setup and reduces the chances of configuration errors. It also allows systems to be replicated across different regions or availability zones without losing consistency.
Security is another major focus in cloud baselines. Since cloud systems are often exposed to the internet, baseline configurations typically include strict security controls. These may involve disabling unnecessary ports, enforcing encryption for data transmission, and restricting administrative access. By embedding these security measures into the baseline, organizations ensure that every deployed resource follows the same protective standards.
Cloud baseline configurations also support cost optimization. By standardizing system setups, organizations can avoid unnecessary resource usage and ensure that systems are deployed efficiently. This helps reduce wasted computing power and storage while maintaining performance and reliability.
Baseline Configurations in DevOps Practices
Baseline configurations are deeply integrated into modern DevOps practices, where automation, collaboration, and continuous delivery are key principles. In DevOps environments, baseline configurations are often defined as infrastructure-as-code, allowing system setups to be version-controlled and automatically deployed.
This approach ensures that development, testing, and production environments remain consistent. Developers can work in environments that closely match production systems, reducing the risk of unexpected behavior when code is deployed. Baseline configurations also enable continuous integration and continuous deployment pipelines to function more reliably.
Another important aspect of DevOps is speed. Baseline configurations allow teams to quickly spin up new environments for testing or deployment. Instead of manually configuring systems, teams can rely on predefined templates that ensure consistency and reduce setup time.
DevOps also emphasizes collaboration between development and operations teams. Baseline configurations act as a shared standard that both teams can follow. This reduces misunderstandings and ensures that system expectations are clearly defined and consistently applied.
Role of Baseline Configurations in Compliance and Auditing
Compliance is a critical concern for organizations operating in regulated industries. Baseline configurations help ensure that systems meet legal, regulatory, and organizational standards. Many compliance frameworks require systems to be configured in specific ways to protect sensitive data and maintain operational integrity.
Baseline configurations provide a clear reference point for auditors. Instead of reviewing each system individually in detail, auditors can compare system states against the approved baseline. This simplifies the auditing process and makes it easier to identify non-compliant systems.
Regular compliance checks are often automated. Tools continuously scan systems and verify whether they match the baseline configuration. If deviations are found, they are logged and reported for further investigation. This helps organizations maintain continuous compliance rather than relying on periodic manual audits.
In addition to external regulations, baseline configurations also support internal governance policies. Organizations often define their own security and operational standards, and baselines ensure that these standards are consistently enforced across all systems.
Baseline Configurations and Change Management
Change management is closely linked to baseline configurations because any modification to a system can potentially affect its alignment with the baseline. Proper change management processes ensure that all changes are controlled, documented, and approved before implementation.
When a change is proposed, it is evaluated for its impact on the baseline. If the change is beneficial and aligns with organizational standards, the baseline may be updated accordingly. This ensures that the baseline evolves in a controlled manner rather than being altered randomly.
Unauthorized changes can lead to configuration drift, which weakens system consistency and security. To prevent this, organizations enforce strict access controls and monitoring systems. Only authorized personnel are allowed to modify baseline configurations.
Change management also helps maintain stability. By carefully reviewing and testing changes before deployment, organizations can avoid introducing errors or vulnerabilities into production systems. This ensures that the baseline remains a reliable foundation for all systems.
Performance Optimization Through Baseline Configurations
Baseline configurations also contribute to system performance optimization. By defining efficient default settings, organizations can ensure that systems operate at optimal levels from the moment they are deployed. This includes configuring memory usage, processor allocation, storage settings, and network parameters.
Performance baselines are often created based on testing and analysis. Systems are evaluated under different workloads to determine the most efficient configuration. These optimized settings are then incorporated into the baseline to ensure consistent performance across all deployments.
Standardized configurations also make it easier to identify performance issues. When all systems follow the same baseline, any deviation in performance can be quickly detected and analyzed. This simplifies troubleshooting and helps improve system reliability.
In large environments, performance baselines also help balance workloads. By ensuring that systems are configured uniformly, organizations can distribute resources more effectively and avoid bottlenecks.
Baseline Configurations in Virtualization and Containerization
Virtualization and containerization technologies rely heavily on baseline configurations. In virtualized environments, baseline images are used to create virtual machines with predefined settings. These images ensure that every virtual machine starts from a consistent state.
In containerized environments, baseline configurations define how containers are built and deployed. This includes specifying runtime environments, dependencies, and security settings. Containers built from the same baseline behave consistently, regardless of where they are deployed.
This consistency is essential for modern application development. It allows applications to run reliably across different environments, from development to production. It also simplifies scaling, as new containers can be quickly deployed using the same baseline configuration.
Baseline configurations in these environments also support portability. Systems can be moved between different platforms without requiring significant reconfiguration. This flexibility is one of the key advantages of modern infrastructure design.
Human Factors in Baseline Configuration Management
While automation plays a major role in baseline management, human factors remain important. System administrators and engineers are responsible for defining, reviewing, and maintaining baselines. Their expertise ensures that configurations are practical, secure, and aligned with organizational goals.
Training is essential for effective baseline management. Administrators must understand how configurations affect system behavior and security. Without proper training, there is a risk of misconfiguration or inconsistent implementation.
Communication between teams is also critical. Development, operations, and security teams must collaborate to define appropriate baseline standards. This ensures that all perspectives are considered and that the final configuration meets diverse requirements.
Human oversight is also necessary for handling exceptions. Not all systems can follow the exact same baseline due to unique requirements. In such cases, administrators must carefully evaluate deviations and ensure they do not compromise overall system integrity.
Future Trends in Baseline Configurations
Baseline configurations are expected to become even more important as technology continues to evolve. With the increasing adoption of artificial intelligence, machine learning, and edge computing, systems are becoming more complex and distributed. This complexity makes standardization even more essential.
Future baseline systems may become more adaptive, using real-time data to adjust configurations automatically. Instead of static baselines, dynamic baselines could evolve based on system performance and environmental conditions.
Artificial intelligence may also play a role in optimizing baseline configurations. By analyzing large amounts of system data, AI tools could recommend improvements and automatically adjust settings for better performance and security.
Another emerging trend is zero-trust security integration. Future baselines are likely to include stricter identity verification and continuous authentication mechanisms as part of their standard configuration.
Advanced Automation in Baseline Configuration Management
As IT environments grow more complex, advanced automation becomes a critical extension of baseline configuration management. Modern organizations no longer rely on manual enforcement of standards; instead, they use intelligent systems that continuously apply, verify, and correct configurations across thousands of endpoints. This level of automation ensures that every system remains aligned with the defined baseline without requiring constant human intervention.
Automated configuration management systems work by comparing the current state of a system with the desired baseline state. If differences are detected, the system either alerts administrators or automatically remediates the deviation. This approach significantly reduces configuration drift and improves system reliability. It also ensures faster response times when inconsistencies occur, minimizing potential downtime or security exposure.
Another important aspect of automation is scalability. In large infrastructures, manually managing baseline configurations is not feasible. Automation allows organizations to apply consistent configurations across distributed environments, including hybrid and multi-cloud systems. Whether a system is deployed in a data center or across global cloud regions, the same baseline can be enforced seamlessly.
Automation also improves accuracy. Human error is one of the leading causes of misconfiguration in IT systems. By replacing repetitive manual tasks with automated processes, organizations reduce the risk of mistakes and ensure higher consistency. This leads to more stable systems and fewer unexpected failures.
Baseline Configuration Documentation and Standardization
Proper documentation is a fundamental component of effective baseline configuration management. Without clear documentation, maintaining consistency across systems becomes extremely difficult. Documentation defines what the baseline includes, why each configuration is necessary, and how it should be implemented.
A well-documented baseline serves as a reference guide for administrators, engineers, and auditors. It ensures that everyone involved in system management has a shared understanding of configuration standards. This reduces ambiguity and improves coordination across teams.
Standardization is closely linked to documentation. When baseline configurations are standardized, organizations can apply the same structure across different environments. This reduces complexity and makes system management more predictable. Standardization also simplifies onboarding for new team members, as they only need to learn one consistent configuration model.
Version control is another important element of documentation. Baseline configurations evolve over time, and tracking these changes is essential for maintaining clarity. Versioning ensures that organizations can trace when changes were made, why they were made, and what impact they had on system behavior.
Baseline Configurations in Hybrid and Multi-Cloud Systems
Hybrid and multi-cloud environments introduce additional complexity to baseline configuration management. In these environments, systems operate across multiple platforms, each with its own infrastructure, tools, and configurations. Maintaining consistency across such diverse systems requires carefully designed baseline strategies.
Baseline configurations in hybrid environments must be flexible enough to adapt to different platforms while maintaining core consistency. This often involves defining a universal baseline structure that can be applied across cloud providers and on-premises systems. While specific settings may vary, the overall configuration principles remain consistent.
Multi-cloud environments also benefit from centralized configuration management. Organizations use unified tools to enforce baselines across different cloud providers. This ensures that systems behave consistently regardless of where they are hosted. It also simplifies monitoring and compliance, as all systems can be evaluated against the same standard.
Another important consideration in these environments is interoperability. Baseline configurations must ensure that systems from different platforms can communicate effectively. This requires careful planning of network settings, authentication methods, and data exchange protocols.
Baseline Configuration Drift Detection and Correction Mechanisms
Detecting and correcting configuration drift is a continuous process in baseline management. Drift occurs when systems gradually deviate from their defined baseline due to updates, manual changes, or external influences. Left unmanaged, drift can lead to security vulnerabilities, performance issues, and operational inconsistencies.
Modern drift detection systems operate in real time. They continuously scan systems and compare their current configuration state against the approved baseline. When discrepancies are identified, alerts are generated and sent to administrators or automated remediation systems.
Correction mechanisms vary depending on organizational policies. In some cases, systems are automatically reverted to the baseline state. In other cases, administrators review the deviation before taking action. This balance between automation and control ensures both security and operational flexibility.
Drift correction also involves identifying root causes. Understanding why a system deviated from the baseline helps prevent future occurrences. This may involve updating processes, improving automation scripts, or revising baseline configurations to better reflect real-world requirements.
Role of Baseline Configurations in System Reliability and Availability
System reliability is closely tied to consistent configurations. Baseline configurations ensure that all systems operate under the same conditions, reducing unexpected behavior and improving predictability. When systems are consistent, it becomes easier to identify and resolve issues quickly.
High availability systems depend heavily on standardized configurations. In environments where uptime is critical, such as financial systems or healthcare platforms, baseline configurations ensure that failover systems are identical to primary systems. This allows seamless switching during outages without performance degradation.
Baseline configurations also support redundancy strategies. When multiple systems are configured identically, they can take over each other’s workload without compatibility issues. This improves resilience and ensures continuous service availability.
In addition, standardized configurations reduce recovery time after failures. Since systems can be rebuilt using predefined baselines, restoration processes become faster and more efficient. This is essential for maintaining service-level agreements and minimizing operational impact.
Baseline Configurations in Security Incident Response
During security incidents, baseline configurations play an important role in detection and recovery. When a system behaves unexpectedly, comparing it against the baseline helps determine whether a compromise has occurred. Any deviation from the standard configuration may indicate unauthorized activity.
Incident response teams rely on baselines to quickly assess system integrity. By knowing what a system should look like, they can identify what has changed and whether those changes are malicious. This speeds up investigation and reduces response time.
Baseline configurations also support recovery efforts after an incident. Once a system is compromised, restoring it to its baseline state ensures that all unauthorized changes are removed. This provides a clean and secure starting point for rebuilding affected systems.
In addition, baselines help improve forensic analysis. By comparing current system states with historical baselines, investigators can trace the timeline of changes and identify how an incident occurred.
Human Oversight and Governance in Advanced Baseline Systems
Even with advanced automation, human oversight remains essential in baseline configuration management. Governance structures ensure that baseline policies align with organizational goals and security requirements. Decision-making processes are typically handled by dedicated teams responsible for IT governance and security compliance.
These teams define baseline standards, approve changes, and monitor enforcement. Their role is to ensure that automation systems operate correctly and that configurations remain aligned with strategic objectives. Without proper governance, automated systems may enforce outdated or incorrect configurations.
Regular reviews are also part of governance practices. Baselines are evaluated periodically to ensure they remain effective and relevant. This includes assessing performance, security posture, and operational efficiency. Adjustments are made based on changing business needs and technological advancements.
Human oversight is especially important when handling exceptions. Not all systems can strictly follow the same baseline due to specialized requirements. Governance teams evaluate these exceptions carefully to ensure they do not introduce risk or inconsistency.
Future Outlook of Baseline Configuration Systems
The future of baseline configurations is moving toward greater intelligence, automation, and adaptability. As systems become more complex, static configurations will gradually evolve into dynamic and self-adjusting models. These future systems will continuously optimize themselves based on real-time data and environmental conditions.
Artificial intelligence will likely play a significant role in this evolution. AI-driven systems can analyze performance patterns, detect anomalies, and recommend configuration improvements automatically. This will reduce the need for manual tuning and improve overall system efficiency.
Another emerging direction is predictive configuration management. Instead of reacting to drift or issues after they occur, future systems may anticipate problems before they happen and adjust configurations proactively.
Edge computing and distributed systems will also influence baseline evolution. As computing moves closer to end users, maintaining consistent configurations across distributed nodes will become increasingly important. Baseline systems will need to adapt to highly decentralized environments while still maintaining central control.
Conclusion
Baseline configurations serve as a fundamental pillar in modern IT and system management by establishing a consistent, secure, and repeatable foundation for all systems. They reduce variability across environments, strengthen security by enforcing standardized protective settings, and improve operational efficiency by simplifying deployment and maintenance processes. Through the use of defined standards, organizations are able to maintain better control over system behavior while minimizing the risks associated with misconfiguration.
Across different environments such as cloud computing, DevOps pipelines, enterprise infrastructure, and hybrid systems, baseline configurations ensure that systems remain aligned with organizational requirements. They support automation, enable scalability, and enhance reliability by ensuring that every system begins from a trusted and approved state. This consistency is especially important in large-scale environments where manual configuration would otherwise lead to errors and inefficiencies.
Baseline configurations also play a key role in compliance, auditing, and governance by providing a clear reference point for evaluating system integrity. They help detect configuration drift, support incident response, and ensure that systems can be quickly restored to a secure state when needed. With continuous monitoring and proper lifecycle management, baselines remain relevant and effective even as technology evolves.
As computing environments continue to grow more complex, baseline configurations will become even more important. Their integration with automation, artificial intelligence, and cloud-native technologies points toward a future where systems are not only standardized but also adaptive and self-correcting. Ultimately, baseline configurations are essential for achieving stability, security, and consistency in today’s rapidly changing digital landscape.